We spent some time talking to CISOs, IAM architects, and engineering leaders and we often heard that they’re witnessing something highly unusual. And honestly, it’s a little terrifying.
AI agents are starting to take on work that humans used to do once. Thanks to MCP servers, custom GPTs, and workflow automation tools, AI agents are no longer just passive helpers running in the background. They are reading sensitive data, triggering real transactions, chaining tools together, and operating with genuine autonomy.
But here’s the uncomfortable part - most of these agents are reusing human credentials or generic service accounts.
And that breaks a core assumption of our identity and access models.
We know how to manage human users. We know how to secure machine workloads. But AI agents? They are an entirely different beast.
The Identity Crisis Nobody is Talking About: Why AI Agents Break Traditional IAM
To understand exactly why AI agents break our current security posture, we have to look at the baseline of how we currently manage identity.
It comes down to two historically distinct buckets:
-
Human Identity - A person authenticates, establishes a session, and interacts with an application through a controlled UI. We verify who they are, authorize their role, and monitor the session until logout. It’s linear, predictable, and governable.
-
Standard Non-Human Identity - These are machine identities, APIs, and backend workloads that communicate system-to-system with no humans in the loop. Historically, this has meant static API keys or long-lived service accounts. They follow rigid, predictable execution paths.
This model worked fine for cron jobs and simple integrations. But it collapses in modern distributed systems where AI agents operate.
Static credentials strip away visibility and accountability. Long-lived access tokens can create massive damage if leaked. And once workloads are spread across clouds and tools, perimeter-based security stops working altogether.
At that point, it becomes hard to tell who actually did what. Add rogue AI agents into this already fragile setup, and the risk compounds fast.
The Danger Zone: What Happens When We Get It Wrong
The danger of shoving AI Agents into the same bracket as human users gives rise to multiple threats.
First, you get the immediate explosion of "Shadow AI". When engineering teams build custom GPTs or MCP-powered workflow bots without a dedicated agent identity framework, these agents often end up orphaned or unsanctioned.
Worse, because they are forced to use legacy machine identities, they are frequently over-privileged. Instead of operating with tightly scoped, ephemeral access tied to a very specific task, these agents are granted broad, platform-level privileges that outlive their creators.
But the most terrifying consequence for a CISO is the "Who did what?" problem. In a traditional setup, if a production database is altered or a sensitive financial transaction is triggered, you look at the logs and easily find the human user's session.
But with AI in the mix, if an agent is sharing a human's OAuth token or using a generic service account, your audit trail effectively vanishes.
Without a separate, verifiable identity explicitly for the AI agent, it is practically impossible to maintain a reliable audit trail. If an agent accidentally deletes a critical system record or moves money, you are left completely blind.
It becomes incredibly hard to answer basic questions:
-
What actor actually performed the action?
-
Was this initiated by a human, a system, or something acting on their behalf?
-
What context led to the action?
Case Study - The Over-Privileged Support Agent
Imagine your team builds an AI assistant to help customer support look up historical tickets. To move fast, they give the AI a Senior Engineer’s credentials.
For a while, everything looks great.
Then a customer asks a complicated payment-related question. The AI gets confused and hallucinates. It decides there’s a critical billing bug that needs to be deleted immediately.
Because the agent is using a Senior Engineer’s all-access credentials, it has the power to do exactly that.
So it deletes a massive database of customer payments - thinking it’s being helpful.
The Fallout:
-
The Audit Trail is a Lie: Your security logs show the Senior Engineer deleted the database at 3:00 AM.
-
The "Why" is Missing: You have no record of what the customer asked or why the AI decided to delete the data, and it deleted pretty much everything.
-
No Safety Net: Because the AI was "pretending" to be a human, there were no restricted boundaries to stop a simple "support agent" from performing a "destroy" action.
The Solution: Enter "Agentic IAM"
We have to stop pretending that a legacy model can solve a fundamentally new problem.
This is exactly why we introduced Agentic IAM at LoginRadius.
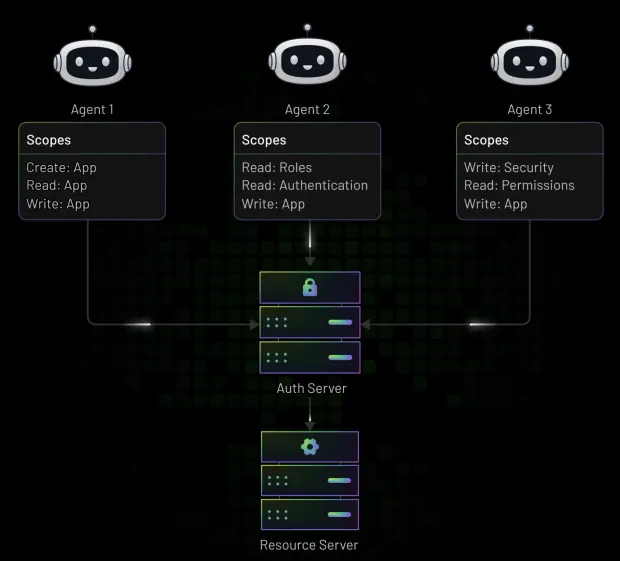
Instead of forcing everything into human and machine silos, we treat AI agents as first-class identities. They get the same lifecycle management, trust controls, and auditability as human users, but with guardrails designed specifically for autonomous behavior.
Here’s what that looks like in practice:
Kill the long-lived Tokens
When an agent needs to act, it receives a short-lived, rotating OAuth 2.1 access token with tightly scoped permissions. Access is ephemeral and purpose-built, enforcing least privilege at runtime.
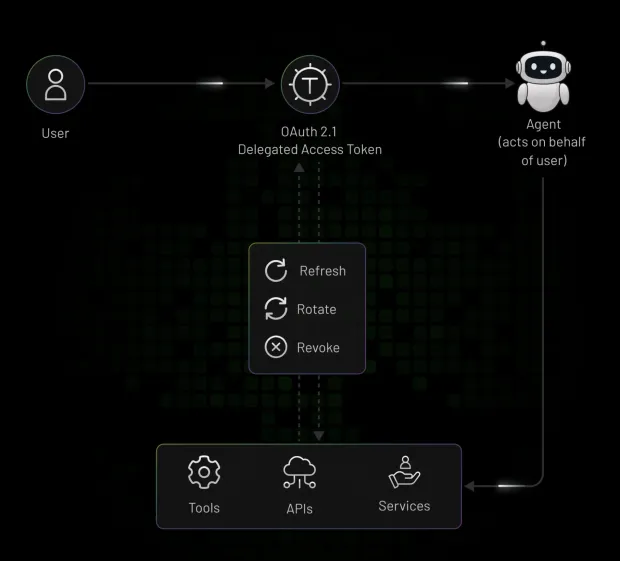
Secure downstream tool access with MCP
As agents connect to external tools and platforms, passing hardcoded credentials is a massive liability. LoginRadius acts as a centralized OAuth 2.1-compliant auth server for MCP environments, issuing tokens validated specifically for MCP servers and supporting RFC 8693 token exchange.
Agents can pass identity context downstream without ever exposing underlying credentials.
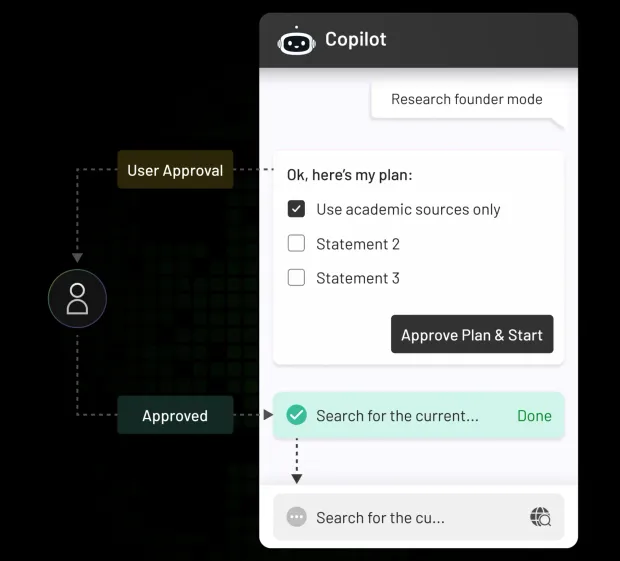
Human-in-the-loop governance
Not every action should be executed blindly. For high-risk operations - moving money, changing access policies, deleting data - the system pauses the agent and requires explicit human approval. You get automation speed, bounded by real safety controls.
Conclusion
Here’s the bottom line: securing AI agents shouldn’t slow your engineering teams down. A proper Agentic IAM layer becomes the zero-trust foundation that lets you scale AI safely, quickly, and with real accountability.
So here’s the question to take back to your security and engineering teams this week:
How are you actually tracking the actions of autonomous AI agents in your environment today?
Are you still relying on static API keys and hoping for the best?
If you’re securing next-generation autonomy with legacy identity models, you have a blind spot.
If you’re ready to close it, let’s talk. Book a Demo.


