Introduction
RBAC sits quietly inside most CIAM systems, rarely questioned until something goes wrong.
Teams spend months refining sign-up flows, optimizing login performance, and hardening authentication. Yet the real security posture of a customer identity platform is decided later when roles, permissions, and access boundaries start interacting with real users, real partners, and real data.
That’s where RBAC identity management stops being an abstract control model and becomes a practical risk surface.
In CIAM, access control isn’t limited to employees following internal policies. It extends to customers who bring their own devices, partners who operate across tenants, and delegated admins who gain authority without ever joining your organization. These identities don’t behave predictably and they don’t stay contained unless the system enforces it.
This is why CIAM authorization is fundamentally different from workforce IAM.
Roles aren’t just labels. They define business authority. They decide who can export data, manage users, modify settings, or act on behalf of someone else. When those decisions are static, broad, or poorly scoped, CIAM security weakens quietly without obvious failure signals.
At the same time, access decisions can’t rely on roles alone anymore.
A role may be valid, but the context may not be. Devices change. Networks shift. Behavior drifts. This is where risk-based authentication becomes inseparable from RBAC not as an add-on, but as a way to preserve trust without redesigning roles every time risk changes.
This blog explores how those pieces fit together when you’re managing end-users and partners at the same time. Not from a theory-first perspective, but from how CIAM systems behave in production where scale, delegation, and edge cases are the norm.
If your CIAM platform has grown beyond simple login, this is the layer that determines whether it stays secure or slowly becomes ungovernable.
What “RBAC Identity Management” Means in CIAM
RBAC looks deceptively simple on paper. Assign a role. Attach permissions. Enforce access. That model works reasonably well inside employee IAM, where identities are issued, devices are managed, and context is relatively predictable.
CIAM is a different environment entirely.
Customer identities are external, fragmented, and fluid. Users sign up with different emails. They authenticate through social providers. They switch devices constantly. Some act as individuals. Others suddenly become “admins” for an organization they created five minutes ago. Partners operate across multiple customer tenants without ever belonging to your company.
So when we talk about RBAC identity management in CIAM, we’re not talking about job titles or static directory roles. We’re talking about behavioral access what a customer, partner, or delegated admin can do inside a specific context.
In CIAM, a role is rarely global.
It’s almost always scoped.
-
Scoped to a tenant
-
Scoped to an organization
-
Scoped to a resource
-
Scoped to a moment in time
That’s the first mental shift teams have to make.
A “Customer Admin” isn’t a universal admin. They’re the admin of this account.
A “Partner Manager” doesn’t manage everything. They manage their assigned customers.
A “Support Agent” shouldn’t inherit customer permissions just because impersonation exists.
RBAC in CIAM is less about hierarchy and more about containment.
The moment roles bleed across tenants, environments, or identity boundaries, CIAM security starts to feel brittle. That’s why customer RBAC needs to be designed as part of the identity architecture not added later as a permission layer bolted onto login.
The 2 RBAC Problems CIAM Teams Actually Face
Most CIAM RBAC failures fall into one of two buckets. And they usually show up months after launch, not during design.
Problem 1: End-User RBAC Grows Sideways
Customer platforms evolve fast.
What starts as “free vs paid” becomes:
-
team plans
-
shared accounts
-
customer-created roles
-
temporary access
-
support visibility
-
regional constraints
Suddenly, a role created for pricing logic starts controlling data access. Permissions overlap. Exceptions pile up. And no one is quite sure which role actually blocks what.
This is where teams unintentionally violate user access management best practices. Not because they ignore security but because RBAC becomes reactive instead of intentional.
The early warning sign is simple: When teams say “just add another role” instead of revisiting permissions.
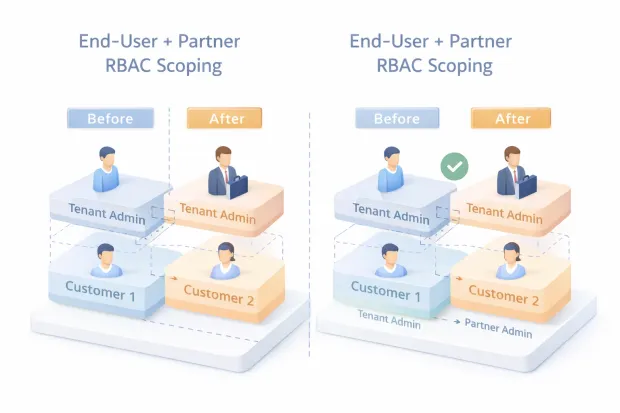
Problem 2: Partner RBAC Multiplies Everything
Partner access introduces a different kind of complexity.
Partners don’t just access your platform. They access other people’s data through your platform.
They might:
-
manage multiple customer tenants
-
administer accounts they don’t own
-
act on behalf of customers
-
require delegated administration
This turns RBAC into a multiplier problem.
One role change doesn’t affect one user, it affects dozens of tenants.
One mis-scoped permission doesn’t expose a feature, it exposes a portfolio.
This is where CIAM RBAC breaks most often. Not at login. Not during signup. But when partner access quietly expands beyond its original boundary.
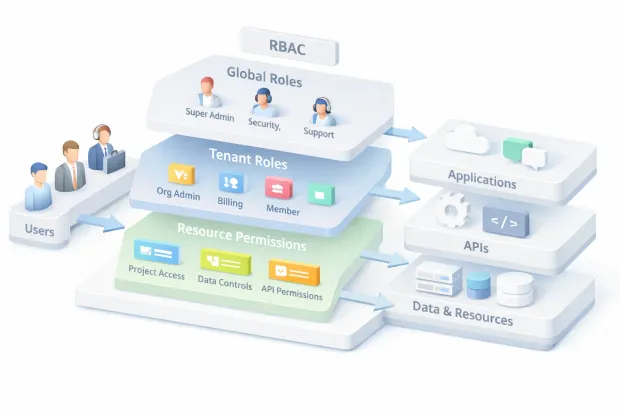
The CIAM RBAC Model That Scales:
Global Roles + Tenant Roles + Resource Permissions
CIAM RBAC scales only when roles are layered, not flattened.
A single role list won’t survive growth. What does work is a three-layer model that separates who you are from where you operate and what you touch.
Global Roles
These exist outside the customer context.
They describe platform-level identity:
-
Internal support
-
Fraud or security analysts
-
System automation
-
Super admins
Global roles should be rare, tightly governed, and heavily audited. Their purpose isn’t convenience, it's controlled exception handling.
Tenant / Organization Roles
This is where most CIAM logic lives.
Tenant roles define authority within a specific customer or partner boundary:
-
Account owner
-
Org admin
-
Billing admin
-
Member
-
Partner admin (scoped per tenant)
These roles should never float freely. They must always be evaluated with tenant context. Without that boundary, RBAC stops being authorization and becomes guesswork.
Resource-Level Permissions
This is the quiet layer that prevents expensive mistakes.
Not every action should be role-wide. Some actions belong at the resource level:
-
project access
-
workspace visibility
-
data export
-
configuration changes
This layer prevents role explosion by allowing fine control without inventing new roles for every edge case.
When teams skip this layer, RBAC becomes bloated. When they use it well, RBAC stays readable even as the platform grows.
Where Roles “Live” in CIAM: Tokens, Sessions, and Claims (OIDC/JWT)
One of the most overlooked RBAC decisions in CIAM is where authorization data actually lives.
Roles don’t just exist conceptually. They’re enforced through tokens, sessions, and claims and poor placement here creates real security gaps.
In modern CIAM systems using OIDC and JWTs, roles typically surface in one of three places:
Tokens
Access tokens often carry role or permission claims so APIs can make decisions without calling back to the identity service.
This works but only when tokens are:
-
short-lived
-
scoped
-
context-aware
Long-lived tokens with static roles are a liability, especially for privileged users and partners.
Sessions
Session context is where CIAM systems can stay flexible.
Sessions allow:
-
tenant switching
-
dynamic permission evaluation
-
step-up challenges when risk changes
This is where RBAC pairs naturally with risk-based authentication. A role may be valid, but the session still needs higher confidence before allowing sensitive actions.
Claims
Claims are powerful and dangerous when abused.
Stuffing too many roles into claims makes tokens heavy, brittle, and hard to rotate. Worse, claims that don’t encode tenant or resource context lead to accidental overreach.
A good rule of thumb: Claims should describe capability, not authority without context.
CIAM authorization works best when claims identify who the user is, while policy and enforcement layers decide what they can do right now.
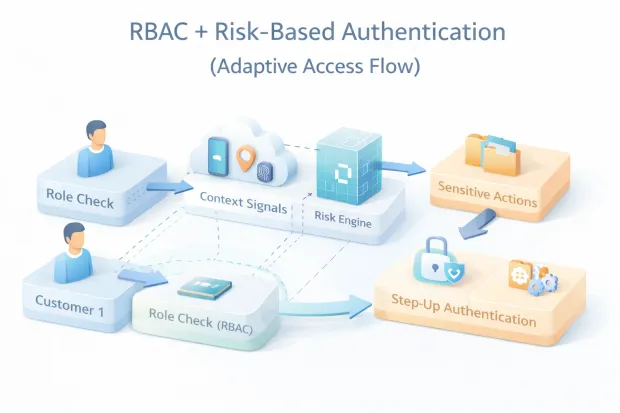
Risk-Based Authentication: How It Pairs with RBAC
RBAC answers a structural question: what is this user allowed to do?
Risk-based authentication answers a situational one: how confident are we right now?
CIAM systems need both because customer behavior doesn’t stay still.
A role is static by design. A customer admin is still an admin tomorrow. A partner manager still manages accounts next week. That stability is useful. But it also creates blind spots. The same role can represent very different risk depending on context.
Consider this:
-
A customer admin logs in from their usual device, during business hours, from a known network.
-
The same admin logs in from a new device, at an odd hour, from a country they’ve never accessed before.
RBAC alone treats both sessions as equal. And that’s the problem.
This is where risk-based authentication stops being a “nice to have” and becomes a safety valve. It doesn’t replace RBAC. It wraps around it.
Instead of changing roles constantly which creates role explosion and governance chaos risk-based authentication changes confidence levels. It decides when to:
-
require step-up authentication
-
block sensitive actions temporarily
-
restrict high-impact permissions
-
challenge sessions that suddenly look wrong
In CIAM, this pairing matters even more because identities are external. You don’t control customer devices. You don’t manage partner networks. Behavior is the signal not employment status.
That’s why modern risk-based authentication solutions are most effective when they don’t try to redefine access models. They simply reinforce them. RBAC defines the ceiling. Risk-based authentication decides how close a session is allowed to get.
CIAM Authorization Failure Patterns
Most CIAM authorization failures don’t look dramatic. There’s no crash. No alert storm. Just quiet overreach.
And almost every incident traces back to one of a few patterns.
The first is role creep.
A role created for convenience slowly accumulates permissions. A temporary exception becomes permanent. No one removes access because “it hasn’t caused issues yet.” Until it does.
The second is missing tenant boundaries.
Roles are evaluated correctly but without tenant context. A partner admin is authenticated properly, but the system doesn’t consistently enforce which customer they’re acting for. That’s how cross-tenant access leaks happen.
Another common one is stale access.
A customer downgrades. A partner offboards a client. An internal support agent switches teams. The identity still exists. The role still exists. The permissions quietly remain. Without provisioning and de-provisioning tied into CIAM workflows, RBAC slowly drifts away from reality.
Then there’s support impersonation without guardrails.
Support needs visibility. That’s reasonable. What’s risky is when impersonation bypasses logging, session limits, or step-up authentication. Many CIAM incidents start here because impersonation feels operational, not security-critical.
What’s striking is that none of these failures come from weak authentication. They come from authorization assumptions that were never revisited as the system grew.
User Access Management Best Practices
CIAM access management works best when teams resist the urge to “solve everything with roles.”
The first best practice is to design permissions before roles.
Roles should be collections of capabilities, not containers for logic. If you can’t explain what a permission does independently of a role, the model will eventually collapse under its own weight.
Next, keep authentication and authorization policies separate.
Login confidence and access entitlement are related but not interchangeable. This separation is what allows risk-based authentication to work without rewriting RBAC every time risk changes.
Another critical practice is to treat the tenant context as non-optional.
Every authorization decision should know which organization, account, or customer it applies to. If tenant context is implicit instead of enforced, RBAC becomes fragile.
Periodic access review also matters more in CIAM than teams expect.
Not because customers change roles constantly, but because partners and delegated admins do. Without review cycles, over-permissioned access quietly becomes the default.
Finally, log everything that changes authority. Not just logins. Not just failures. Role assignments, permission changes, impersonation, and admin actions.
CIAM security is as much about visibility as it is about prevention.
A Realistic CIAM Scenario
Imagine a SaaS platform that starts as consumer-focused.
At first, it’s simple. Users sign up. They have basic roles. Some upgrade to paid plans. RBAC feels manageable.
Then teams arrive.
Customers create organizations. They invite teammates. One person becomes the admin. Another handles billing. Someone else just needs read access. Tenant-scoped roles appear.
Now partners enter the picture.
An agency manages accounts for multiple customers. They need access but only to the tenants they’re assigned. They can configure settings, but not billing. They can onboard users, but not export data. They’re powerful, but only within narrow boundaries.
On top of that, support needs visibility. Not full authority just enough to troubleshoot.
Here’s where RBAC, tenant scoping, and risk-based authentication intersect.
-
Roles define who can act.
-
Tenant context defines where they can act.
-
Risk-based authentication decides when extra assurance is required especially for sensitive actions like data export, account recovery, or permission changes.
Nothing here is exotic. This is a very normal CIAM evolution path.
And it’s exactly why CIAM authorization can’t be an afterthought. Once partners, tenants, and delegated admins coexist, access control stops being simple and starts being foundational.
Conclusion
CIAM doesn’t fail because teams ignore security. It fails because access decisions quietly outgrow the models designed to contain them.
RBAC, at its core, is still the most practical way to organize permissions for customer identity. It’s understandable. It’s governable. And when done right, it keeps complexity from leaking into every part of your application.
But customer identity is dynamic by nature.
Users change behavior. Partners expand access. Admin privileges move closer to revenue, data, and payouts. That’s where static roles start to feel brittle and where risk-based authentication becomes essential.
Same role. Same user. Different context.
A customer admin logging in from a known device is one thing.
The same admin attempting sensitive actions from a new location or network is something else entirely.
This is why modern CIAM security isn’t about choosing between RBAC or risk-based authentication.
When teams get this right, access feels invisible. Predictable. Boring in the best way possible.
When they don’t, access becomes fragile. Hard to explain. Harder to audit. And nearly impossible to fix once partners, customers, and internal teams are already relying on it.
If your CIAM system is growing beyond simple end-user login if you’re onboarding partners, enabling delegated admins, or scaling multi-tenant access this is the moment to revisit your RBAC model.
Not to add more roles. But to make roles mean something again. In CIAM, security isn’t determined at login. It’s decided every time a role meets real-world behavior.
FAQs
Q: What is RBAC in CIAM?
A: RBAC in CIAM controls what customers, admins, and partners can do after login by assigning roles with scoped permissions. Unlike employee IAM, roles are usually tenant- and context-aware.
Q: How is RBAC in CIAM different from workforce IAM?
A: Workforce RBAC assumes managed users and stable environments. CIAM RBAC must handle external users, shared devices, partner access, and delegated administration across multiple tenants.
Q: Is risk-based authentication a replacement for RBAC?
A: No. RBAC defines access boundaries, while risk-based authentication adjusts confidence based on behavior and context. They work together, not in place of each other.
Q: Why do CIAM authorization issues cause security incidents?
A: Most incidents come from over-permissioned roles, missing tenant scoping, or stale access. Authentication succeeds, but authorization silently allows more access than intended.


