Introduction
In today’s digital-first economy, authentication has become the cornerstone of every secure interaction. From logging into a banking app to accessing a cloud-based workspace, verifying who a user really is without adding friction defines the foundation of trust between users and businesses. Yet, the challenge remains: how can organizations offer seamless access while ensuring airtight security?
This is where OpenID Connect (OIDC) steps in as a modern authentication protocol built to simplify and standardize the way we confirm digital identities across systems, platforms, and devices. By extending the OAuth 2.0 framework, OIDC bridges the gap between authorization and authentication, offering a user-first model that delivers both security and convenience.
In this blog, we’ll break down everything you need to know about OIDC authentication from its fundamental principles and protocol flow to its components and business benefits. Whether you’re a developer integrating secure sign-ins or a product leader aiming to enhance customer trust, this guide will help you understand how OIDC reshapes modern authentication into something truly seamless, secure, and scalable.
What is OIDC Authentication?
OpenID Connect (OIDC) is a modern identity layer built on top of the OAuth 2.0 framework, designed to make authentication both secure and effortless for users and developers. While OAuth 2.0 focuses on granting access to resources (authorization), OIDC extends it to confirm who the user is (authentication).
In simpler terms, OIDC helps an application verify a user’s identity and obtain basic profile information in a standardized, interoperable way.
At its core, OIDC acts as a trusted bridge between users, applications, and identity providers. When a user logs in, OIDC ensures their identity is verified by a trusted source like Google, Microsoft, or any enterprise IdP, so they don’t have to maintain separate credentials for every platform. This approach eliminates the risks of password fatigue and poor credential hygiene, two major culprits behind modern security breaches.
Unlike older authentication methods that rely heavily on stored passwords and session-based validation, OIDC uses tokens secure, digitally signed data packets to establish trust between parties. These tokens carry verified identity details, allowing applications to authenticate users quickly and consistently across multiple devices and services.
The protocol’s biggest strength lies in its versatility and scalability. It supports a wide range of use cases from consumer social logins (like “Sign in with Google”) to enterprise-grade access control within Customer Identity and Access Management (CIAM) platforms. Because it’s based on open standards, OIDC can integrate seamlessly into any ecosystem without disrupting existing workflows.
In short, OIDC authentication simplifies secure sign-ins for users and developers alike. It provides a unified framework that strengthens digital trust, reduces friction, and ensures every login is verified, not just permitted.

How OpenID Connect Works?
To understand how OpenID Connect (OIDC) functions, think of it as a conversation between three main parties each playing a critical role in verifying identity securely and seamlessly:
-
The End User (Resource Owner) – the person who wants to access an application or service.
-
The Relying Party (RP) – the application or website that needs to confirm the user’s identity before granting access.
-
The Authorization Server (Identity Provider or IdP) – the trusted authority responsible for authenticating the user and issuing tokens that confirm their identity.
OIDC builds this communication flow on top of the OAuth 2.0 authorization framework, transforming it from a simple access-granting system into a full-fledged identity verification protocol.
Here’s how the typical OIDC authentication flow unfolds step-by-step:
1. User Initiates Login
The process starts when the user tries to log in to an application (the Relying Party). Instead of entering credentials directly into the app, the user is redirected to an Authorization Server (like Google or Microsoft) that supports OIDC.
2. Redirect to the Authorization Server
The Relying Party sends an authentication request to the Authorization Server, specifying the type of information (known as “scopes”) it needs—such as basic profile details or email. This redirect ensures the user’s credentials are handled only by a trusted identity provider, not by the app itself.
3. User Authenticates
The user authenticates with their credentials on the Authorization Server’s login page. If the credentials are valid, the IdP confirms the user’s identity and prepares a set of cryptographically secure tokens.
4. Tokens Are Issued
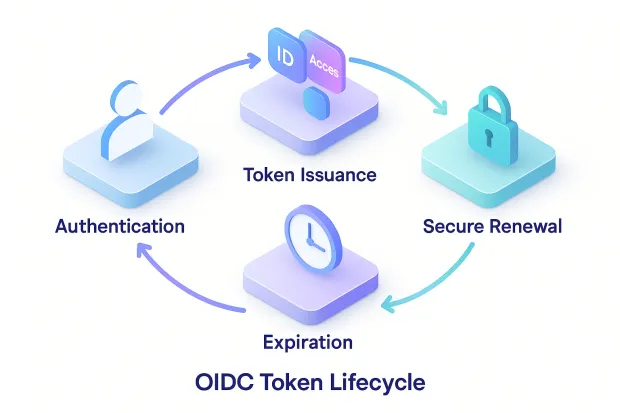
Upon successful authentication, the Authorization Server sends tokens, typically an ID Token, an Access Token, and optionally a Refresh Token back to the Relying Party via a secure channel. These tokens serve as verifiable proof of the user’s identity and authorization.
5. Application Grants Access
The Relying Party validates the ID Token to confirm the user’s authenticity. Once verified, it grants access to the user and may use the Access Token to fetch additional profile details from the UserInfo Endpoint.
This entire flow happens in seconds, ensuring a frictionless experience for users while maintaining strict security protocols in the background.
What makes OIDC exceptional is its token-based architecture, which eliminates direct password exchanges between apps and users. Instead, it relies on digitally signed JSON Web Tokens (JWTs) that are nearly impossible to forge. Each token has built-in expiry, encryption, and claims that define exactly what data is being shared, offering both transparency and control.
In short, OIDC takes the complexity out of secure authentication. It provides a simple, standardized method to verify identities across any device, platform, or service, helping businesses focus on user experience without compromising on security.
Core Components of the OIDC Protocol
To truly grasp how OpenID Connect (OIDC) secures and simplifies authentication, it’s essential to understand the key components that make the protocol function. Each element plays a unique role in verifying identity, granting access, and maintaining continuous trust between the user, the application, and the identity provider.
Let’s break down the core building blocks of the OIDC protocol:
1. ID Token
The ID Token is the heart of OIDC authentication. It’s a JSON Web Token (JWT) issued by the Authorization Server that contains verified information about the authenticated user, such as their name, email, and a unique identifier called a “sub” (subject).
This token is digitally signed to ensure it hasn’t been tampered with, making it a reliable source of truth for the Relying Party. The application uses this token to confirm that the identity provider has indeed authenticated the user.
In short: the ID Token answers the question, “Who is the user?
2. Access Token
The Access Token is what allows an application to access specific resources on behalf of the user. It doesn’t contain detailed user data itself, but acts as a key that unlocks APIs or services linked to the user’s account.
For example, once the user has authenticated, the Relying Party can use the Access Token to retrieve additional details from the UserInfo Endpoint or to call other secure APIs.
In short: the Access Token answers the question, “What can the app do for the user?”
3. Refresh Token
The Refresh Token is optional but highly valuable, especially for long-lived sessions. It allows the Relying Party to obtain a new Access Token when the previous one expires without asking the user to log in again.
This creates a balance between security and convenience, keeping sessions active while minimizing friction. It’s particularly useful in mobile or enterprise applications where frequent reauthentication would disrupt user experience.
In short: the Refresh Token answers the question, “Can we keep this session active securely?”
4. UserInfo Endpoint
The UserInfo Endpoint is a protected resource provided by the Identity Provider. After a successful login, the Relying Party can use the Access Token to fetch verified user profile information, such as name, email, or locale.
This enables personalization, allowing businesses to deliver tailored experiences without needing users to fill out repetitive forms. The endpoint acts as a secure, trusted data source, ensuring that every piece of user information is validated and consistent.
In short: the UserInfo Endpoint answers the question, “What verified details can the app use about this user?”
Together, these components form the backbone of the OIDC ecosystem. Each token and endpoint works in harmony to balance security, usability, and interoperability, enabling consistent authentication experiences across devices and environments.
Whether you’re building a consumer app, an enterprise portal, or a CIAM platform, understanding these OIDC components is key to implementing a secure and user-friendly identity layer.

Benefits of Using OpenID Connect
In a world where digital interactions define user trust, OpenID Connect (OIDC) offers more than just a way to log in; it redefines how authentication can be secure, scalable, and seamless at the same time. By combining the reliability of OAuth 2.0 with the simplicity of a standardized identity layer, OIDC brings tangible advantages to both users and organizations.
Let’s explore the key benefits that make OIDC the go-to protocol for modern authentication systems.
1. Simplified and Unified Login Experience
One of the biggest strengths of OIDC lies in its user-centric design. It enables Single Sign-On (SSO) across multiple applications, allowing users to log in once and access all connected services without re-entering credentials.
This frictionless experience not only enhances convenience but also reduces the cognitive load of remembering multiple passwords, a common cause of password fatigue and weak security practices. For businesses, a smoother authentication journey means higher engagement, faster conversions, and improved customer satisfaction.
2. Enhanced Security Through Tokens
OIDC eliminates the need for applications to directly handle or store user credentials. Instead, it uses cryptographically signed tokens (like ID Tokens and Access Tokens) to validate identity and access rights.
This token-based approach minimizes exposure to threats like phishing, credential theft, and man-in-the-middle attacks, since credentials are never shared with third-party apps. Tokens also come with built-in expiration times and scopes, ensuring access is always time-bound and purpose-specific.
3. Seamless Interoperability Across Systems
Built on open standards, OIDC ensures seamless interoperability between applications, platforms, and devices. Whether it’s a web app, a mobile application, or an enterprise API, OIDC works consistently across all environments.
This makes it an ideal solution for organizations operating in hybrid or multi-cloud ecosystems. It also simplifies integrations with major Identity Providers (IdPs) like Google, Microsoft, and LoginRadius, offering flexible options for developers to build secure authentication flows faster.
4. Scalability for Modern Digital Platforms
OIDC is designed for scale. It efficiently manages high authentication volumes without compromising performance or security, making it suitable for everything from small SaaS products to global enterprise systems.
By centralizing authentication and delegating identity verification to a trusted provider, OIDC reduces overhead for developers and administrators, allowing them to focus on innovation instead of constantly patching security issues.
5. Privacy and Compliance by Design
OIDC supports granular control over the data shared between users and applications through scopes and claims. Users can decide which details to share, and organizations can enforce data minimization and consent-based access, aligning with global privacy regulations like GDPR and CCPA.
This privacy-centric approach helps businesses not only build trust but also meet compliance requirements effortlessly, something legacy authentication systems often struggle to achieve.
6. Future-Ready for Advanced Authentication
As organizations move toward passwordless authentication, adaptive MFA, and federated identity systems, OIDC provides the flexible foundation needed to integrate these modern methods seamlessly.
Its architecture supports continuous innovation in authentication technologies, ensuring that as security evolves, your identity strategy evolves with it.
In essence, OpenID Connect transforms authentication from a basic login function into a strategic enabler of trust, usability, and compliance. It empowers users with secure and effortless access while giving businesses the confidence that every identity interaction is verified, encrypted, and future-proof.
Implementing OpenID Connect: A Step-by-Step Guide
Adopting OpenID Connect (OIDC) doesn’t have to be complicated. In fact, one of the reasons it’s become the preferred authentication standard for modern businesses is its simplicity in deployment and adaptability to existing systems.
Whether you’re a growing startup or a large enterprise, implementing OIDC is about creating a secure, unified, and user-friendly login experience without overhauling your entire infrastructure.
Here’s a clear, non-technical breakdown of how organizations can bring OIDC to life in their authentication flow:
1. Choose a Reliable Identity Provider (IdP)
Every OIDC setup starts with an Identity Provider, which handles the user verification process. Trusted IdPs like Google, Microsoft, LoginRadius, or Okta authenticate users and issue secure tokens that confirm their identity.
Selecting a reliable IdP ensures that your users’ credentials are protected under top-tier security practices, giving both your organization and your customers peace of mind.
2. Register Your Application
Once you’ve chosen an IdP, the next step is to register your application with that provider. This registration establishes a secure relationship between your app (known as the Relying Party) and the IdP.
In simple terms, it lets the IdP know who you are and ensures only your authorized application can request authentication for your users.
3. Configure Authentication Settings
Next, you define the scope of what information your application needs, like a user’s name, email address, or profile picture.
This step helps maintain privacy and compliance, as users are always informed about what data will be shared and can choose whether to grant access. Transparency at this stage helps strengthen user trust in your brand.
4. Establish Secure Token Exchange
Once the authentication flow is in motion, the IdP issues tokens like the ID Token and Access Token that confirm the user’s identity and grant access to specific resources.
Your application uses these tokens to verify the user’s identity and allow entry to protected areas or data. The best part? The user doesn’t need to remember or re-enter credentials for each service they access.
5. Enable Continuous and Frictionless Access
For long-term sessions, OIDC can maintain access using refresh tokens, ensuring users enjoy a seamless experience without being logged out repeatedly.
This approach keeps the login process simple while maintaining strict security standards ideal for customer-facing applications that value both convenience and trust.
6. Test and Monitor for Security and Experience
Before fully rolling out OIDC, it’s important to test how smoothly your login journey performs both from a user experience and security perspective.
Regular monitoring helps detect anomalies early and ensures your authentication process remains compliant, fast, and resilient to emerging threats.
By following these foundational steps, organizations can deploy OIDC smoothly without deep technical complexity. The result? \
A secure, standardized, and user-friendly authentication system that simplifies access across every digital touchpoint while ensuring your business stays ahead in trust, compliance, and experience.
OIDC vs OAuth 2.0: Understanding the Difference
In the world of digital identity, OIDC and OAuth 2.0 are often mentioned in the same breath and for good reason. They work hand in hand, yet their purposes are distinct. Understanding how they differ is key to seeing why OpenID Connect is the smarter choice for secure authentication in today’s connected landscape.
Let’s break this down in a way that’s clear, engaging, and relevant to how modern organizations handle access and identity.
The Foundation: OAuth 2.0 as the Base Layer
OAuth 2.0 was designed primarily for authorization, not authentication. In simple terms, it’s a protocol that allows an application to access specific resources or data on behalf of a user without needing to know the user’s credentials.
For example, when you grant an app permission to access your Google Drive or Spotify account, OAuth 2.0 ensures that the app receives limited access via an Access Token, rather than your password. This token tells the resource server, “This user has permitted me to do X and Y,” but it doesn’t say who the user actually is.
That’s where the gap begins.
The Evolution: OpenID Connect Steps In
While OAuth 2.0 solved the problem of secure access, it didn’t answer the most fundamental question: “Who is the user behind this access?”
OpenID Connect (OIDC) was created to fill that missing piece. It adds an identity layer on top of OAuth 2.0, turning authorization into full-fledged authentication.
With OIDC, applications don’t just receive permission tokens; they receive ID Tokens, digitally signed data that confirms who the user is, along with verified profile information like their email or user ID.
This means that when someone logs into an app using OIDC, the system isn’t just allowing access; it’s verifying identity through a trusted source.
The Key Difference in Purpose
You can think of OAuth 2.0 as the “gatekeeper”, while OIDC acts as the “identity verifier.”
| Aspect | OAuth 2.0 | OpenID Connect (OIDC) |
|---|---|---|
| Purpose | Authorizes access to resources | Authenticates the user’s identity |
| Core Token | Access Token | ID Token (plus Access Token) |
| Use Case | “Can this app access my data?” | “Who is the user logging in?” |
| Focus | Secure resource access | Secure and verified user login |
| Data Scope | Permissions only | Identity + Permissions |
This layered approach ensures that OIDC can do everything OAuth 2.0 does and more. It not only grants access but also establishes digital trust, verifying every user’s identity before allowing any action.

Why This Difference Matters
In an era where one compromised password can lead to massive data breaches, authentication must go beyond access control. OIDC brings clarity, verification, and confidence to every login attempt.
It allows businesses to protect users without complicating their experience, streamlining authentication across multiple systems while maintaining airtight security.
From social logins like “Sign in with Google” to enterprise-level CIAM frameworks managing millions of identities, OIDC ensures that every authentication is verified, standardized, and secure.
In essence, if OAuth 2.0 is the foundation of digital trust, OIDC is the structure built upon it, a system that doesn’t just permit access but proves identity. Together, they create the perfect balance between convenience and control in the evolving landscape of secure digital interactions.
Conclusion
As the digital world expands, so does the need for authentication methods that are both seamless and secure. Passwords alone are no longer enough; they’re cumbersome for users and a goldmine for attackers. In this environment, OpenID Connect (OIDC) emerges as a crucial evolution, redefining how trust is built between users and digital systems.
OIDC brings together the best of both worlds: simplicity for users and robust security for organizations. It empowers businesses to provide effortless, one-click logins while ensuring that every identity verification happens through trusted, standards-based mechanisms. With token-based authentication, encrypted communication, and cross-platform compatibility, OIDC turns the login process into a secure handshake of trust rather than a vulnerable exchange of passwords.
For developers and enterprises alike, adopting OIDC is more than a technical upgrade; it’s a strategic investment in digital trust. Whether it’s customer-facing apps, partner ecosystems, or internal systems, OIDC ensures that identity is managed with precision, compliance, and future readiness.
And as the industry moves toward passwordless authentication, adaptive MFA, and federated identity, OIDC will remain the foundation that ties it all together, making authentication smarter, safer, and frictionless.
So, if your organization is still relying on outdated login methods or managing multiple identity systems, it’s time to move forward. Embrace OpenID Connect and transform how your users log in securely, effortlessly, and confidently.




