Introduction: Janrain Inc. is Shutting Down. Here’s What You Need to Know
If you're currently using Janrain inc, now known as Akamai Identity Cloud, you’ve likely heard the news: the platform is being sunset. Akamai has formally announced the end-of-life (EOL) for Janrain’s CIAM services by December 31, 2027, with key functionality like social login set to shut down as early as 2026.
For businesses relying on Janrain to manage customer identities, this signals more than just the end of a contract-it’s the start of a critical migration journey. And while transitions like this can feel overwhelming, they also present a rare opportunity.
This is your chance to migrate to a modern customer identity and access management platform that not only replaces Janrain’s core functionality, but goes further-with better scalability, uptime, security, and developer experience.
At LoginRadius, we’re here to help you turn this forced shift into a strategic advantage. In this guide, we’ll walk you through the shutdown timeline, what it means for your business, your migration options, and why LoginRadius is the most future-ready and reliable Janrain alternative available today.
Janrain (Akamai Identitdy Cloud) End-of-Life Timeline: Key Dates and What to Expect
Akamai has officially initiated the sunset of Janrain, the CIAM platform it acquired in 2019 and rebranded as Akamai Identity Cloud. If your organization is still using Janrain CIAM, it’s important to understand the end-of-life timeline and what each milestone means for your authentication infrastructure and compliance needs.
Here’s a breakdown of the key dates:
-
March 7, 2024 – End of Sales : Akamai stopped accepting new sales for Identity Cloud. This marked the beginning of the platform’s phase-out across all Janrain services.
-
October 31, 2024 – End-of-Life Announcement : Akamai formally announced the retirement of the Identity Cloud product line, affecting all existing customers and CIAM implementations.
-
March 31, 2026 – Social Login (Janrain Engage) Shutdown : One of Janrain’s core offerings, its social login capability will be decommissioned. Businesses relying on Janrain Engage will need to switch to a new provider before this date to avoid login disruptions.
-
December 31, 2027 – Full Platform Shutdown : All remaining Akamai Janrain services will be permanently discontinued. This includes core Janrain authentication, user management, APIs, login flows, and administrative tools.
What Happens After the Shut Down?
After December 2027, there will be no platform access, no API support, and no guarantee of security updates. Continuing to use Janrain identity management tools beyond that point introduces risks like broken login flows, compliance issues, and service interruptions.
That’s why it’s important you start planning your Janrain alternative migration now, while you still have the time and flexibility to make a smooth transition.
What Janrain’s Shutdown Means for Your Business
As Janrain heads toward full sunset under Akamai’s roadmap, the implications go far beyond vendor change. If your product or app is still built on Janrain CIAM, the impact will ripple through your customer login flows, developer maintenance cycles, and long-term compliance strategy.
Here are the risks associated in detail:
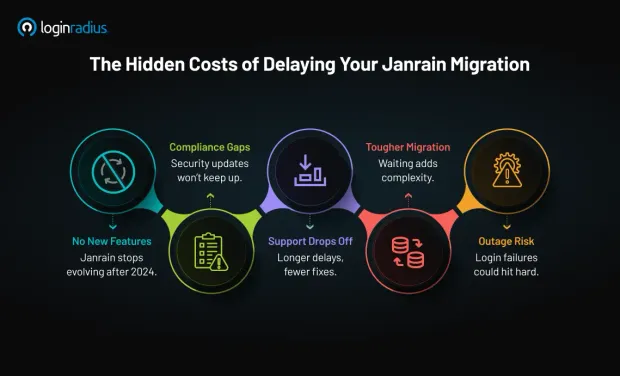
1. No new features or product innovation
Akamai has confirmed that no new features will be added after 2024, even as the platform remains operational until 2027. That means you'll miss out on important industry trends in identity, such as passwordless authentication, advanced orchestration, and next-gen compliance tools. Sticking with Janrain CIAM past this point means your identity stack stays static while competitors move forward.
2. Security and compliance will gradually fall out of sync
After 2024, Janrain inc will receive only maintenance-level updates. While that includes critical patches, any emerging identity requirements (like evolving interpretations of GDPR, CCPA, or newer regional privacy laws) may not be addressed. This leaves your security posture and audit readiness in a progressively fragile state.
For developers and IT teams, this means more time spent creating stopgap solutions for a system that’s no longer keeping up.
3. Declining support and vendor engagement
While Akamai Identity Cloud is technically supported through 2027, it’s increasingly a legacy product. As engineering resources shift internally, you’re likely to face longer support delays, fewer updates, and reduced access to knowledgeable specialists. This puts more pressure on internal teams to diagnose and fix identity issues on their own.
For developers, this can result in increased technical debt, urgent patches, and integration duct-tape that burns time and increases risk.
4. Technical debt and migration urgency
Migration projects are never plug-and-play. They require careful planning, technical lift, and cross-team coordination. The longer you don’t find a Janrain alternative, the more custom SDKs, workarounds, and workflows like consent and profile sync may start breaking over time without updates.
The longer you wait, the more complex the migration becomes. A project that could take weeks today might take months in 2026.
5. Platform instability and risk to user trust
Past incidents have shown that outages can and do happen. If login fails during peak usage, your users won’t care why—it’s a bad experience that affects engagement and trust.
Once Janrain support fully stops, even minor issues could lead to full authentication failure. For mission-critical systems, that’s not a risk most businesses can take.
What It Adds Up To
Choosing not to look for Janrain alternatives means accepting rising risk, added pressure on your dev teams, and declining reliability. Eventually, you’ll have to make the move. But acting early gives you control. You get time to evaluate the right partner, avoid last-minute chaos, and set your identity infrastructure up for the next decade—not just the next deadline.
Up next, we’ll look at your Janrain migration options, and how LoginRadius is helping your fellow businesses transition to a modern identity platform before the EOL clock runs out.
What Are Your Janrain Alternatives?
Fortunately, you do have options. Let’s take a look at them.
Many Janrain customers are using this moment as a fresh start—re-evaluating Janrain alternatives with a focus on modernization, extensibility, and developer-friendliness. Several vendors are stepping up to capture this opportunity, including:
| Janrain Alternatives | Strengths | Considerations |
|---|---|---|
| LoginRadius | Developer-first CIAM, 100% uptime, flexible APIs, fast to launch | Deep migration support, self-serve model, transparent pricing, global readiness |
| Okta/Auth0 | Strong developer tools, integrations, and global presence | Pricing can escalate; post-acquisition changes in roadmap |
| ForgeRock | Enterprise-grade identity suite with IAM/CIAM convergence | Heavy platform; often suited to complex, high-touch projects |
| Microsoft Entra ID B2C | Deep integration with Azure ecosystem, granular user flows and MFA support | High customization may require specialized Azure knowledge; pricing model tied to Azure usage |
| Descope | No-code passwordless-first workflows, fast time-to-market | Newer provider; may not offer the same breadth of enterprise features or compliance standards |
Why this moment is a strategic opportunity
Whether you choose LoginRadius, or other Janrain competitors, this transition is a chance to re-architect your customer identity strategy for the future.
That means:
-
Moving to standards-based identity (OAuth 2.0, OIDC, WebAuthn)
-
Adopting passwordless and passkey-ready workflows
-
Designing scalable, multi-tenant systems if you serve partners or B2B use cases
-
Ensuring zero-downtime migrations and seamless UX for users
Janrain Identity Cloud Complaints: What Users Are Saying
Over the past years, the LoginRadius team has spoken with numerous organizations navigating away from Janrain Identity Cloud—and a clear pattern has emerged. Whether due to product stagnation, rising costs, or poor support after the Akamai acquisition, many teams were actively seeking Janrain alternatives that align with modern identity needs.
Here are the most common pain points driving that decision:
“We lost the freedom to use our existing stack.”
This is a direct feedback from a brand that previously relied on Janrain—and others’ feedback also followed this like a clear pattern. After Akamai acquired Janrain, many customers began experiencing reduced flexibility, limited roadmap visibility, and slower response times.
One of the most pressing concerns was around service-level agreements (SLAs) and stack compatibility. Some companies shared that once the platform was absorbed into Akamai’s broader ecosystem, retaining access to full support and optimal features often meant conforming to Akamai’s preferred tools and architecture. Custom setups or non-Akamai components were no longer treated as first-class citizens.
This reminded several teams of what happened during the SAP acquisition of Gigya where businesses were subtly pushed toward SAP’s stack to maintain service levels they previously had by default. And with Janrain, that pattern appeared to be repeating. Companies found themselves having to choose between losing SLA coverage or restructuring parts of their tech stack, an expensive and resource-draining decision, especially for large enterprises.
These concerns are part of why many teams have since begun actively evaluating Janrain alternatives that won’t compromise their architectural independence or force long-term vendor lock-in.
“We noticed a decline in support.”
Following Akamai’s acquisition of Janrain, many teams reported a noticeable drop in technical responsiveness and customer service quality. It’s a common risk during major product transitions: resources shift, priorities change, and long-standing support structures often take a hit.
Several organizations told our consultants that what once felt like a partnership began to feel like an afterthought. For companies running identity at scale, that kind of support gap wasn’t just frustrating, it was untenable. It became one of the top reasons they began evaluating Janrain alternatives that offer both platform reliability and high-touch guidance.
“What happened to auto-renew?”
Previously, renewals were often seamless—but post-acquisition, many found that their contracts no longer auto-renewed as expected. Instead, Akamai began exercising its right to renegotiate terms, prompting surprise and uncertainty among long-standing customers. For some, this introduced unexpected legal reviews, pricing shifts, and changes in SLA language.
The result? A growing wariness around the fine print and a broader feeling that control was slipping away. It’s another reason businesses began actively exploring Janrain alternatives that offer clearer terms, transparent pricing, and continuity without renegotiation anxiety.
“We can’t afford any outages.”
Several customers reported increased downtime after the Akamai acquisition, with some pointing to high-profile outages during peak events. One example often cited is the NBA Finals game outage on Sportsnet, which drew public backlash. Since Janrain was Rogers’ CIAM provider at the time, the disruption highlighted a critical weakness: inability to handle authentication spikes at scale.
According to industry averages, even a short CIAM failure can cost upwards of $300,000 in lost revenue. For many teams, this was the tipping point. The risk of outages, especially under pressure, has accelerated the search for more resilient Janrain alternatives with proven uptime, elastic scaling, and real-world performance under load.
Up next, we’ll show you why LoginRadius is the best Janrain alternative, especially if you're looking for an identity platform that blends power, simplicity, and enterprise support.
Why LoginRadius is the Best Janrain Alternative
Akamai is a security company, so its acquisition of Janrain confirmed that CIAM is a security platform. Akamai clearly saw Janrain as a missing piece in their security company.
However, LoginRadius made this pivot sooner than Janrain—in 2016, to be precise. Simply put, we've spent more years innovating and delivering value to enterprises than Janrain has. Here are just some of the reasons why LoginRadius is the best Janrain alternative for your business.
1. LoginRadius is feature-complete and continuously evolving
Janrain covered the basics of CIAM: user registration, social login, SSO, and profile management. But with feature development frozen and an end-of-life deadline looming, businesses still relying on Janrain are stuck with outdated workflows, limited extensibility, and no support for modern authentication standards.
LoginRadius delivers all of Janrain’s core functionality and significantly extends it with a platform that’s actively developed and aligned with today’s identity and privacy demands.
Here’s what that means:
-
Comprehensive CIAM coverage : All standard identity operations are supported out of the box—email/password registration, customizable login forms, progressive profiling, multi-language support, and session management.
-
Authentication beyond passwords : LoginRadius supports passwordless login options including OTP, magic links, and passkeys via FIDO2/WebAuthn, allowing your product to phase out passwords entirely while boosting both usability and security.
-
Risk-adaptive MFA : Instead of forcing MFA for every session, LoginRadius enables adaptive MFA based on geolocation, device recognition, and behavior analytics, striking the right balance between user experience and security.
-
Drag-and-drop identity orchestration : Janrain lacked orchestration tooling. With LoginRadius, product and security teams can visually configure complex authentication, registration, and recovery flows without writing backend logic, ideal for agile iteration and business-specific journeys.
-
Partner IAM and Multi-Tenant Access : Unlike Janrain, which focused primarily on consumer identity, LoginRadius offers built-in support for B2B use cases. You can model multiple organizations under your account, apply tenant-specific branding, provision roles, and federate access via SAML or OIDC without building that architecture from scratch.
-
Data privacy built in : LoginRadius as a Janrain alternative includes granular consent management, audit trails, and tools to comply with GDPR, CCPA, and region-specific privacy requirements without relying on third-party add-ons.
-
Actively updated SDKs and APIs : The platform ships regular SDK improvements for JavaScript, Node.js, Python, React, and mobile platforms. All APIs are RESTful, OpenAPI documented, and backward-compatible, ensuring developers stay productive as identity needs evolve.
2. 100% Uptime and proven scalability
For any identity platform, reliability isn’t optional. Janrain customers have experienced service outages in the past, especially during high-traffic events, putting user logins and digital experiences at risk. As the platform winds down, that risk only grows.
LoginRadius eliminates this concern with a proven track record of 100% uptime, backed by a globally distributed infrastructure built for real-world scale.
Here’s how:
-
Distributed, multi-cloud architecture : This Janrain alternative runs across multiple cloud providers and global regions, with automatic failover and load balancing to ensure service continuity even during outages in a specific zone.
-
Auto-scaling under peak load : Whether you’re handling 1,000 or 10 million logins per hour, the platform automatically scales to match usage with no pre-provisioning, manual interventions, or no login slowdowns.
-
Performance-first design : Authentication latency is minimized through edge caching, regional data replication, and CDN integration. LoginRadius routes traffic through the nearest data center, ensuring low-latency response times regardless of user location.
-
No maintenance windows : Unlike traditional platforms that require downtime for updates or patches, LoginRadius performs hot deployments and rolling updates. Your identity system stays online, always.
-
Real-time monitoring and incident response : Internal health checks, third-party uptime monitoring, and alerting mechanisms ensure proactive issue resolution. Uptime SLAs are backed by 24/7 operations teams and are supported by enterprise-grade guarantees.
3. Seamless migration with no password resets
One of the biggest concerns in any identity migration is user disruption, especially around passwords. Janrain’s end-of-life announcement offers no direct tools for preserving credentials or executing a phased transition, often leaving developers facing a hard choice: force password resets or rebuild identity from scratch.
That’s where LoginRadius sets itself apart from other Janrain alternatives. It removes that burden entirely. Our migration framework is built to preserve credential integrity, maintain user experience, and give your developers full control over timing and execution.
Whether you prefer to migrate everything at once or roll it out gradually, LoginRadius supports two enterprise-grade migration options:
-
Bulk Migration – A one-time transfer of your full user base, handled securely by the LoginRadius implementation team.
-
Just-in-Time (JIT) Migration – Users are silently migrated when they next authenticate. Ideal for cleaning inactive records, reducing backend load, and avoiding UX friction.
In both options, password hashes are retained (including bcrypt, scrypt, and SHA variants), so users never need to reset credentials or re-register. This allows you to preserve login continuity—even during backend transitions.
Migration tools built for developers
LoginRadius, unlike other Janrain competitors, gives your engineering team full control over how and when to migrate without disrupting your users.
| Capability | Description |
|---|---|
| Just-in-Time (JIT) Migration | Seamlessly migrates users as they authenticate. No password resets needed. |
| Bulk Migration | One-time full data migration managed by LoginRadius experts. |
| Janrain API Integration | Connects directly to Janrain’s Entity & Entity Type APIs for smooth data flow. |
| Field Mapping Engine | 1:1 field mapping across platforms for full schema compatibility. |
| Password Hash Support | Supports bcrypt and other common hash algorithms. |
| Orchestration Engine | Low-code workflow builder for flexible migration phases. |
| API-Based Migration | Full developer control using RESTful endpoints. |
| Secure Transfer Options | SFTP, token-based auth, and encrypted channels supported. |
For teams that want precision and customization, the entire migration process can be scripted via RESTful APIs—or designed visually using our Identity Orchestration Engine. Direct Janrain API integration accelerates data extraction and mapping, ensuring you retain structure and metadata during the switch.
Unlike many Janrain alternatives, LoginRadius also supports intelligent filtering through JIT migration—allowing you to bring over only active users. That means you can treat this transition not just as a lift-and-shift, but as an opportunity to clean up your identity store, optimize performance, and sunset legacy records gracefully.
4. Transparent pricing and better ROI
One of the challenges many Janrain customers faced especially after the Akamai acquisition was unclear pricing tied to opaque enterprise contracts. Add-on charges for features like social login, MFA, or advanced analytics made total cost of ownership unpredictable. And now, migrating to PingOne or other large providers often means trading one complex pricing model for another.
LoginRadius takes a fundamentally different approach to other Janrain competitors. Our pricing is built around transparency, predictability, and value, especially for businesses looking to scale without surprise costs.
Straightforward MAU-based billing
LoginRadius charges based on Monthly Active Users (MAUs) not storage, API calls, or rate-limited tiers. Whether your users log in once or twenty times a day, your cost remains consistent and easy to forecast.
No add-on charges for core features
Features like:
-
Traditional login (password and username)
-
Social login integrations (Google, Facebook, Apple, etc.)
-
Passwordless login with magic link, SMS /Email OTP
-
Passkeys
-
Standard Account Security
-
Hosted login pages
...are all included in their free plan. You don’t need to worry about paying extra for what’s considered baseline CIAM functionality today.
Measurable ROI compared to legacy vendors
In contrast to Okta, ForgeRock, or PingOne, businesses typically see a 30–50% reduction in total cost of ownership (TCO). This stems from:
-
A comprehensive feature set included out of the box
-
Faster development using out-of-the-box SDKs and tooling
-
Lower support and maintenance overhead due to platform reliability
Flexible plans at every stage
-
Free Forever tier includes up to 25,000 MAUs and standard CIAM features like passkeys, social login, and OTPs—no credit card required.
-
Professional tier starts at affordable fixed monthly rates, with enhanced SLA, uptime guarantees, and support.
-
Enterpris plans include single-tenant or private-cloud options, custom SLAs, and any specialized features you need.
Costs aligned with developer productivity
Transparent pricing keeps dev teams focused on building, not justifying spikes in usage. With built-in orchestration, migration tools, and experts available, build cycles are faster—reducing time-to-launch and associated costs.
Compared to other Janrain alternatives, LoginRadius offers industry-leading CIAM capabilities without enterprise bloat, making it a smart choice for migrating, especially for teams sensitive to TCO and loving modular, flexible platforms.
5. Integration with your existing stack and white‑glove support from identity experts
We understand that migrating your identity platform is a high-stakes project that requires guidance, expertise, and ongoing support. Janrain’s end-of-life arguably eroded once-great customer support. Many teams found themselves troubleshooting alone as the product wound down. That’s a risk no business should take again.
When it comes to integration, we meet you where you are:
-
Out-of-the-box SDKs and RESTful APIs support seamless integration with modern frameworks like React, Node.js, Angular, Python, and more.
-
Support for custom workflows and legacy infrastructure means you don’t have to rebuild what already works.
-
Direct integration with your user store, consent systems, marketing platforms, and data lakes ensures continuity across your identity architecture.
-
SAML, OIDC, and SCIM compatibility means federated identity and provisioning flows slot in cleanly alongside your current stack.
Whether you're a digital-native startup or an enterprise with deeply embedded systems, LoginRadius adapts to your ecosystem—not the other way around.
LoginRadius also offers dedicated identity experts who stand by you from migration through expansion. Learn more about LoginRadius Professional Services.
-
24/7 Global Support : Our support team is available 24/7, 365 days a year backed by service level agreements ensuring urgent issues are handled immediately.
-
Dedicated Customer Success & Solution Architects : Each enterprise account receives a Customer Success Manager (CSM) and Solutions Architect, who guide the migration, help optimize performance, and plan long-term identity strategies. Unlike many Janrain alternatives, all of our CSMs have deep technical backgrounds, ensuring your questions never go to a generic ticket queue.
-
Expert-Led Onboarding and Migration Workshops : Rather than unpacking migration tools yourself, your team will work alongside LoginRadius experts during onboarding, i.e., plan migrations, design orchestration flows, and validate API integration in hands-on sessions.
-
Proactive Monitoring and SLAs : We don’t just react to incidents; our platform is monitored continuously. LoginRadius offers SLA-backed uptime, incident notifications, and dedicated escalation paths to ensure any issue is resolved before your users even notice.
-
Developer-Focused Resources and Community : Access in-console help, RESTful API documentation, SDK examples, GitHub repos, and community forums. Developers can quickly find code samples for OAuth2, WebAuthn, social login, and more, all without raising a support ticket.
LoginRadius: A Platform Built for Longevity, Innovation, and Customer Trust
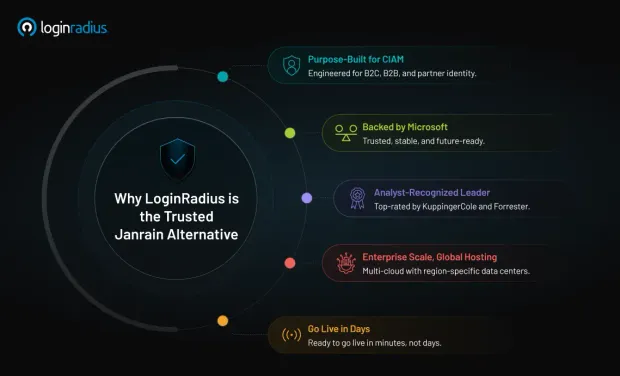
With Akamai Janrain inc shutting down, many businesses are understandably cautious about their CIAM provider stability. LoginRadius was built to address that very concern. From day one, LoginRadius has been engineered for longevity, innovation, and customer trust.
Here’s more on why LoginRadius can be your best Janrain alternative option:
-
Backed by Microsoft Ventures : LoginRadius is venture-backed by Microsoft’s accelerator fund, adding credibility, long-term stability, and access to trusted infrastructure partnerships.
-
Recognized by industry analysts : Consistently named a CIAM Leader in KuppingerCole, and Forrester’s industry evaluations, LoginRadius stands shoulder-to-shoulder with Okta, ForgeRock, and other global players, while remaining more nimble and developer-first.
-
Modern Architecture Built for Change : Unlike legacy IAM solutions that were retrofitted for CIAM, LoginRadius was purpose-built for consumer and B2B identities from day one. It supports:
- Hosted login options
- Multi-tenant B2B architecture
- Passkeys, WebAuthn, and orchestration out of the box
- Multi-region hosting, including Canada, EU, and APAC
-
Committed Roadmap and Rapid Innovation : Features like Partner IAM, passkey support, and risk-based authentication were released in direct response to developer needs and privacy regulations.
-
Designed for Scale Across Use Cases : Whether you're a startup scaling to 100K users or a global brand with 100M+ accounts, LoginRadius handles it. Unlike many Janrain alternatives, our platform is engineered from the ground up for scale—featuring multi-cloud deployment, horizontal scaling, and high concurrency support that goes live in minutes, not days.
Janrain vs. LoginRadius: Before and After Migration
| Category | Before Migration w/ Janrain (Akamai Identity Cloud) | After Migration w/ LoginRadius |
|---|---|---|
| Platform Status | End-of-life, no updates | Active roadmap, full support |
| Authentication | Legacy login flows, limited MFA | Passwordless, passkeys, adaptive MFA, orchestration |
| Uptime & Reliability | Historical outages reported | 100% uptime across all environments |
| Migration Tools | No native tooling | JIT + Bulk migration, orchestration engine, full API support |
| Password Handling | Re-authentication often required | Password hashes preserved (e.g., bcrypt) |
| Data Integration | Manual field mapping | Field mapping engine, Janrain API integration, SFTP support |
| Support | Basic support tapering over time | 24/7 expert-led support and onboarding |
| Compliance | GDPR/CCPA supported but stagnant | Actively maintained certifications, regional hosting options |
| Developer Experience | Outdated SDKs and limited extensibility | GitHub SDKs, public API docs, low-code workflows |
| Pricing | Enterprise-focused, opaque | Transparent MAU-based pricing, no add-ons for essential features |
With LoginRadius, you’re not just migrating from a legacy platform—you’re joining an identity ecosystem that’s modern, responsive, and built to evolve with your product roadmap.
Planning Your Move to Janrain Alternatives? Here’s How to Do It Right
With Janrain CIAM shutting down, many businesses are facing urgent decisions about moving millions of user accounts, logins, and integrations without disrupting their services. This is where LoginRadius steps in, not just as a Janrain alternative, but as a migration partner that provides purpose-built tools, and expert support designed to make this transition seamless.
Step 1: Assess your Janrain usage
Start by documenting what you’re currently using:
-
Identity schemas (fields, formats, custom attributes)
-
Authentication flows (social logins, password policies, MFA)
-
APIs, webhooks, and third-party integrations
-
Consent and privacy management configurations
This gives you a clear picture of what needs to be replicated or improved in your new system.
Step 2: Choose a migration strategy
Depending on your infrastructure, team bandwidth, and risk tolerance, LoginRadius supports two main migration approaches:
| Strategy | Best For | Pros | LoginRadius Tools |
|---|---|---|---|
| Bulk Migration | Organizations needing to migrate all user data at once | Fast switchover, suitable for low-traffic or staged environments | SFTP import, field mapping, password hash support |
| Just-in-Time (JIT) | Large-scale systems aiming to migrate users gradually | No downtime, only active users migrate, seamless for end-users | LoginRadius Auth Callback APIs, migration hooks |
Step 3: Map your data and integrate
-
Field Mapping : Use LoginRadius' flexible schema mapping to align Janrain’s user model with LoginRadius’ entity structure. Custom fields are fully supported.
-
Password Retention : LoginRadius supports import of hashed passwords using bcrypt, SHA256, SHA512, and others—eliminating the need for forced resets.
-
Migration APIs : Whether importing via batch (bulk) or triggering on login (JIT), you’ll have RESTful API endpoints to control every step.
Step 4: Leverage expert-led migration support
Every migration project gets direct guidance from:
-
A Customer Success Manager to drive progress and coordination
-
A Solutions Architect to assist with schema design, migration tooling, and go-live cutover
-
24/7 Technical Support for real-time issue resolution
Our identity experts have led hundreds of successful migrations from Janrain, Auth0, Okta, and even homegrown IAM systems ensuring you get a low-risk, high-visibility transition tailored to your infrastructure.
If you're comparing Janrain alternatives, LoginRadius doesn’t just check the feature boxes—it gets you migrated faster, with less disruption and full transparency along the way.
Conclusion: The Janrain Sunset is Coming—But It’s Also a New Beginning
Janrain’s end-of-life isn’t just a technical deadline, it’s a pivotal moment to rethink what your identity platform should deliver. And switching to another legacy solution with a new logo won’t fix the limitations you’ve already outgrown.
If you’re actively exploring Janrain alternatives, LoginRadius is a customer identity and access management platform built for today’s real-world demands. From passwordless login and passkeys to 100% uptime, low-code orchestration, and seamless migration paths—LoginRadius gives you all the tools to move forward without compromise.
Janrain is shutting down. Your user experience doesn’t have to.
Ready when you are. Let's make the switch seamless.
FAQs
1. When is Janrain shutting down?
A. Janrain (now Akamai Identity Cloud) will be fully shut down on December 31, 2027. Akamai officially announced the end-of-life (EOL) timeline on October 31, 2024, with a phased feature sunset beginning March 2026—including the shutdown of Janrain Engage (social login).
2. What is the best Janrain alternative?
A. The best Janrain alternative is LoginRadius, a modern CIAM platform offering feature parity, passwordless login, passkey support, and robust migration tools.
3. Can I migrate from Janrain without resetting passwords?
A. Yes, you can migrate from Janrain without forcing users to reset their passwords. LoginRadius supports importing existing hashed passwords (e.g., bcrypt, SHA-256, SHA-512), preserving user credentials during both bulk and just-in-time (JIT) migrations.
4. Will users face downtime during the Janrain migration?
A. No, your users won't face downtime if you choose LoginRadius' JIT migration method. Users are seamlessly migrated the next time they log in, without disruptions or password resets.
5. What happens to old user records after I switch CIAM?
A. During Just-in-Time (JIT) migration, your system imports only active users helping clean up inactive or redundant accounts.
6. Will consent, profile data, and custom fields map over correctly?
A. Yes, LoginRadius provides comprehensive field mapping tools and supports migration of user metadata, consent logs, and custom attributes.
7. What happens if I wait until close to the 2027 deadline?
A. Waiting increases risk. Akamai Janrain support may slow down, and integrations may break due to changing standards.