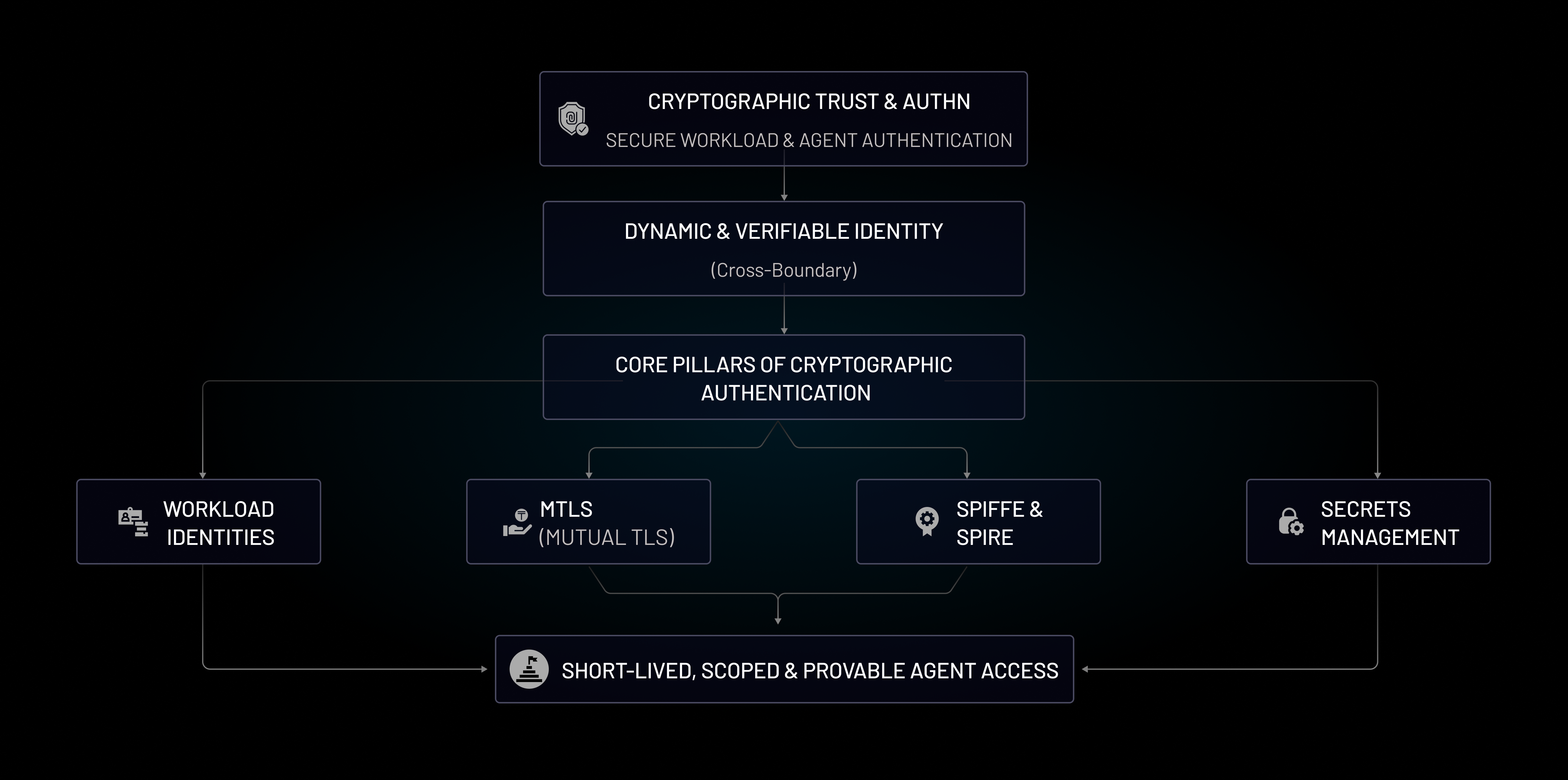
Cryptographic Trust & AuthN: Modern Foundation for Agentic IAM
As agentic systems move from experimentation to production, trust can no longer be assumed it must be cryptographically proven. Every agent, workload, API, and service must be verifiable, scoped, and continuously authenticated.

What is Cryptographic Trust & AuthN in Agentic IAM?
Cryptographic Trust & AuthN verifies identities using cryptographic proof (certificates, signed JWTs, and time-bound tokens) rather than reusable secrets. In agentic systems, authentication is continuous and every action is verifiably attributable.
Why Cryptographic AuthN Matters for Agentic IAM
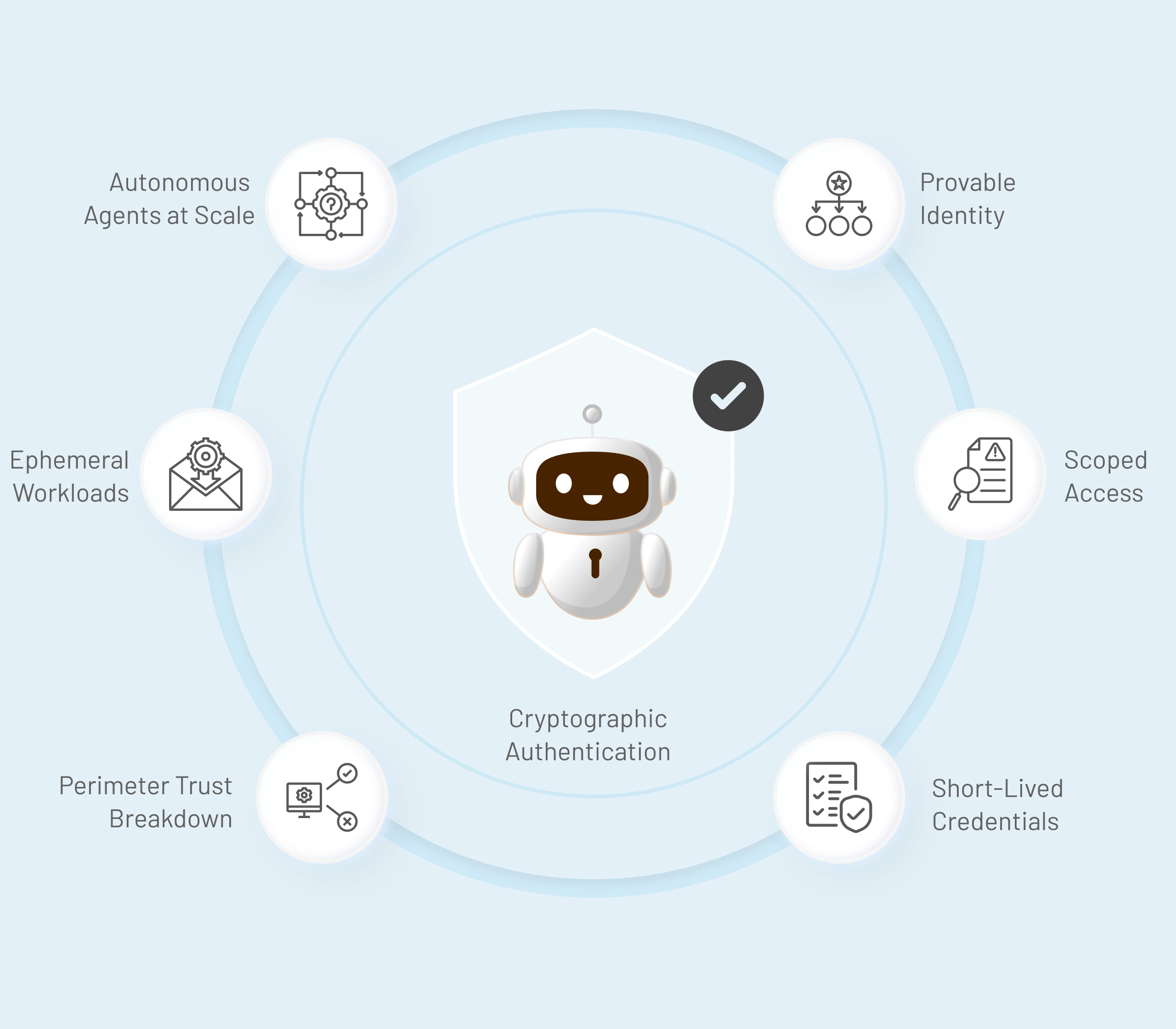
Agentic systems introduce unique trust challenges:
- Agents run autonomously and at scale
- Workloads are ephemeral and dynamic
- Traditional perimeter-based trust breaks down
Without cryptographic authentication:
- Agents rely on long-lived secrets that leak
- Identity becomes implicit instead of enforced
- Token misuse and privilege creep go undetected
- Breaches propagate silently across systems
Cryptographic AuthN replaces fragile trust with provable identity, scoped access, and short-lived credentials designed for automation-first environments.
Core pillars of Cryptographic Trust & AuthN
Trust Pillar
What It Covers
Why It Matters
What It Covers
Cryptographically verifiable identities for agents, services, and workloads instead of shared secrets or static credentials.
Why It Matters
Ensures every agent action is tied to a provable identity, not an implicit trust assumption.
Cryptographically verifiable identities for agents, services, and workloads instead of shared secrets or static credentials.
Ensures every agent action is tied to a provable identity, not an implicit trust assumption.
What It Covers
Two-way authentication, where both client and server validate each other using certificates before communication.
Why It Matters
Prevents unauthorized service-to-service or agent-to-API calls while securing communication in transit.
Two-way authentication, where both client and server validate each other using certificates before communication.
Prevents unauthorized service-to-service or agent-to-API calls while securing communication in transit.
What It Covers
Standards-based workload identity documents are issued dynamically across environments without embedding secrets.
Why It Matters
Enables consistent, portable identity for agents across clouds, clusters, and runtimes.
Standards-based workload identity documents are issued dynamically across environments without embedding secrets.
Enables consistent, portable identity for agents across clouds, clusters, and runtimes.
What It Covers
Secure storage, rotation, and controlled access to credentials, keys, and sensitive configuration.
Why It Matters
Reduces secret sprawl and minimizes blast radius when credentials are compromised.
Secure storage, rotation, and controlled access to credentials, keys, and sensitive configuration.
Reduces secret sprawl and minimizes blast radius when credentials are compromised.
What It Covers
Short-lived, scoped credentials are issued only for the duration of a task or interaction.
Why It Matters
Limits exposure by design and prevents long-lived credentials from being abused.
Short-lived, scoped credentials are issued only for the duration of a task or interaction.
Limits exposure by design and prevents long-lived credentials from being abused.
What It Covers
Secure generation, signing, validation, and expiry of authentication tokens.
Why It Matters
Ensures tokens cannot be replayed, forged, or misused outside their intended scope.
Secure generation, signing, validation, and expiry of authentication tokens.
Ensures tokens cannot be replayed, forged, or misused outside their intended scope.
What It Covers
Continuous rotation, expiration, revocation, and monitoring of cryptographic credentials.
Why It Matters
Maintains long-term trust and prevents stale or orphaned credentials from becoming attack vectors.
Continuous rotation, expiration, revocation, and monitoring of cryptographic credentials.
Maintains long-term trust and prevents stale or orphaned credentials from becoming attack vectors.