Customer identity strategies have shifted dramatically in recent years. Passwordless authentication, biometric login, adaptive risk scoring, and identity orchestration are no longer experimental capabilities — they’re baseline expectations.
Transmit Security has positioned itself as a passwordless-first CIAM and identity orchestration platform, particularly strong in financial services and high-security environments. Its focus on FIDO-based authentication, fraud prevention, and AI-driven orchestration appeals to enterprises prioritizing credential-less login experiences.
However, as organizations scale digital ecosystems — especially across B2C, B2B SaaS, and multi-tenant environments — many teams begin evaluating Transmit Security alternatives. Common evaluation triggers include deployment complexity, broader CIAM feature depth, B2B tenant management, developer tooling maturity, global data residency flexibility, and total cost of ownership.
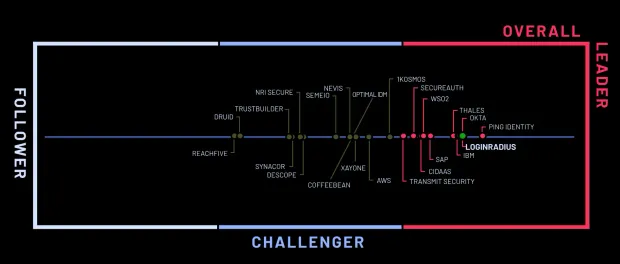
In this guide, we evaluate the top Transmit Security competitors across core CIAM criteria and explain why many organizations ultimately shortlist LoginRadius when modernizing customer identity.
Evaluation Criteria: What Makes a Great CIAM Platform
When evaluating alternatives to Transmit Security, we recommend using a structured CIAM-focused framework rather than workforce IAM criteria.
Use Case Fit: CIAM vs Workforce IAM vs B2B/Partner IAM
Transmit Security is primarily focused on passwordless CIAM and fraud prevention. But identity use cases vary widely:
-
High-volume B2C platforms (retail, gaming, media)
-
Multi-tenant B2B SaaS applications
-
Citizen and public sector portals
-
Partner ecosystems
-
Hybrid consumer + workforce environments
A modern CIAM platform must support:
-
Elastic scaling during traffic spikes
-
Tenant-level isolation for B2B SaaS
-
Progressive profiling and flexible onboarding
-
API-first identity for microservices architectures
Platforms built purely around authentication innovation may not fully address tenant modeling, SaaS onboarding workflows, or global enterprise deployment requirements.
Security & User Experience
Modern CIAM demands both security and frictionless UX, including:
-
Passwordless authentication and passkeys
-
Adaptive MFA
-
Risk-based authentication
-
Bot and fraud detection
-
Breached password monitoring
-
Device intelligence
Transmit Security is strong in passwordless and identity proofing. However, some organizations seek a broader security stack bundled natively rather than relying on orchestration layers or additional services.
Architecture & Performance
Enterprise CIAM architectures should prioritize:
-
Cloud-native multi-region infrastructure
-
Horizontal scalability
-
SLA-backed uptime
-
Multi-tenant separation
-
Low-latency global performance
Organizations handling millions of customer logins per day often evaluate alternatives based on real-world throughput, managed infrastructure support, and operational simplicity.
Data Residency & Compliance
Regulated industries increasingly require:
-
Region-specific data hosting
-
GDPR, SOC 2, ISO certifications
-
Financial services and healthcare compliance controls
-
Granular data privacy management
Flexibility in data residency options is often a deciding factor in global CIAM initiatives.
Developer Experience & Integration Effort
Engineering teams prioritize:
-
Clear documentation
-
Mature SDKs
-
RESTful APIs
-
Terraform/CI-CD support
-
Sandbox environments
-
Migration tooling
Platforms that require heavy professional services or orchestration complexity can slow product teams operating on rapid release cycles.
Top 7 Transmit Security Alternatives
Below are the most relevant CIAM competitors based on scalability, feature completeness, B2B readiness, developer experience, and architectural maturity.
1. LoginRadius – Best for Enterprise-Scale CIAM with Built-In B2B
LoginRadius is a pure CIAM platform purpose-built for high-volume consumer identity and multi-tenant B2B SaaS use cases.
Where LoginRadius Works Especially Well
-
CIAM-native architecture: Multi-region cloud, high-availability SLAs, and built-in tenant isolation support B2C and B2B SaaS at scale.
-
Rapid deployment: Your team can integrate auth, MFA, social login, progressive profiling, and branded pages without professional services.
-
Broad authentication coverage: Passwords, OTPs, social login, passkeys, federated SSO, adaptive MFA, and device intelligence.
-
Modern security stack: Bot detection, IP throttling, breached password checks, fraud signals, anomaly detection, and DDoS protection, built in, no separate product line.
-
Low/no-code UX orchestration: AI-powered login builders, hosted pages, drag-and-drop flows, and customizable templates.
Ideal For
-
Retail, media, and gaming apps requiring global scale
-
B2B SaaS needing multi-tenant identity
-
Government and public sector needing strict residency
-
Fast-moving digital teams that need identity changes weekly
2. Auth0 – Best for Developer-Driven Customization
Auth0 is widely adopted for its developer-first extensibility and flexible identity logic.
Where it works well
-
Extensive SDK ecosystem
-
Rules, hooks, and Actions for customizable flows
-
Strong marketplace integrations
-
Good fit for SaaS platforms needing SAML and OIDC federation
Where it can fall short
-
Pricing scales aggressively with MAUs and feature usage
-
Rate limits can affect high-volume B2C
-
Some enterprise B2B features require custom engineering
3. Okta Customer Identity Cloud – Best for Enterprise Ecosystems
Okta (including Customer Identity Cloud) provides enterprise-grade IAM capabilities.
Where it works well
-
Strong enterprise trust and compliance posture
-
Broad federation and SSO capabilities
-
Deep integration ecosystem
Where it can fall short
-
Workforce-first heritage
-
CIAM features sometimes feel bolted onto enterprise IAM
-
Higher operational complexity
4. ForgeRock – Best for Regulated & Hybrid Enterprises
ForgeRock is often chosen by banks and telecom providers requiring hybrid IAM.
Where it works well
-
Advanced identity orchestration
-
On-prem + hybrid deployment flexibility
-
Fine-grained authorization controls
Where it can fall short
-
Long implementation timelines
-
Heavy reliance on specialized engineers
-
Higher total cost of ownership
5. Microsoft Entra ID – Best for Microsoft-Centric Organizations
Microsoft Entra ID (formerly Azure AD) is deeply integrated into the Microsoft ecosystem.
Where it works well
-
Strong conditional access
-
Seamless Azure integration
-
Enterprise governance features
Where it can fall short
-
Not purpose-built for CIAM
-
Requires stitching together Azure AD B2C components
-
Limited UX flexibility for consumer flows
6. Amazon Cognito – Best for AWS-Native Development
Amazon Cognito provides basic authentication services within AWS.
Where it works well
-
Cost-effective for MVPs
-
Native AWS integration
-
Simple user pool management
Where it can fall short
-
Limited out-of-the-box CIAM features
-
Requires custom Lambda development
-
No built-in fraud or orchestration layer
7. Keycloak – Best Open-Source Identity Platform
Keycloak is an open-source IAM and CIAM platform.
Where it works well
-
Full control over deployment
-
Standards-based (SAML, OAuth, OIDC)
-
No licensing costs
Where it can fall short
-
Self-managed scaling and maintenance
-
No built-in managed SaaS
-
Operational overhead for large-scale deployments
Why People Switch From Transmit Security to LoginRadius
Across enterprise evaluations, several themes consistently emerge.
1. Need for Broader CIAM Capabilities
Transmit Security excels in passwordless innovation. However, organizations often require:
-
Social login ecosystems
-
Progressive profiling
-
Flexible branded experience layers
LoginRadius provides these natively rather than layering them on top of orchestration frameworks.
2. Deployment Complexity and Engineering Overhead
Some teams report that implementing advanced orchestration logic and integrating fraud components requires significant engineering effort. This can slow digital product releases.
LoginRadius offers a no-code orchestration builder and API-first architecture that allows faster implementation without professional services dependency.
3. Global Scale & SLA Guarantees
High-volume consumer platforms prioritize predictable SLAs and region-specific hosting. LoginRadius’ CIAM-native infrastructure is built specifically for consumer-scale workloads.
4. Total Cost of Ownership
Organizations comparing platforms often consider:
-
Licensing structure
-
Engineering resources required
-
Maintenance overhead
-
Integration complexity
LoginRadius aims to simplify identity delivery with bundled capabilities rather than modular add-ons.
Compare Transmit Security vs LoginRadius in detail to evaluate feature coverage, B2B readiness, passwordless support, and deployment models.
Conclusion
Transmit Security has pushed the market forward in passwordless authentication and identity orchestration. For financial institutions and security-first enterprises, its approach can be compelling.
However, many organizations expanding into multi-tenant SaaS, high-volume B2C platforms, or globally distributed applications require broader CIAM functionality, simplified deployment, and stronger B2B identity modeling.
When evaluating Transmit Security alternatives, focus on:
-
Use case alignment
-
Architectural scalability
-
Developer experience
-
Built-in security coverage
-
Total operational overhead
LoginRadius consistently emerges as a strong contender because we are purpose-built for customer identity at scale — not retrofitted from workforce IAM or authentication-only frameworks.
If you’re evaluating Transmit Security competitors, our team can:
-
Map your CIAM requirements
-
Review architecture trade-offs
-
Demonstrate migration pathways
-
Provide a tailored technical walkthrough
Explore our documentation or schedule a technical consultation with our identity architects to determine whether LoginRadius aligns with your long-term customer identity roadmap.



