Customer identity is evolving faster than many legacy identity platforms can keep up with. While Ping Identity remains a respected enterprise IAM player, particularly in federation, policy control, and hybrid deployments, many organizations exploring modern CIAM (Customer Identity and Access Management) soon discover friction. Teams navigating B2C, B2B, or citizen-facing workloads frequently report long implementation cycles, dependence on professional services, and a steep learning curve, all of which slow down product shipping and user experience improvements.
As digital businesses scale, the demand for global availability, flexible authentication journeys, low-code orchestration, passwordless methods, and real-time threat protection becomes non-negotiable. This is often the point where teams begin evaluating Ping Identity alternatives that better align with modern CIAM expectations, faster deployment, and simplified development workflows.
In this guide, we evaluate the top Ping Identity competitors across CIAM criteria, summarize common pain points, and outline why many teams ultimately gravitate toward LoginRadius for customer identity modernization.
Evaluation Criteria: What Makes a Great CIAM Platform
Choosing the right CIAM platform requires a framework that goes beyond traditional workforce IAM priorities. Below are the dimensions that most organizations use when assessing alternatives to Ping Identity.
Use Case Fit: CIAM vs Workforce IAM vs Partner IAM
Ping Identity’s heritage is in enterprise workforce IAM, which makes it powerful for internal employee and partner authentication. However, high-volume consumer use cases require:
-
elastic scale during spikes
-
dynamic onboarding flows
-
frictionless user experiences
-
API-first identity interactions
-
multi-tenant B2B controls
A dedicated CIAM platform is designed for customer-facing latency requirements, flexible UX, broad authentication methods, and high-throughput performance, areas where many teams find Ping’s workforce-first design less adaptable.
Security & User Experience
Modern CIAM demands a balance of strong authentication and seamless UX, typically including:
-
Passwordless login and passkeys
-
Adaptive MFA
-
Bot and fraud detection
-
Breached password monitoring
-
Progressive profiling
-
Social login and SSO federation options
Ping Identity supports strong enterprise security controls but often requires custom development or professional services to adapt customer-facing flows. In comparison, leading CIAM platforms offer built-in, low-code orchestration to continuously refine enrollment and login experiences.
Architecture & Performance
Modern CIAM architectures prioritize cloud-native design with:
-
multi-region availability
-
horizontal scalability
-
multi-tenant separation for B2B SaaS
-
real-time SLAs
-
edge-optimized performance
Many organizations evaluating Ping Identity alternatives cite deployment complexity and upgrade cycles as friction points, especially when supporting hybrid or distributed cloud environments. CIAM-native vendors, by contrast, provide managed global infrastructure designed specifically for customer-scale workloads.
Data Residency & Compliance
With increasingly strict privacy laws, CIAM platforms must support:
-
regional data residency choices
-
enterprise-grade privacy controls
-
certifiable compliance frameworks
-
secure data orchestration
Ping offers strong compliance positioning, but its residency options may not match the flexibility required by global consumer applications or region-specific deployments. Alternatives often provide more granular residency selections.
Developer Experience & Integration Effort
This remains one of the most significant factors in CIAM vendor selection. Teams expect:
-
clear documentation
-
robust SDK coverage
-
API-first workflows
-
migration tooling
-
sandbox environments
Ping Identity’s developer experience is commonly described as powerful but complex. The steep learning curve, combined with reliance on professional services, often slows teams working on customer-product timelines. CIAM-native vendors typically simplify this dramatically.
Top 7 Ping Identity Alternatives to Look Out for in 2026
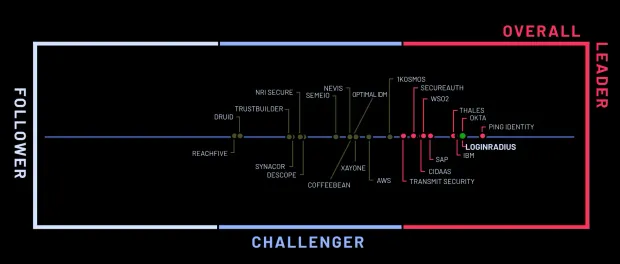
Below are the leading CIAM alternatives based on feature-completeness, implementation agility, security posture, and developer experience, supported by data from your competitor matrix and comparison resources.
1. LoginRadius
LoginRadius is a pure CIAM platform designed for high-volume consumer, citizen, and B2B SaaS identity use cases. Unlike Ping Identity’s workforce-first foundation, LoginRadius was built from day one to support customer traffic patterns, rapidly evolving UX journeys, and flexible developer control.
Where LoginRadius Works Especially Well
-
CIAM-native architecture : Multi-region cloud, high-availability SLAs, and built-in tenant isolation support B2C and B2B SaaS at scale.
-
Rapid deployment : Your team can integrate auth, MFA, social login, progressive profiling, and branded pages without professional services.
-
Broad authentication coverage : Passwords, OTPs, social login, passkeys, federated SSO, adaptive MFA, and device intelligence.
-
Modern security stack : Bot detection, IP throttling, breached password checks, fraud signals, anomaly detection, and DDoS protection, built in, no separate product line.
-
Low/no-code UX orchestration : AI-powered login builders, hosted pages, drag-and-drop flows, and customizable templates.
Ideal For
-
Retail, media, and gaming apps requiring global scale
-
B2B SaaS needing multi-tenant identity
-
Government and public sector needing strict residency
-
Fast-moving digital teams that need identity changes weekly
2. Auth0
Auth0 (Okta Customer Identity Cloud) is a developer-centric CIAM solution widely used by startups, mid-market SaaS companies, and teams that want maximum extensibility via code.
Where Auth0 Performs Well
-
Developer-first flexibility : Rules, actions, hooks, and extensive SDKs allow deep identity customization.
-
Large marketplace ecosystem : Prebuilt integrations for analytics tools, marketing platforms, fraud tools, and enterprise SAML providers.
-
Good for SaaS products : Supports SSO, SAML, and OpenID Connect use cases commonly required by B2B buyers.
CIAM Fit Analysis : Auth0 works well for app builders who want to script identity flows. However, some workloads run into constraints around rate limits or require custom logic to handle large user populations.
Ideal For
-
Early-stage to mid-market SaaS
-
Agile developer teams comfortable writing identity logic
-
Products that rely heavily on third-party integrations
Trade-Offs
-
Pricing escalates aggressively as MAUs, tenants, or extensibility usage increases
-
Rate limits can impact high-volume B2C applications
-
Some enterprise CIAM features require custom development
3. ForgeRock
ForgeRock excels when organizations need hybrid IAM, on-prem integration, or advanced orchestration that blends legacy directories with modern cloud services.
Where ForgeRock Performs Well
-
Highly flexible identity orchestration : Complex attribute mapping, journey logic, and enterprise workflows are capabilities ForgeRock leads in.
-
Hybrid deployment support : Ideal for organizations with existing LDAP directories or regulatory requirements that restrict cloud deployments.
-
Enterprise-grade access management : Strong compliance controls, fine-grained authorization, and robust workforce features.
CIAM Fit Analysis : ForgeRock is significantly more adaptable than other enterprise IAM platforms for CIAM workloads, but usually only when paired with enough engineering and professional services support.
Ideal For
-
Financial institutions modernizing legacy systems
-
Telecom and insurance organizations with mixed cloud/on-prem environments
-
Enterprises with heavy regulatory constraints
Trade-Offs
-
Long deployment cycles
-
Requires specialized technical expertise
-
High total cost of ownership (TCO)
4. Entra ID (Azure AD)
Microsoft’s Entra ID (formerly Azure Active Directory) is widely deployed in IT environments anchored in Microsoft 365 and Azure ecosystems. It is primarily a workforce IAM tool, but some teams consider it for customer identity.
Where Entra ID Performs Well
-
Native Azure integration : Ideal if your organization heavily uses Azure services—monitoring, logging, and RBAC align seamlessly.
-
Strong enterprise security posture : Conditional access, identity governance, and threat detection capabilities are robust.
-
Global infrastructure : Microsoft’s global footprint ensures reliable scale.
CIAM Fit Analysis : Entra ID is not built for customer identity. Creating login journeys, progressive profiling, social login, and modern UX generally requires:
-
custom development
-
Azure AD B2C components
-
multiple Azure services stitched together
This complexity is a primary reason teams ultimately evaluate CIAM platforms rather than extending Entra ID.
Ideal For
-
Organizations standardized on Microsoft
-
Workflows heavily tied to Azure services
-
Internal workforce and partner IAM
Trade-Offs
-
CIAM features require substantial development
-
UX customization is difficult
-
Not optimized for high-volume B2C traffic patterns
5. Amazon Cognito
Cognito appeals to developer teams prioritizing low cost and tight AWS integration. It provides basic authentication and user pool management, but requires significant engineering to achieve CIAM parity.
Where Cognito Performs Well
-
Extremely cost-effective : Cognito is one of the cheapest ways to add authentication to an app.
-
Strong AWS integration : Lambda, API Gateway, DynamoDB, and CloudWatch integrate natively.
-
Simple use cases : Good for straightforward login flows for MVPs or internal apps.
CIAM Fit Analysis : To achieve CIAM-level functionality, social login, progressive profiling, custom journeys, advanced MFA, bot defense, teams must:
-
build custom Lambda code
-
maintain complex workflows
-
design UX themselves
-
solve scaling logic manually
This makes Cognito a high-maintenance option for consumer applications.
Ideal For
-
Developer-heavy teams already deep in AWS
-
MVPs and early-stage apps
-
Internal apps with low complexity
Trade-Offs
-
Very limited out-of-the-box CIAM capabilities
-
Painful migration paths
-
Difficult UI customization
-
No built-in fraud or threat detection
6. Keycloak
Keycloak is a widely adopted open-source IAM and CIAM solution backed by Red Hat. Organizations choose Keycloak for flexibility, cost control, and full ownership of the identity layer.
Where Keycloak Performs Well
-
Open-source extensibility : Teams can modify code, integrate custom identity protocols, and self-host deployments.
-
Broad standards support : SAML, OpenID Connect, OAuth 2.0, fine-grained authorization, and identity brokering.
-
Community modules & plugins : Valuable for teams wanting rapid customization without vendor lock-in.
CIAM Fit Analysis : Keycloak can support CIAM workloads but requires strong DevOps maturity. Scaling, patching, monitoring, and ensuring high availability become internal responsibilities.
Ideal For
-
Organizations avoiding SaaS vendors
-
Teams that need deep protocol customization
-
Privacy-sensitive industries requiring self-hosting
Trade-Offs
-
No official managed cloud (unless using third-party MSAs)
-
Requires engineering teams to manage scaling and uptime
-
Upgrade cycles can be disruptive
7. CyberArk
CyberArk is a leader in privileged access management (PAM) and workforce IAM. Some teams evaluate CyberArk Identity as an alternative to Ping Identity, especially in highly regulated industries.
Where CyberArk Performs Well
-
Enterprise identity security : CyberArk is unmatched in privileged access and internal identity threat protection.
-
Compliance-driven workflows : Ideal for industries needing elevated access controls and governance.
-
Strong MFA and SSO : Covers foundational authentication needs for internal and partner identity.
CIAM Fit Analysis : CyberArk is not built for high-volume customer identity. Supporting CIAM-scale journeys, social login, UX flows, and global traffic patterns often requires significant customization, or simply isn't feasible.
Ideal For
-
Enterprise workforce IAM
-
Privileged identity use cases
-
Compliance-heavy environments (finance, defense, healthcare)
Trade-Offs
-
Limited CIAM features
-
Not suitable for consumer-scale identity
-
Heavy overhead for B2B SaaS or digital product teams
Why People Switch From Ping Identity to LoginRadius
Below are the most common reasons companies tell us they explore moving from Ping Identity to LoginRadius:
1. Deployment Speed and Complexity
Many teams experience months-long implementation cycles, often requiring professional services. This slows down modernization initiatives and introduces operational dependencies. LoginRadius, by contrast, deploys in under a month and does not depend on pro-services to get started.
2. Steep Learning Curve and Engineering Overhead
Teams frequently report that Ping Identity is powerful but difficult to configure, especially for CIAM use cases requiring flexible journeys and frequent UX updates. LoginRadius simplifies this with intuitive no-code builders and an API-first architecture.
3. Friction Integrating With Modern Environments
Because Ping Identity grew out of enterprise workforce IAM, adapting the platform for customer-scale traffic, multi-tenant B2B SaaS, or rapidly evolving product needs often requires custom work. LoginRadius provides CIAM-native features out of the box.
4. Need for Simpler, User-Friendly CIAM Experiences
Several customers highlight that Ping’s interface and workflows are not optimized for non-technical teams. LoginRadius’ UI and no-code capabilities allow product, marketing, and CX teams to modify journeys without heavy engineering.
5. Stronger Built-In Threat Protection
LoginRadius includes adaptive MFA, bot defense, breach detection, and DDoS protection natively, whereas implementing similar controls in Ping often requires additional modules or engineering effort.
These patterns are reinforced by sentiment captured in your uploaded unhappiness data: difficulty integrating with existing systems, reliance on professional services, documentation gaps, and the perception that Ping is being outpaced by competitors offering more modern, user-friendly CIAM capabilities.
Ping Identity vs LoginRadius: Feature Comparison Table
| Capability | LoginRadius | Ping Identity |
|---|---|---|
| Deployment Time | Under 1 month | Often requires months + professional services |
| CIAM Specialization | Full CIAM platform | Primarily workforce IAM |
| Passwordless & Passkeys | Built-in | Requires configuration and add-ons |
| Social Login | Native + 40+ providers | Supported with configuration |
| Adaptive MFA | Built-in | Available but complex |
| Bot & Fraud Detection | Built-in | Requires add-ons or customization |
| No-Code Journey Builder | Yes | Limited; requires technical setup |
| Global Data Centers | Multi-region, flexible | Regional but less granular |
| Multi-Tenant B2B | Native | Requires architecture work |
| Support Model | CIAM-specialized with fast response | Enterprise support, variable experience |
Conclusion and Next Steps
Ping Identity remains a respected leader in traditional IAM, especially for enterprises managing workforce or partner access. However, CIAM initiatives require a different architectural approach, one that prioritizes developer agility, seamless customer experiences, rapid deployment, and flexibility for global digital products.
Organizations exploring Ping Identity alternatives typically seek:
-
faster implementation
-
simpler configuration
-
lower operational overhead
-
modern authentication experiences
-
CIAM-native security features
-
global scalability with data residency options
LoginRadius consistently emerges as a strong contender because our platform is purpose-built for customer identity. We partner closely with teams who want to accelerate product delivery, enhance security, and streamline authentication without complex professional service dependencies.
If you're evaluating Ping Identity alternatives, our team can help you:
-
Map your CIAM requirements
-
Review architectural options
-
Provide a personalized technical demo
-
Explore migration processes and timelines
Explore our documentation, or speak to our engineers about your identity roadmap. Together, we can design a customer identity foundation that supports long-term growth and digital innovation.



