Introduction
Multi-Factor Authentication (MFA) is a security approach that verifies a user’s identity using multiple independent factors instead of relying on just a single factor, usually password. These factors typically fall into four categories:
-
something you know (password or PIN)
-
something you have (a mobile device or security key)
-
something you are (biometric data like fingerprints or facial recognition)
-
Something you do (interactions with apps or websites).
The idea behind MFA is simple: even if one factor is compromised, the attacker still cannot gain access without the others. Cybersecurity has evolved from MFA being a recommended security feature to a baseline requirement for protecting modern digital systems.
Why MFA matters
-
Adds a second line of defense when credentials are exposed in data breaches
-
Limits the impact of automated attacks like credential stuffing and brute force
-
Enables risk-based authentication by adapting security based on user behavior and context
-
Reduces dependency on passwords, which are inherently weak and reusable
-
Strengthens overall identity security without requiring major infrastructure changes
In essence, MFA shifts authentication from a single point of failure to a layered defense system, making unauthorized access exponentially more difficult.
MFA doesn’t just strengthen security, it changes the rules of access control in your favor.
MFA by the Numbers
-
MFA blocks 99.9% of automated attacks (Microsoft)
-
Over 80% of breaches involve stolen credentials (Verizon DBIR)
-
The average cost of a data breach is $4.88 million (IBM 2024)
-
90% of cyberattacks start with phishing (Google / Mandiant)
These numbers make one thing clear: MFA is no longer optional for modern security.
In this guide, we break down the top benefits of MFA, supported by real-world examples, security insights, and practical implementation considerations to help you choose the right approach for your use case. If you are looking for a comprehensive guide on what is mfa, then please read this other blog of ours and come back here.
Common Multi-Factor Authentication Methods
SMS or Email-Based One-Time Passwords (OTP)
Imagine you’re logging into your online banking account, and right after entering your password, you receive a six-digit code via text or email. This one-time password (OTP) is only valid for a short time, making it difficult for hackers to use stolen credentials alone.
While this is a widely used method, it’s not foolproof SIM swapping and phishing attacks can still pose a risk. However, one of the benefits of two-factor authentication is that it provides an added security step.
Authenticator Apps Generating Time-Based One-Time Passwords (TOTP)
Apps like Google Authenticator or Microsoft Authenticator take OTPs to the next level. Instead of relying on SMS or email, they generate codes directly on your device every 30 seconds. This method significantly reduces the risk of interception and is commonly used in securing email and cloud accounts.
Hardware Tokens
For industries dealing with highly sensitive data, hardware tokens provide an extra layer of security. These are physical devices, like YubiKeys, that generate codes or require tapping on a USB port for authentication.
While incredibly secure, they can be inconvenient if lost or misplaced. This is an important aspect when considering the pros and cons of multi-factor authentication for an organization.
Biometric Authentication
You probably unlock your phone using your fingerprint or facial recognition—this is biometric authentication in action.
From Apple’s Face ID to Windows Hello, biometrics provide a seamless and highly secure authentication method, as they rely on unique personal traits that cannot be easily replicated.
Push Notifications on Registered Devices
Instead of entering a code, push notifications allow users to verify logins with a simple tap on their mobile devices.
For example, when logging into Gmail from a new device, Google might send a prompt that says “Was this you?” to your phone, letting you confirm the login attempt instantly. This method reinforces why you should use the multi-factor authentication approach for strong security.
Learn how to incorporate push notification MFA into your apps with LoginRadius.
Why is MFA Good for Security?
Before we learn the benefits of multi-factor authentication, let’s understand why MFA is good for security. The answer lies in its ability to stop unauthorized access in its tracks. Even if a hacker manages to steal your password, they would still need the second (or third) authentication factor to gain access.
MFA significantly reduces the risk of cyber attacks such as phishing, credential stuffing, and brute-force attacks. It’s particularly valuable for businesses with remote employees, as it ensures that only verified users can access company systems, reducing the risk of a data breach. These are key MFA benefits that improve cybersecurity measures.
Hardening the Security Perimeter
1. Enhanced Security
Hackers love weak passwords. MFA ensures that even if your password gets leaked, cybercriminals still can’t access your account without additional verification. This is a core reason why MFA is important in securing online accounts. MFA significantly improves account security by requiring multiple forms of verification.
According to Microsoft, MFA can block over 99.9% of automated attacks, making it one of the most effective defenses against credential-based threats.
For example, even if an attacker steals a password, they still need access to the second factor, such as a mobile device or biometric verification, making unauthorized access far more difficult.
2. Reduced Risk of Unauthorized Access
Think of MFA as an extra lock on your door. Even if someone picks the first lock (password), they still need a second key (a fingerprint, OTP, or hardware token) to break in.
MFA adds an additional layer of protection that prevents unauthorized users from accessing accounts, even when credentials are compromised.
The Verizon Data Breach Investigations Report states that over 80% of breaches involve stolen or weak credentials. MFA directly addresses this risk by requiring a second factor beyond the password.
For example, in credential stuffing attacks where attackers reuse leaked passwords across multiple accounts, MFA blocks access unless the attacker also has access to the second factor.
Passwords alone fail. MFA closes the gap.
3. Protection Against Phishing Attacks
Phishing emails trick users into entering their passwords on fake websites. But with MFA, stolen passwords alone aren’t enough to gain access, preventing attackers from infiltrating accounts.
Phishing remains the most common entry point for cyberattacks, but MFA significantly reduces its effectiveness.
According to Google and Mandiant, over 90% of targeted attacks begin with phishing attempts. MFA ensures that stolen credentials alone are not enough to gain access.
However, it’s important to note that not all MFA methods are equally secure. Phishing-resistant methods like passkeys and hardware security keys offer stronger protection compared to SMS-based OTPs.
4. Future-Proof Security Architecture
MFA is a foundational component of modern identity and access management strategies, including Zero Trust security models.
As organizations move toward passwordless authentication, adaptive security, and decentralized identity, MFA acts as a bridge between traditional and next-generation authentication systems.
Implementing MFA today ensures that your authentication infrastructure is ready to evolve with future security standards and technologies.
User Experience & Trust
1. Improved User Trust and Confidence
Users are more likely to trust platforms that prioritize security and protect their accounts from unauthorized access.
When users see MFA options such as biometric login or push notifications, it signals that the platform takes security seriously.
This increased trust can lead to higher user retention, better brand reputation, and stronger customer relationships especially in industries like finance, healthcare, and eCommerce.
2. Better User Experience with Modern Methods
Modern MFA methods have evolved to reduce friction while maintaining strong security.
Technologies like push notifications, biometrics (Face ID, fingerprint), and passkeys provide seamless authentication experiences without requiring users to remember complex passwords.
According to FIDO Alliance data, passkey-based logins show significantly higher success rates compared to traditional password-based logins, improving both usability and security.
3. Reduced Password Fatigue
Users often struggle with managing multiple complex passwords, leading to reuse and weak password practices.
MFA reduces reliance on passwords by introducing additional authentication methods, allowing users to adopt simpler and more secure login experiences.
With the rise of passwordless authentication and passkeys, MFA is helping eliminate password fatigue altogether while improving security outcomes.
Business Operations & Compliance
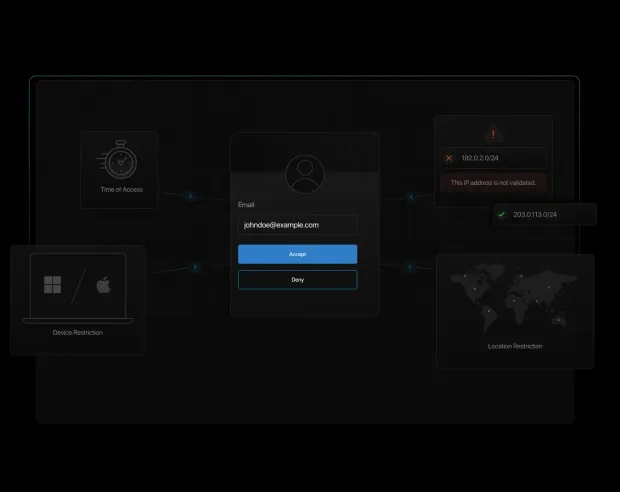
1. Customizable Security Policies (Adaptive MFA)
MFA enables organizations to implement flexible, risk-based authentication policies tailored to different users and scenarios.
Adaptive MFA evaluates contextual signals such as location, device, IP address, and user behavior to determine whether additional verification is required.
For example, a login attempt from a trusted device may require only a password, while a login from a new country may trigger step-up authentication. This approach improves both security and user experience.
You can quickly configure adaptive authentication with LoginRadius.
2. Cost Savings from Preventing Breaches
Implementing MFA can significantly reduce the financial impact of cyberattacks.
The IBM Cost of a Data Breach Report (2024) estimates the average breach cost at $4.88 million globally. Preventing even a single breach can save organizations substantial financial losses.
Additionally, MFA reduces costs associated with account recovery, fraud, legal penalties, and reputational damage.
3. Compliance with Security Regulations
MFA helps organizations meet regulatory and compliance requirements across multiple industries.
Frameworks such as PCI DSS 4.0, HIPAA, GDPR, and NIST 800-63B require or strongly recommend multi-factor authentication for protecting sensitive data.
By implementing MFA, organizations not only improve security but also reduce audit risks and ensure compliance with industry standards.
MFA enables businesses to track login attempts, enforce role-based access controls, and mitigate insider threats by ensuring that only authorized personnel can access critical systems.
Real-World Examples Where MFA Prevents Attacks
-
Colonial Pipeline Attack (2021): A compromised VPN account without MFA led to a ransomware attack, causing major operational disruption.
-
MGM Resorts Breach (2023): Attackers used social engineering and weak authentication methods, resulting in over $100 million in damages.
-
Credential Stuffing Attacks: Millions of accounts are compromised annually using reused passwords MFA prevents these by requiring a second factor.
These incidents highlight the real-world importance of MFA in preventing large-scale breaches.
MFA vs 2FA vs Passwordless Authentication
| Feature | MFA | 2FA | Passwordless |
|---|---|---|---|
| Number of Factors | 2 or more | Exactly 2 | No password |
| Security Level | High | Medium–High | Very High |
| Phishing Resistance | Medium–High | Medium | Strong |
| User Experience | Moderate | Moderate | Seamless |
| Best Use Case | Enterprises, SaaS | Standard apps | Modern, passwordless systems |
MFA Benefits: Businesses vs Individuals
| Audience | Key Benefits |
|---|---|
| Businesses | Prevent breaches, ensure compliance, reduce financial risk |
| Individuals | Protect personal accounts, prevent identity theft, secure devices |
MFA and Regulatory Compliance
MFA is not just a security best practice—it is a requirement across multiple frameworks
-
PCI DSS 4.0 mandates MFA for all access to cardholder data
-
HIPAA requires strong authentication for healthcare systems
-
NIST 800-63B defines MFA assurance levels
-
GDPR Article 32 mandates appropriate security measures
-
SOC 2 requires secure access control mechanisms
Implementing MFA helps organizations meet compliance requirements while reducing audit risks and penalties.
Conclusion
Authentication is no longer just about logging users, it's about protecting identities in an increasingly hostile digital environment.
Multi-Factor Authentication (MFA) plays a critical role in this shift. It reduces reliance on passwords, mitigates modern attack vectors like phishing and credential stuffing, and adds a resilient layer of defense across applications, APIs, and user journeys.
More importantly, MFA is not just a security upgrade, it's a business enabler. It helps organizations build trust, meet compliance requirements, and protect both user data and brand reputation.
As threats continue to evolve, so must authentication strategies. Modern implementations of MFA such as adaptive authentication, biometrics, and passwordless methods are making it possible to achieve both strong security and seamless user experience.
The question is no longer whether you should implement MFA, but how effectively you can deploy it.
Get Started with MFA Using LoginRadius
If you're looking to implement secure, scalable MFA for your applications, LoginRadius provides everything you need to get started quickly:
-
Support for multiple MFA methods (OTP, push, biometrics, passkeys)
-
Adaptive MFA with risk-based authentication
-
Developer-friendly APIs and SDKs
-
Pre-built authentication workflows for faster integration
Explore the documentation or book a demo
Build a stronger authentication layer today and stay ahead of tomorrow’s threats.
FAQs
Q: What is the risk of not using multi-factor authentication?
A: Without MFA, your accounts are vulnerable to hacking, phishing, and credential stuffing. A single stolen password can lead to a full-blown data breach.
Q: The Importance of MFA for Securing Remote Access?
A: Remote work exposes businesses to cyber threats. The importance of MFA lies in ensuring that employees can securely access corporate systems from anywhere without increasing security risks.
Q: Are magic links more secure than password authentication?
A: Magic links offer convenience but are only as secure as the email account receiving them. MFA remains a stronger option as it requires multiple authentication steps.
Q: What types of authentication solutions are available?
A: Authentication methods include passwords, security questions, MFA, biometrics, hardware tokens, and risk-based authentication. The best approach combines multiple layers of security. By implementing MFA, businesses can ensure stronger security, reduce risks, and build trust among users. If you haven’t already adopted MFA, now is the time to do so!
Q: What is the biggest benefit of MFA?
A: The biggest benefit is preventing unauthorized access, even if passwords are compromised.
Q: Does MFA stop phishing attacks?
A: MFA reduces phishing risks, but only phishing-resistant methods like passkeys provide full protection.
Q: Which MFA method is most secure?
A: Hardware keys and passkeys offer the highest level of security.
Q: Is MFA required for compliance?
A: Yes, many frameworks like PCI DSS and HIPAA require MFA.