Risk-Based Authentication on Amber app
Implement Risk-Based Authentication Authentication/Login on your Amber App using LoginRadius
 Amber
Amber
 Risk-Based Authentication
Risk-Based AuthenticationBuilt for Developers
Performs for Enterprise Scale!
Try our platform for free or talk to our CIAM expert to book a customer demo.
1.5B+
Identities
28+
Data Centers
100%
Uptime
200,000
RPS Scaling
Start Risk-Based Authentication Implementation Using LoginRadius Admin Console
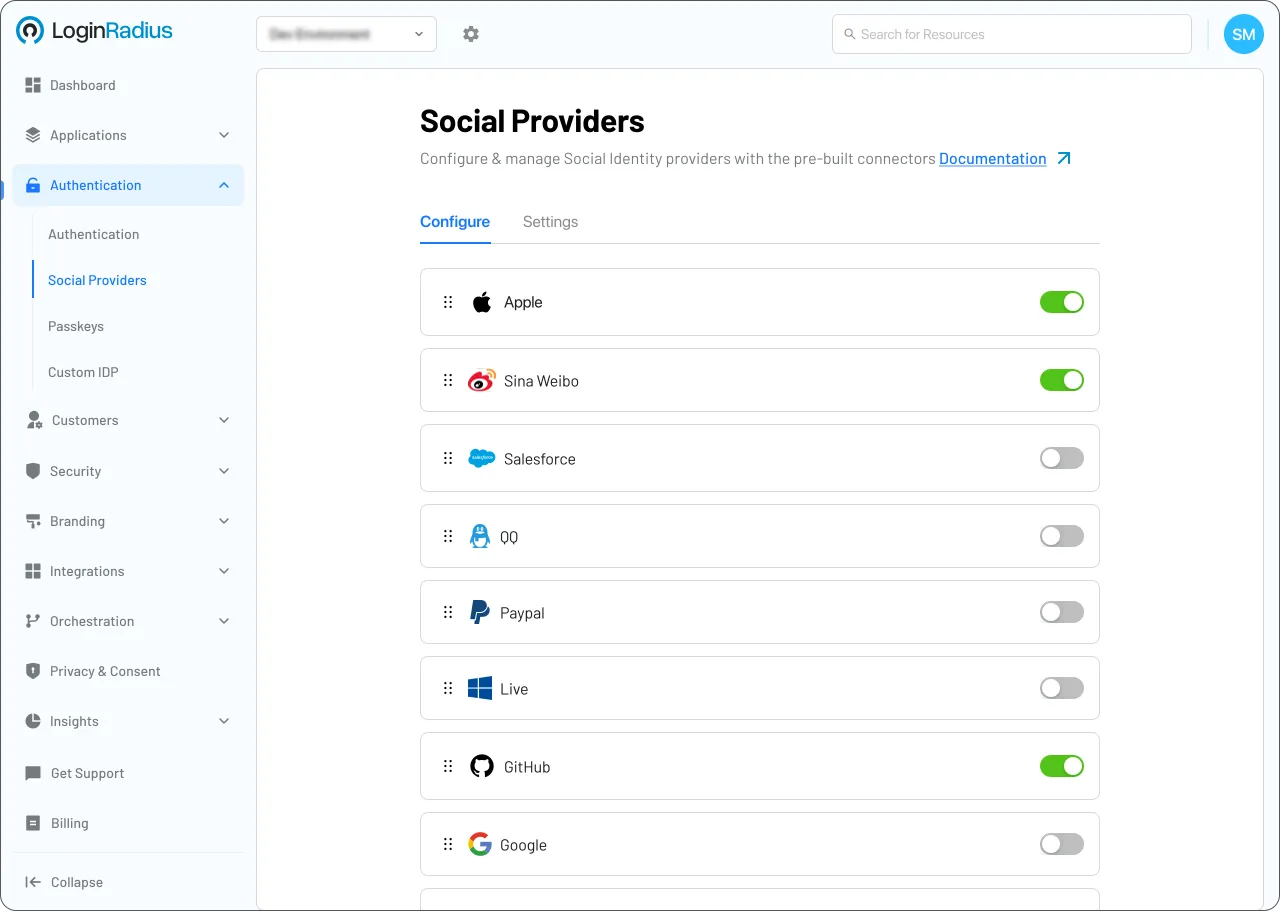
1
Go to Security > Attack Protection > Risk-Based Authentication.
2
Click the Enable toggle.
3
Select the risk factors to track (IP, Browser, City, or Country).
Trusted by Developers
From Startups to Fortune 500 Companies






Interactive Resources
You might also be interested in
Risk-Based Authentication on other appsOther features for your Amber apps
Social Identity Providers for your Amber apps