Adversarial Defense & Agent Safety
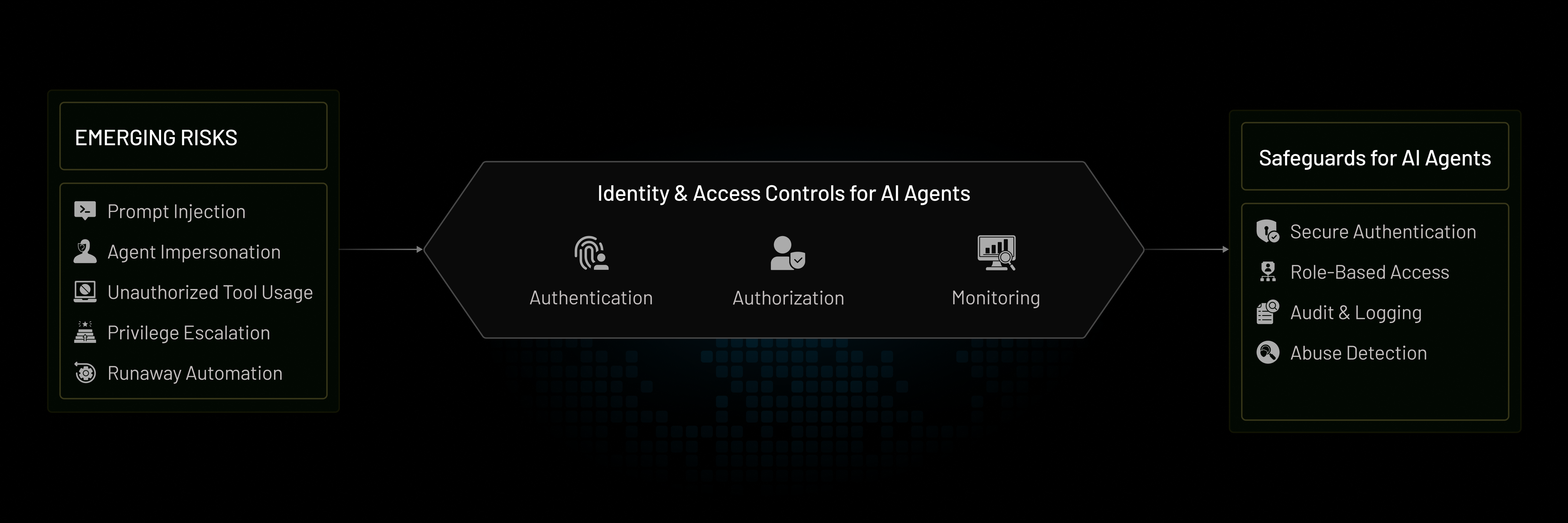
In agentic and AI-driven systems, identity is no longer limited to human users or static services. Autonomous agents can reason, act, and interact with tools, data, and systems independently—introducing new security and safety challenges.

What is Adversarial Defense & Agent Safety?
Adversarial Defense & Agent Safety refers to the identity, access, and governance controls used to protect autonomous and semi-autonomous agents from adversarial inputs, abuse scenarios, and unsafe behavior.
It addresses emerging risks such as prompt injection, agent impersonation, unauthorized tool usage, privilege escalation, and runaway automation. A safety-aware IAM approach ensures that agents remain accountable, constrained, and observable throughout their lifecycle.
Core Pillars of Adversarial Defense & Agent Safety
Safety Pillar
What It Covers
Why It Matters
What It Covers
Detection of anomalous behavior, agent impersonation, and adversarial inputs.
Why It Matters
Prevents malicious or unintended actions before impact.
Detection of anomalous behavior, agent impersonation, and adversarial inputs.
Prevents malicious or unintended actions before impact.
What It Covers
Ephemeral credentials, task-scoped permissions, and just-in-time access.
Why It Matters
Limits blast radius and reduces long-lived risk.
Ephemeral credentials, task-scoped permissions, and just-in-time access.
Limits blast radius and reduces long-lived risk.
What It Covers
Context-aware authorization, intent constraints, and action guardrails.
Why It Matters
Ensures agents operate only within approved scope.
Context-aware authorization, intent constraints, and action guardrails.
Ensures agents operate only within approved scope.
What It Covers
Approval flows, step-up verification, and override mechanisms.
Why It Matters
Maintains accountability for high-risk actions.
Approval flows, step-up verification, and override mechanisms.
Maintains accountability for high-risk actions.
What It Covers
Action logging, attribution, and traceability across agent workflows.
Why It Matters
Enables investigation, auditing, and trust.
Action logging, attribution, and traceability across agent workflows.
Enables investigation, auditing, and trust.
What It Covers
Tenant, environment, and tool isolation for agents.
Why It Matters
Prevents cascading failures and cross-tenant exposure.
Tenant, environment, and tool isolation for agents.
Prevents cascading failures and cross-tenant exposure.
Agent Safety Approaches
As organizations adopt autonomous workflows, different approaches emerge for managing agent safety and control. The following models represent how teams typically evolve their defenses.Unconstrained Agent Execution
Agents operate with broad permissions and minimal oversight. Identity and access controls are static, and agent actions are trusted by default.This approach accelerates experimentation but carries high risk as agents scale or interact with sensitive systems.
Guardrailed Agent Access
Agents are constrained by scoped permissions, predefined tools, and approval checks. Access is limited by policy, and sensitive actions require explicit safeguards.This model balances autonomy with control and is common in early production deployments.
Policy-Driven Agent Safety
Agent behavior is continuously governed by identity, intent, context, and risk. Permissions are ephemeral, actions are observable, and escalation paths are tightly controlled.This approach enables safe, scalable autonomy across complex and regulated environments.