Introduction
If you search for the best CIAM platforms, the results start to blend together quickly. Every vendor claims strong security, smooth authentication, flexible APIs, and a developer-friendly setup. On paper, it all looks polished. In practice, the differences show up the moment implementation begins.
That is where teams usually get stuck.
A CIAM platform is not just something that handles login. It shapes how you launch products, manage customer identities, support compliance, scale globally, and reduce security risk over time. Pick the wrong one, and the problem is not limited to authentication. It spills into developer effort, integration complexity, audit readiness, and long-term maintenance. Infrastructure decisions do that. They stay with you.
Auth0, Keycloak, AWS Cognito, and LoginRadius are four of the most recognized names in this space. All of them support core identity functions such as token issuance, OAuth, OpenID Connect, and social login. But feature overlap does not mean platform fit. That is the part comparison pages often skip.
Some platforms work well for teams that want fast experimentation. Some make more sense if you already have strong in-house engineering and DevOps support. Some fit naturally inside a single cloud ecosystem. Others are built for enterprises that need stronger compliance controls, data residency, flexible deployment, and customer identity management at scale without building too much of the identity layer themselves.
So the real question is not which CIAM platform has more features. It is which one that fits your architecture, security model, compliance needs, operational capacity, and growth plans.
Because setting up authentication is one thing. Building an identity infrastructure you can live with for years is something else entirely.
What Enterprise CIAM Actually Means
Before comparing features, pricing tiers, or SDKs, we need to clarify something important: enterprise CIAM is not just “login for customers.”
Traditional IAM was built for employees. Controlled environments. Known devices. Predictable usage patterns. Enterprise CIAM, on the other hand, deals with millions of unpredictable users logging in from everywhere, at any time, on any device. That changes everything.
Enterprise CIAM platforms must handle massive concurrency without breaking session management. They must support global traffic while respecting regional data residency laws. They must enforce strong ciam security controls without turning login into a 12-step obstacle course.
Then there’s compliance. GDPR. HIPAA. SOC 2. PIPEDA. Industry-specific regulations. Enterprise CIAM solutions must support consent management, audit logging, encryption standards, and configurable data retention policies. This isn’t optional. It’s table stakes.
Scalability is another non-negotiable. Consumer traffic spikes are not polite. They don’t announce themselves. A marketing campaign, a product launch, or a viral moment can multiply authentication load instantly. Enterprise-grade ciam providers must scale elastically without degrading user experience.
And modern enterprises rarely operate in just one model. They support B2C users, B2B partners, resellers, and sometimes internal dashboards all through a unified identity layer. That requires flexible multi-tenant architecture and advanced access controls.
So, before asking which is the best ciam solution, the real question is: does the platform treat identity as a lightweight plugin or as a core architectural system designed for enterprise scale and security? Because that distinction decides everything that follows.
Evaluation Criteria: What Actually Matters in CIAM Security
Now that we’ve established what enterprise CIAM really involves, let’s talk about how to evaluate ciam platforms without getting distracted by shiny dashboards and marketing phrases.
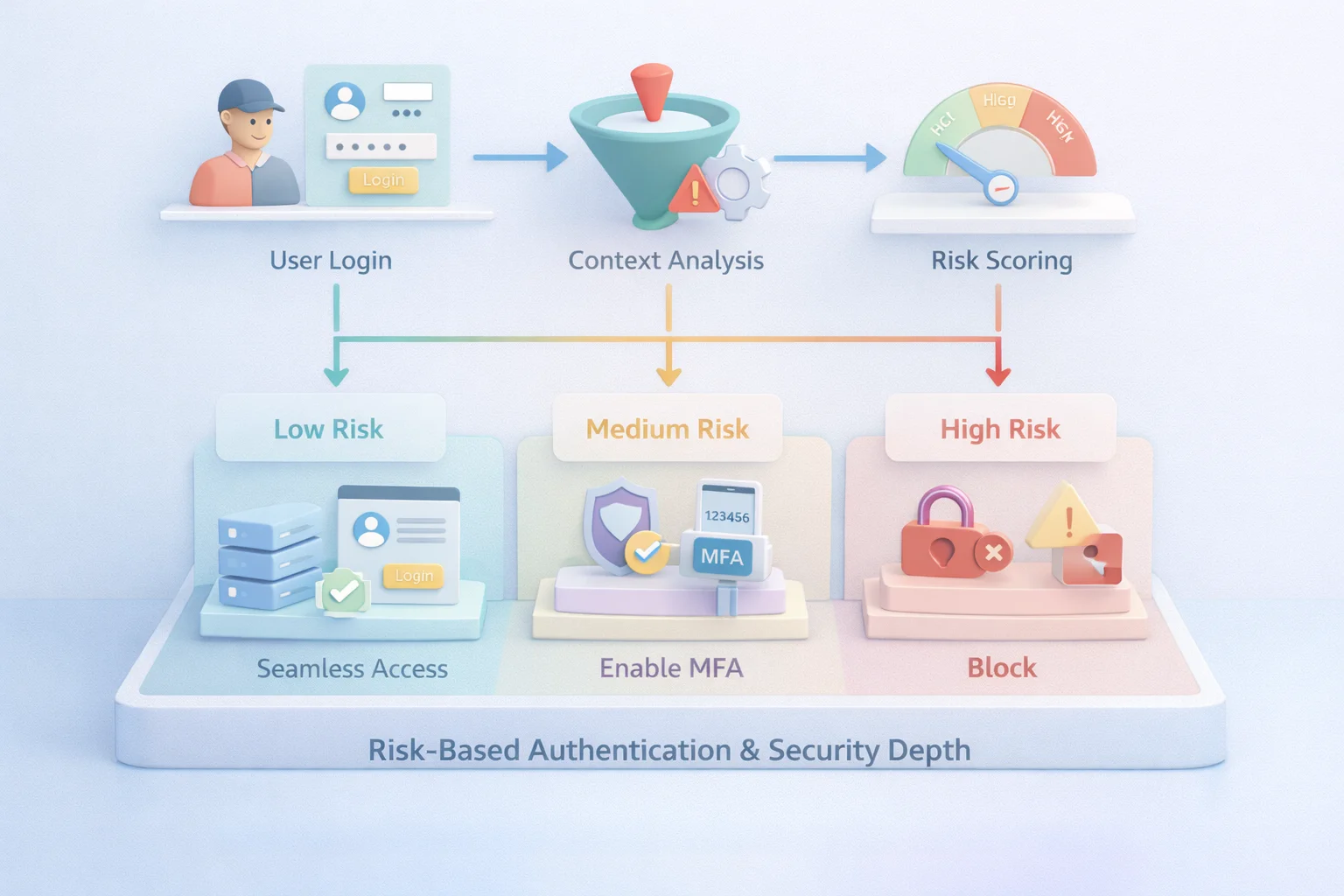
First, security depth. Not just “supports MFA,” but how. Does the platform offer adaptive authentication? Risk-based challenges? Bot detection? Credential stuffing protection? Enterprise ciam security is layered. If the solution only checks a password and issues a token, it’s not enterprise-ready.
Second, scalability under real-world pressure. Can it handle millions of identities without performance degradation? Does token issuance remain fast during peak traffic? Can it support global regions without routing everything through a single data center?
Third, architectural flexibility. Some ciam providers are optimized for a single-cloud ecosystem. Others are multi-cloud friendly. Some require heavy customization for B2B use cases. Enterprise CIAM solutions must support multi-tenant models, custom roles, API security, and integration with downstream systems.
Fourth, compliance and data residency. Enterprises operating in regulated markets need configurable data storage locations, audit trails, and strong encryption controls. If your ciam solution makes compliance a “future roadmap item,” that’s a red flag.
Fifth, developer experience and extensibility. Enterprise teams rarely run identity “out of the box.” They extend it. They customize workflows. They integrate fraud engines and analytics systems. A CIAM platform that resists customization becomes friction for engineering teams.
Finally, cost transparency. Usage-based pricing can look attractive at low volumes. At scale, it can become unpredictable. Enterprise buyers don’t just evaluate features; they evaluate long-term cost stability.
The best ciam solutions are not necessarily the ones with the most features. They are the ones that align security, scalability, compliance, and architecture without forcing your team to become identity engineers overnight.
Auth0 vs Keycloak vs Cognito: Same Problem, Very Different Trade-Offs
Auth0, Keycloak, and AWS Cognito almost always show up in the same conversation. On paper, they check similar boxes: OAuth, OpenID Connect, MFA, social login. So the comparison looks straightforward. It isn’t.
Here’s where it gets interesting.
Each of these platforms represents a completely different philosophy of identity. And that difference only becomes visible once you move past quick setup and start thinking about scale, operations, and long-term ownership.
Take Auth0. It’s often the easiest place to start. Clean SDKs, strong documentation, fast time to implementation it just works, especially for teams that want to move quickly. But once usage grows, things change.
Pricing starts becoming part of architecture decisions. Enterprise requirements like complex B2B structures, regional hosting, or advanced workflows may need deeper configuration or higher tiers. A surprising pattern we’ve seen: teams choose Auth0 for speed, then revisit that decision when scale and cost collide.
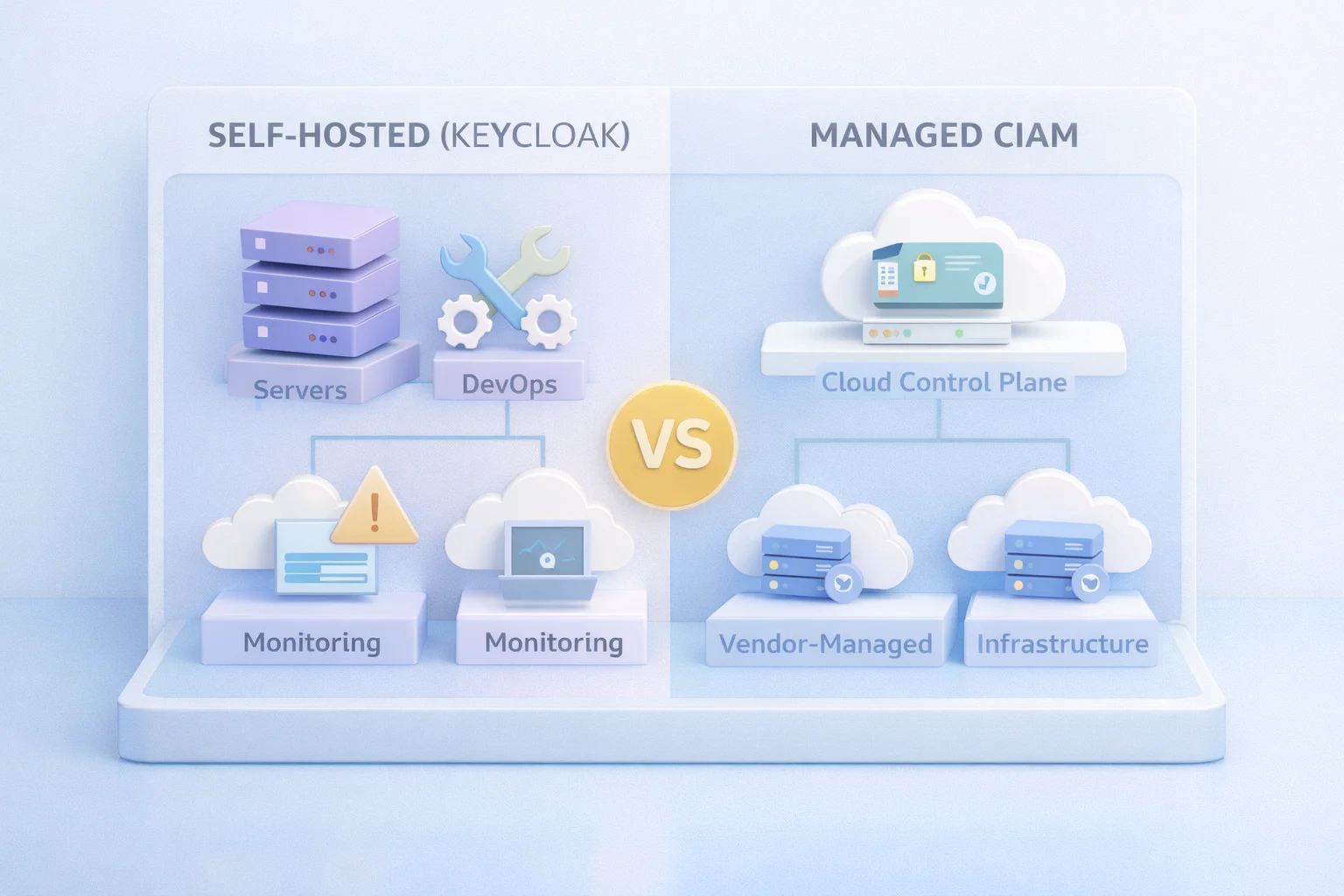
Now contrast that with Keycloak. Completely different trade-off. It gives you control full control. You can shape your identity layer exactly how you want. No licensing constraints. No vendor lock-in. Sounds great, right? Until you realize what comes with it.
You are now responsible for uptime, scaling, patching, monitoring, and security hardening. All of it. At a small scale, manageable. At enterprise scale, it becomes a full-time discipline. This is where teams usually go wrong: they underestimate what “owning identity infrastructure” actually means.
Then there’s AWS Cognito. It fits naturally if your stack already lives inside AWS. Integration feels smooth. Setup is familiar. For many teams, it becomes the default choice without much debate.
But step outside that comfort zone, multi-cloud setups, complex B2B requirements, deep customization and friction starts showing up. You can extend it, of course. But that usually means more engineering effort. More services. More moving parts. And over time, more architectural weight.
So while all three platforms can authenticate users, that’s not really the decision you’re making.
You’re deciding how much control you want. How much are you willing to build? How much complexity your team can realistically manage? And how your identity system will behave not just on day one, but when you have millions of users, strict compliance requirements, and zero tolerance for failure.
Because choosing a CIAM platform isn’t about features.
It’s about the kind of identity system you’re signing up to live with.
LoginRadius: Enterprise-Focused CIAM Without the DIY Burden
LoginRadius positions itself specifically as an enterprise CIAM platform rather than a general-purpose IAM tool adapted for customers. That distinction matters.
Unlike open-source frameworks that require full operational ownership, LoginRadius offers managed ciam services designed for high-scale consumer environments. The platform supports global data residency, compliance-ready infrastructure, and elastic scalability without requiring internal teams to architect identity clusters from scratch.
From a capability standpoint, it covers the expected foundations OAuth 2.0, OpenID Connect, social login, passwordless authentication, MFA, and API security. But enterprise CIAM rarely stops at foundations.
Advanced account linking is a notable differentiator. Instead of leaving identity consolidation as custom logic, LoginRadius supports automatic, consumer-initiated, and API-based linking approaches. For enterprises dealing with fragmented user identities across social and traditional login methods, that becomes operationally significant.
The benefit is not just cleaner UX. Unified identity improves behavior insights and strengthens ciam security posture by reducing duplicate accounts and takeover vectors. At enterprise scale, identity fragmentation isn’t just messy, it’s risky.
LoginRadius also leans into adaptive authentication and bot protection, which aligns well with organizations facing credential stuffing, fraud attempts, or high-volume login traffic. Enterprises that treat identity as a security perimeter rather than a login utility tend to evaluate this depth carefully.
Architecturally, it supports both B2C and B2B use cases within the same identity layer. That flexibility matters for SaaS platforms serving consumers, partners, and enterprise customers simultaneously.
In essence, LoginRadius targets organizations that want enterprise-grade CIAM solutions without becoming full-time identity infrastructure operators. It shifts the balance from building identity systems to consuming them as a managed, scalable service while still maintaining architectural control.
For enterprises evaluating ciam platforms through the lens of scale, compliance, and long-term stability, that positioning can be compelling.
Side-by-Side Comparison Table: Auth0 vs Keycloak vs Cognito vs LoginRadius
Below is a practical, enterprise-focused comparison of these leading CIAM platforms based on real-world decision criteria not just feature checklists.
| Evaluation Criteria | Auth0 | Keycloak | AWS Cognito | LoginRadius |
|---|---|---|---|---|
| Type | Managed CIAM (Okta-owned) | Open-source, self-hosted | AWS-native managed service | Enterprise-focused managed CIAM |
| Best Fit | Developer-first SaaS | Organizations with strong DevOps | AWS-native applications | Regulated enterprises & global brands |
| Enterprise CIAM Readiness | Strong, but pricing scales | Depends on your implementation | Moderate, cloud-bound | Built for enterprise scale |
| Scalability | High, usage-based | Infrastructure-dependent | High within AWS | High, multi-region scalable |
| CIAM Security Depth | MFA, extensibility | Customizable, self-managed | Basic MFA, integrations needed | Adaptive MFA, bot protection, risk-based controls |
| Account Linking | Supported (configuration required) | Custom implementation | Limited flexibility | Built-in advanced account linking |
| B2B + B2C Support | Supported (org features) | Requires customization | Limited native B2B support | Native B2B + B2C support |
| Multi-Tenant Architecture | Supported | Realm-based (manual scaling) | User pool-based | Enterprise multi-tenant design |
| Data Residency Options | Region-based | Fully controlled (self-hosted) | AWS region dependent | Global data residency options |
| Compliance Support | Enterprise tier | Self-managed responsibility | AWS compliance baseline | Compliance-ready enterprise framework |
| Customization Flexibility | High via actions/rules | Very high | Moderate | High with managed extensibility |
| Infrastructure Ownership | Vendor-managed | Fully self-managed | AWS-managed | Vendor-managed |
| Operational Overhead | Low–Moderate | High | Moderate | Low |
| Pricing Predictability | Usage-based, can scale rapidly | Infra + DevOps costs | Usage-based | Tiered enterprise pricing |
| Vendor Lock-in Risk | Moderate | Low (open-source) | High (AWS-bound) | Moderate |

Managed vs Self-Hosted CIAM: The Architecture Trade-Off
At some point in the evaluation process, the discussion shifts from features to architecture. This is where enterprise CIAM decisions become serious.
Broadly speaking, ciam platforms fall into two categories: self-hosted frameworks and managed CIAM services.
Self-hosted options, like Keycloak, give you full control. You provision infrastructure, configure clusters, manage updates, monitor performance, and enforce security controls. You decide how data is stored, how logs are handled, and how scaling works. That flexibility is powerful.
But control comes with responsibility. High availability, disaster recovery, performance tuning, and patch management become ongoing operational commitments. Enterprise CIAM environments don’t forgive downtime or misconfiguration. When millions of users depend on your authentication layer, reliability isn’t optional.
Managed CIAM solutions, on the other hand, abstract much of that operational burden. Infrastructure scaling, uptime guarantees, and security hardening are handled by the provider. Your team focuses on configuration and integration rather than cluster management.
The trade-off is not just technical it’s strategic. Self-hosted identity can reduce vendor dependency but increases engineering overhead. Managed CIAM services reduce infrastructure responsibility but require trust in the provider’s compliance posture and roadmap.
For enterprises, this often comes down to core competency. Is identity infrastructure something you want to build and operate long term? Or is it a foundational service you’d rather consume while focusing on product differentiation?
In smaller environments, self-hosting may feel economical. At enterprise scale where compliance audits, bot mitigation, adaptive authentication, and global traffic management are daily realities the cost of operational complexity becomes more visible.
The best ciam solutions for enterprise are rarely chosen based on ideology. They are chosen based on which architecture model aligns with internal expertise, security maturity, and long-term growth plans.
Use-Case Breakdown: Which CIAM Platform Fits Which Scenario?
Not every enterprise has the same identity needs. The phrase “best ciam solutions” only makes sense when paired with a specific context. Architecture, scale, compliance requirements, and internal capabilities all influence the decision.
If you’re a fast-growing SaaS startup with strong engineering talent and moderate user volume, Auth0 may feel like a natural fit. It provides flexibility, quick integration, and enough extensibility to evolve with your product without requiring full infrastructure ownership on day one.
If you’re deeply invested in AWS and building entirely within that ecosystem, Amazon Cognito can align well with your architecture. It simplifies integration with other AWS services and keeps identity within your existing cloud boundary. For AWS-native teams, that cohesion can reduce operational friction.
If your organization prioritizes full control, has DevOps expertise, and is comfortable managing identity infrastructure directly, Keycloak becomes attractive. Open-source flexibility allows deep customization. But this path assumes you’re prepared to operate identity as a long-term infrastructure commitment.
If you’re a regulated enterprise, a global consumer brand, or a B2B SaaS platform supporting multiple customer types across regions, the equation changes. Enterprise CIAM platforms that offer managed ciam services, built-in adaptive security, global data residency, and advanced account linking capabilities tend to reduce operational complexity.
In those cases, solutions like LoginRadius are often evaluated for their enterprise-specific focus.
The key is alignment. A platform that works brilliantly for a startup may create scaling pain at the enterprise level. A self-hosted solution that feels empowering early on may become resource-intensive under compliance pressure.
There is no universal winner among ciam providers. There is only the right fit for your scale, security expectations, cloud strategy, and operational model. Choosing wisely means evaluating your present reality and your future growth curve.
The Hidden Costs of CIAM Nobody Mentions in Sales Demos
When evaluating ciam platforms, most conversations revolve around features, SDKs, and pricing tiers. What rarely gets equal attention are the long-term costs that don’t show up on the first invoice.
Engineering overhead is one of them. Highly customizable systems can become highly complex systems. Every custom rule, workflow extension, or integration adds maintenance responsibility. Over time, identity logic becomes deeply embedded in your architecture, and refactoring it is rarely trivial.
Compliance preparation is another silent cost. Enterprise CIAM solutions must withstand audits. That means detailed logging, access controls, encryption policies, and documented processes. If those capabilities require manual configuration or external tooling, the operational burden increases.
Security incidents carry their own price tag. Weak ciam security configurations can lead to credential stuffing attacks, account takeovers, or session hijacking. Responding to such events is not just technical, it’s reputational and legal. Enterprises must evaluate how much built-in protection a platform provides versus how much must be layered on separately.
Scaling friction also has a cost. Platforms that perform well at thousands of users may struggle with millions. Infrastructure tuning, database scaling, and performance troubleshooting consume time and resources. What looks economical at low volume can become unpredictable at enterprise scale.
Vendor lock-in is another consideration. Deep integration with a single ecosystem can simplify development initially, but may limit flexibility later. Enterprises expanding into multi-cloud or global regions must assess whether their CIAM solution supports that evolution.
The best ciam solutions are not just judged by feature lists. They are evaluated by the total cost of ownership, engineering effort, compliance alignment, security maturity, and operational stability over time.
Identity is foundational infrastructure. The true cost isn’t just what you pay for it. It’s what you pay to maintain, secure, and scale it over the life of your platform.
Enterprise Decision Framework: How to Choose the Right CIAM Platform
After comparing features, architectures, and trade-offs, the final decision shouldn’t feel like guesswork. Enterprise CIAM selection works best when approached as a structured evaluation not a brand popularity contest.
Start with scale reality. How many users do you support today, and what does your growth curve look like over the next three to five years? A platform that performs well at 500,000 identities may behave very differently at 20 million. Enterprise CIAM platforms must demonstrate proven high-concurrency performance.
Next, clarify your security posture. Are you operating in a high-risk industry where fraud, bot attacks, and credential stuffing are daily concerns? If so, ciam security depth becomes a deciding factor. Built-in adaptive authentication, anomaly detection, and advanced account protection should not be optional add-ons.
Then evaluate compliance requirements. Do you require specific data residency regions? Do you need audit trails that satisfy regulatory audits? Are you subject to GDPR, HIPAA, or region-specific privacy mandates? Enterprise CIAM solutions must align with these constraints without excessive customization.
Cloud strategy is another critical input. Are you single-cloud, multi-cloud, or hybrid? Platforms tightly bound to one ecosystem may simplify integration initially but complicate expansion later. Enterprises with global ambitions often prioritize flexibility.
Operational maturity also matters. Do you have an internal team ready to manage identity infrastructure long term? Or do you prefer managed ciam services that reduce operational responsibility? The right answer depends on your internal capabilities and risk tolerance.
Finally, assess architectural alignment. Do you need strong B2B support alongside B2C? Do you require advanced account linking? Do you anticipate complex partner hierarchies or delegated administration? Not all ciam providers handle these scenarios equally well.
Choosing the best ciam solutions is less about selecting the most feature-rich platform and more about selecting the one that fits your enterprise architecture, compliance landscape, and growth strategy.
When identity becomes foundational to your customer experience, the right CIAM platform doesn’t just authenticate users; it supports your business at scale, securely, and sustainably.
Conclusion
At a glance, Auth0, Keycloak, Cognito, and LoginRadius all appear capable. They support OAuth. They issue tokens. They handle social login. On a feature checklist, the differences can seem subtle. But enterprise CIAM isn’t won on checklists.
It’s won on how well the platform handles scale spikes, compliance audits, bot attacks, regional data requirements, B2B complexity, and long-term architectural evolution. It’s won on whether your team can operate it sustainably for years, not just on whether it can be launched quickly.
Auth0 offers flexibility and strong developer adoption. Keycloak provides control and open-source extensibility. AWS Cognito aligns tightly with AWS-native environments. LoginRadius focuses specifically on enterprise-grade CIAM with managed services and built-in capabilities designed for large-scale customer ecosystems.
None of these options are universally “best.” Each serves a different architectural philosophy.
The real decision comes down to this: do you want to build and operate identity infrastructure yourself, adapt a cloud-native tool to enterprise needs, or adopt a purpose-built enterprise CIAM platform designed for scale and compliance from the start?
Identity is no longer just a login screen. It’s a security perimeter, a compliance boundary, and a growth enabler. Choose a CIAM platform that fits your enterprise reality—not just your current roadmap.
Because in enterprise environments, authentication is the entry point. Sustainable identity architecture is the long game.
Choosing the right CIAM platform is a long-term architectural decision. Don’t gamble on identity. Talk to our CIAM experts and see how an enterprise-ready platform can support your scale, compliance, and security goals.



