Key Takeaways / Introduction Summary
Biometric authentication is transforming digital identity by replacing passwords with who we are — our fingerprints, facial patterns, and behavioral traits.
In this blog, you’ll learn:
-
What biometric authentication is and how it works.
-
The key biometric methods and when to use them.
-
How biometrics enhance security and user experience.
-
How LoginRadius helps developers and businesses enable secure, passwordless, and privacy-first authentication.
By the end, you’ll know how to make biometric authentication a core strength of your digital identity strategy.
If you think about every digital experience you’ve had today—from unlocking your phone to signing in to an app—chances are at least one of them involved biometrics. Fingerprint sensors, Face ID, and voice unlock are now common. Yet behind that simplicity lies a sophisticated process of encryption, template matching, and risk mitigation.
Passwords once seemed secure enough, but breaches and credential stuffing have made them a liability. Users forget them, reuse them, and abandon sign-ups when the process feels tedious. The industry is moving toward passwordless authentication, and biometric authentication is the most intuitive path forward.
What Is Biometric Authentication?
Biometric authentication verifies a user’s identity using unique physical or behavioral traits—such as fingerprints, facial recognition, iris patterns, or typing behavior—instead of traditional passwords. It offers stronger security, reduces friction, and enables fast, passwordless login across devices.
At its core, biometric authentication is the science of identifying and verifying a person through their unique biological or behavioral characteristics. These traits—fingerprints, facial geometry, voice timbre, iris structure, or even typing rhythm—are distinctive enough to serve as personal keys.
Unlike passwords that depend on memory, biometric authentication relies on something immutable: you. Because biological features are hard to replicate, biometric security drastically lowers the chance of credential theft or phishing.
In essence, biometric authentication merges security and experience—two goals that were once at odds.
How Biometric Authentication Works
Biometric authentication works by capturing a user’s physical or behavioral trait, converting it into an encrypted template stored securely on the device, and comparing it against a new sample during login. If the match meets a required threshold—and passes liveness checks—the system grants access instantly without using passwords.
Behind every instant biometric login is a multi-layered workflow that blends hardware, encryption, and behavioral analytics.
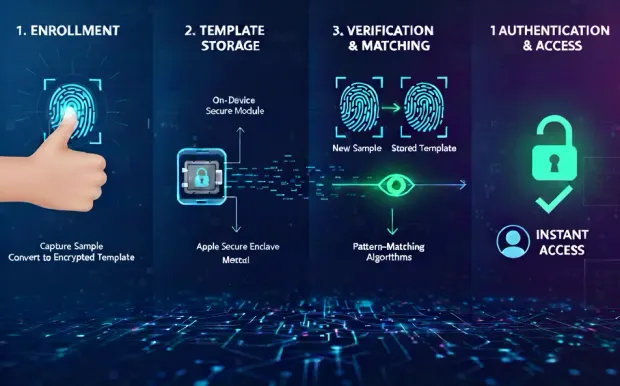
1. Enrollment
Enrollment begins when a user allows an app or device to capture a biometric sample—say, a fingerprint or face scan. Rather than storing the raw image, the system converts it into a biometric template, a mathematical representation of unique markers.
Developers integrating LoginRadius can embed this step using the Passwordless or WebAuthn APIs, ensuring templates never leave the user’s secure hardware enclave.
2. Template Storage
Security best practice dictates that biometric templates remain on-device—inside secure modules like Apple’s Secure Enclave or Android’s Keystore.
This approach aligns with privacy-by-design principles and data-protection laws. Central servers store only cryptographic references, not the biometric data itself.
3. Verification and Matching
During login, the sensor captures a new sample and compares it with the stored template using pattern-matching algorithms.
If the match score surpasses a defined threshold, authentication succeeds. Many systems add liveness detection—checking for blink, movement, or temperature—to prevent spoofing with photos or replicas.
4. Authentication & Access
Once verified, the user gains access instantly. For developers, this means reduced friction and fewer failed logins. For businesses, it means happier users and stronger security metrics.
Biometric workflows integrate smoothly with LoginRadius CIAM, enabling passwordless experiences without storing or processing raw biometric data centrally.
Types of Biometric Authentication
Biometric authentication falls into two main categories: physical biometrics (what you are) such as fingerprints, facial recognition, iris scans, and voice patterns; and behavioral biometrics (what you do) like typing rhythm, swipe gestures, and device movement.
Some systems also combine both to create hybrid or multi-modal authentication for stronger security and a smoother user experience. Let’s break them down.
1. Physical (Physiological) Biometrics
Physical biometrics are based on the parts of you that don’t really change — your fingerprints, face, eyes, or voice. They’re the backbone of most biometric systems today.
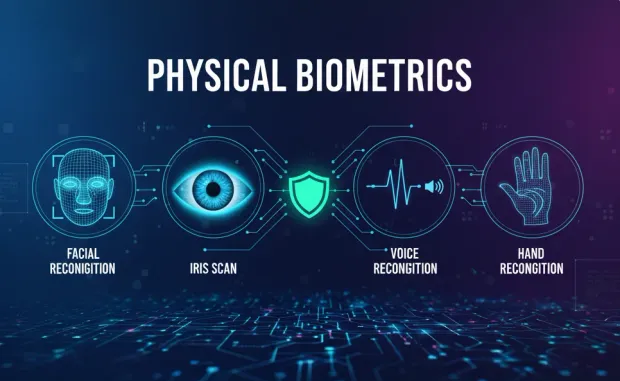
Fingerprint Recognition
You’ve probably used this one already — maybe when logging into your banking app or unlocking your phone with a quick tap.
The scanner reads your unique ridge patterns and matches them against an encrypted version stored safely on your device.
For developers, integrating this is a breeze using native frameworks like Android’s BiometricPrompt or iOS Local Authentication — and for added flexibility, LoginRadius WebAuthn endpoints handle it securely across devices.
Facial Recognition
This method uses 2D or 3D imaging to identify facial geometry. It’s fast, contactless, and feels effortless.
A quick glance and — voilà — you’re in. Liveness detection ensures the system isn’t fooled by a photo or mask. Businesses love it because smoother logins mean more completed sign-ups and happier users.
Iris or Retina Scans
These are the heavyweights of biometric security. Each person’s iris pattern is unique, making this method nearly impossible to spoof.
You’ll see it in healthcare systems and airport checkpoints where accuracy matters more than speed. Though it requires specialized sensors, the precision is unmatched.
Voice, Palm-Vein, and Hand Geometry Recognition
These are less common but serve specific purposes. Voice recognition is great for accessibility or hands-free use, while palm-vein and hand geometry systems often show up in secure workplaces where physical access control is key.
Physical biometrics shine in mobile-first environments — anywhere users expect quick, seamless access. They turn everyday actions like a touch or glance into trusted security moments that feel natural rather than intrusive.
2. Behavioral Biometrics
If physical biometrics focus on who you are, then behavioral biometrics focus on how you behave.
They don’t look at your face or fingerprint — they look at the subtle ways you interact with your device.
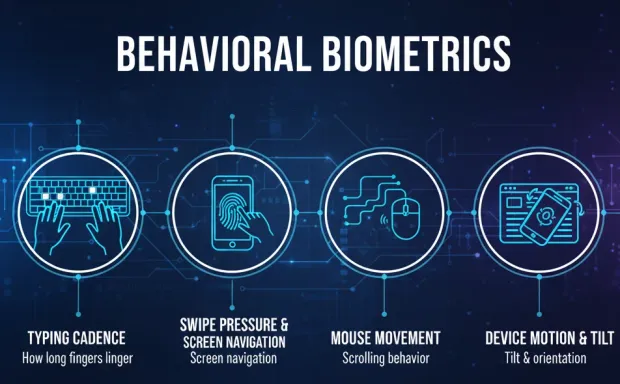
Everything from how fast you type to how firmly you press your touchscreen can create a behavioral signature that’s unique to you. Over time, algorithms learn your habits and build a pattern so familiar that even the tiniest deviation — a change in typing rhythm or swipe speed — can alert the system that something’s off.
Here’s what behavioral biometrics might quietly track behind the scenes:
-
Typing cadence and how long your fingers linger on each key
-
Swipe pressure and screen navigation habits on mobile devices
-
Mouse movement paths and scrolling behavior on web apps
-
Device motion, tilt, and orientation while you use it
Unlike one-time logins, behavioral biometrics keep working in the background. They continuously confirm your identity throughout a session, almost like an invisible guard who knows your digital “body language.”
If something feels unusual — say, a fraudster suddenly takes over your account — the system can instantly trigger step-up verification or log the user out.
Developers can plug into this intelligence using LoginRadius’ Adaptive Authentication module, which combines behavioral data, device signals, and risk scores to make smarter, real-time decisions.
For businesses, this creates an invisible safety net that spots suspicious activity without frustrating legitimate users. It’s especially powerful in fintech, e-commerce, and online banking, where continuous trust validation is crucial. Behavioral biometrics turn every interaction into a security layer — quietly, seamlessly, and intelligently.
3. Multi-Modal and Hybrid Biometrics
The next generation of biometric security isn’t about choosing one method — it’s about combining the best of several.
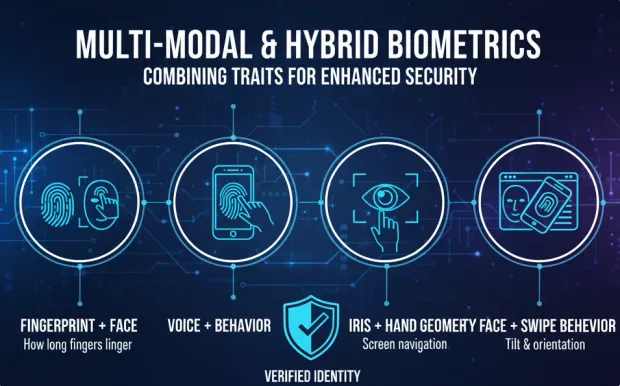
Multi-modal biometrics use two or more traits, such as fingerprint + facial recognition or voice + behavior, to verify identity. These blended systems fill the gaps of single-method approaches, balancing usability, speed, and assurance in one seamless experience.
For instance, if facial recognition struggles in low light, the system can fall back on fingerprint or voice data without slowing the user down. Similarly, a login flow might silently analyze your typing rhythm alongside your face scan to double-check authenticity.
Hybrid systems are fast becoming the new standard for industries like banking, healthcare, and enterprise SaaS — places where both precision and convenience matter. By blending physical and behavioral biometrics, organizations can deliver authentication that’s not just strong but smart, adapting to users and environments in real time.
Biometric Authentication Methods and Use Cases
Fingerprint Authentication
Fingerprint biometrics are a proven blend of convenience and accuracy. They’re inexpensive to deploy and widely supported.
In business terms, fingerprint login reduces friction by up to 70 % compared with password entry, cutting abandonment during sign-up. Fingerprint authentication is widely used in consumer mobile apps, smart devices, and retail kiosks.
Facial Recognition
Facial recognition is becoming the default for frictionless sign-ins. 3D depth sensors and ML-based liveness detection make it highly secure.
Integration is seamless for developers because the major operating systems expose standardized biometric APIs. LoginRadius CIAM can then treat the face match as a verified WebAuthn credential.
For business leaders, facial login builds trust—users see their data protected by visible technology. It’s perfect for loyalty programs, banking, or digital onboarding that must feel sophisticated yet simple.
Iris or Retina Scanning
Highly accurate and secure, iris scanning analyzes intricate eye patterns.
It’s best suited for environments with stringent identity assurance requirements, such as border control or healthcare.
Though implementation requires specialized hardware, the method delivers near-zero false acceptance rates—making it valuable for high-risk sectors, including government security agencies.
Voice Authentication
Voice recognition verifies identity through unique vocal signatures, ideal for voice assistants, call centers, and remote authentication.
It’s accessible and easy to use, requiring only a microphone. However, environmental noise and recorded voice attacks can challenge reliability, necessitating anti-spoofing algorithms. It’s widely used in smartphones and virtual assistants to recognize voice and offer personalized experiences.
Behavioral Biometrics
Instead of a single checkpoint, behavioral authentication runs continuously.
A fintech app, for instance, can detect if a user suddenly types differently—flagging possible account takeover.
The LoginRadius adaptive engine can assign risk scores in real time and request secondary verification only when needed.
Behavioral biometrics turn static security into dynamic defense, making them a cornerstone of modern CIAM for fraud prevention and identity verification in various sectors, including but not limited to financial institutions, e-commerce, cybersecurity, and healthcare.
When to Use Biometric Authentication
Biometric authentication is best used when you need fast, passwordless login with high security—such as mobile-first apps, banking, healthcare, government systems, and digital onboarding. It’s also ideal for continuous authentication, fraud detection, and frictionless CX. Use caution when device sensors are limited or users need accessibility alternatives.
Ideal Scenarios
-
Mobile-First Applications :
Mobile ecosystems already support native biometric sensors, making integration nearly effortless.
Using LoginRadius, developers can build unified flows across Android, iOS, and web with one API call.
-
High-Security Environments :
Industries handling sensitive data—banking, healthcare, government—benefit from the assurance that biometrics provide.
-
Passwordless Journeys :
Biometric credentials work perfectly with FIDO2 WebAuthn. Businesses adopting passwordless see up to 90 % reduction in credential-related support tickets.
-
Continuous Authentication :
Behavioral signals provide session-long verification, invaluable for fraud detection and insider-threat prevention.
-
Frictionless CX Goals :
Biometrics trim login times to seconds. The smoother the access, the greater the loyalty.
Use with Caution
-
Limited Hardware Support : Not all desktops or low-end devices include biometric sensors. Always offer OTP or social-login fallback.
-
Privacy Concerns : Explicit consent and transparent policy are non-negotiable.
-
Accessibility : Provide options for users who cannot use certain biometrics due to physical or cultural reasons.
Developers can manage all fallback logic and consent flows through the LoginRadius Admin Console, ensuring compliance and inclusivity.
Pros and Cons of Biometric Authentication
Like any powerful technology, biometric authentication comes with incredible benefits — and a few important considerations. When done right, it delivers stronger protection, smoother experiences, and measurable business ROI. When mishandled, it can create privacy or accessibility hurdles.
Let’s unpack both sides so you can make informed choices about implementing biometrics in your product or organization.
Pros: Why Biometric Authentication Wins
1. Strengthened Security
Traditional passwords are only as strong as the person creating them — and people often reuse or forget them. Biometric authentication replaces guessable credentials with traits that are uniquely human.
A fingerprint, face, or iris pattern can’t be easily shared or phished. When stored securely on-device, these templates remain private and mathematically protected.
This makes biometrics one of the most effective defenses against credential theft and account takeovers.
2. Frictionless User Experience
Security doesn’t have to mean extra steps. With biometrics, a simple glance or touch can unlock access instantly.
For users, it’s effortless — no typing, no remembering, no “reset password” frustration. For businesses, it’s a direct path to higher engagement. Organizations integrating biometrics report noticeable boosts in login completion rates and far fewer abandoned sign-up flows.
When authentication feels natural, users stay longer, convert faster, and return more often.
3. Reduced Operational Cost
Password resets are a silent budget drain. Help desks spend countless hours dealing with forgotten credentials.
By eliminating or minimizing passwords, businesses reduce those tickets significantly — freeing up resources for innovation rather than troubleshooting. In large enterprises, that can translate into thousands of saved hours annually.
4. Stronger Customer Trust and Brand Perception
When logging in feels secure and simple, it sends a clear signal: this brand values my time and my privacy.
Trust isn’t just technical — it’s emotional. Users feel safer when security is invisible yet effective.
Biometric authentication tells customers that your organization is forward-thinking and committed to protecting their identity.
The combination of convenience and safety builds loyalty that goes beyond any marketing campaign.
5. Alignment with the Passwordless Future
Biometric authentication is a cornerstone of the global shift toward passwordless identity. Using the LoginRadius Passwordless Authentication Suite, organizations can mix biometrics with OTPs or magic links to create adaptive, risk-based login experiences that meet every user where they are.
For developers, it’s an easy way to implement FIDO2 standards; for marketers, it’s a path to brand experiences that feel modern and friction-free.
Cons: What to Watch Out For
1. Privacy and Data Concerns
Biometric data is deeply personal. Storing it improperly could erode trust or even violate regulations like GDPR.
The best practice is on-device storage — something LoginRadius supports by design. Templates stay encrypted on the user’s device, not in a central database.
2. Accessibility Limitations
Not everyone can or wants to use biometrics. Injuries, disabilities, or cultural sensitivities may limit adoption. Always offer backup options such as OTPs, passkeys, or passwords to ensure inclusivity.
3. Hardware Dependence
Biometrics rely on sensors — cameras, fingerprint readers, microphones — that may not exist on every device.
A fallback strategy (for example, adaptive authentication) keeps users connected regardless of hardware.
4. Spoofing and Environmental Factors
While rare, spoofing attacks (like fake fingerprints or printed faces) do occur. Combining liveness detection, multi-modal biometrics, and adaptive policies greatly reduces that risk.
5. Regulatory Compliance
Laws governing biometric data are evolving fast. Organizations must stay up to date with local and global requirements. Platforms like LoginRadius simplify compliance by supporting GDPR, CCPA, SOC 2, and ISO 27001 frameworks out of the box.
Challenges of Biometric Authentication and How to Overcome Them
The main challenges in biometric authentication include privacy concerns, accessibility limitations, spoofing risks, device sensor differences, and evolving compliance laws. These can be overcome by storing templates on-device, offering fallback login options, using liveness detection and adaptive authentication, standardizing SDKs, and following GDPR/CCPA-aligned data practices.
| Challenge | Solution |
|---|---|
| Data Privacy & Consent | Templates remain on device; encrypt data and secure user consent. |
| Accessibility & Inclusion | Offer fallback options like OTP or social login through the Admin Console. |
| Spoofing Attacks | Deploy liveness detection and adaptive step-up authentication. |
| Device Fragmentation | Standardize via LoginRadius SDKs. |
| Compliance Variance | Follow GDPR/CCPA with built-in encryption and retention settings. |
| User Education | Provide transparent onboarding explaining privacy safeguards. |
Biometric Authentication with LoginRadius
For organizations looking to move beyond passwords and strengthen their digital defenses, biometric authentication offers a powerful path forward. It’s not just about modernizing login experiences — it’s about creating trust at every touchpoint.
Because biometric traits like fingerprints, facial geometry, or voice patterns are unique and incredibly difficult to replicate, they provide stronger protection than traditional credentials ever could.
Before implementing biometrics, evaluate whether the approach fits your organization’s goals and compliance standards. If your priority is frictionless access, passwordless convenience, or high-assurance verification for sensitive workflows, the LoginRadius CIAM platform can help you achieve it securely and at scale.
Here’s how to get started:
-
Define Your Use Case
Clarify your primary objective — are you aiming to reduce friction, replace MFA tokens, or enable step-up authentication for high-value actions? Identifying the goal ensures a smoother rollout.
-
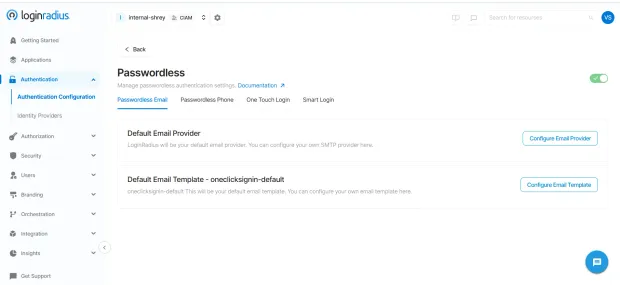
Enable Passwordless Authentication
Activate the Passwordless API to support device-bound biometric logins. This allows users to authenticate securely using built-in sensors on their devices.
-
Integrate WebAuthn
Implement browser-based biometric login using WebAuthn and FIDO2 standards. These protocols use public/private key cryptography — your users’ biometric data never leaves the device.
-
Configure Adaptive Authentication
Layer in contextual intelligence — device type, location, and behavior — to dynamically assess risk before granting access.
→Adaptive Authentication Overview
-
Use Developer SDKs
Deploy platform-specific SDKs for Android, iOS, or web to simplify integration and speed up development.
-
Monitor and Optimize
Use the LoginRadius Admin Console to monitor performance, analyze user adoption, and fine-tune your UX for better engagement.
By consolidating identity management, compliance, analytics, and policy control in one platform, LoginRadius ensures biometric authentication becomes an organic part of your CIAM ecosystem — not an isolated feature.
And as biometric technologies continue to advance, their use cases will only expand — from frictionless consumer logins to high-assurance enterprise verification. With the right strategy and platform, biometrics can move your organization confidently into the passwordless future.
Conclusion
Biometric authentication has evolved from novelty to necessity. It’s no longer a futuristic concept but a practical solution driving secure, passwordless access everywhere—from fintech apps to healthcare portals and retail experiences.
With LoginRadius, you can adopt biometrics confidently—leveraging a unified CIAM platform that handles compliance, privacy, SDKs, and adaptive logic so you focus on delivering experiences users love.
In short, biometric authentication isn’t about replacing passwords—it’s about replacing frustration with trust.
When identity verification feels natural, users stay, transact, and advocate for your brand.
Start building secure, passwordless biometrics today: Get Started with LoginRadius
FAQs
1. What is biometric authentication?
Biometric authentication verifies identity using unique human traits like fingerprints, facial features, or voice patterns for secure, passwordless login.
2. What are the main types of biometric authentication?
They include physical biometrics (fingerprint, face, iris) and behavioral biometrics (typing rhythm, gestures, device movement).
3. How does biometric authentication improve security?
It eliminates reusable passwords and relies on traits that are extremely hard to duplicate, preventing phishing and account takeovers.
4. What is biometric login?
Biometric login allows users to sign in using on-device biometrics such as fingerprint or Face ID instead of traditional passwords, enhancing both UX and protection.