Introduction
Refresh tokens don’t fail loudly. They don’t break login flows. They don’t throw visible errors. Most of the time, everything looks perfectly normal and that’s exactly what makes them risky.
In modern authentication, access tokens are intentionally short-lived. They expire quickly, limit exposure, and are treated as disposable. Refresh tokens play a different role. They sit quietly in the background, renewing access tokens and keeping users logged in for days, weeks, or even months without interruption.
Here’s where things start to go wrong.
When a refresh token is stolen, nothing breaks. The system continues to function as designed. The attacker doesn’t need credentials. They don’t need to bypass authentication again. They simply use the refresh token to keep generating new access tokens silently, repeatedly. From the application’s perspective, it all looks legitimate.
This is why many real-world compromises don’t show up as failed logins or brute-force attempts. They hide in long-lived tokens that were never built to defend themselves once copied.
Teams often follow the standard refresh token flow, implement everything correctly, and still run into this problem. Sessions persist longer than expected. Logging out doesn’t fully terminate access. Password resets don’t always help. The refresh token has already moved beyond its original boundary.
At the center of this issue is an assumption that no longer holds: that a refresh token will only be used by the client it was issued to. In real environments browsers, mobile devices, logs, proxies, extensions, backups that assumption breaks more often than we’d like to admit.
Refresh token rotation changes how systems respond to this reality.
Instead of relying on tokens to remain secret, it treats token theft as inevitable. Each refresh token becomes single-use. Every refresh creates a new token. And if an old token appears again, it’s no longer ignored; it becomes a signal.
That’s the real shift.
Refresh tokens stop behaving like silent credentials and start acting like observable security events. Systems gain the ability to detect misuse, limit exposure, and respond immediately rather than discovering issues weeks later during an audit or incident review.
Over 80% of breaches today involve compromised credentials, according to Verizon’s DBIR and in modern systems, those credentials aren’t just passwords anymore they’re tokens.
And once you see how often refresh tokens quietly fail in traditional setups, it becomes clear why rotation is no longer just a best practice, it's the secure pattern modern systems are expected to follow.
What Is a Refresh Token and Why It Exist
A refresh token exists for one reason: to avoid forcing users to log in again every few minutes.
Access tokens are intentionally short-lived. They’re designed to expire quickly so that if one leaks, the damage window stays small. That works well for APIs and backend services, but it creates a terrible user experience if every expiration sends someone back to a login screen.
This is where refresh tokens come in.
A refresh token is a long-lived credential issued alongside an access token. When the access token expires, the client presents the refresh token to the authorization server and receives a new access token in return. No password. No user interaction. Just a quiet renewal in the background.
That separation of short-lived access token and a long-lived refresh token is foundational to modern authentication. It’s also where risk starts to concentrate.
From a token architecture perspective, refresh tokens sit in a privileged position. They don’t call APIs directly, but they can mint unlimited access tokens until they expire or are revoked. In practice, that means a stolen refresh token is more powerful than any single access token it creates.
This is also why refresh tokens are treated differently across application types. In server-side applications, they’re often stored securely on the backend. In mobile apps and browsers, they live closer to the edge inside devices, storage APIs, or secure enclaves. The closer a token lives to the user’s environment, the more likely it is to be copied, leaked, or replayed.
Many teams assume refresh tokens are “safe enough” because they’re not exposed to APIs directly. That assumption doesn’t hold up in real systems. Logs get shipped. Devices get compromised. Extensions overreach. Backups travel to places they shouldn’t.
A refresh token doesn’t need to be used maliciously to become a problem. It only needs to be reused.
Once that happens, the traditional refresh token flow has no way to tell the difference between a legitimate client and a copied token. Both look the same. Both keep working. And that limitation is what refresh token rotation is designed to fix.
Access and Refresh Token: Same System, Very Different Risk
Access tokens and refresh tokens often get discussed together, but they don’t behave the same way and they definitely don’t fail the same way.
An access token is built for speed and scope. It carries the permissions an API needs to make an authorization decision and then it expires. When an access token leaks, the blast radius is limited by time. The clock is already ticking.
A refresh token works on a completely different timeline.
It isn’t meant to be presented to APIs. It isn’t checked for scopes on every request. Instead, it sits behind the scenes with one job: create new access tokens whenever the client asks. As long as it remains valid, it keeps the session alive.
This is why refresh tokens quietly become the most sensitive credential in the system.
In many implementations, the access and refresh token are issued together, stored together, and protected the same way. That’s a mistake. The access token can afford to be disposable. The refresh token cannot. Once it escapes its intended boundary, there’s no natural expiration pressure to force a stop.
Another difference teams often underestimate is visibility. Access token abuse shows up quickly in unexpected API calls, permission errors, and rate limits. Refresh token abuse blends in. Every refresh request looks legitimate. Every response looks normal. Nothing raises a flag.
This is also where a lot of “why didn’t we catch this sooner?” conversations start.
If an attacker gets hold of an access token, they race the expiration timer. If they get a refresh token, they don’t have to rush at all. They can stay quiet. They can refresh on a schedule. They can mirror normal user behavior closely enough to avoid suspicion.
That gap short-lived access, long-lived renewal is intentional. It’s what makes modern authentication usable at scale. But it also means refresh tokens need their own defensive model, not just longer lifetimes and better storage.
Understanding this difference is critical, because refresh token rotation doesn’t exist to protect access tokens. It exists to put guardrails around the one credential that never naturally times out fast enough on its own.
The Standard Refresh Token Flow (And Where It Breaks Down)
On paper, the refresh token flow looks clean and controlled. A user signs in. The application receives an access token and a refresh token. The access token expires quickly, as expected. When that happens, the client sends the refresh token back to the authorization server and gets a fresh access token in return. The user stays logged in. No friction. No drama.
This flow is still widely used because it works until the moment it doesn’t.
The problem is that the refresh token flow assumes something it can’t verify: that the refresh token is being used by the same client it was issued to. There’s no built-in signal that proves the token hasn’t been copied, replayed, or quietly exfiltrated somewhere along the way.
In real systems, refresh tokens travel through more places than teams expect. They pass through mobile OS backups. They sit in browser storage alongside third-party scripts. They end up in crash reports, analytics payloads, and debug logs. None of this requires an attacker to be especially clever. It just requires time and access.
Once a refresh token is copied, the flow stops being exclusive.
The legitimate client keeps refreshing as usual. The attacker does the same. Both present the same refresh token. Both receive valid access tokens. From the authorization server’s point of view, everything looks normal. There’s no reason to suspect misuse because the protocol never asks the server to question reuse.
This is the breaking point.
Traditional refresh token flows are not designed to detect replay. They don’t track lineage. They don’t know which refresh request came first or whether a token has already been used. As long as the token hasn’t expired or been revoked manually, it remains valid.
That’s why revoking access tokens or forcing a logout often doesn’t help. The refresh token survives. The session silently rebuilds itself.
This is also why breaches tied to refresh tokens tend to linger. Days turn into weeks. Sometimes months. By the time someone notices unusual behavior, the token has already done its job far too well.
Token-based session hijacking is one of the fastest-growing attack vectors in web applications.
The standard flow optimizes for continuity, not containment. And without an additional control layer, it has no way to defend itself once the assumption of exclusivity breaks.
Refresh token rotation exists precisely to address this blind spot by changing what happens the moment a refresh token is used.
Refresh Token Rotation: What Changes and Why It Matters
Refresh token rotation starts with a simple idea: a refresh token should not be reusable.
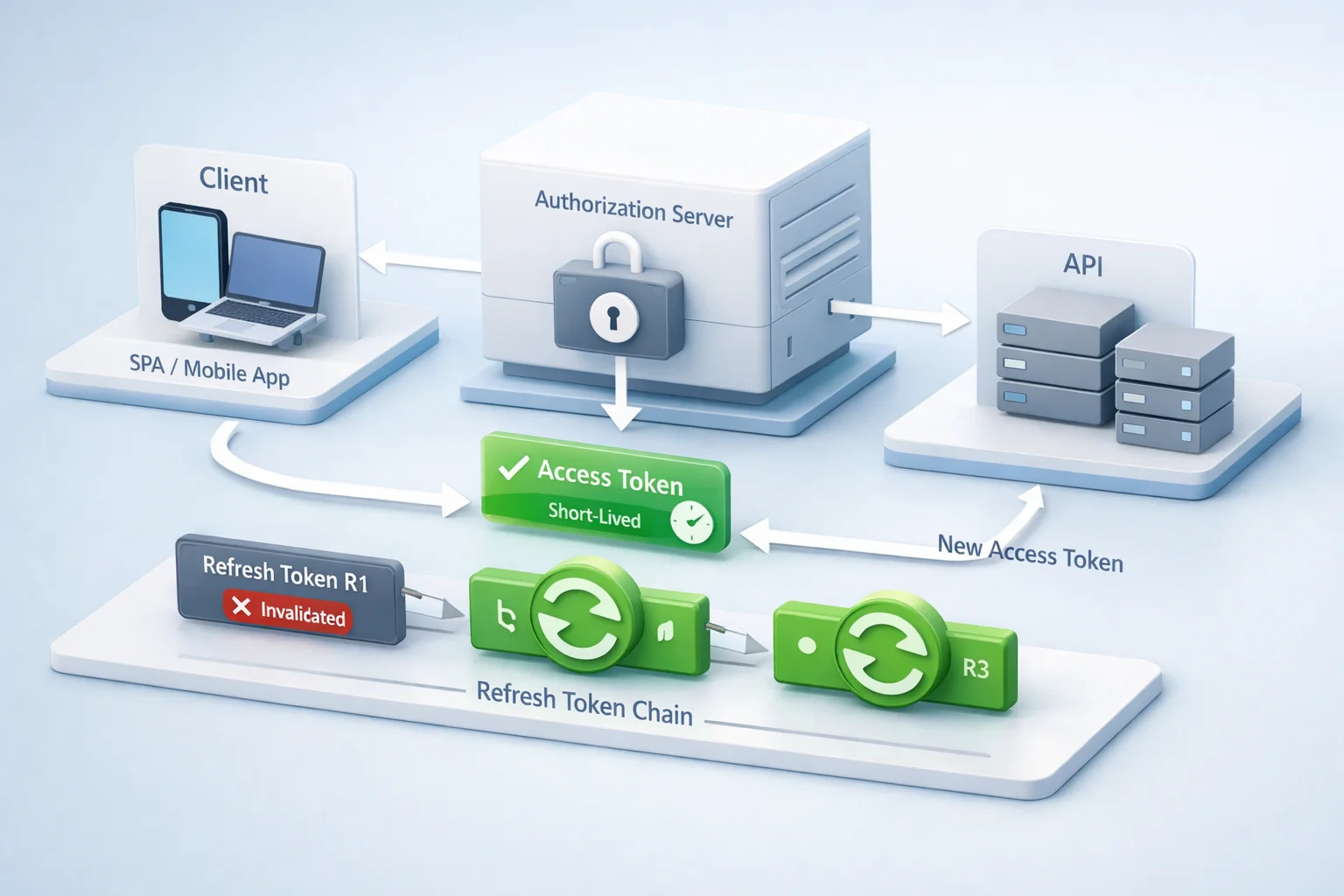
In a rotated setup, every time a client uses a refresh token, the authorization server issues two things in response: a new access token and a brand-new refresh token. The refresh token that was just used is immediately invalidated. It can’t be used again. Not by the original client. Not by anyone else.
This one change alters the entire security model.
In the traditional flow, refresh tokens are static. They live for weeks or months and can be replayed endlessly until they expire or are revoked. With rotation, refresh tokens become single-use credentials. They move forward in a sequence. Each refresh replaces the previous one.
Although both approaches keep users logged in, the risk profile is completely different.
Here’s how rotation shifts the balance. If a refresh token is stolen and an attacker tries to use it after the legitimate client has already refreshed, the server sees something it never saw before: a refresh token that has already been used. That moment is no longer invisible. It’s a signal.
Instead of quietly issuing another access token, the system can react. It can revoke the entire token family, force re-authentication, and cut off access on both sides. What used to be an undetectable replay becomes a clear security event.
This is why modern OAuth guidance treats refresh token rotation as the secure default, especially for public clients like SPAs and mobile apps. These environments can’t reliably protect long-lived secrets, so the protocol compensates by limiting how far a leaked token can go.
Rotation doesn’t pretend token theft won’t happen. It assumes it will and makes sure the damage window collapses quickly when it does.
The important thing to understand is that rotation isn’t just about issuing new tokens more often. Without detection and invalidation, rotation alone doesn’t buy you much. The real value comes from what happens when an old token shows up again.
And that’s where the design gets more interesting because reuse isn’t an edge case. It’s the exact condition refresh token rotation is meant to catch.

Reuse Detection: The Real Reason Refresh Token Rotation Exists
If refresh token rotation is the mechanism, reuse detection is the payoff.
Rotation by itself only limits how long a single refresh token stays valid. Reuse detection is what turns that limit into a security control. It’s the moment the system stops assuming good behavior and starts responding to evidence.
Here’s how reuse actually shows up.
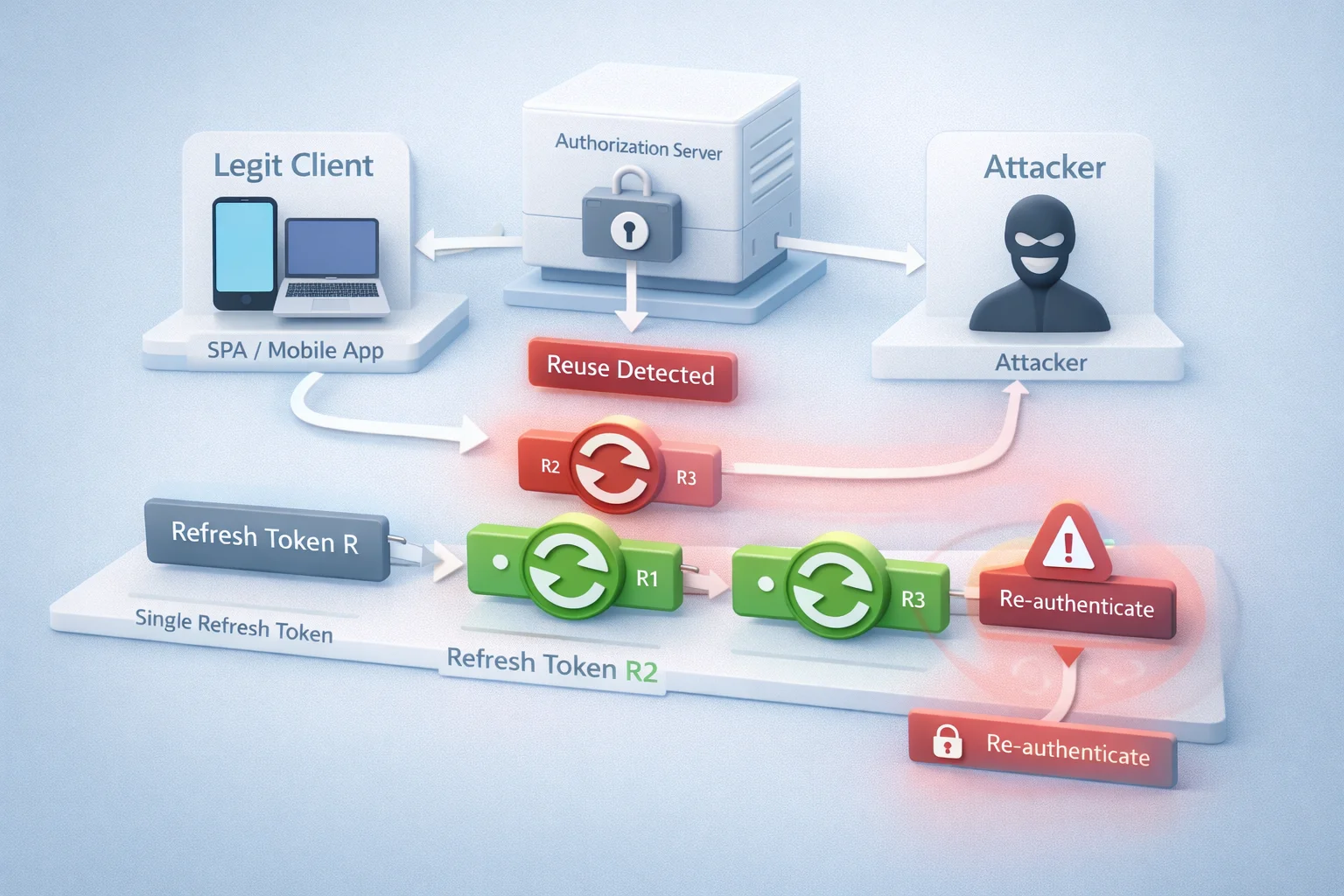
A legitimate client refreshes its access token and receives a new refresh token. A little later, the authorization server receives another refresh request using the previous refresh token. That token should no longer exist. It has already been spent.
At that point, something is wrong.
The server doesn’t need to know who used the token first. It doesn’t need to guess intent. The fact that an invalidated refresh token appeared again is enough. That single signal tells you the token has been copied and is now being replayed.
This is what traditional refresh token flows are blind to. Without rotation, reuse looks normal. With rotation, reuse becomes unmistakable.
Once reuse is detected, the response matters just as much as the detection itself. Well-designed systems treat this as a compromise, not a retry. They revoke the entire refresh token family, invalidate any active access tokens, and require the user to authenticate again. Quietly allowing the flow to continue defeats the purpose.
This is also where teams often hesitate, worrying about false positives. Multiple tabs. Slow networks. Background refreshes colliding. These scenarios do happen, but they’re manageable. Short grace windows, atomic token handling, and clear client retry behavior prevent accidental lockouts without weakening detection.
The key point is this: reuse detection doesn’t rely on guessing attacker behavior. It relies on protocol guarantees. A refresh token that has already been used should never appear again. If it does, the system has learned something important.
Refresh token rotation turns what used to be a silent failure into a visible event. Reuse detection is the reason that visibility matters.
Once you accept that refresh tokens will be copied in the real world, designing for detection stops feeling aggressive. It starts feeling necessary.
Traditional token flows cannot distinguish between legitimate and replayed token usage.
And from there, the question shifts from “should we rotate?” to “how do we do it without breaking everything else?”
JWT Refresh Token Best Practices That Hold Up in Production
This is where theory usually collides with reality.
On paper, refresh tokens are simple. In production, they live inside browsers, phones, networks, and systems that don’t behave politely. The difference between a secure setup and a fragile one often comes down to a few decisions teams don’t revisit after the first implementation.
Let me make this simple. If you’re using JWTs, that doesn’t automatically mean your refresh tokens should be JWTs too.
In fact, most secure systems treat refresh tokens as opaque values. No claims. No scopes. No embedded metadata. Just a random string the authorization server understands. JWT access tokens make sense because APIs need to read them. Refresh tokens don’t. Making them opaque reduces exposure and removes the temptation to trust client-side data.
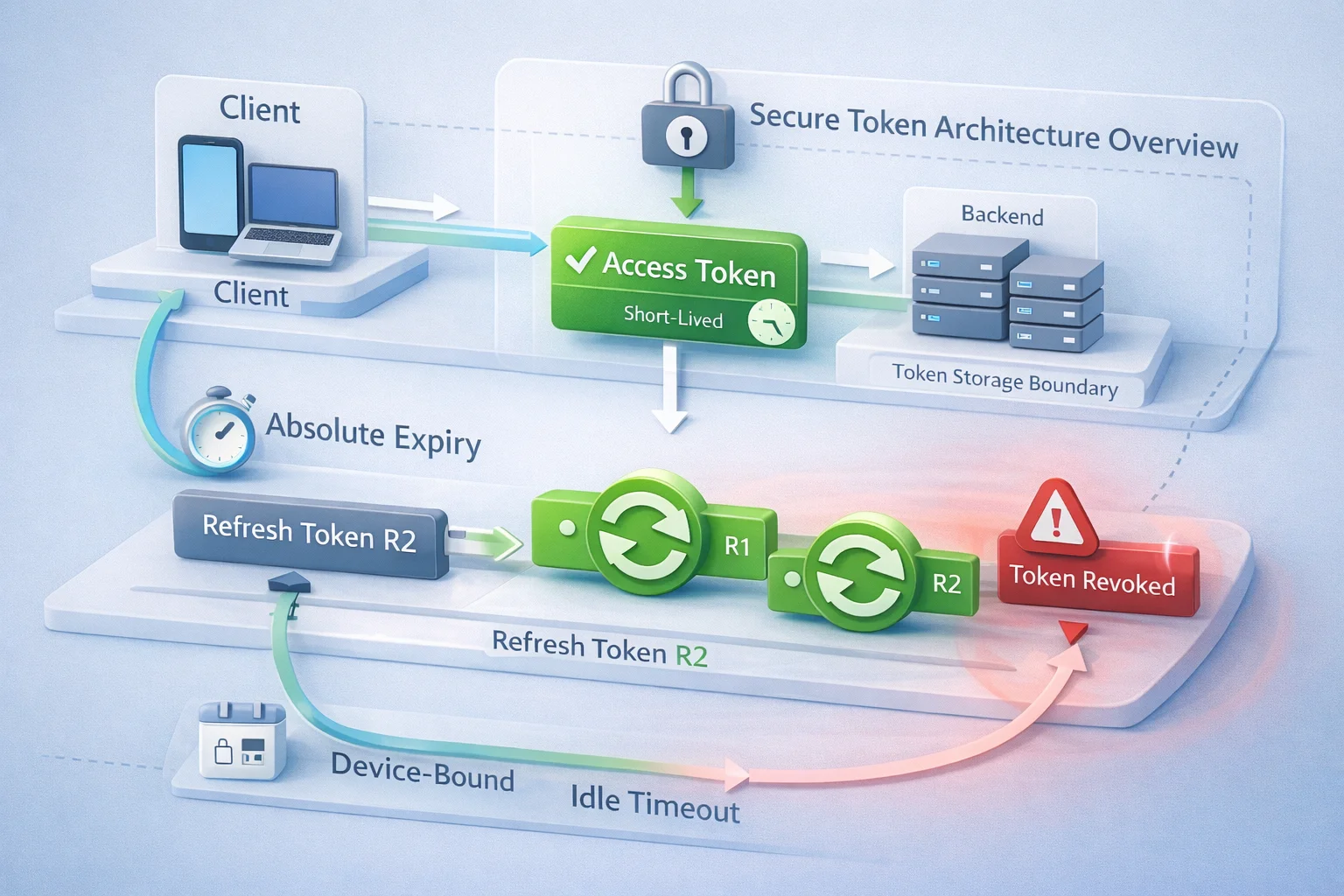
Lifetimes matter more than most teams expect. A refresh token that rotates forever becomes a permanent credential. That’s how silent access sticks around long after a user thinks they’ve logged out.
Strong setups use two limits together: an absolute expiration that never moves, and an idle timeout that resets only when rotation happens normally. Rotation should extend convenience, not immortality.
Storage is another fault line. In browsers, refresh tokens should never touch localStorage. That’s not a best practice it’s damage control. HttpOnly cookies, BFF patterns, or backend-held tokens reduce how often refresh tokens are exposed to scripts and extensions. On mobile, platform-secured storage exists for a reason. If a refresh token is sitting in plain storage, it’s already living on borrowed time.
Concurrency is where many well-intentioned implementations fall apart.
Multiple tabs refresh at once. Mobile apps retry after flaky networks. Background processes wake up unexpectedly. If rotation doesn’t account for this, users get logged out randomly and teams disable rotation to “fix” the problem.
The better approach is controlled tolerance: short reuse grace windows, single-flight refresh logic, and clear retry rules. Enough flexibility to handle real usage, not enough to hide abuse.
One more thing teams often miss: refresh endpoints deserve protection too. Rate limits. Client binding. Basic anomaly checks. A refresh token flow that can be hammered endlessly is an invitation for quiet exploitation.
JWT refresh token best practices aren’t about locking everything down until usability breaks. They’re about accepting how systems actually behave and designing refresh behavior that fails fast, visibly, and safely.
Once these foundations are in place, rotation stops feeling risky. It starts feeling boring. And that’s exactly what you want from something this critical.
JWT Refresh Token Example: Rotation Done the Right Way
Abstract explanations only go so far. The behavior of refresh token rotation makes the most sense when you see what actually changes once rotation is in place.
Let’s look at the difference.
In a non-rotated setup, the client receives a refresh token and keeps using the same one over and over. Every time the access token expires, the refresh token goes back to the authorization server and gets a new access token. If that refresh token is copied at any point, both the legitimate client and the attacker can keep refreshing in parallel. There’s no conflict. There’s no signal. The system never notices.
Now introduce rotation.
The client refreshes its access token using refresh token R1. The server responds with a new access token and a new refresh token R2. At the same time, R1 is marked as spent. It no longer exists as a valid credential.
From this point forward, only R2 should ever appear.
If the legitimate client refreshes again, it presents R2, receives R3, and the chain moves forward. Each refresh token belongs to the same family, but only the newest one is valid at any moment.
Here’s where rotation proves its value.
If an attacker tries to use R1 after the client has already moved on to R2, the authorization server sees an impossible state: a refresh token that has already been used. That’s not a retry. That’s reuse.
A well-designed system treats this as a compromise. It revokes the entire refresh token family, invalidates any access tokens derived from it, and requires the user to authenticate again. Both the attacker and the legitimate client lose access at the same time. The damage stops immediately.
This is the critical difference. Rotation doesn’t just limit exposure it creates a moment where misuse becomes undeniable.
One important detail often overlooked is ordering. The server must handle refresh requests atomically. Only one refresh operation should succeed for a given token. Everything else should fail cleanly and predictably. This is what prevents race conditions from turning into false alarms.
Another subtle point: refresh token rotation doesn’t require refresh tokens to be JWTs. In fact, using opaque values often simplifies this logic. The server tracks state. The client just passes tokens back. There’s no guesswork.
Once you see this flow in action, the purpose of rotation becomes obvious. It’s not about refreshing more often. It’s about making refresh tokens behave like one-time credentials instead of permanent keys.
And when refresh tokens stop behaving like permanent keys, token theft stops being a silent problem.
How to Use Refresh Token Rotation Across Different App Types
Refresh token rotation isn’t a one-size-fits-all switch. The pattern stays the same, but how you apply it depends heavily on where your client runs and how much control you have over its environment.
For browser-based apps, rotation is non-negotiable.
Single-page applications live in hostile territory. Third-party scripts, browser extensions, shared devices there are too many ways for long-lived tokens to escape. This is why modern OAuth guidance treats refresh token rotation as the baseline for SPAs unless you’re using additional protections like sender-constrained tokens. Rotation ensures that even if a refresh token leaks, it can’t be replayed quietly for long.
Mobile apps face a different version of the same problem.
Secure storage helps, but it doesn’t eliminate risk. Devices get backed up. Debug builds leak data. Network conditions trigger retries and race conditions. Rotation works well here as long as concurrency is handled carefully and refresh logic is centralized so the app doesn’t accidentally invalidate itself.
Server-side web applications and BFF architectures sit on more stable ground, but rotation still adds value.
When refresh tokens live on the backend, exposure risk drops but it doesn’t disappear. Logs, internal tooling, and service-to-service calls can still leak credentials. Rotation limits how long a leaked token remains useful and gives you a clear signal if something goes wrong. It also simplifies logout-everywhere and revocation scenarios because tokens don’t linger indefinitely.
Confidential clients deserve a quick reality check.
Yes, they can protect secrets better than public clients. No, that doesn’t make refresh tokens immune to misuse. Rotation isn’t strictly required in every confidential-client setup, but skipping it should be a deliberate choice backed by strong isolation and monitoring not an assumption.
Across all app types, one rule holds: rotation only works when refresh logic is centralized and predictable. If multiple components can refresh independently, you’ll fight false positives and broken sessions. The cleanest implementations treat refresh as a single responsibility with clear ownership.
Once rotation is applied correctly per client type, refresh tokens stop being an afterthought. They become part of a security model that adapts to how real applications are actually used.
Designing Token Architecture That Doesn’t Create Long-Term Risk
Token architecture is where refresh token rotation either quietly succeeds or slowly collapses under its own weight.
You can rotate refresh tokens perfectly and still end up with persistent risk if the surrounding design keeps extending trust without limits. This usually happens when teams focus on individual flows instead of how tokens behave over time.
Start with lifetimes. Access tokens should stay short-lived, no surprises there. Refresh tokens are trickier. If rotation simply pushes the expiration forward on every use, the token never truly ages out. That’s how sessions quietly stretch from days into years.
A healthier model uses two clocks: an absolute lifetime that never moves and an idle timeout that resets only when refresh happens normally. Rotation extends convenience, not existence.
Scope matters too.
Some systems issue a single refresh token per user and reuse it across devices. That feels simpler until one device is compromised and everything has to be torn down. Device-bound refresh tokens reduce blast radius. One stolen token shouldn’t force a global logout unless reuse is detected.
Revocation deserves more attention than it usually gets.
Logging out should mean something. Password resets should mean something. If refresh tokens survive those events, users are left with a false sense of control. A clean architecture ties refresh token families directly into revocation logic so trust can be cut decisively when needed.
Visibility is the last missing piece.
Refresh token events are security events, even when they’re expected. Track issuance, rotation, reuse attempts, revocations, and family invalidations. When something goes wrong, these signals are often the only timeline you have. Without them, incidents turn into guesswork.
Well-designed token architecture doesn’t rely on refresh token rotation alone. It treats rotation as one control inside a system that understands age, scope, ownership, and recovery.
When those pieces line up, refresh tokens stop being long-lived secrets floating in the dark. They become managed credentials with clear boundaries.
And once that structure is in place, the remaining failures tend to come from the same few mistakes patterns teams repeat even when they know better.
Here’s Where Teams Usually Go Wrong
Most refresh token failures aren’t caused by exotic attacks. They come from small, reasonable decisions that stack up over time.
One of the most common mistakes is rotating tokens without actually enforcing reuse detection. A new refresh token is issued, the old one is technically invalid, but nothing meaningful happens if it shows up again. At that point, rotation becomes a ceremony. The system looks modern, but it behaves like the old flow.
Another pattern shows up in token lifetimes. Teams rotate refresh tokens but allow them to live indefinitely. Every successful refresh quietly extends trust. Months pass. Users change devices. Employees leave. The token family keeps going. When something finally goes wrong, there’s no clean cutoff point.
Storage decisions cause more damage than most people admit.
Putting refresh tokens in browser storage because “it’s easier” feels harmless early on. Later, when an extension leaks data or a script behaves badly, there’s no safe rollback. The token has already left the building. At that point, no amount of rotation logic can undo the exposure.
Concurrency issues push teams into bad trade-offs.
Multiple refresh attempts collide, users get logged out, support tickets spike and rotation gets blamed. Instead of tightening the implementation, teams disable reuse detection or add massive grace windows. That fixes UX in the short term and reintroduces silent replay in the long term.
Revocation is often treated as optional.
Logout flows that don’t revoke refresh tokens. Password resets that don’t touch existing token families. Incident response plans that assume sessions will “eventually expire.” These gaps are easy to miss and hard to explain when access persists longer than it should.
None of these mistakes come from ignoring security. They come from underestimating how refresh tokens behave outside controlled environments.
The good news is that these failures are predictable. They show up again and again across systems of all sizes. Once you know where they live, they’re easier to avoid.
And that leads to the final question teams usually ask: how do you roll out refresh token rotation without breaking users, clients, or production systems that already depend on it?
A Practical Path to Rolling Out Refresh Token Rotation
Rolling out refresh token rotation doesn’t require ripping apart your authentication stack. Most teams get stuck because they assume it’s an all-or-nothing switch. It isn’t.
The safest place to start is with public clients, SPAs, and mobile apps, where refresh tokens already live closest to the edge. These are also the environments where silent replay does the most damage. Introducing rotation here gives you immediate risk reduction without touching backend-only flows.
Next, add family tracking and reuse handling before you worry about perfect lifetimes. Even a basic “this token has already been used” check changes the game. It gives you visibility you didn’t have before. From there, you can decide how aggressively to respond to full family revocation, forced re-authentication, or stepped-up verification.
Lifetimes come after detection.
Instead of tuning numbers endlessly, set a clear absolute expiration that never moves and a reasonable idle window that resets only on valid rotation. This alone prevents refresh tokens from becoming permanent credentials. It also makes user expectations easier to manage: sessions last a long time, but not forever.
Concurrency deserves deliberate attention early on.
Before enabling strict reuse enforcement, identify where refresh calls originate. Centralize refresh logic. Add short grace windows where needed. Test multi-tab behavior and flaky network retries. Fixing these upfront prevents the most common “rotation broke my app” complaints.
Finally, wire rotation into your monitoring and support workflows.
Log refresh token issuance, rotation events, reuse attempts, and revocations. Make these visible to the teams that handle incidents and customer support. When a user gets logged out unexpectedly, the reason should be traceable in seconds not guessed after digging through unrelated logs.
The goal isn’t to make refresh tokens perfect. It’s to make them observable, limited, and recoverable.
Once rotation is live and monitored, refresh tokens stop being invisible infrastructure. They become part of your security posture, something you can reason about, audit, and improve over time.
At that point, refresh token rotation stops feeling like a risky change. It starts feeling like overdue hygiene.
And that’s when it becomes clear why this pattern isn’t optional anymore; it's simply how secure token-based systems are expected to work today.
Conclusion
For a long time, refresh tokens sat outside most threat models. They worked quietly, extended sessions reliably, and stayed out of sight. As long as users didn’t get logged out, everything felt fine. That world doesn’t exist anymore.
Modern apps run in browsers full of third-party code, on mobile devices that sync and back up constantly, and across networks that log more than anyone intends. In that environment, long-lived credentials will escape. The only real question is whether your system notices and how fast it reacts when it does.
Refresh token rotation answers that question directly.
It accepts that refresh tokens can be copied and builds the protocol around that reality. Single-use tokens. Lineage tracking. Reuse detection. Clear cutoffs when trust breaks. Instead of hoping refresh tokens stay secret, rotation limits how far a mistake can travel.
What’s changed in recent years isn’t just guidance it’s expectation. OAuth 2.1 direction, browser security models, and real breach patterns all point the same way. Static refresh tokens without detection are no longer a reasonable default, especially for SPAs, mobile apps, and distributed systems.
The good news is that rotation doesn’t require perfect security or heroic rewrites. It works because it’s practical. You can roll it out incrementally. You can tune it. You can observe it. And once it’s in place, refresh tokens stop being silent liabilities and start behaving like managed credentials.
That’s the real shift.
Refresh token rotation isn’t about adding complexity for its own sake. It’s about closing one of the last blind spots in token-based authentication before it closes on you.
FAQs
Q: What is refresh token rotation?
A: Refresh token rotation means issuing a new refresh token every time the old one is used, while immediately invalidating the previous token. This makes refresh tokens single-use and prevents silent replay if a token is copied.
Q: Is refresh token rotation required for all applications?
A: It’s strongly recommended for public clients like SPAs and mobile apps where tokens live close to the user environment. Confidential clients may choose otherwise, but skipping rotation should be a deliberate, well-justified decision.
Q: Do refresh tokens need to be JWTs?
A: No. In most secure setups, refresh tokens are opaque values. JWTs make sense for access tokens that APIs need to read, but refresh tokens don’t benefit from being self-contained.
Q: What happens when a refresh token is reused?
A: A reused refresh token signals possible compromise. Well-designed systems revoke the entire token family and require the user to authenticate again, cutting off both legitimate and malicious access immediately.



