Thales (SafeNet Trusted Access) vs IBM Security Verify
Which One Is A Better Workforce IAM?
Read on to find out what they reveal:
- Thales (SafeNet Trusted Access)'s Strong Authentication & HSM Focus makes them a fan favorite.
- IBM Security Verify offers Integration with IBM Ecosystem & Customization.
- Thales (SafeNet Trusted Access) suits best for Enterprise, whereas IBM Security Verify has target audience in Large Enterprise.( Link )
INDUSTRY LEADER
Industry Analysts pick Thales (SafeNet Trusted Access) over IBM Security Verify
By the way, if you are looking for a CIAM platform, do explore LoginRadius, which has been recognized as an overall leader by Kupingercole, ahead of Thales (SafeNet Trusted Access)!
Your Peers pick Thales (SafeNet Trusted Access) over IBM Security Verify
ProsDeep External integrationsSecurity and reliabilitySSO
ConsExpensive and MAU Traps
ProsIntegration with M365SecurityIdentity Governance and SSO
ConsExpensive and external integration issues
When we were looking for an customer identity management platform, we tried a lot of big companies. Of which some were too expensive, and some were not feature-rich enough. We needed something that was as powerful as it was cost-effective. That’s when we found LoginRadius, and it was kind of exactly that right fit—easy to use, feature-rich, and had reasonable pricing.

Why Organizations Choose LoginRadius for CIAM

Purpose-built CIAM

Expert Support - NOT Outsourced!
Developer-Supported Deployment

Flexible Partnership
We believe that the best CIAM platform is one that is purpose-built for your use cases and can help your developers go-to market quickly. See for yourself.
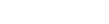
Feature-by-Feature Comparison
Category
Parameter