Let’s be honest: the way we currently use AI agents without much thought about security is a ticking time bomb!
Even for devs, if you are building agents today, you are likely dealing with a mess of static API keys buried in .env files, shared service accounts that never rotate, and a nagging fear that one prompt injection could expose your entire database. We are handing "God-mode" access to non-deterministic software and hoping for the best.
That approach doesn't scale, and it certainly isn't anywhere secure.
At LoginRadius, we are architecting the fix. We are moving away from treating agents as simple scripts and starting to treat them as First-Class Identities. By combining the strict security of OAuth 2.1 with the connectivity standards of the Model Context Protocol (MCP), we are building a framework where agents are authenticated, authorized, governed, and audited just like your human users.
In this blog, we will discuss in detail how we are solving the “Agent Identity Crisis”. So, keep reading!
The Problem: Your Agent Shouldn't Be "You"
The biggest mistake developers make is letting an agent inherit a user's root credentials. When an agent acts as "you", it has your full permission set. If that agent gets confused or compromised, the blast radius is your entire digital footprint.
In the identity and auth circle, experts define this as the "Governance Gap".
Agents have evolved into a distinct class of application users that act autonomously - fetching data, triggering workflows, and calling partner APIs in the background. Yet, legacy identity stacks try to jam these autonomous entities into user-centric boxes.
To fix this, we need to separate the Agent Identity from the User Identity.
-
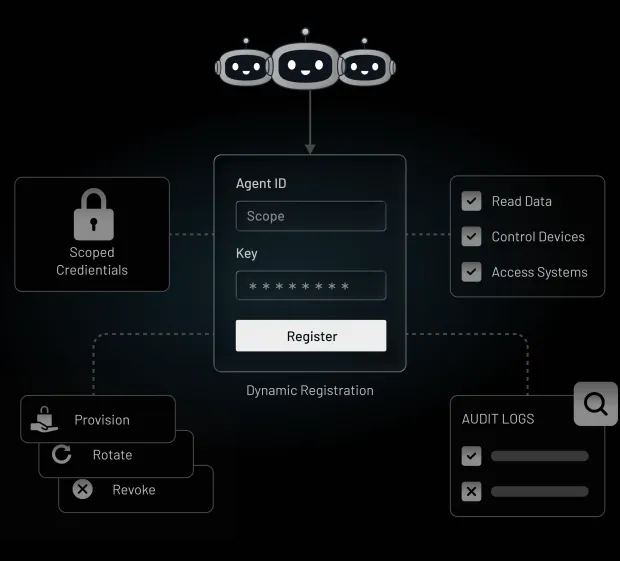
Independent Lifecycle : You need to be able to provision, rotate, and revoke an agent’s identity without breaking the human user's access.
-
Traceability : When an action happens, your logs need to show exactly who did it. Was it Sarah? Or was it "Sarah’s Scheduling Agent" acting on her behalf?.
LoginRadius solves this by assigning verifiable, unique identities to every AI agent. We don't just give them a key; we give them a profile, a lifecycle, and a set of distinct permissions managed centrally.
How AI is Going to Change Your IAM Initiatives.
Why Traditional IAM are Not Made for the Agentic Era?
If you try to secure an autonomous AI agent with a standard Identity and Access Management (IAM) stack, you are effectively trying to fit a square peg into a round hole.
Legacy identity systems were architected for humans - biological entities who work 9-to-5, click buttons synchronously, and have a singular, stable identity. AI Agents are fundamentally different beasts. They are non-deterministic, they run 24/7, and they have an "insatiable appetite for data".
Here is why your existing IdP (Identity Provider) setup is struggling to keep up with the agentic shift.

1. Speed vs. Control
Traditional IAM relies on human speed controls - manual provisioning, ticket-based access requests, and quarterly reviews. But agents operate at machine speed. They don’t wait for approval queues, they enter your system instantly, act autonomously across systems, and are gone before a review ever happens.
When developers deploy agents that are faster than their identity infrastructure can register them, you get "Shadow AI" - invisible workloads operating without oversight, often bypassing security reviews entirely.
2. The Problem with "Service Accounts"
For years, the industry solution for non-human identity was the humble Service Account. But Service Accounts do not go well with AI Agents. They typically rely on static API keys or long-lived secrets.
-
No Rotation : These keys often sit in .env files for years. If an agent leaks a key, the blast radius is massive because the key is rarely scoped to specific tasks.
-
No Context : A service account creates a binary "all-or-nothing" access. It doesn't understand that this specific run of the agent is on behalf of a junior analyst, while that run is on behalf of the CFO.
3. Non-Deterministic Behavior
Traditional software is predictable: If Input A, then Action B. Traditional IAM uses static Role-Based Access Control (RBAC) to match this predictability.
But, AI Agents are non-deterministic. They make decisions based on context. An agent might decide to call a weather API today and a database API tomorrow to solve the same problem.
Static permission models can't handle this flexibility without granting dangerous "God-mode" privileges to cover every possible scenario
4. The "Impersonation" Blind Spot
The AI agents might "impersonate" a user to get work done. This destroys accountability. If an agent deletes a production table while acting as you, the audit logs just say "You deleted the table".
There is no cryptographic distinction between your hand on the keyboard and the agent’s autonomous decision. This lack of traceability makes forensics impossible and compliance a nightmare
5. Consent Fatigue
Finally, there is the scale of authorization. If we used standard OAuth user consent flows for agents, you would be bombarded with pop-ups every time your agent wanted to read a file or search the web. We call this Consent Fatigue.
Users stop reading and start clicking "Allow" on everything, defeating the purpose of security. Agents need a model that supports pre-authorized trust envelopes and asynchronous approvals, not constant, synchronous nagging.
OAuth 2.1: A Strong Foundation for Non-Human Auth
So, if static API keys are the "governance gap," what fills it?
Interestingly, we didn't need to invent a new cryptographic protocol from scratch. We needed to apply the best parts of an existing one, strictly. This is why LoginRadius, and the broader AI ecosystems including the Model Context Protocol (MCP), has chosen OAuth 2.1.
Now, you might know OAuth 2.1 as a cleanup of OAuth 2.0, deprecating insecure flows like the Implicit Grant. But for AI agents, it is much more than a cleanup. It is the structural foundation that allows us to treat non-human entities with the same rigorous security hygiene we apply to humans.
Here is why OAuth 2.1 is the non-negotiable standard for Agentic IAM.
1. Killing the "Forever Token" with Rotation
The most dangerous thing about a standard API key is that it usually works forever. If an agent’s key leaks, attackers have a permanent backdoor until someone manually rotates it (which, let’s be honest, rarely happens).
LoginRadius utilizes OAuth 2.1 to enforce short-lived, rotating access tokens. Instead of a static secret, the agent authenticates to the LoginRadius Authorization Server to request a JSON Web Token (JWT). This token has a strict expiration (exp claim) - often valid for just minutes or hours.
If a token is leaked, its window of utility is tiny, drastically limiting the "blast radius" of a breach. Furthermore, because we at LoginRadius handle the lifecycle centrally, we support automatic key rollover (JWKS), meaning we can rotate the underlying signing keys without needing to redeploy a single line of agent code.
2. Solving the "Confused Deputy" with Audience Binding
"Confused Deputy" problem - where a malicious service tricks an agent into giving up its credentials has been a big risk associated with AI agents. OAuth 2.1 slams the door on this via Audience Binding.
In the LoginRadius Agentic IAM architecture, every token we issue is cryptographically bound to a specific target.
-
The Mechanism : When an agent requests access, it must use Resource Indicators (RFC 8707) to specify exactly who it wants to talk to.
-
The Result : We issue a token with an aud (audience) claim matching that resource.
-
The Enforcement : If the agent tries to pass that token to a different service (like a malicious logger), that service cannot replay the token against Salesforce because the aud claim won't match. The token is useless outside its intended destination
3. PKCE is Mandatory (Even for Machines)
Finally, OAuth 2.1 mandates Proof Key for Code Exchange (PKCE) for all clients. Historically, PKCE was used to protect mobile apps.
In the agentic world, it prevents authorization code injection attacks. Even if an attacker intercepts the authorization code returning to your agent, they cannot exchange it for an access token without the cryptographic code verifier that only your agent possesses.
LoginRadius Agentic IAM: The Key Principles
Here are the key principles driving our architecture:
1. The Centralized Authorization Server
In an agentic architecture, the LoginRadius platform functions as the Centralized Authorization Server. It acts as the "brain" of your security posture, handling three critical jobs:
-
It Authenticates the Agent : We don’t let AI Agents roam free. Every agent is assigned a verifiable, unique identity managed independently of users. Whether through Dynamic Client Registration (DCR) or Client ID Metadata Documents (CIMD), we ensure the agent is exactly who it claims to be before it ever gets a credential.
-
It Evaluates Policies : Just because an agent is authenticated doesn't mean it gets a free pass. Our server evaluates access policies in real-time. It checks if the agent is allowed to request specific scopes (e.g., files:read) and enforces context-aware guardrails.
-
It Issues Scoped Tokens : Once the agent passes these checks, we issue a short-lived access token (JWT). This token is strictly scoped to the requested permissions and bound to a specific audience, ensuring that if it’s intercepted, it can’t be used to attack unrelated services
2. Token Exchange & Delegation (RFC 8693)
Agents usually do their best work when they are helping someone. But letting an agent "impersonate" a user is a security nightmare that destroys accountability.
We leverage RFC 8693 (OAuth 2.0 Token Exchange) to solve this. Instead of impersonation, we use Delegation.
-
The Flow : The agent authenticates with its own credentials but presents a "subject token" representing the human user.
-
The Result : We issue a new downstream token that cryptographically encodes both identities: the User (the resource owner) and the Agent (the acting party).
-
The Benefit : This ensures that your audit logs are crystal clear. You can trace every API call back to the specific agent instance and the human who authorized it.
3. Standards-Based (OAuth 2.1)
LoginRadius aligns agent authentication with the MCP mandate by enforcing OAuth 2.1, ensuring native compatibility with the growing MCP ecosystem. Agents automatically discover authorization servers via RFC 9728, eliminating custom integrations.
OAuth 2.1–mandated PKCE protects against intercepted authorization codes, while RFC 8707 resource indicators bind tokens to specific audiences to prevent “confused deputy” attacks.
For cross-system workflows, OAuth token exchange (RFC 8693) enables agents to securely chain calls across domains without losing user context.
The “Kill Switch” - Lifecycle Management & Observability
What happens when an agent goes rogue?
Maybe it’s a prompt injection attack, maybe it’s a hallucination loop, or maybe the agent just decided to query 50,000 records instead of 50. In a legacy system using static API keys, you are stuck scrambling to rotate secrets and redeploy code—a process that takes hours, if not days.
We built LoginRadius Agentic IAM to provide an immediate "Kill Switch."
Because we handle the full lifecycle of the agent—from provisioning to de-provisioning—we give you a level of control that static keys can’t match.
1. Automated Rotation (No More Secrets in Code)
The biggest security risk in AI is "Secret Sprawl"—hardcoded keys scattered across repositories. LoginRadius eliminates this by acting as a Token Vault. We centralize the issuance and rotation of credentials.
Agents use short-lived JWTs that are automatically rotated using JSON Web Key Sets (JWKS). This means your agents never hold a "forever secret" that can be stolen and reused indefinitely. If a key is compromised, it is already obsolete by the time the attacker tries to use it.
2. Action-Level Observability
You need to know exactly who did what. Because we use Delegated Access Tokens, our audit logs don't just show a generic "System User" event. They show the full context: "Agent X performed Action Y on behalf of User Z".
This allows your security team to trace an API call back to the specific agent instance and the human user who authorized it, satisfying the strictest compliance requirements for auditability.
3. Real-Time Revocation
If an anomaly is detected—say, an agent attempting to access a high-risk scope it hasn't used before—you don't need to shut down the whole system. You can trigger a Universal Logout for that specific agent. LoginRadius allows admins to revoke credentials instantly.
By invalidating the refresh tokens and killing the session at the server level, you cut off the agent's access to all downstream MCP servers and tools immediately. It is a surgical strike against risk, keeping the rest of your fleet operational.
Human-in-the-Loop: Governance Where It Matters
Let’s be realistic: some decisions are too important to be automated.
While we want agents to be autonomous, we don't want them transferring large sums of money or deleting production databases without supervision. LoginRadius enforces Human-in-the-Loop (HITL) governance to bridge this gap.
Step-Up Authorization for High-Risk Scopes
We allow you to define "Trust Boundaries" for your agents.
-
Low Risk : An agent wants to read a calendar? Auto-approve based on policy.
-
High Risk : An agent wants to delete a calendar event? That triggers a Step-Up Authorization challenge.
When an agent hits a high-risk boundary, the execution pauses. The system triggers an approval workflow—sending a notification to the human user to review the action. The agent can only proceed once the human explicitly clicks "Approve," at which point we issue the necessary scoped token to complete the task.
This approach gives you the best of both worlds: the speed of automation for routine tasks and the safety of human judgment for critical ones.
Conclusion
We are transitioning from an era of Human-Computer Interaction to Computer-Computer Interaction.
In this new world, your Identity Provider cannot just be a database of usernames and passwords. It needs to be the Unified Trust Fabric that governs how autonomous entities connect, communicate, and act.
By treating AI agents as First-Class Identities, securing them with OAuth 2.1 and MCP, and enforcing Human-in-the-Loop oversight, LoginRadius provides the infrastructure you need to deploy AI safely. Get in touch with us to learn more about our cutting-edge agentic IAM and how it can transform your business.




