Partner Identity remains largely unaddressed by today’s Workforce IAM and Customer IAM (CIAM) solutions. If you’re building a B2B SaaS product, you’ve probably felt this already.
Most teams building B2B SaaS apps are still forced to cobble together identity features meant for employees (Workforce IAM) or end-users (CIAM), hacking in support for multi-tenancy, federation, and delegated access. The result?
-
Endless custom logic
-
High maintenance overhead
-
Ever-increasing tech debt
-
Slower time to market
-
Fragile integrations that don’t scale
Partner IAM, also known as B2B Identity Management, was supposed to fix this. But too often, it’s just a bullet point in a product sheet — not a real, extensible system.
At LoginRadius, we’ve built Partner IAM from the ground up to serve one job: give your external organizations secure, scalable access without making your developers pay the price.
With it, you can:
-
Define and isolate partner organizations
-
Support federated SSO (SAML, OIDC)
-
Enable delegated administration
-
Customize login experiences per partner
-
And manage everything through APIs or low-code workflows
In this guide, we’ll show you how to implement LoginRadius Partner IAM, step by step from architecture to onboarding to scaling it across your ecosystem.
If you’re building for B2B and identity is slowing you down, this is how you fix it.
What is Partner IAM?
Partner IAM manages external organizations and their users, providing secure access through federation, delegated administration, and multi-tenant B2B identity structures.
Partner IAM, also known as B2B Identity Management, addresses a growing need in modern SaaS: providing businesses, not just individual users, secure and customized access to platforms.
Unlike workforce IAM or traditional CIAM, Partner IAM models organizations as first-class entities. It enables B2B authentication, delegated administration, custom branding, and scalable, secure B2B integration without the engineering rework.
Why is B2B IAM Important?
Partner IAM or B2B IAM provides external businesses with secure, isolated access to your platform while simplifying partner onboarding, governance, and growth at scale.
B2B software isn’t just about users anymore — it’s about organizations. And each one brings its own complexity: unique domains, user roles, identity providers, compliance needs, and branding expectations.
Your product has to do more than authenticate individual users. It has to understand the structure of the businesses using it.
That’s what B2B identity management solves.
When done right, it becomes the foundation for:
-
Secure external collaboration : Every user is scoped to their organization, every action auditable, every access path defensible.
-
Streamlined onboarding : Because partners don’t want a support ticket to create users. They want to bring their own SSO and manage their own teams.
-
Consistent experience, tailored per org : One platform, but with login pages, MFA settings, and roles that feel purpose-built for each partner.
-
Compliance-ready controls : From tenant-level policies to data isolation and access logs, built in from day one. Standards like OWASP Identity Management Guidelines emphasize that proper identity isolation and federation are critical for B2B systems.
This is where B2B identity management earns its keep.
It lets you model the real world, which is orgs with internal hierarchies, custom SSO, and lifecycle ownership—and implement them in a way that’s secure, flexible, and low-friction for everyone involved.
More than anything, it allows your platform to grow with your ecosystem, without your team having to rewrite authentication every time a new partner joins.
How is B2B IAM Different From CIAM and Workforce IAM?
Most identity systems fall into two categories: CIAM, which focuses on consumers, and Workforce IAM, which secures internal employees.
But when you’re building for external organizations — your partners, vendors, resellers, or enterprise customers — neither one fits.
Let’s break it down:
| Feature | Workforce IAM | CIAM | B2B IAM |
|---|---|---|---|
| User Type | Internal employees | Individual consumers | External organizations and their users |
| Ownership | Managed by internal IT | Self-managed by end users | Administered by external orgs or delegated admins |
| Identity Federation | Limited to enterprise SSO | Sometimes supported | Required per org (SAML/OIDC) |
| Provisioning | Centrally controlled (HRIS/ITSM) | Self-registration or social login | SCIM, JIT, and delegated provisioning |
| Branding | Single enterprise look & feel | Public-facing UX | Org-specific branding and domains |
| Access Control | Department or role-based | Basic preferences | Fine-grained per-org, per-role policies |
| User Lifecycle | On/offboarding via IT | User-driven | Partner-admin driven, automated via APIs |
| Scalability Model | Fixed user base | Broad public scale | Multi-tenant, multi-org structure |
TL;DR:
-
CIAM handles scale but not structure.
-
Workforce IAM handles structure but not flexibility.
-
B2B IAM is the missing third model - purpose-built for managing identity across many external organizations, each with their own requirements and expectations.
With B2B IAM, the unit of management isn’t just the user, but also the organization. And that shift changes everything about how identity flows, permissions, and admin models are designed.
What are the Benefits of B2B IAM?
Partner IAM or B2B IAM helps businesses manage external organizations securely by reducing risk, accelerating onboarding, and enabling scalable access control through SSO, delegated admin, and automation.
When you shift from managing users to managing organizations, your IAM system stops being just a security layer and starts becoming a growth engine.
A well-architected B2B identity management setup doesn’t just solve access control. It reduces risk, accelerates partner onboarding, and improves the experience across every business relationship.
Here’s what changes when you get it right:
1. Reduces business risk
With each partner operating independently, isolation is non-negotiable.
LoginRadius’ B2B IAM gives you:
-
Data boundaries by default — partners can’t see what they shouldn’t
-
Role-based access controls — so the right people get the right access, every time
-
Built-in MFA and adaptive policies — because trust shouldn't mean tradeoffs in security
You get auditability, compliance, and peace of mind — without having to handhold every login.
2. Drives business growth
The faster a partner gets access, the sooner they can deliver value.
And the smoother the experience, the more likely they are to stick around.
With LoginRadius B2B IAM:
-
You enable federated SSO or self-service sign-up
-
Provision users on the fly with Just-In-Time onboarding
-
Deliver a customized login experience that feels built just for them
Better B2B integration equals better adoption & better retention.
3. Simplifies partner onboarding and builds trust
You don’t scale by adding support tickets.
You scale by letting partners onboard and manage themselves securely.
That’s what LoginRadius B2B IAM enables:
-
SAML and OIDC federation for enterprise-grade convenience
-
Self-serve admin portals so partners can control their own users
-
SCIM provisioning and APIs to automate every step
It’s not just faster — it shows partners you’re serious about making collaboration seamless.
What is the Difference Between B2B and B2C IAM?
B2B IAM manages external organizations with multiple users, SSO, and delegated admin, while B2C IAM focuses on individual user access, self-registration, and unified brand experiences.
To design the right identity flows, you first need to understand how both the models differ at a fundamental level.
Here’s how B2B identity management stacks up against B2C IAM:
| Capability | B2C IAM (Consumer Identity) | B2B IAM (Partner IAM) |
|---|---|---|
| Identity Unit | Individual user accounts | External organizations with multiple users |
| Onboarding | Self-registration, social login | Admin-driven, Just-In-Time (JIT), or SCIM-based provisioning |
| Authentication | Email/password, social login, passkeys | SAML, OIDC, passwordless, org-specific MFA policies |
| Access Control | Simple role-based or user-specific | Hierarchical org roles, fine-grained access control (FGA) |
| Administration | Centralized or user-managed | Delegated administration per organization |
| Data Isolation | Shared across a single tenant | Strict tenant-based data boundaries |
| Compliance Focus | Consent, privacy (e.g., GDPR, CCPA) | Data governance, audit trails, B2B access policies |
| Use Case Fit | Retail apps, social platforms, SaaS freemium | Partner portals, B2B SaaS, marketplaces, vendor access |
Why It Matters
Trying to stretch a B2C identity model to fit a B2B authentication use case introduces technical debt from day one.
Your partners expect org-specific SSO, custom login flows, and delegated control. Your system expects: one user, one role.
With B2B identity management, you architect identity around the organization, not the individual — and that shift is what enables secure, scalable access at the enterprise level.
What Should a B2B IAM Solution Offer?
A purpose-built B2B IAM solution isn’t just about logging users in. It’s about giving each partner organization a secure, scalable, self-contained identity experience, without increasing your engineering burden.
Here’s what that looks like and how LoginRadius Partner IAM delivers it:
1. Tenant Management (Org-Level Control)
Each partner organization operates as its own isolated tenant within your platform.
LoginRadius lets you:
-
Define and manage orgs independently
-
Scope users, roles, and access policies to a specific org
-
Cleanly separate data, auth settings, and experiences across orgs
2. Configuration Inheritance
Not every partner needs a custom setup.
LoginRadius supports:
-
Default authentication policies across orgs
-
The ability to override configurations at the org level
-
Streamlined setup for new orgs based on predefined templates
3. Delegated Administration
You shouldn’t have to manage every user for every partner.
LoginRadius enables:
-
Granular role assignment within each org
-
Partner-level admins who can invite, remove, and manage their own users
-
Self-service without loss of visibility or control
4. Relationship Modeling (Users ↔ Organizations)
In B2B, a user’s access is defined by their relationship to an organization.
LoginRadius gives you:
-
Flexible user-org mappings
-
The ability to assign users to one or more organizations
-
Org-aware roles and policies — so access is always in the right context
5. Federated SSO (SAML, OIDC) with JIT Provisioning
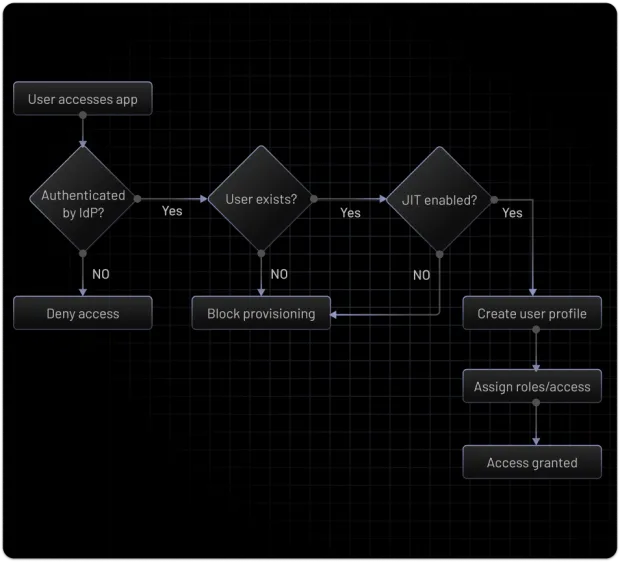
Enterprise partners don’t want new accounts — they want to use their existing identity provider.
With LoginRadius, you can:
-
Set up federated SSO per org, using SAML or OIDC
-
Enable Just-In-Time (JIT) provisioning when a user logs in
-
Support a frictionless, secure onboarding experience
6. SCIM-Based User Provisioning
For orgs with advanced IT, SCIM integration is a must.
LoginRadius supports:
-
Inbound SCIM provisioning for creating and managing users automatically
-
Real-time sync of user roles, deactivation events, and profile updates
-
Better lifecycle management, zero manual intervention
7. Adaptive MFA, Passkey, and Risk Detection
Modern threats demand modern defenses.
LoginRadius provides:
-
Org-specific MFA settings (SMS, email, TOTP, passkeys)
-
Risk-based authentication policies (IP checks, device context, velocity detection)
8. Custom Branding and White-Labeled Domains
Partners expect to see their brand when their users log in.
With LoginRadius, you can:
-
Customize login screens per org (logos, colors, copy)
-
Support org-specific domains like login.partnername.com
-
Deliver a seamless brand experience without writing UI code
9. Low-Code Orchestration Flows
No need to build complex identity flows from scratch.
LoginRadius’ identity orchestration platform allows you to:
-
Design and customize workflows visually
-
Control what happens before, during, and after login
-
Launch auth updates without long dev cycles
10. Fine-Grained Access Controls (FGA)
Not all partner users are the same.
LoginRadius supports:
-
Role - and permission-based access per user
-
API-level and dashboard-level access control
-
Scoped actions within a partner org (e.g., view-only, billing-only, admin)
When you combine these capabilities, you get more than just a login system. You get a B2B-ready identity foundation — built for scale, security, and partner experience from day one.
Benefits of LoginRadius Partner IAM
LoginRadius Partner IAM enables fast, scalable B2B authentication through prebuilt onboarding flows, delegated user management, federated SSO, and seamless B2B integration — all backed by a developer-first architecture.
All the right capabilities don’t mean much if they take months to implement or crumble under scale. That’s where LoginRadius makes a difference.
It’s not just that the platform supports federation, multi-tenancy, and delegated admin — it’s that it does so in a way that’s developer-friendly, scalable by design, and built to move fast.
Here’s what you get out of the box:
1. Partner onboarding in minutes, not months
LoginRadius lets you onboard external organizations through preconfigured flows — whether it's federated SSO, self-registration, or JIT provisioning. No custom workarounds. No hand-holding.
2. Delegated user management
Each organization can manage its own users with role-based admin privileges. That means fewer tickets for your team and faster user lifecycle management for your partners.
3. Branded logins per organization
Login pages don’t just work — they match your partner’s brand. Customize logos, themes, and even domains per org, all without deploying new code.
4. Federated SSO without custom code
Support SAML or OIDC integration for each partner through the LoginRadius console or API. Provision users dynamically and map them to org roles, without writing glue code or reinventing workflows.
5. Built to scale across 1,000s of orgs
LoginRadius’ multi-tenant infrastructure and org-aware architecture make it easy to isolate data, enforce per-org policies, and scale access across your ecosystem without compromising performance or security.
6. Built for integration
RESTful APIs. Clean SDKs. Built-in orchestration. Whether you’re integrating with your app, partner dashboard, or provisioning system, LoginRadius plays well with your existing stack.
If you’re building for external businesses and are tired of bending identity systems that weren’t made for it, this is what getting it right looks like.
Common Use Cases of LoginRadius Partner IAM
Anywhere multiple external organizations need secure, independent access, like SaaS platforms, portals, ecosystems, and regulated industries.
LoginRadius Partner IAM isn’t just built for theory; it’s engineered for the real-world complexity of modern B2B platforms.
When your users are part of other businesses, each with their own structure, compliance needs, and authentication systems, the complexity multiplies.
LoginRadius Partner IAM is purpose-built for that complexity. Here’s where it fits best:
1. SaaS Platforms Requiring Organization-Aware Access
For multi-tenant SaaS products where each customer is a business, Partner IAM provides:
-
Organization-level identity and role scoping
-
SSO per customer org
-
Delegated user management
-
Custom login experiences
You don’t have to manually stitch together user groups, roles, and routing logic — it’s all built in.
2. Partner, Vendor, or Franchise Portals
In ecosystems where third-party organizations need controlled access to your systems — vendors placing orders, franchisees managing stores, partners updating customer records —
Partner IAM delivers:
-
Isolated org-level authentication and authorization
-
Org-specific access policies
-
SCIM and JIT provisioning for seamless user management
It replaces manual provisioning and spreadsheet-based access control with repeatable, secure identity flows.
3. Internal Tools with External Collaborators
When internal apps need to support contractors, agencies, or external developers, treating them like employees doesn’t scale.
Partner IAM enables:
-
External SSO integration (SAML/OIDC)
-
Role enforcement across org boundaries
-
Visibility into external access without compromising internal policies
This is essential for platforms that involve third parties in product development, support, or content delivery.
4. Industry-Specific Platforms (Pharma, Insurance, Manufacturing)
Regulated industries require tenant-level governance. Partner IAM gives you:
-
Per-org data boundaries and compliance support
-
Full audit trails and admin segmentation
-
Identity federation for partner enterprises
Ideal for provider portals, supplier ecosystems, and any platform handling sensitive B2B interactions.
Step-by-Step: Implementing Partner IAM With LoginRadius
Implementing B2B Identity Management with LoginRadius involves a structured, straightforward approach. Here’s what you’ll need to do:
Step 1: Define Your Partner Organizations
Use the LoginRadius Admin Console or API to create a new organization:
-
Go to the Organization tab in the Admin Console.
-
Click Create Organization.
-
Enter the organization name and one or more email domains to associate.
-
Click Save to generate a unique Org ID.
The domain is later used for routing users to the correct identity provider and enabling Just-In-Time (JIT) user provisioning.
Step 2: Configure Authentication at the Org Level
Once the org is created:
-
Assign authentication methods per organization — email/password, passkeys, or federated SSO.
-
Enable domain-based IdP routing for users with matching email domains.
-
Apply org-specific MFA settings via the LoginRadius Console.
Identity providers and MFA flows can be customized at the org level.
Step 3: Set Up Delegated Admin Access
Allow organizations to manage their own users with scoped roles:
-
Create roles via the **Roles **tab in each organization.
-
Assign tenant-level permissions to those roles.
-
Set one role as the default for JIT provisioning.
-
Add users manually or invite them via email, and assign roles.
Users can only be added if they already exist at the tenant level; invited users are added once they accept their email invitation.
Step 4: Add Federated SSO
For external authentication:
-
Configure Custom Identity Providers (SAML or OIDC) under Authentication > Custom IDPs.
-
Map these providers to domains.
-
Enable JIT provisioning to create user accounts automatically when a partner logs in for the first time.
This simplifies enterprise onboarding by removing the need for manual account creation.
Step 5: Customize Branding
Login experiences can be branded for each organization:
-
Upload org-specific logos, color themes, and domain names.
-
Set up **white-labeled login pages **tied to each organization.
-
Configure theme settings per org in the Admin Console.
This ensures each partner sees a familiar, brand-aligned interface.
Step 6: Test and Monitor
Before going live:
-
Walk through onboarding flows for invited and JIT users.
-
Validate authentication paths, MFA enforcement, and role assignment.
-
Monitor login activity and errors via the LoginRadius Audit Logs.
Ongoing visibility into login events helps with security, debugging, and compliance.
For more detailed information, refer to the LoginRadius Technical Documentation.
Gameplan for B2B Identity Management Adoption
The technical architecture is only half the battle.
To make B2B Identity Management work at scale, across orgs, teams, and real-world partner complexity, you need more than APIs and policy configs. You need a strategy.
That means aligning identity infrastructure with your product goals, risk posture, and operational model from day one. Here’s how to build a rollout plan that won’t break the moment you add your tenth partner, or your hundredth.
1. Define Objectives and Scope
Start by identifying who your external users are, what systems they need access to, and how that access should be governed.
Ask:
-
Are we onboarding resellers, enterprise customers, franchisees, or vendors?
-
Do they require SSO, delegated user management, or branded experiences?
-
Which applications or services will they interact with?
This ensures you align identity architecture with actual business use cases, not assumptions.
2. Conduct a Comprehensive Risk Assessment
External access increases your threat surface.
Before rolling out Partner IAM, assess:
-
Data segmentation risks : What happens if a user accesses another org’s data?
-
Authentication vectors : Will some orgs require stronger MFA or passkeys?
-
Lifecycle controls : What’s the deactivation flow when a partner leaves?
Mapping risks early allows you to architect with enforcement, not emergency patches.
3. Develop a Governance Policy for Partners
IAM isn't just about who gets in; it’s about who stays in, who manages access, and how it's audited.
Establish:
-
A delegation model : What roles can partner admins assign, and to whom?
-
A review cadence : How often is access audited or rotated?
-
Escalation procedures : How are permissions elevated, revoked, or reported?
Clear policies reduce ambiguity and ensure access remains correct over time, even as your ecosystem grows.
Developer’s Corner: API Snippets for Partner IAM Integration
1. Create a New Organization
Endpoint : POST /v2/manage/organizations
Sample Request:
1{
2 "organizationName": "Acme Corp",
3 "domains": ["acme.com"],
4 "defaultRole": "org-admin"
5}This API call creates a new organization named "Acme Corp" with the specified domain and assigns a default role.
2. Assign Roles to a User in an Organization
Endpoint : PUT /account/:uid/orgcontext/:orgid/roles
Sample Request:
1{
2 "roles": ["manager", "viewer"]
3}Replace :uid with the user's UID and :orgid with the organization's ID. This assigns the specified roles to the user within the organization.
3. Create a Role
Endpoint : POST /v2/manage/role
Sample Request:
1{
2 "roleName": "org-admin",
3 "description": "Administrator role with full access",
4 "permissions": ["read:data", "write:data"]
5}This creates a new role named "org-admin" with the specified permissions.
4. Create an Organization Connection (e.g., for SSO Integration)
Endpoint : POST /organizations/:orgId/connections
Sample Request:
1{
2 "provider": "SAML",
3 "name": "Acme SSO",
4 "configuration": {
5 "idpEntityId": "https://idp.acme.com/entity",
6 "ssoUrl": "https://idp.acme.com/sso",
7 "certificate": "MIIC...AB"
8 }
9}Replace :orgId with the organization's ID. This sets up a SAML-based SSO connection for the organization.
These code snippets provide practical examples for managing organizations, roles, and SSO integrations using LoginRadius APIs. For more detailed information and additional endpoints, refer to the LoginRadius API Documentation.
FAQs
How can LoginRadius manage multiple partner organizations with different login methods
LoginRadius Partner IAM uses a multi-tenant architecture to manage multiple organizations. Each partner can have separate login methods (SSO, email/password), branding, MFA settings, and access control — all managed centrally without custom development.
What security features does LoginRadius Partner IAM offer
LoginRadius Partner IAM includes:
- Multi-Factor Authentication (MFA)
- Passwordless login options (passkeys, magic links)
- Anomaly detection (login velocity, IP reputation)
- Data encryption at rest and in transit
- Per-org access controls and audit logging
These security features help meet compliance standards like GDPR, SOC 2, and HIPAA.
What is the difference between Partner IAM and Customer IAM?
Partner IAM manages external organizations with delegated administration, federated SSO, and shared access. Customer IAM manages individual users like shoppers or app users. LoginRadius supports both models on one platform for B2B and B2C use cases.
Do partners need a separate LoginRadius account
No. Partners interact directly with your platform. LoginRadius powers authentication, access control, and user management in the background without requiring partners to sign up for LoginRadius separately.
Can LoginRadius Partner IAM scale to thousands of organizations
Yes. LoginRadius Partner IAM is designed for large B2B ecosystems. It supports thousands of partner organizations with isolated authentication flows, multi-tenant scalability, federated SSO, and SCIM provisioning — without increasing management overhead.