Hey there! Today, let's talk about something huge that most people never even think about until it's too late: Identity Security.
In today's digital world, you shop online, pay bills, and manage your health via apps and websites. Yet, every time you log on, you're giving some company the keys to your personal castle.
Cyber attackers know this. They don't attempt to hack servers anymore; they try to steal you - your username, your password, your digital identity.

The good news? We now have a solid plan, a playbook, to fight back. This guide will take you through building a modern Identity Security strategy using Customer Identity and Access Management, or CIAM.
We'll show you exactly how to stop fraud before it even starts, catch threats in real time, and, best of all, do all that without annoying your customers. This is at the very core of a Zero-Trust Customer Experience or Zero-Trust CX.
It's time to make security smart, invisible, and focused on the protection of the one identity that really matters: the customer's.
Why Identity Is the #1 Attack Surface
Think of your company's network like a high-security office building. A few years ago, attackers focused on blowing up the walls - that is, the network perimeter - trying to break into the main servers.
Today, those walls are gone, replaced by everyone working from home, on coffee shop Wi-Fi, using their personally-owned devices. The network boundary has disappeared and the main doors are wide open.
So, where do attackers go? They go for the people.
Your customer's identity is the new front door.
Simply put, an identity is a set of credentials that grants a person access: a username, a password, a phone number, and biometrics. Thus, attackers don't have to break in; they merely log in with their stolen identity.
-
Poor Passwords : Simple passwords used across numerous sites by many people.
-
Stolen Data : Major breaches keep leaking billions of credentials online.
-
Frictionless Access : As businesses make it easier to sign up and log in, sometimes they accidentally give fraudsters an easier time.
Major security reports confirm that the vast majority of all breached records are due to unauthorized access using stolen or guessed identities. If you protect the identity, you protect everything. That's why having an Identity Security Playbook is essential.
Types of Account Fraud: The Attacks You Must Stop
Fraudsters are creative. They use different methods, depending on what they want to steal: money, data, or just the ability to cause chaos. In the CIAM world, here are four major threats you need to look out for:
1. Fake Accounts: New Account Fraud, or NAF
This happens when one creates a completely new account using either stolen or fake personal information. They might use a bot to create hundreds of accounts in a minute. Why? To claim signup bonuses, try free trials, or create many accounts for phishing later.
2. Account Takeover (ATO)
This is the big one: An attacker uses stolen credentials-the result of a data breach and often bought on the dark web-to log into a real, existing customer account. They can then change the shipping address, pilfer stored payment details, or transfer money. The aim is to impersonate the customer perfectly.
3. Credential Stuffing
This is a specific type of ATO. Attackers take lists of usernames and passwords stolen from other company breaches and "stuff" them into your login page. Because so many people reuse passwords, this attack tends to work far better than one might expect.
4. Magic Link Abuse
Many companies provide passwordless sign-in today, such as sending a "magic link" to your email address or sending an OTP to your phone. This is usually safer, but does not prevent abuse from attackers altogether. They may:
-
Trigger endless links to spam a user's inbox; Denial of Service.
-
Social engineering to dupe a customer into giving out the link/code.
Your CIAM system needs to be smart enough to identify the difference between a real customer and any of these threats.
Threat Detection: The CIAM Security Brain
How do you keep security high yet make the login process easy for real customers? The secret is Threat Detection in CIAM.
Rather, the system should act more like an intelligent security guard that knows who the regulars are: only challenging those that appear risky, based on suspicious behavior.
This demands that one go beyond mere passwords or MFA to Risk-Based Authentication.
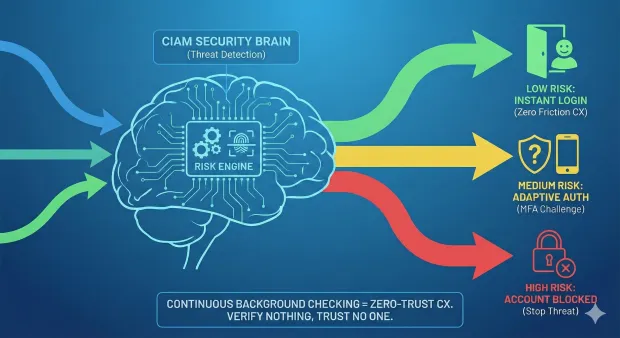
The CIAM is like a brain that continuously receives information and analyses it through a risk engine. That engine looks at each action, from signup down to checkout, and decides whether or not the individual is trusted.
-
If the risk is low: The customer logs in instantly - Zero Friction CX.
-
Medium risk: adaptive authentication is requested to perform an additional check, such as a one-time code.
-
If the risk is high, then the account is either completely locked or blocked.
This is constant, quiet background checking. That's how you create a Zero-Trust CX. You verify nothing and trust no one until the system proves their identity.
Bot Control, Brute-Force Protection, and Lockouts
Specific tools are required to fight back when it comes to automated attacks. These defensive layers make up your playbook:
1. Bot Control and CAPTCHAs
Bots are software programs that try to overwhelm your signup or login pages. Modern Bot Control uses sophisticated detection that looks at how a user moves the mouse or types-not just simple 'I am not a robot' checkboxes, though those still help. The idea is to make the automated attack too slow and expensive for the fraudster.
2. Brute-Force Protection
A brute-force attack involves a bot trying thousands of combinations of passwords or guessed usernames at a very rapid rate. This generally occurs on the login page. The CIAM system should detect this unusual speed and frequency.
3. Lockouts and Throttling
The barrier to brute-force attacks lies in these two simple yet effective defence mechanism:
-
Lockout : If a user or a bot fails to enter the correct password three to five times, an account is locked for 30 minutes. This stops rapid guessing.
-
Throttling : When this system detects too many requests, it slows down the response time from the same IP address. If a bot tries 100 logins a second, then throttling makes each login take 5 seconds, ruining an attacker's speed advantage.
These measures will protect the system without unduly punishing a legitimate customer who may have forgotten his password once or twice.
Fraud Signals: The Data That Tells the Story
How does a CIAM risk engine know whether the user is a regular or a fraudster? By gathering and analyzing a stream of signals. These are the key clues to create a real-time risk profile:
1. IP Risk Score
Every device on the internet has an IP address, which in simple terms is like a digital street address. The system checks this address against massive databases in order to see:
Is it from a country where the customer normally lives?
Is this a known VPN or proxy used to disguise a true location?
Does the IP address have a history of prior attacks or spam activity?
If the system sees a login attempt from an IP address classified as high risk-say, a known malicious server farm-the risk score goes up instantly.
2. Device Fingerprinting
This technique looks at the specific device that a user is logging in from, considering factors such as:
-
The type of browser used: Chrome, Firefox.
-
Operating system: Windows 11, iOS 17.
-
The screen size and fonts installed.
Put these together, and you have a sort of "fingerprint" for that particular device. If a customer always logs in from their Samsung phone with the same version number of the same browser, and then an attempt comes from a brand-new desktop computer in another city, the system suspects something is amiss.
3. Velocity Checks
Velocity identifies the speed and rate of user events. This is an effective method to detect bots and script attacks. For instance, the system tracks:
-
Login Velocity : A human can only try a few logins per minute. A bot can try thousands.
-
Account Creation Velocity : Does one IP address create 50 new accounts in 10 minutes? That is a huge fraud signal.
-
Location Velocity (Impossible Travel) : Did the user log in from London one minute and then successfully log in from Tokyo five minutes later? Since such travel is not possible, this is a clear sign of a compromised account, likely by different attackers or a VPN/ proxy switch.
Identity Attestation and the Confidence Score
All those signals do not just sit there: IP, device, and velocity are fed into a machine learning model that weighs together to come up with a single, crucial number, which is the Identity Confidence Score or Identity Attestation.
This score is the brain's final answer to the question: "How sure are we that this person is the real customer?"
-
A score of 95+ means the system is highly confident. The user logs in instantly, enjoying a frictionless experience.
-
A score of 50-95 might trigger a step-up. The system is fairly sure, but needs one extra check-just to be certain.
-
A score of less than 50 results in an immediate block or a challenge that requires human verification.
The beauty of this system is that it delivers the Zero-Trust CX promise, which is maximum security with minimum customer friction. The trustworthy customer never sees the security walls, while the attacker immediately runs into brick walls.
Transaction-Level Authentication (Step-Up Security)
Authentication of the login is only the beginning. Sometimes, a legitimate customer will have their session hijacked, or they might be logging in from an unfamiliar location. In these high-risk moments, you need Transaction-Level Authentication.
This is the principle of "step-up" security. You don't ask for extra proof until the user attempts to do something sensitive.
Now, imagine you log in to your banking app without any problem, but after that, you want to do something such as:
-
Transfer $5,000 to a new account.
-
Change your password or phone number.
-
Add a new credit card to your file.
Learn how LoginRadius step-up authentication works like a breeze in high-risk scenarios:
These are high-risk actions. The CIAM system notices the action and temporarily raises the risk level. Even if the user is already logged in, the system pauses and asks for a second factor—a fingerprint scan, a face ID check, or a code sent to their registered device.
The approach ensures that, even if an attacker successfully logs in-ATO-they are stopped cold the moment they try to steal money or permanently hijack the account.
How LoginRadius Cuts Fraud Without Killing UX
Of course, many successful companies, like those that leverage platforms like LoginRadius, have mastered this juggling act of combining robust security with a smooth customer flow. They understand that if security is too difficult, customers will leave; if security is too weak, customers will be breached.
Their approach is based on the main elements of a modern Identity Security Playbook:
Prioritizing Passwordless
They focus on authentication methods such as magic links, biometrics, and social login. These are considerably easier for a customer yet much harder to steal or guess by fraudsters than traditional passwords. This immediately reduces the threat of credential stuffing.
Leveraging Risk-Based MFA
Instead of forcing every customer to enable MFA for every login, which creates friction, they are using the Identity Confidence Score. If a user is logging in from his usual device and at his usual time, he gets waved right through. If the user is logging in from a new country at 3 a.m., instantly, he gets hit with an MFA code coming via text message. That keeps the experience flawless for 95% of users. Learn more about risk-based MFA.
Real-time Behavioral Analysis
They constantly observe user behavior, velocity, and device profiles to derive trust. And when a user attempts to create an account, their system uses dozens of signals in milliseconds to analyze whether the sign-up is human or a bot, preventing New Account Fraud (NAF) well before the account is fully created.
This invisible yet intelligent combination of security minimizes the number of steps required by a real customer while maximizing the barriers for an attacker. It simply shows that one can absolutely cut fraud without killing the user experience.
Conclusion: Your Next Step to a Secure Future
Identity is the root of all digital trust. As part of an Identity Security Playbook focused on Zero-Trust CX, you're accomplishing a dual purpose:
Safeguard your company against major financial loss and reputational damage from fraud.
Delivering a great, frictionless experience to your customers, building loyalty.
Gone are the days of simple, static passwords. The future of security is dynamic, intelligent, and identity-centered.