Introduction
For years, security advice sounded simple: add another factor and you’re safe. One-time passwords, push approvals, SMS codes these became the default definition of strong authentication. But attackers evolved faster than that model.
Today’s phishing attacks don’t just steal passwords, they replicate entire login flows. Modern phishing kits can proxy sessions in real time, capture OTPs, intercept session cookies, and even trigger push notifications until a user taps “Approve” out of habit. What looks like strong multi-factor authentication (MFA) can quietly break under a well-crafted phishing page.
That’s why the conversation has shifted.
It’s no longer enough to ask, “Do you have MFA?” The real question is: Is your authentication phishing-resistant?
Phishing-resistant authentication changes the model entirely. It doesn’t rely on shared secrets like passwords or OTPs that can be intercepted or replayed. Instead, it uses cryptographic verification tied to the user’s device and the exact origin (domain) of your application.
This makes it extremely difficult for attackers to trick users into visiting fake websites or to carry out man-in-the-middle attacks.
Standards like WebAuthn and FIDO2 were built for this new reality. They replace “what you know” with “what you have,” a private key stored securely on a device that never leaves it. Authentication becomes origin-bound, meaning even a perfect phishing site can’t replicate the trust required to log in.
The result is a fundamentally stronger approach, one that attackers can’t easily proxy, replay, or socially engineer around.
In this guide, we’ll break down what phishing-resistant authentication actually means, why traditional MFA fails against modern attacks, how WebAuthn and FIDO2 work in practice, and why this approach is quickly becoming the new security baseline for SaaS platforms and enterprises.
Because in today’s threat landscape, adding more factors isn’t enough. You need authentication that attackers can’t fake in the first place.
What Is Phishing-Resistant Authentication?
Phishing-resistant authentication is an authentication method designed to prevent attackers from stealing or replaying credentials through phishing attacks. Unlike traditional login methods, it cryptographically binds authentication to the legitimate domain and device, making credential reuse nearly impossible.
At its core, phishing resistance eliminates the very thing attackers depend on: transferable secrets.
In password-based systems, the secret is something you know. In OTP-based MFA, the secret is a time-bound code. Even with push-based authentication, approval can still be socially engineered. All of these can be intercepted, proxied, or manipulated if a user is tricked into interacting with a malicious site.
Phishing-resistant authentication works differently. It relies on public-key cryptography. When a user registers, a unique key pair is generated on their device. The private key stays securely stored on that device. The public key is shared with the server.
During authentication, the server sends a cryptographic challenge. The device signs it with the private key. The server verifies the signature using the stored public key. No password is transmitted. No OTP is shared. No reusable secret exists.
More importantly, the authentication request is bound to the origin, the exact domain name of the website. If a user lands on a phishing site that looks identical to the original application, the authentication simply fails because the domain does not match. The browser enforces this check automatically.
This is the defining characteristic of phishing-resistant MFA. It is resistant not because users are more careful, but because the protocol itself refuses to cooperate with fraudulent domains.
In other words, phishing resistance is not a feature layered on top of authentication. It is a property built into the cryptographic design.
Why Traditional MFA Is Not Phishing Resistant
Multi-factor authentication was designed to strengthen passwords, and for a time, it reduced credential stuffing and brute-force attacks. But phishing evolved faster than MFA defenses did.
Traditional MFA still depends on shared secrets. Passwords, SMS OTPs, and even authenticator app codes are derived from secrets known to both the client and the server. If an attacker tricks a user into revealing those codes in real time, the system cannot distinguish between the legitimate user and the attacker.
Modern phishing campaigns exploit this weakness using adversary-in-the-middle (AiTM) kits that proxy legitimate login pages. When a user submits credentials, the attacker forwards them instantly.
When the service issues an OTP challenge, the phishing page captures and relays the code back to the real service, allowing the attacker to hijack the authenticated session.
From the system’s perspective, the login appears valid. The credentials match. The OTP verifies. The session is created. The breach happens within the rules of the protocol.
Push-based MFA faces similar risks. Attackers repeatedly trigger push requests until a user approves one out of frustration, a tactic known as MFA fatigue. The second factor exists, but it can still be manipulated.
This is why not all MFA qualifies as phishing resistant MFA. Multiple factors do not guarantee protection if those factors can be intercepted or socially engineered.
Phishing-resistant authentication addresses this flaw by removing shared secrets entirely. Instead of transmitting reusable codes, it relies on cryptographic proof that cannot be proxied across domains. That architectural difference is what separates traditional MFA from truly phishing-resistant access.
Enter FIDO: The Cryptographic Shift Toward Phishing Resistance
If traditional MFA still relies on secrets that can be replayed, the logical next step is simple: eliminate shared secrets altogether. That idea led to the creation of the FIDO standards.
Developed by the FIDO Alliance, FIDO introduced an authentication model built on public-key cryptography. Instead of verifying knowledge of a password, it verifies possession of a private key that never leaves the user’s device. This is not a minor upgrade; it is a structural redesign of authentication.
In a FIDO-based system, each registration generates a unique key pair. The private key is securely stored on the device, often within hardware-backed secure elements such as a TPM or Secure Enclave. The public key is stored on the server. Because no shared secret exists, there is no password database to breach and no OTP to intercept.
FIDO authentication is also origin-bound. Credentials created for one domain cannot be used on another. If a user lands on a phishing site that imitates a legitimate application, the authentication simply fails because the private key will not sign a challenge for the wrong origin.
This domain-level enforcement is what makes FIDO phishing-resistant by design. Security is enforced cryptographically, not through user awareness.
FIDO supports both platform authenticators, such as built-in biometrics and device PINs, and roaming authenticators, like hardware security keys. In both cases, authentication is based on cryptographic proof of possession rather than knowledge of a secret.
This model forms the foundation of phishing-resistant authentication in modern systems, shifting trust from what users remember to what devices can securely prove.
What Is WebAuthn?
WebAuthn, short for Web Authentication, is a web standard developed by the W3C that enables phishing-resistant authentication directly in browsers. It provides the JavaScript API that allows web applications to register and authenticate users using public-key cryptography.
In simple terms, if FIDO defines the security model, WebAuthn is how web applications actually use it.
WebAuthn allows a browser to communicate with authenticators such as built-in biometrics, device PIN systems, or external security keys in a standardized way. When a user registers, WebAuthn coordinates the creation of a unique cryptographic key pair. When the user logs in, it facilitates a secure challenge-response process between the server and the authenticator.
The critical detail is that WebAuthn enforces origin binding. The credential generated for example.com cannot be used on examp1e.com, even if the phishing site looks identical. The browser itself ensures that authentication only succeeds for the exact registered domain.
This browser-level enforcement is what gives WebAuthn its resistance to phishing. The user does not have to inspect URLs or detect subtle spelling changes. The protocol refuses to cooperate with fraudulent origins.
WebAuthn works with two types of authenticators. Platform authenticators are built into devices such as fingerprint sensors, facial recognition systems, or device PIN verification. Roaming authenticators are portable hardware keys that users can connect via USB, NFC, or Bluetooth. Both support the same public-key model, and both contribute to phishing-resistant MFA implementations.
When people ask, “What is WebAuthn?” the accurate answer is this: WebAuthn is the browser standard that makes FIDO2-based phishing-resistant authentication possible on the web. It replaces passwords and OTP-based flows with cryptographic proof tied to a specific domain and device.
FIDO2 vs WebAuthn: Understanding the Difference
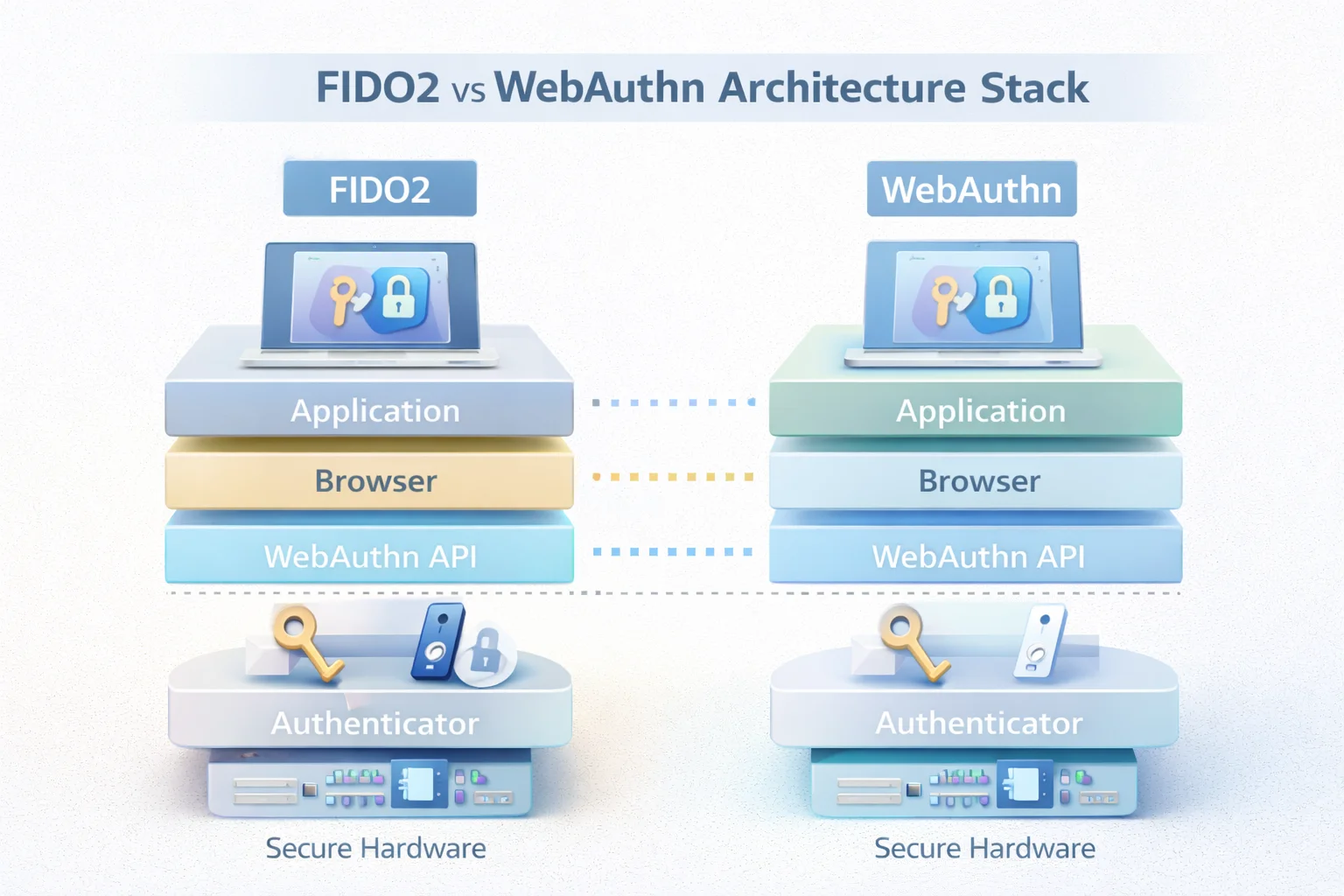
FIDO2 and WebAuthn are closely related but not identical. Understanding the distinction is important when evaluating phishing-resistant authentication solutions.
WebAuthn is a browser API defined by the W3C that enables web applications to register and authenticate users using public-key credentials. It operates at the browser layer, facilitating communication between the application and the authenticator.
FIDO2 is the broader standard defined by the FIDO Alliance. It includes WebAuthn along with CTAP (Client to Authenticator Protocol), which governs how authenticators such as hardware security keys communicate with devices over USB, NFC, or Bluetooth.
In short, WebAuthn is the web-facing interface developers implement, while FIDO2 is the complete authentication framework that includes device communication.
When comparing WebAuthn vs FIDO2, phishing resistance comes from the FIDO2 model as a whole public-key cryptography, origin binding, and device-based key storage with WebAuthn serving as the browser implementation layer.
Phishing Resistant MFA Examples in the Real World
Phishing-resistant authentication is already embedded in modern devices and platforms — most users just don’t realize it.
Passkeys are one of the most visible phishing-resistant MFA examples. Built on FIDO2 and WebAuthn standards, they replace passwords with origin-bound cryptographic authentication.
Even if a login page is cloned, the credentials cannot be used on a fraudulent domain. In fact, major platforms have reported that passkeys can reduce phishing-related account takeovers by up to 99% compared to password-based logins.
Hardware security keys provide another strong example. These USB or NFC devices securely store private keys and generate signatures tied to the exact origin, preventing credential replay.
According to industry reports, organizations deploying hardware-backed authentication have seen phishing success rates drop to near zero.
Platform authenticators such as Windows Hello, Touch ID, and Face ID work similarly. Biometrics unlock a device-held private key, and authentication succeeds only when a valid challenge is signed for the legitimate domain. This approach has helped reduce reliance on passwords, which still account for over 80% of data breaches globally.
What unites these approaches is the absence of shared secrets. No OTP to forward. No password to steal. Just device-bound cryptographic proof.
For enterprises implementing phishing-resistant access, platforms like LoginRadius enable WebAuthn and passkey-based authentication to enforce origin binding and device verification at scale, helping organizations align with modern security standards and reduce account takeover risk.
Not all passwordless solutions meet this standard. Email magic links and push-based approvals can still be intercepted or socially engineered.
Phishing-resistant MFA must cryptographically bind identity to both device and domain otherwise, the login should fail.
How WebAuthn Authentication Actually Works
Phishing-resistant authentication becomes clearer when examining how WebAuthn operates. Its security guarantees stem from cryptographic challenge-response verification rather than shared secrets.
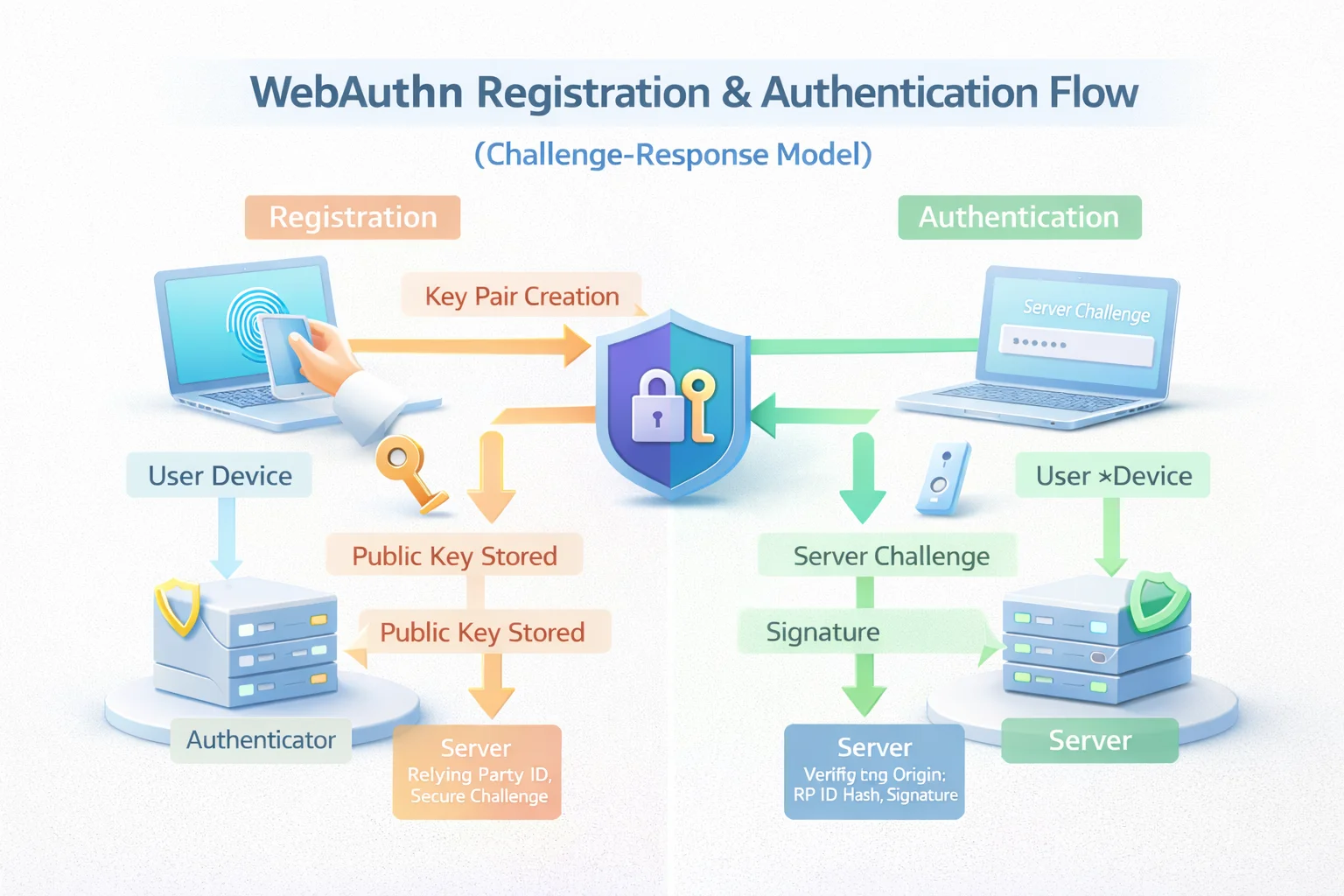
WebAuthn functions in two phases: registration and authentication.
During registration, the server generates a challenge and sends it to the browser. The authenticator creates a unique key pair for that specific domain. The private key remains securely stored on the device, while the public key is returned to the server and associated with the user account.
No password is created or transmitted. The server stores only the public key, which cannot be used to impersonate the user.
During authentication, the server issues a new challenge. After verifying user presence or user verification locally (via biometrics or device PIN), the authenticator signs the challenge using the private key. The server verifies the signature with the stored public key and validates the origin before granting access.
Origin binding is critical. Credentials are tied to the exact domain where they were created. If a user attempts to authenticate on a lookalike phishing domain, the signature will not validate.
Because the proof is cryptographic and request-specific, there is nothing reusable for an attacker to intercept or replay. Phishing resistance is embedded directly into the protocol.
Why FIDO Authentication Is Truly Phishing Resistant
Phishing resistance in FIDO-based authentication is enforced cryptographically, not behaviorally. The system prevents credentials from being used outside their intended context.
First, credentials are origin-bound. A key pair created for one domain cannot be used on another. The browser enforces this at the protocol level.
Second, authentication relies on asymmetric cryptography. The private key never leaves the device, and no shared secret exists on the server. Even if public keys are exposed, they cannot be used to generate valid signatures.
Third, each website receives a unique key pair. This prevents credential reuse and limits breach impact to a single service.
Fourth, user verification occurs locally. Biometrics or PINs unlock the private key on the device without transmitting sensitive data externally.
In a phishing scenario, attackers can proxy login pages and forward credentials in traditional systems. With FIDO-based authentication, they cannot obtain a valid signature for a fraudulent origin. The browser acts as a built-in security boundary.
This is the structural difference between traditional MFA and phishing-resistant MFA. Instead of layering additional secrets onto passwords, FIDO removes the secret-based model entirely.
Phishing resistance here is not incremental risk reduction; it is the elimination of the credential replay attack path.
Phishing Resistant Access in Enterprise and Zero Trust Architectures
Phishing-resistant authentication is becoming a baseline requirement in enterprise security strategies.
Zero Trust architectures treat identity as the primary security perimeter. Every request must be continuously verified. If credentials can be phished, the model collapses.
Traditional MFA reduced risk but did not eliminate phishing-based account takeovers. OTP forwarding and push fatigue attacks have repeatedly demonstrated this gap.
Phishing-resistant access addresses that gap by cryptographically binding authentication to both the domain and the device. Even if users are tricked into visiting malicious sites, authentication fails because the origin does not match.
This approach aligns naturally with Zero Trust principles. Device-bound credentials, hardware-backed key storage, and enforced origin validation strengthen identity assurance across workforce, partner, and B2B environments.
Regulatory guidance increasingly emphasizes phishing-resistant MFA as a standard for strong authentication. Organizations implementing WebAuthn and FIDO2 are aligning with these evolving expectations.
Phishing-resistant authentication is not simply an enhancement to MFA. It is a structural improvement in identity verification, one that directly reduces breach risk in environments where identity defines the security boundary.

Common Misconceptions About WebAuthn and FIDO2
As phishing-resistant authentication adoption grows, misconceptions often slow implementation more than technical challenges do.
One common belief is that biometrics are transmitted to the server. They are not. In WebAuthn and FIDO2 flows, biometrics remain on the device and are used only to unlock the private key stored in secure hardware. The server receives only a signed cryptographic response.
Another misconception is that WebAuthn is merely a passwordless feature. While it removes passwords, its primary value is phishing resistance through origin binding and device-based cryptographic verification. Usability improves, but the real gain is structural security.
There is also confusion about hardware requirements. Many assume phishing-resistant MFA requires external security keys for every user. In reality, most modern devices include built-in platform authenticators capable of generating and storing secure credentials.
Some organizations hesitate due to perceived complexity. However, WebAuthn is standardized across major browsers, and many identity platforms abstract the cryptographic details. The complexity lies in the protocol design, not necessarily in implementation.
Finally, phishing-resistant authentication does not eliminate all risk. It significantly reduces credential phishing and replay attacks but does not prevent every form of endpoint compromise or social engineering. It removes one of the most common breach paths for stolen credentials but security remains layered.
The standards are mature, browser support is broad, and the gap is often conceptual rather than technical.
Implementation Considerations for Developers
Phishing-resistant authentication requires thoughtful implementation to preserve both security and usability. The protocol provides the foundation, but configuration and lifecycle decisions determine effectiveness.
Credential registration must be handled carefully. Applications generate a challenge, define the relying party correctly, and configure authenticator selection criteria. Since WebAuthn strictly binds credentials to domain identifiers, misconfiguration can weaken protection.
Attestation policies require deliberate choice. Some organizations enforce hardware-backed authenticators through attestation validation, while others prioritize broader compatibility. The decision depends on risk tolerance and device diversity.
Discoverable credentials and resident keys improve user experience by enabling username-less flows, but developers must plan for account recovery and device loss. A secure system should not create unnecessary lockout scenarios.
Credential lifecycle management is critical. Devices are replaced, and security keys can be lost. Applications need secure re-registration processes and fallback mechanisms that do not reintroduce weaker authentication factors.
Multi-device passkey synchronization enhances usability but extends the trust boundary into operating system storage environments. Understanding platform key management models is essential.
Server-side verification must rigorously validate challenge values, origin, RP ID hash, and signature. Skipping verification steps undermines phishing resistance.
Organizations often roll out phishing-resistant MFA gradually, maintaining transitional fallback methods while encouraging adoption for high-value accounts first.
The objective is not simply enabling WebAuthn, but preserving end-to-end phishing resistance from domain configuration to cryptographic validation and credential lifecycle management. Done correctly, it removes the credential replay vulnerability that traditional MFA leaves exposed.
Conclusion
For a long time, authentication has been built on things users can share — passwords, codes, approvals. And as long as something can be shared, it can be stolen. That’s the uncomfortable truth the industry has been working around for years.
Phishing-resistant authentication flips that model. It doesn’t try to make secrets harder to steal — it removes them from the equation. Authentication becomes a proof, not a guess. A device signs a challenge. The domain is verified. If everything doesn’t match exactly, access is denied. No second chances, no clever workarounds for attackers.
WebAuthn and FIDO2 aren’t just upgrades to MFA. They change the rules entirely. Security is no longer dependent on users spotting fake links or resisting push fatigue. It’s enforced by design, at the browser and protocol level.
Of course, this shift won’t happen overnight. Passwords will linger. Hybrid setups will exist. But the direction is already clear: if authentication can be replayed, it will eventually be exploited. If it’s bound to the device and domain, that attack path disappears.
So the real shift isn’t from single-factor to multi-factor. It’s from “Can we verify this user?” to “Can this authentication even be misused?”
Because in modern security, adding layers helps. But removing the attacker’s options is what actually changes the outcome.
Ready to Make Your Authentication Phishing Resistant?
Stop relying on authentication methods that attackers already know how to bypass.
It’s time to move beyond OTPs, push approvals, and “good enough” MFA and adopt authentication that is secure by design.
With LoginRadius, you can implement WebAuthn and passkey-based authentication to deliver true phishing-resistant access across your applications without compromising user experience or developer velocity.
Start building phishing-resistant authentication today with LoginRadius. Because the goal isn’t just to add another factor. It’s to remove the attack path entirely.
FAQs
Q: What makes authentication phishing resistant?
A: Phishing-resistant authentication uses public-key cryptography and origin binding to ensure credentials only work on the legitimate domain. There are no shared secrets that attackers can intercept or replay.
Q: Is phishing-resistant MFA better than traditional MFA?
A: Yes. Traditional MFA can still be bypassed through OTP forwarding or push fatigue attacks. Phishing-resistant MFA eliminates reusable secrets and blocks authentication on fraudulent domains.
Q: What is the difference between WebAuthn and FIDO2?
A: WebAuthn is the browser API that enables public-key authentication on the web. FIDO2 is the broader standard that includes WebAuthn and the protocol used to communicate with authenticators.
Q: Are passkeys considered phishing-resistant?
A: Yes. Passkeys are built on WebAuthn and FIDO2 standards, making them cryptographically bound to the correct domain and device, which prevents credential reuse on phishing sites.



