Introduction
For years, enterprises believed access control was a solved problem. Define roles. Assign permissions. Move on.
That worked until identities stopped behaving predictably.
Today, users log in from everywhere. Devices change. Context shifts mid-session. APIs talk to APIs. Contractors become power users overnight. And suddenly, those neat role definitions feel… brittle. Over-permissioned. Blind to risk.
This is where zero trust identity management enters the picture, not as a replacement for RBAC, but as a reality check.
Here’s the uncomfortable truth: most security incidents don’t happen because systems lack roles. They happen because access decisions are made without understanding who is asking, from where, under what conditions, and whether that access still makes sense right now. Static trust breaks fast in a dynamic environment.
RBAC role-based access control is still widely used for a reason. It gives structure. It creates clarity. It keeps auditors sane. But on its own, RBAC was never designed to evaluate risk, session context, or device posture. And that gap is exactly where Zero Trust reshapes the conversation.
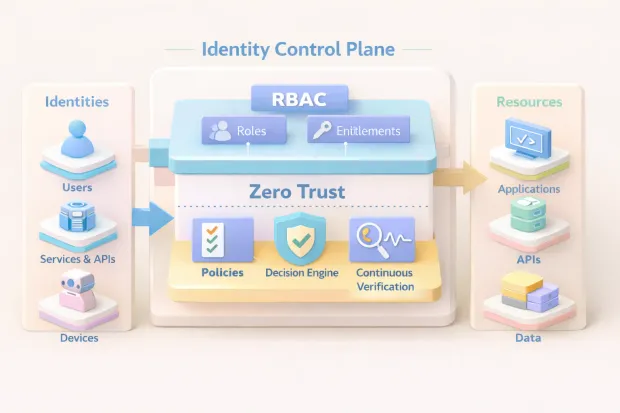
Modern enterprises aren’t choosing between RBAC and Zero Trust. They’re figuring out how RBAC fits inside a Zero Trust access management strategy, one where identity becomes the control plane, not the network.
This blog breaks down that relationship without drowning you in frameworks or theory. We’ll look at what RBAC is in security, where RBAC security still shines, where it quietly falls short, and how zero-trust identity and access management uses identity-based segmentation and continuous verification to close those gaps.
If you’ve ever wondered why your RBAC model looks clean on paper but messy in production, this will feel familiar.
Why RBAC Shows Up in Every Enterprise… and Why It Still Fails in Modern Environments
RBAC shows up everywhere because it solves a very human problem: clarity.
When organizations grow, access chaos grows faster. RBAC steps in with structure. It answers simple, necessary questions: Who should see this? Who can edit that? Who is allowed to approve? For auditors, compliance teams, and platform owners, RBAC security feels reassuring. Roles map to responsibility. Permissions look deliberate. Nothing feels random.
And for a long time, that was enough.
But modern environments don’t behave the way RBAC expects them to. Users don’t log in from a single office. Applications aren’t confined to one network. Access isn’t limited to humans. APIs, service accounts, contractors, partners, all of them now act like first-class users. Context changes constantly, sometimes within the same session.
This is where RBAC starts to strain.
Roles are static by design. They don’t understand risk. They don’t know whether a device is compromised, whether a login is happening from a new country, or whether the same role should behave differently at 9 a.m. versus 2 a.m. As a result, teams compensate by creating more roles. Then more exceptions. Then shared admin privileges “just to keep things moving.”
Before long, RBAC hasn’t failed; it has been stretched beyond what it was built to do.
That’s why RBAC still appears in every enterprise architecture diagram. And that’s also why, on its own, it struggles in modern, highly dynamic environments.
What Is Role-Based Access Control
At its core, what is role-based access control really asking?
It’s asking how organizations translate responsibility into access.
RBAC works by grouping permissions into roles and assigning those roles to users. Instead of granting permissions one by one, you say: If you perform this function, you get this set of access. A support agent can read tickets. A finance approver can authorize payments. An admin can manage systems.
Simple. Predictable. Easy to reason about.
That simplicity is exactly why RBAC is still widely used. It gives teams a shared language. It reduces decision fatigue. It allows systems to scale without turning every access request into a debate.
A solid RBAC model example doesn’t try to mirror job titles perfectly. It focuses on actions and resources. What can be read? What can be changed? What requires approval? When roles are built around those questions, RBAC creates clean boundaries that are easy to audit and explain.
Where people get tripped up is expecting RBAC to answer questions it was never designed for. RBAC doesn’t decide when access should be allowed. It doesn’t evaluate how risky a request is. It doesn’t adapt in real time.
RBAC defines the outer limits. It draws the map. It does not choose the route.
Zero Trust Access Management: What Modern Enterprises Actually Mean by It
When enterprises talk about zero trust access management, they’re not talking about distrusting everyone all the time. They’re talking about removing assumptions.
No assumption that someone is safe because they’re “inside.” No assumption that a role is enough.
No assumption that yesterday’s access decision still holds today.
In practice, zero-trust identity and access management treats every access request as a decision point. Identity is verified. Context is evaluated. Policies are applied. Enforcement happens close to the resource applications, APIs, and data, not just at the network edge.
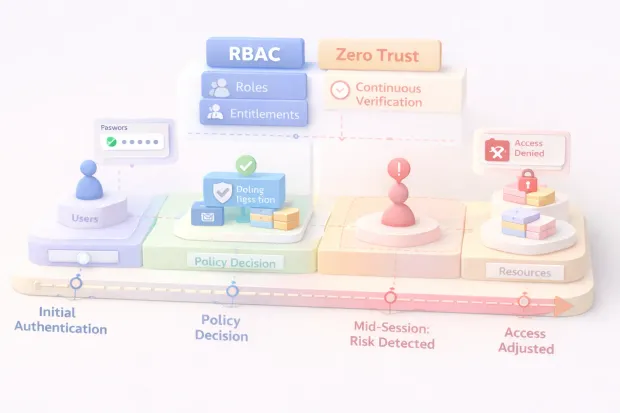
This isn’t a one-time check at login. It’s continuous. If the session changes, the decision can change. If risk increases, access can tighten. If conditions improve, friction can reduce.
Here’s where it gets interesting: Zero Trust doesn’t eliminate structure. It relies on it.
Policies need something stable to evaluate against. That “something” is identity roles, entitlements, and attributes. Without those anchors, Zero Trust becomes guesswork. With them, it becomes precise.
Modern Zero Trust systems aren’t replacing access models. They’re orchestrating them.
Where RBAC Fits Inside Zero Trust
RBAC fits into Zero Trust the way a foundation fits into a building. It doesn’t decide everything but without it, nothing stands.
RBAC defines what actions are ever permissible for a given identity. It establishes entitlement boundaries. A user without a role should never reach a sensitive action, no matter how perfect their context looks. That’s RBAC doing its job.
Zero Trust steps in at runtime. It asks a different set of questions: Should this role be allowed to act right now? From this device? Under this risk level? For this session? This is where adaptive decisions happen. This is where access becomes conditional instead of absolute.
Where RBAC doesn’t belong is decision-making under uncertainty. It can’t handle fluctuating risk. It can’t evaluate device health. It can’t distinguish between a trusted internal session and a compromised one using the same credentials.
That’s not a flaw, it's a boundary.
The most effective enterprises treat RBAC as the entitlement layer and Zero Trust as the judgment layer. RBAC provides stability. Zero Trust provides intelligence. Together, they create RBAC controls that are both understandable and resilient.
When teams try to force RBAC to behave like Zero Trust, they end up with role sprawl and brittle policies. When they ignore RBAC in favor of pure context, policies become opaque and hard to govern.
The balance is deliberate. And when done right, it’s what makes modern access management actually work.
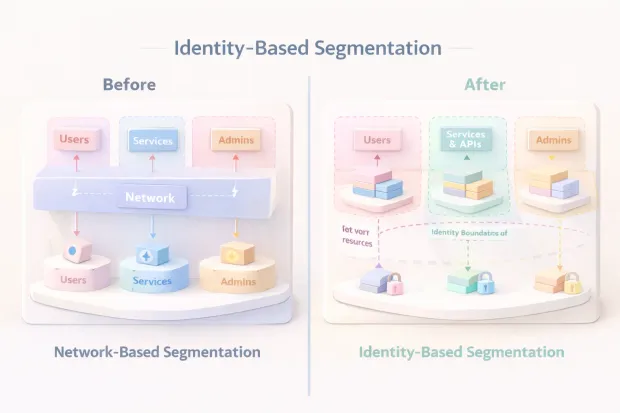
Identity-Based Segmentation: The Missing Bridge Between IAM and Security Posture
For a long time, identity teams and security teams solved adjacent problems without fully meeting in the middle.
IAM focused on who someone is and what they should be allowed to do. Security focused on where access happens and how risky that moment looks.
Identity-based segmentation is what finally connects those two worlds.
Instead of drawing access boundaries around networks or IP ranges, segmentation happens around identity itself. Roles, entitlements, session signals, and risk posture determine what a user or a workload can reach. Not globally. Not permanently. But deliberately.
This shift matters because modern breaches rarely start with a firewall failure. They start with valid credentials being used in the wrong context. Once inside, lateral movement does the real damage.
Identity-based segmentation reduces that blast radius. Even if an identity is compromised, access remains constrained by role, policy, and runtime conditions.
A support role can’t suddenly wander into finance systems. A partner account can’t drift into admin territory. The segmentation lives at the identity layer, not the perimeter.
This is also where Zero Trust becomes operational instead of aspirational. Segmentation stops being a network diagram and becomes an access decision evaluated every time, enforced everywhere.
RBAC Model Example: A Simple Enterprise Scenario
Consider a mid-sized SaaS company. Not hypothetical. This pattern shows up constantly.
They have four core teams: Customer Support, Finance, Engineering, and Security.
Their core systems include: A CRM, a billing platform, a production admin console, and internal analytics.
Instead of mapping access to job titles, they define roles around actions.
Support Viewers can read customer profiles and tickets.
The Support Editor can update tickets but can’t touch billing.
Finance Approver can authorize refunds and access billing reports.
Engineer Deployers can push code but can’t modify user data.
Security Admin can manage policies but doesn’t approve payments.
This RBAC model example works because each role is scoped to a clear responsibility. No role exists “just in case.” No role spans unrelated systems.
Now here’s where teams usually go wrong.
An urgent request comes in. Someone needs temporary access. Instead of granting time-bound permissions, an admin assigns a broader role. Then forgets to remove it. Over time, those exceptions become permanent. RBAC didn’t break. Discipline did.
When RBAC roles are treated as durable entitlements not shortcuts the model stays clean. When they become convenience tools, risk quietly accumulates.
Role-Based Access Control Best Practices for Zero Trust Environments
Role-based access control best practices change once Zero Trust enters the picture.
The first shift is mindset. RBAC stops being the final authority and becomes the entitlement baseline. Roles define what could be allowed, not what must always be allowed.
Strong Zero Trust RBAC starts with permissions, not org charts. What actions exist? What resources matter? Roles are built by grouping those actions logically, not by copying HR titles.
Roles should be small. Composable. Purpose-built. The more a role tries to do, the less trustworthy it becomes. Smaller roles make policy decisions cleaner and easier to audit.
Another best practice that matters more than teams expect: ownership. Every role needs an owner. Someone is accountable for its lifecycle. If no one owns a role, it will grow. Guaranteed.
In Zero Trust environments, RBAC also pairs tightly with step-up controls. Privileged roles don’t grant silent power. They trigger additional verification, shorter sessions, or just-in-time access. RBAC defines eligibility. Zero Trust enforces conditions.
That separation keeps access flexible without becoming reckless.
RBAC Controls That Actually Matter
Not all RBAC controls deliver meaningful security outcomes. Some just create paperwork.
The controls that matter are the ones that expose drift.
Access reviews are a good example. When done well, they don’t ask managers to rubber-stamp permissions. They ask whether access still aligns with responsibility. If a role no longer makes sense, it gets removed. Quietly. Regularly.
Segregation of duties is another control that separates mature RBAC programs from fragile ones. No single role should be able to initiate and approve the same critical action. This isn’t theory. It’s how fraud gets prevented in real systems.
Privileged access controls matter even more. Admin roles should be rare, time-bound, and monitored. Persistent admin access is one of the fastest ways RBAC security erodes without anyone noticing.
Finally, logging closes the loop. RBAC isn’t just about who has access, but who uses it. Enforcement logs, denied actions, and policy decisions reveal where roles are too permissive or where Zero Trust policies are doing real work.
Governance isn’t a separate layer. It’s how RBAC stays honest over time.
How to Implement Zero Trust Identity Management with RBAC
Most Zero Trust diagrams look clean. Real systems don’t.
In practice, Zero Trust identity management with RBAC works when responsibilities are clearly split across layers and when no single layer tries to do everything.
RBAC sits at the entitlement layer. It answers a narrow but critical question: What actions should this identity ever be eligible to perform? Those entitlements are static by design. They don’t change with location, device, or time. That stability is what makes RBAC reliable.
Zero Trust begins the moment an access request happens.
A user or a workload authenticates. A session is created. At that point, identity is no longer just a username with roles attached. It becomes a decision object. Device posture, login behavior, network signals, risk indicators, and policy rules all come into play. A policy decision engine evaluates whether access should be granted for this request, not in general.
Enforcement happens as close to the resource as possible. APIs, applications, admin consoles each becomes an enforcement point. RBAC defines what’s even on the table. Zero Trust decides whether the table is open right now.
The most important architectural detail teams miss is sequencing. RBAC must be evaluated before dynamic policy logic. Otherwise, policies grow complex trying to compensate for unclear entitlements. When RBAC is clean, Zero Trust policies stay readable and predictable.
This isn’t about adding more tools. It’s about making sure each layer does its job and stops there.
Common Failure Patterns (and Quick Fixes)
Here’s where teams usually go wrong and why it keeps happening.
The first failure pattern is role explosion. Every exception becomes a new role. Over time, no one understands what roles actually represent. The fix isn’t deleting roles blindly. It’s tightening role design around actions and resources, then moving conditional logic into Zero Trust policies where it belongs.
Another common issue is treating RBAC as a real-time decision engine. Teams try to encode context location, device, and urgency into roles. That always backfires. Roles should remain boring. Context belongs to policy evaluation.
Then there’s the “temporary access that never expires” problem. It shows up everywhere. Admin roles granted during incidents quietly become permanent. The fix is procedural, not technical: time-bound access, ownership, and regular reviews.
A quieter but more dangerous failure pattern is identity blind spots. Service accounts, integrations, and APIs get powerful roles without the same scrutiny as human users. Zero Trust doesn’t work if non-human identities bypass controls. They need the same RBAC discipline and runtime evaluation.
And finally, teams underestimate governance. If no one owns roles, reviews get skipped. If logs aren’t reviewed, misuse goes unnoticed. Zero Trust amplifies whatever RBAC foundation exists, good or bad.
Practical Checklist
You don’t need a full transformation to make progress. Thirty days is enough to uncover real risk.
Start with roles. Can every role be explained in one sentence? Does each role map to a clear responsibility and resource set? If not, it’s already drifting.
Review privilege. Identify all admin and high-impact roles. Check how many users have them—and for how long. Persistent privileged access should be rare.
Look at segmentation. Verify that roles don’t automatically grant access across unrelated systems. Identity-based segmentation should be visible in how access is enforced, not just in documentation.
Evaluate runtime decisions. Confirm that high-risk logins trigger different outcomes than low-risk ones. If every successful login behaves the same, Zero Trust isn’t actually in effect.
Audit governance. Are access reviews happening? Are role owners accountable? Are denied actions logged and examined, or ignored?
Finally, examine non-human identities. List service accounts and integrations. Check their roles. These accounts often hold more power than they should—and attract the least attention.
If these checks feel uncomfortable, that’s a good sign. It means the system is finally being examined the way attackers already do.
Conclusion
RBAC was never meant to make decisions in isolation.
It defines what should be possible.
Zero Trust decides what should be allowed right now.
That distinction matters more than ever.
In modern environments, access control fails not because roles are missing, but because context is ignored. A user with the right role can still be the wrong user on the wrong device, in the wrong location, at the wrong time. RBAC controls can’t see that. Zero Trust can.
When RBAC is used correctly, it becomes the entitlement backbone. Clear permissions. Clean boundaries. Predictable access patterns. When zero trust access management is layered on top, identity becomes dynamic, continuously evaluated, segmented, and enforced at runtime.
This is where identity-based segmentation changes the game. Access stops being tied to networks or assumptions and starts being tied to identity, session, and risk. Lateral movement shrinks. Overexposure drops. Security teams regain control without slowing the business.
But here’s the part teams often underestimate: Zero Trust doesn’t fix sloppy RBAC. It amplifies it. If roles are bloated, Zero Trust policies become noisy. If ownership is unclear, enforcement turns inconsistent. Strong Zero Trust outcomes depend on disciplined RBAC foundations.
The enterprises getting this right don’t ask whether RBAC is obsolete. They ask how to make RBAC work with Zero Trust, how to align structure with judgment, entitlement with verification.
RBAC still remains. Zero Trust decides when to trust it.
And in a world where identity is the new perimeter, that balance is what keeps access secure without breaking how people actually work.
FAQs
Q: Is RBAC enough for Zero Trust security?
A: RBAC alone isn’t enough because it defines static permissions. Zero Trust access management adds context device, risk, session behavior to decide whether access should be allowed at that moment.
Q: What is RBAC in security, and why is it still used?
A: RBAC in security assigns permissions based on roles tied to responsibilities. It’s still widely used because it provides clarity, auditability, and predictable access boundaries across large organizations.
Q: How does identity-based segmentation improve Zero Trust?
A: Identity-based segmentation limits access based on identity and role rather than network location. Even if credentials are compromised, lateral movement stays restricted to approved identity boundaries.
Q: How do RBAC controls support Zero Trust identity management?
A: RBAC controls define which actions are ever possible, while Zero Trust identity management evaluates when and under what conditions those actions are allowed, using continuous verification.


