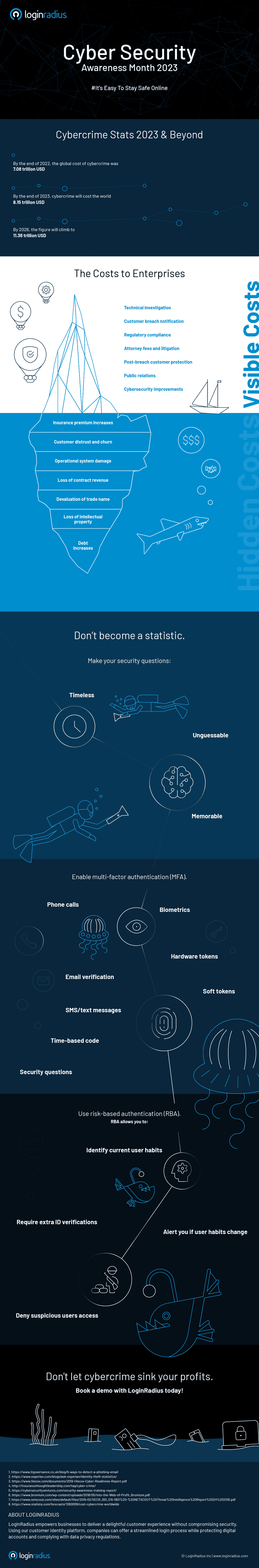
In the coming years, cybercrime will continue to grow. Between 2023 and 2028, the global 'Estimated Cost of Cybercrime' indicator in the cybersecurity market was anticipated to rise consistently, reaching a total of 5.7 trillion U.S. dollars, marking a significant increase of 69.94 percent.
Businesses of all sizes will continue facing new threats on a daily basis—phishing scams and malware being the most common ones. Both can be devastating to unprotected companies. To help you avoid becoming another cybercrime statistic, we’ve created this infographic with our top cybersecurity best practices.
In 2020, when a large chunk of the world population shifted to work from home models, cybercriminals also transitioned to remote operations. In fact, a report also suggested that remote working accounted for 20% of cybersecurity incidents that occurred during the pandemic.
2021 and 2022 were no different. Remember when Taiwanese computer giant Acer was hit by a REvil ransomware attack in March this year? The hackers demanded a whopping $50 million. They shared images of stolen files as proof of breaching Acer’s security and the consequent data leak.
Not only was the same gang responsible for the 2020 ransomware strike on Travelex, they reportedly extorted more than $100 million in one year from large businesses.
These are wake-up calls, and it is high time organizations must understand cyber threats and do everything possible to prevent data breaches.
Here are some cybersecurity best practices this infographic will cover.
Use tougher security questions.
Security questions prevent imposters from infiltrating the verification process. So what does a good security question look like?
The best ones will make it easy for legitimate users to authenticate themselves. They should be:
- Safe: Hackers shouldn’t be able to guess or research it.
- Stable: The answer shouldn’t change over time.
- Memorable: The user should be able to remember it.
- Simple: The password should be precise, easy, and consistent.
- Many: The password should have many possible answers.
Enable multi-factor authentication (MFA).
Multi-factor authentication is a powerful feature to prevent unauthorized users from accessing sensitive data.
For the most secure user sign-ins, you should use a combination of elements like biometrics, SMS/text messages, emails, and security questions. Use extra layers of protection, like text verification, email verification, or time-based security codes.
For example, you can allow an employee to log in on a managed device from your corporate network. But if a user is logging in from an unknown network on an unmanaged device, ask them to crack an additional layer of security.
Create a strong password policy.
To protect your organization's network, enforce a strong password security policy with the following practices:
- Longer passwords: The minimum length should be 15 characters, more if possible.
- Mix characters: The password should be a combination of uppercase and lowercase letters, numbers, and symbols. The more complex your password is, the harder will it be for brute force attackers.
- Do not allow dictionary words: Do not use everyday dictionary words or even a combination of words. For example, "chocolate" is a bad password, so is "dark chocolate". Go for a passphrase instead. They are a string of related words with no sentence structure. Here is an example: hotdog food ketchup relish mustard mayo.
- Don’t use memorable keyboard paths: Do not use sequential keyboard paths like qwerty, a1s2d3f4, or asdfgh.
- Change passwords regularly: Change passwords at a regular interval. It can be once every month or twice a month.
- Use a password manager: Password managers can auto-generate and store strong passwords on your behalf. They save your passwords in an encrypted, centralized location, and allow you to access them with a master password.
Embrace cybersecurity training.
Conduct cybersecurity awareness workshops to train your employees at regular intervals. It will help reduce cyberattacks caused by human error and employee negligence to a great extent.
Create data backups.
A data backup solution is one of the best measures to keep personal and business data secure from a ransomware attack. Ransomware is malicious software that is accidentally deployed by an employee by clicking on a malicious link. And deployed, all data in the site is taken hostage.
You can ensure the protection of your data by implementing continuous backups. You can use the cloud to create a copy of your data on a server and hosts it in a remote location. In case, your system is hacked, you can restore back your data.
Aside from login security tips, this infographic will also highlight:
- A few fascinating facts about cybercrime.
- The hidden costs of cybercrime.
- The intensity of damage predictions.
- A cybercriminal’s ROI
- A few eye-opening statistics
To learn more about the cybersecurity best practices for your business in 2023 and beyond, check out the infographic created by LoginRadius.
Get the best cybersecurity solutions for your enterprise with LoginRadius.

