Interoperability & Agent Mesh
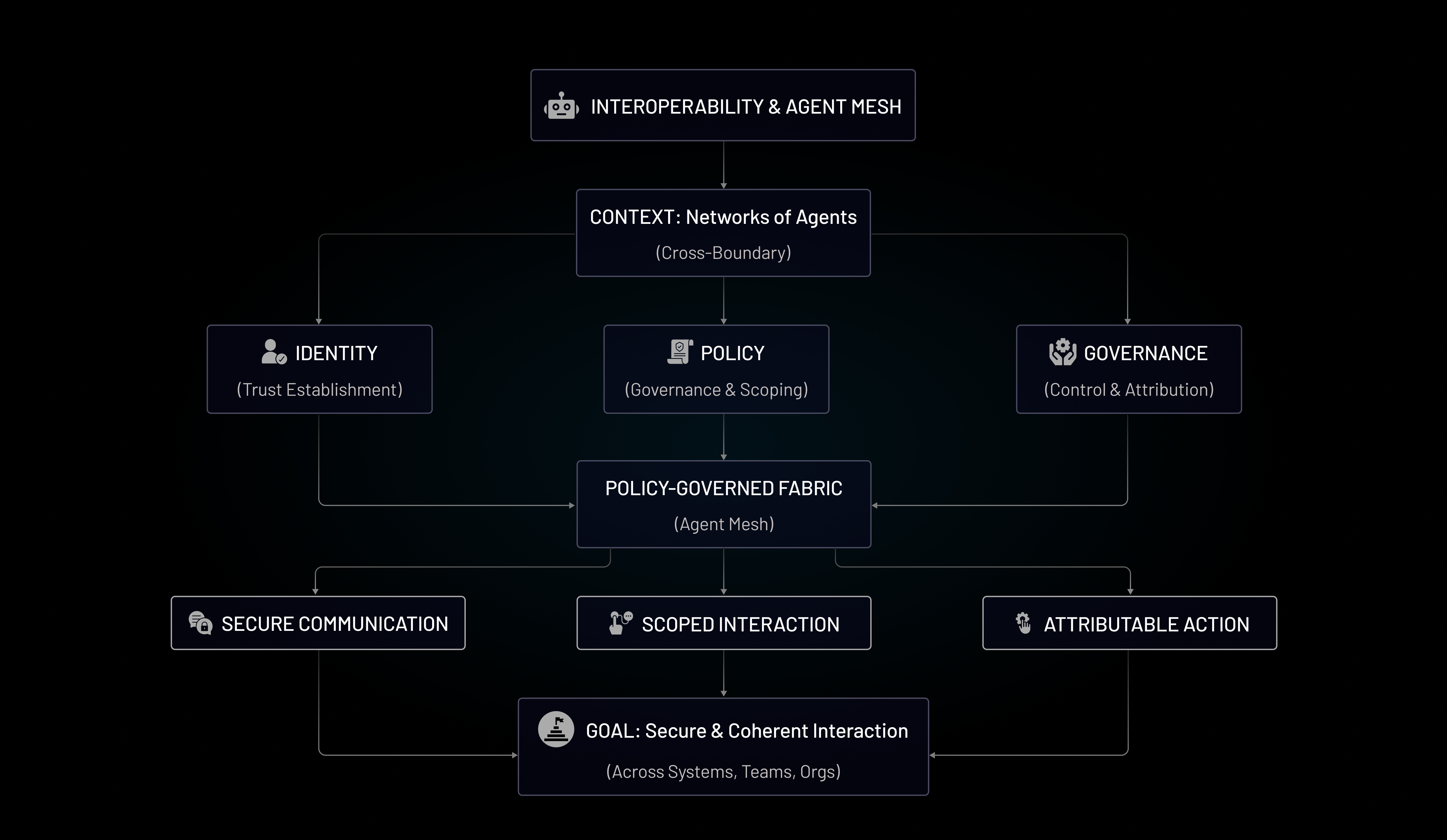
As organizations adopt agentic systems, value increasingly comes not from isolated agents, but from networks of agents working together across tools, platforms, and organizational boundaries. This shift introduces new challenges around trust, coordination, and control.
What is Interoperability & Agent Mesh?
Interoperability & Agent Mesh refers to the ability for multiple agents, services, and systems to interact securely and coherently, even when they are built by different teams, run in different environments, or belong to different organizations.
An agent mesh is not just connectivity—it is a policy-governed fabric where identity establishes trust, scopes interaction, and ensures every action remains attributable and controlled across agent boundaries.
Why Interoperability Matters for Agentic Systems
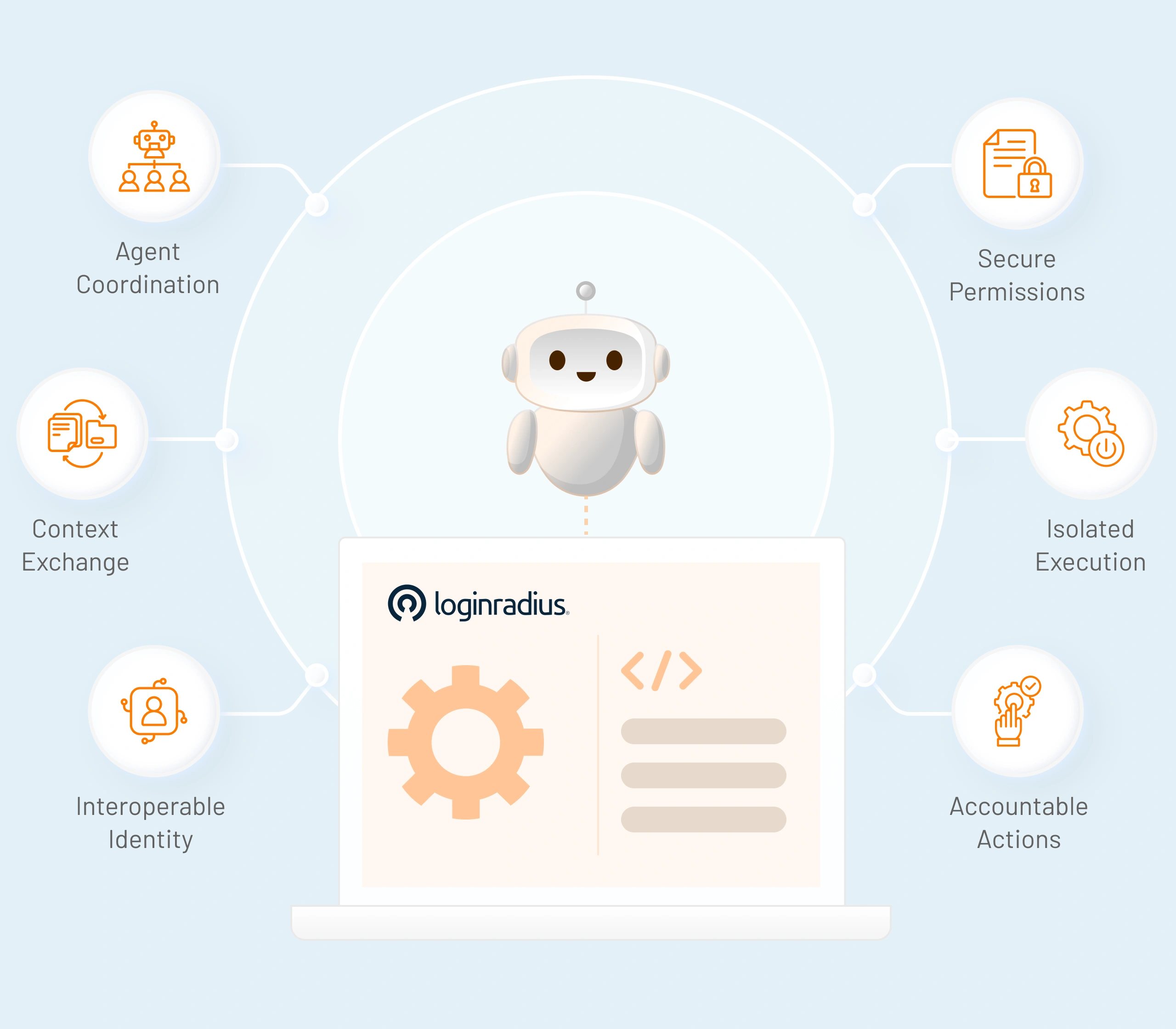
Agentic systems rarely operate in isolation. Agents call tools, delegate tasks to other agents, exchange context, and act across APIs and environments.
Without interoperable identity controls:
- Trust relationships become implicit and unsafe
- Permissions sprawl across agents and systems
- Failures and abuse propagate across the mesh
Interoperability ensures that coordination scales without sacrificing security, isolation, or accountability.
Core Pillars of Interoperability & Agent Mesh
Agent Mesh Architecture Models
As agent ecosystems evolve, organizations typically adopt one of the following approaches to interoperability and coordination.Point-to-Point Agent Integration
Agents communicate directly with each other using custom integrations.Trust and permissions are embedded in code or configuration.
This approach works at small scale but becomes fragile and difficult to govern as the number of agents grows.
Centralized Orchestration Layer
Agents are constrained by scoped permissions, predefined tools, and approval checks. Access is limited by policy, and sensitive actions require explicit safeguards.This model balances autonomy with control and is common in early production deployments.
Policy-Governed Agent Mesh
Agents interact through a shared identity and policy fabric.Trust is established dynamically, permissions are scoped per interaction, and actions are continuously validated.
This model enables scalable, secure collaboration across diverse agents and systems.