Intent-Based Authorization – What, How, Why, When
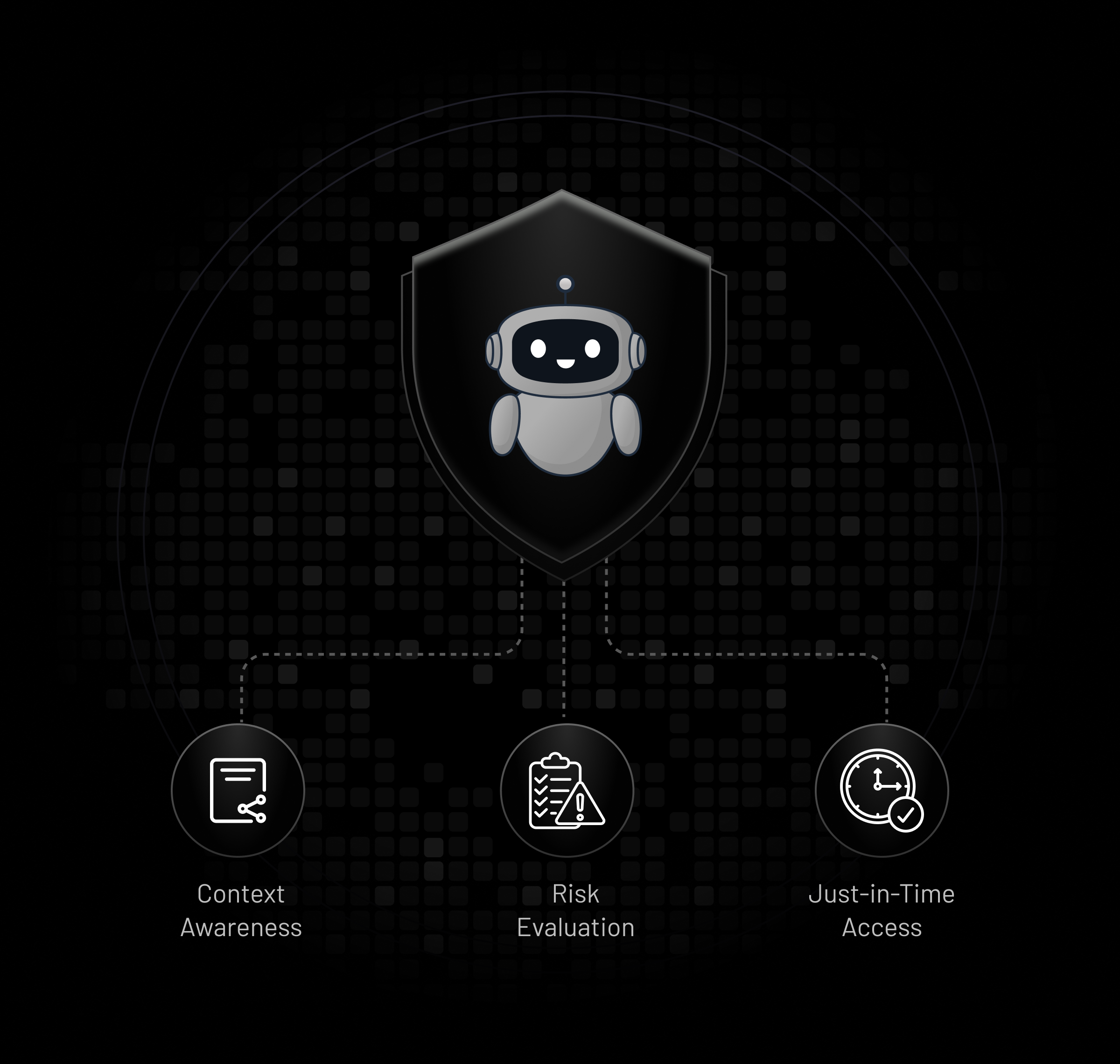
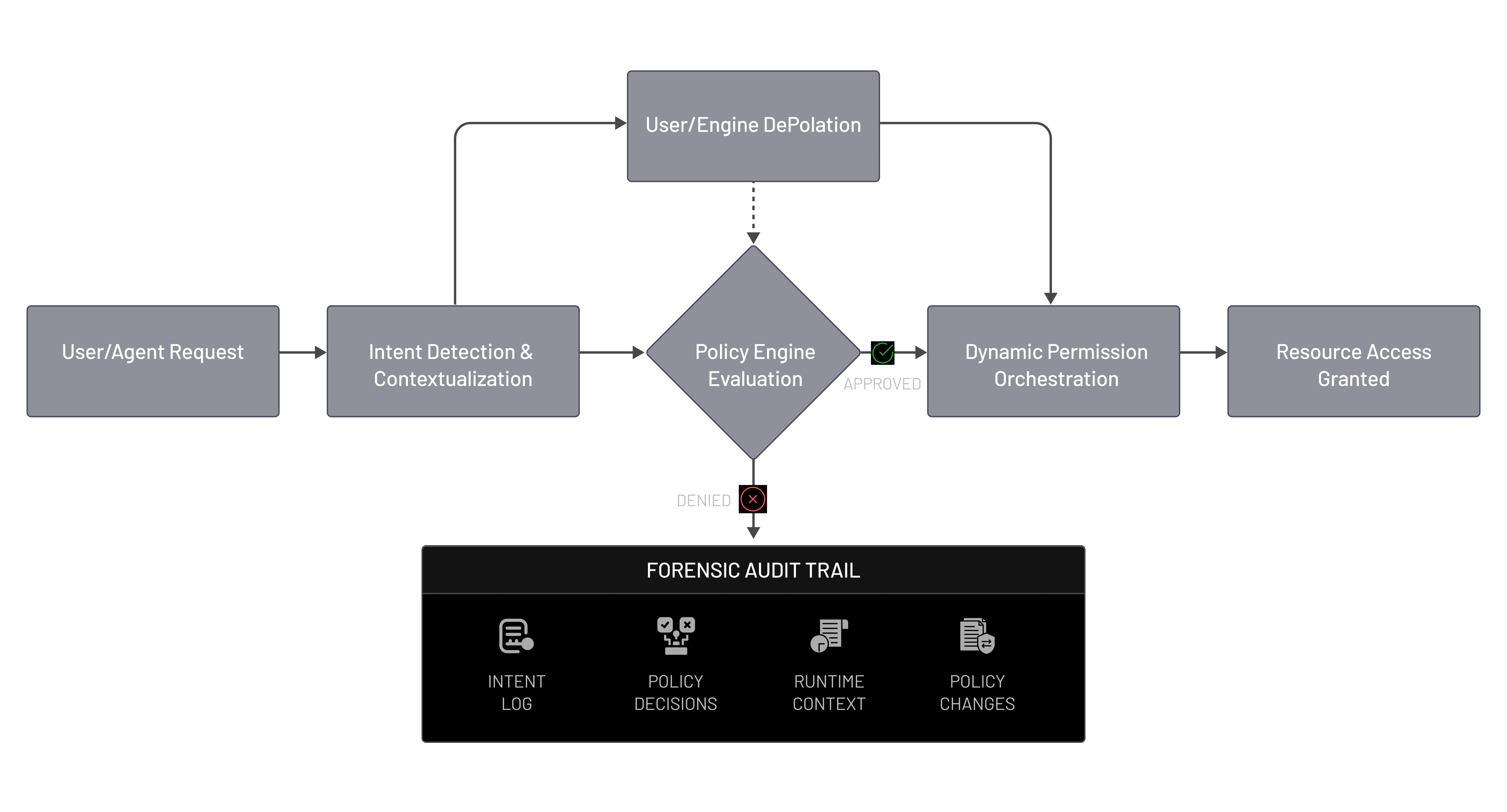
In Agentic IAM, where autonomous agents act continuously across systems, static authorization models fall short. Intent-based authorization introduces policy intelligence that evaluates context, purpose, risk, and constraints in real time—ensuring agents receive just enough access, only when needed.
What Is Intent-Based Authorization in Agentic IAM?
Intent-Based Authorization shifts access decisions from fixed roles to intent, context, and policy logic. In agentic systems, identities extend beyond users to include agents, services, and automations, with every action evaluated based on intent, task scope, context, and active policies—enabling fine-grained, adaptive access control with strong governance and auditability.
Core Pillars of Intent-Based Authorization
Authorization Pillar
What It Covers
Why It Matters
What It Covers
Transition from RBAC to ABAC/PBAC, contextual attributes, and policy-driven access decisions.
Why It Matters
Enables precise control for agents whose permissions cannot be predefined by static roles.
Transition from RBAC to ABAC/PBAC, contextual attributes, and policy-driven access decisions.
Enables precise control for agents whose permissions cannot be predefined by static roles.
What It Covers
Expression of “why” an action is requested, mapped to allowable outcomes.
Why It Matters
Prevents over-privileged access by aligning permissions with declared purpose.
Expression of “why” an action is requested, mapped to allowable outcomes.
Prevents over-privileged access by aligning permissions with declared purpose.
What It Covers
Time-bound, scope-limited, and task-specific permissions.
Why It Matters
Reduces blast radius and limits long-lived or excessive agent privileges.
Time-bound, scope-limited, and task-specific permissions.
Reduces blast radius and limits long-lived or excessive agent privileges.
What It Covers
Real-time authorization decisions based on live signals and constraints.
Why It Matters
Ensures access adapts to changing conditions, risk, and execution context.
Real-time authorization decisions based on live signals and constraints.
Ensures access adapts to changing conditions, risk, and execution context.
What It Covers
Policy versioning, evaluation logs, and decision traceability.
Why It Matters
Provides accountability, explainability, and compliance readiness.
Policy versioning, evaluation logs, and decision traceability.
Provides accountability, explainability, and compliance readiness.