Introduction
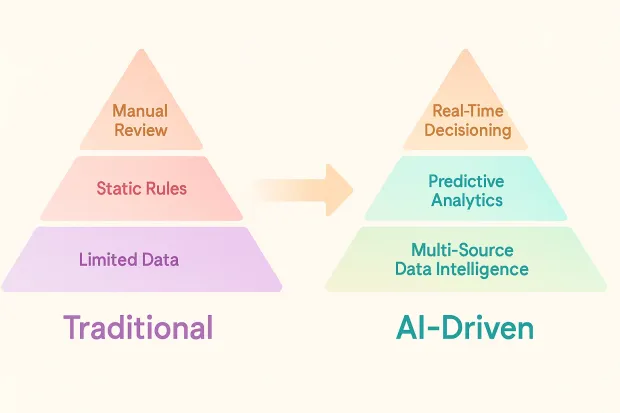
In today’s digital-first world, fraudsters move faster than ever, adapting, automating, and exploiting every weak link they find. Traditional fraud detection systems, built on static rule sets and manual reviews, simply can’t keep up. This is where AI-driven fraud detection steps in, not just as an upgrade, but as a revolution in how organizations identify and prevent fraud.
Unlike rule-based systems that react after a threat is detected, AI and machine learning algorithms actively learn from every interaction, transaction, and anomaly. They recognize complex patterns across billions of data points, spotting unusual behavior that humans might miss and do it all in real time.
Whether it’s unauthorized logins, identity theft, payment fraud, or synthetic account creation, AI has the speed and intelligence to predict and prevent these attacks before they cause damage.
For modern businesses, especially those managing large user bases through Customer Identity and Access Management (CIAM) systems, this shift is critical. By embedding AI into authentication, behavioral analytics, and real-time risk scoring, organizations can detect suspicious logins or transactions as they happen, rather than after the fact.
This proactive, adaptive approach doesn’t just stop fraud; it builds digital trust. Customers feel safer, transactions stay legitimate, and brands maintain their reputation for security in an era where confidence is everything.

Key Features of AI-Powered Fraud Detection Systems
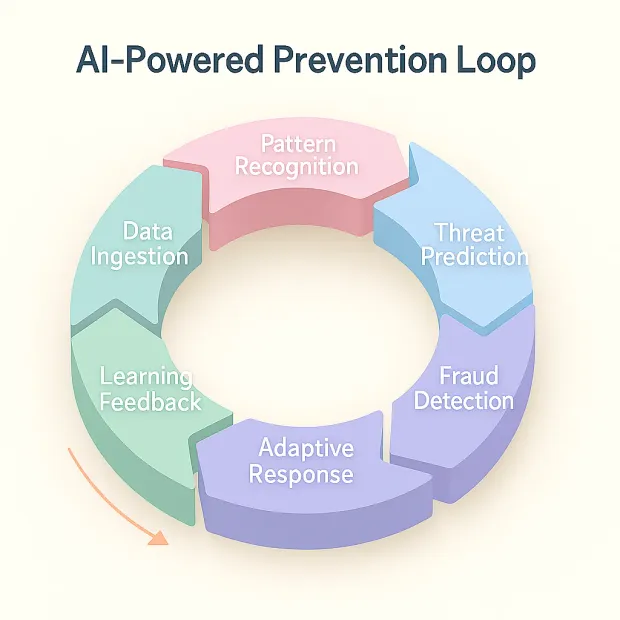
Modern fraudsters don’t follow a pattern; they invent new ones. That’s why businesses today rely on AI-powered fraud detection systems that learn, adapt, and evolve in real time. These systems go beyond traditional security controls, merging machine learning, behavioral analytics, and identity intelligence to create a dynamic shield against fraudulent activities.
Let’s explore the core features that make AI indispensable in fraud prevention:
1. Real-Time Analysis and Decisioning
In an age where thousands of digital transactions happen every second, speed defines security. AI systems excel at real-time fraud analytics, scanning transactions and user behavior as they occur.
Whether it’s a sudden change in device location, an unusual login attempt, or a risky payment pattern, AI engines can instantly flag and stop suspicious activity. This immediate response time minimizes losses, prevents account takeovers, and strengthens trust, especially critical for industries like banking, fintech, and eCommerce, where a single second can make all the difference.
2. Pattern Recognition and Behavioral Profiling
Fraud rarely looks the same twice. AI solves this by learning what “normal” looks like for every user and transaction. Using pattern recognition and behavioral biometrics, it builds unique behavioral profiles from typing speed and device use to transaction timing and location.
When a user behaves differently from their usual pattern, AI notices the deviation. It doesn’t just look at isolated incidents; it understands the full context. This continuous learning helps detect even subtle fraud attempts that might bypass static rule engines.
3. Anomaly Detection with Context Awareness
Not every anomaly is fraud, and AI knows that. Traditional systems often trigger false alarms, frustrating customers and burdening analysts. But AI-driven systems use contextual anomaly detection, understanding intent and situation before raising alerts.
For example, a login from a new device may not be suspicious if it’s accompanied by typical behavior patterns or known geolocation data. By assessing risk in context, AI dramatically reduces false positives and ensures legitimate users aren’t penalized.
4. Machine Learning and Continuous Improvement
Fraud tactics evolve, and so do AI systems. Through machine learning, AI continuously re-trains itself using new data, attack patterns, and user behavior trends. Every incident teaches the model to become more accurate, minimizing blind spots over time.
This adaptive intelligence keeps organizations several steps ahead of fraudsters, ensuring the system remains effective even as new forms of digital fraud emerge, from deepfake identity theft to synthetic identity creation.
5. Integration with Identity Verification and CIAM
The real strength of AI emerges when it’s combined with Customer Identity and Access Management (CIAM) platforms. By integrating fraud detection directly into login, registration, and transaction flows, businesses can assess identity risks before granting access.
This fusion of AI + CIAM ensures every user interaction from authentication to payment passes through a smart, fraud-aware decision layer. It allows businesses to enable frictionless, secure experiences, adapting authentication methods dynamically based on detected risk.
The Benefits of AI in Fraud Detection and Prevention
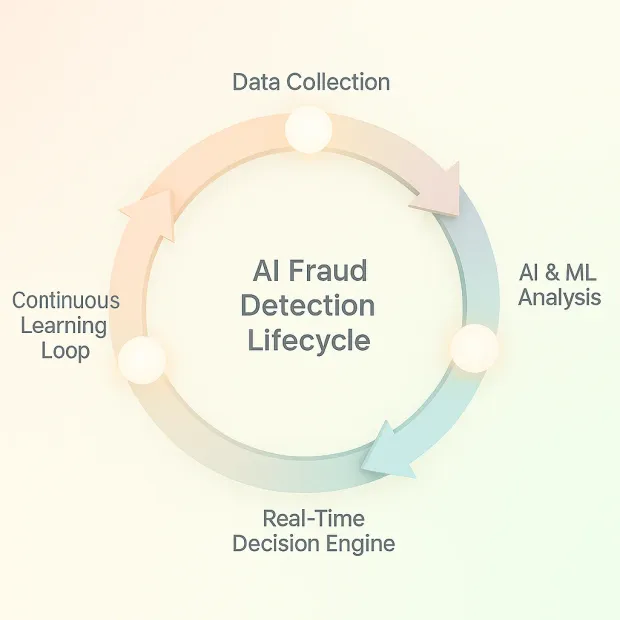
Fraud detection used to be reactive: detect, report, recover. Today, with AI-driven fraud prevention, it’s predictive, adaptive, and customer-first. Businesses no longer just detect fraud; they anticipate it, block it in real time, and protect user trust without adding unnecessary friction.
Here are the most impactful benefits organizations experience when adopting AI and machine learning for fraud detection:
1. Enhanced Accuracy and Reduced False Positives
Traditional fraud systems often generate too many alerts, most of which are false. Every unnecessary flag disrupts operations and frustrates legitimate customers.
AI changes this by using advanced behavioral modeling and context-aware algorithms to differentiate between real threats and normal variations in behavior. The result? Significantly fewer false positives and more accurate detections.
For businesses, this means a smoother user experience, fewer manual reviews, and more confidence that the system is targeting real risks, not loyal customers.
2. Proactive Fraud Prevention Instead of Reactive Response
AI doesn’t wait for fraud to happen; it predicts it. By analyzing patterns across millions of transactions, AI models identify early indicators of potential fraud before any actual damage occurs.
For instance, a spike in login attempts from new devices or mismatched behavioral signals might trigger step-up authentication or temporary holds.
This proactive approach gives businesses a critical edge: stopping fraud at the source rather than reacting after losses. It’s a true shift from damage control to damage prevention.
3. Real-Time Decision Making
In fast-moving industries like fintech, retail, and telecommunications, fraud detection needs to happen in milliseconds.
AI systems can process vast datasets in real time, assessing device fingerprints, user history, and transactional risk instantly.
This enables instant approvals for low-risk users and additional verification for high-risk scenarios, keeping both security and user experience balanced.
The result is an ecosystem where security decisions happen invisibly and instantly, supporting seamless digital interactions while keeping threats under control.
4. Cost and Resource Optimization
Manual fraud investigations are time-consuming and costly. AI automates much of this workload by performing continuous data analysis, risk scoring, and anomaly detection without human intervention.
Businesses save significantly on operational costs while investigators can focus on high-value, complex fraud cases that require human judgment.
This automation advantage not only reduces financial losses but also frees up teams to work on strategic initiatives like improving authentication journeys or scaling compliance frameworks.
5. Continuous Learning and Scalability
Unlike static rule-based systems that require frequent manual updates, AI models evolve naturally. As they process new data, they adapt to emerging fraud tactics, making them future-ready.
This continuous learning ensures that detection accuracy improves over time. Plus, AI-based systems are highly scalable, capable of handling growing transaction volumes across new markets, devices, or digital channels without compromising performance.
6. Improved Consumer Trust and Brand Reputation
Every fraudulent transaction erodes consumer confidence and trust; once lost, is hard to rebuild. By adopting AI-powered fraud prevention, organizations signal that customer safety comes first.
Consumers today expect security to be seamless. When authentication feels natural and transactions remain secure, they trust the brand more, stay longer, and recommend it to others. This is where AI-driven systems create lasting value not just by preventing fraud but by enhancing digital trust as a brand differentiator.
Implementing AI-Based Fraud Detection Systems
While the advantages of AI in fraud prevention are undeniable, implementing it successfully requires more than just integrating a few algorithms. It’s about building an ecosystem where data, intelligence, and security work together to create a real-time shield against evolving threats.
A well-structured implementation strategy ensures that businesses not only detect fraud effectively but also do it in a way that enhances the customer experience. Here’s how to build a strong foundation for AI-driven fraud detection:
1. Assessment and Goal Setting
Every successful AI initiative starts with clarity. Begin by evaluating your current fraud detection capabilities and identifying key pain points — are you losing money to chargebacks, account takeovers, or identity fraud?
Define measurable goals for your AI system:
-
Reduce false positives by X%
-
Improve fraud detection accuracy
-
Lower investigation turnaround time
-
Automate risk-based authentication decisions
Having clear objectives ensures that your AI deployment is focused and outcomes-driven, rather than just a technology experiment.
2. Data Collection and Integration
AI thrives on data. The more diverse and high-quality your data sources are, the smarter your models become.
Integrate data from multiple touchpoints, login patterns, transaction histories, device fingerprints, behavioral biometrics, and geolocation signals to give the AI system a 360° view of user behavior.
In the context of Customer Identity and Access Management (CIAM), this integration can extend across registration, authentication, and post-login activities. When all this information is unified, AI can make real-time, context-aware decisions that prevent fraud before it happens.
3. Selecting the Right AI Solution
Not every AI model fits every business. Consider factors like scalability, integration ease, real-time processing, and compliance readiness.
Choose a solution that blends seamlessly with your existing security stack or CIAM platform and supports adaptive authentication workflows.
Also, look for vendors that emphasize transparency. AI should explain its decisions, not just make them. Explainable AI (XAI) helps security teams trust the system’s logic and act quickly when anomalies arise.
4. Model Training and Testing
AI models are only as good as the data and validation they receive. Train them with historical fraud data and simulate real-world attack patterns to test their accuracy.
Include both fraudulent and legitimate data samples so that the system learns to distinguish between the two.
Rigorous A/B testing under different conditions ensures that the system performs consistently across channels, devices, and traffic volumes.
This phase is where human expertise still plays a critical role in validating results, fine-tuning algorithms, and preventing data bias.
5. Deployment, Monitoring, and Continuous Optimization
Once your AI models are live, the work doesn’t stop. Fraud tactics evolve constantly, and your system must evolve faster.
Implement continuous monitoring and feedback loops to detect performance drops, retrain models with fresh data, and optimize thresholds as new threats emerge.
Many organizations integrate real-time dashboards and alert systems that provide visibility into fraud trends, model decisions, and user risk scores, ensuring that both human analysts and automated systems stay aligned.
In essence, AI-based fraud detection isn’t a one-time setup; it’s a living, learning defense mechanism that improves with every transaction.

6. Addressing Key Challenges
AI adoption isn’t without hurdles. Businesses must consider:
-
Data Privacy & Compliance: Ensure that personal and financial data used for model training adheres to GDPR, CCPA, and other data protection laws.
-
Skilled Personnel: Employ or train data scientists and fraud analysts who understand both AI modeling and regulatory frameworks.
-
Integration Complexity: Seamless integration across legacy systems can be challenging prioritize open APIs and cloud-native models that simplify deployment.
With thoughtful planning, these challenges can be managed effectively, allowing businesses to harness AI’s full potential without compromising compliance or performance.
Real-World Applications of AI in Fraud Detection
AI-powered fraud detection isn’t just a theoretical advantage; it’s a proven, practical force that’s reshaping how industries fight fraud. Across every digital ecosystem, from banking to telecom, AI is enabling organizations to spot risks earlier, respond faster, and build lasting customer trust.
Let’s look at how various sectors are using AI-driven fraud prevention to strengthen their security and safeguard consumer identities.
1. Banking and Financial Services
Few industries face as relentless an attack surface as banking. Every second, millions of transactions flow through digital channels, and each could be a potential target for fraudsters.
Banks are now using machine learning and behavioral analytics to identify unusual spending habits, detect account takeovers, and prevent unauthorized transactions in real time.
For example, if a customer who usually makes local purchases suddenly initiates multiple high-value international transfers, the AI model can flag or freeze the transaction instantly.
Beyond transactional fraud, AI-driven identity verification also plays a major role. By analyzing device data, login behavior, and biometric cues, banks can confidently verify identities without adding friction. This dual impact, which reduces fraud and provides a smoother customer experience, is why AI has become foundational in financial fraud management.
2. E-commerce and Retail
For online retailers, fraud can take many forms: payment fraud, fake returns, coupon abuse, and account takeovers. These not only cause financial losses but also damage customer trust.
AI combats this through real-time fraud scoring, analyzing user history, device fingerprinting, purchase behavior, and IP anomalies during checkout. If a user suddenly buys multiple high-value items from a new device or location, AI systems can instantly trigger step-up authentication or transaction holds.
In addition, many retailers integrate AI fraud detection with their Customer Identity and Access Management (CIAM) platforms, ensuring that suspicious user accounts are automatically flagged, locked, or challenged before any purchase takes place. The result? A seamless, secure shopping experience that keeps both merchants and consumers safe.
3. Insurance
Insurance fraud is one of the most costly and complex types of fraud to detect, often hidden in legitimate claims. Traditional systems struggle to uncover these patterns because they rely on manual investigations and rule-based filters.
AI simplifies this through claims data analysis, spotting subtle inconsistencies, duplicate records, or abnormal claim patterns that suggest deception.
For example, AI models can cross-check claims against historical patterns and external data sources to detect staged accidents or inflated damages.
Moreover, predictive modeling helps insurers identify high-risk claims early, allowing them to prioritize investigations efficiently. This not only saves millions in payouts but also ensures genuine customers are paid faster, strengthening overall brand reputation.
4. Telecommunications
Telecom companies face a different flavor of fraud: subscription fraud, SIM card cloning, and identity spoofing. With millions of users and devices connecting every day, manual monitoring simply isn’t possible.
AI helps telecoms by performing real-time network surveillance and detecting unusual connection behaviors or call patterns that signal fraud. It can, for instance, identify an abnormal surge in data usage or simultaneous logins from different regions, both common indicators of SIM cloning or account misuse.
In addition, AI systems integrated with telecom CIAM platforms enable continuous authentication, ensuring that only verified, legitimate users maintain access over time. This combination of identity intelligence and AI detection keeps telecom infrastructures resilient against both insider and external threats.
5. Emerging Sectors: Healthcare and Travel
Even industries like healthcare and travel are rapidly adopting AI-driven fraud prevention tools.
In healthcare, AI validates patient identities, detects false claims, and flags abnormal billing behaviors to reduce insurance exploitation.
In travel, it tracks suspicious booking behaviors and prevents fraudulent use of loyalty points or stolen payment credentials, all while maintaining smooth digital experiences for legitimate customers.
Across industries, one theme remains consistent: AI doesn’t just detect fraud, it transforms digital trust.
By making authentication smarter, transactions safer, and customer journeys frictionless, AI-driven fraud prevention empowers organizations to stay one step ahead of fraudsters in every domain.
The Future of AI in Fraud Detection and Prevention
Fraud is constantly evolving, and so is AI. What started as a tool to detect anomalies has now become a strategic layer of digital defense, continuously learning, adapting, and predicting. As technology advances, AI will play an even deeper role in redefining how organizations prevent, detect, and respond to fraud in real time.
The next wave of innovation will revolve around intelligence, integration, and trust.
1. Predictive and Adaptive Risk Intelligence
Tomorrow’s fraud detection systems won’t just react to suspicious activity; they’ll predict it before it happens.
Using deep learning, pattern clustering, and historical trend mapping, AI will anticipate fraud attempts by identifying risk signatures even before a transaction takes place.
This evolution from reactive to predictive fraud prevention means organizations can deploy preemptive controls, stopping emerging attacks while keeping user journeys seamless.
2. Integration with Blockchain for Immutable Security
When combined, AI and blockchain form a powerful trust framework. Blockchain’s immutable ledger ensures transaction transparency, while AI monitors the chain for anomalies, double-spending attempts, or manipulated data.
This integration can revolutionize how businesses verify transactions, execute smart contracts, and authenticate identities securely across decentralized ecosystems.
The result? A fraud detection model that’s transparent, tamper-proof, and self-verifying.
3. AI and IoT: Securing the Connected World
With billions of devices connected globally, the Internet of Things (IoT) with ai presents a massive new attack surface.
AI’s role here is crucial; it will act as the real-time watchdog, analyzing device interactions, location consistency, and behavioral anomalies across networks.
For example, if a smart home device begins transmitting data at odd hours or to unfamiliar endpoints, AI can flag or disconnect it instantly.
This kind of autonomous AI oversight will become essential as industries embrace IoT-driven operations, from connected cars to digital healthcare systems.
4. AI-Driven Biometrics and Continuous Authentication
The future of authentication is not static passwords; it’s AI-powered biometric intelligence.
Advanced AI models will analyze multi-layered biometric data such as facial expressions, voice modulation, gait patterns, and even micro-movements to verify identities in real time.
Unlike traditional biometrics, which verify once at login, continuous biometric authentication keeps verifying users subtly throughout their session, making it nearly impossible for impostors to stay undetected.
This will be a major step forward for both fraud prevention and user convenience.
5. Collaborative AI Networks
Fraudsters often exploit gaps between organizations, but collaborative AI networks can close those gaps.
Future systems will securely share anonymized fraud data across industries, financial, retail, and telecom, allowing AI models to learn from broader datasets.
This shared intelligence ecosystem will help businesses detect emerging fraud tactics faster and coordinate defense strategies across sectors without compromising user privacy.
6. The Human-AI Partnership
While AI is becoming increasingly autonomous, the human element remains vital. The future will see human analysts and AI systems working side by side AI handling large-scale data analysis and humans focusing on strategy, ethics, and interpretability.
This partnership ensures decisions remain transparent and fair, especially as regulations tighten around automated fraud detection.
As these advancements unfold, AI-driven fraud prevention will no longer be a reactive security layer it will be a core business capability.
From predictive analytics and federated intelligence to behavioral trust modeling, AI will form the backbone of a world where every transaction, login, and identity is continuously protected by intelligent security.
Conclusion
In a world where digital interactions are growing faster than security can catch up, AI-driven fraud detection and prevention has become the new cornerstone of digital trust. Unlike traditional systems that react after damage is done, AI empowers businesses to predict, prevent, and protect in real time, transforming fraud management from a defensive measure into a proactive strategy.
The real advantage lies not only in detecting anomalies but in understanding behavior, knowing when something doesn’t feel right, and acting instantly without disrupting genuine users. When combined with a Customer Identity and Access Management (CIAM) platform, AI transforms authentication into a dynamic, risk-aware experience, one that adapts to user context, device, and behavior seamlessly.
Businesses that embrace this intelligence-led model gain far more than just protection they gain resilience, reputation, and trust. From securing financial transactions to defending digital identities, AI is now the silent guardian of every secure interaction, every verified user, and every brand that values safety as much as convenience.
Fraudsters innovate. So should you. As the digital landscape expands, relying on outdated, rule-based fraud detection systems is no longer enough. The future belongs to organizations that harness AI to anticipate risk, protect identities, and build confidence at every digital touchpoint.
Don’t wait for fraud to expose your vulnerabilities; prevent it before it happens.
Ready to fortify your CIAM strategy with AI-driven fraud detection?
Discover how LoginRadius can help you implement adaptive, intelligent, and real-time fraud prevention without compromising user experience. Book a personalized demo.




