Introduction
Most teams don’t sit down to compare JWT vs. session-based authentication when everything is running smoothly. That conversation usually starts when something breaks, traffic spikes, a new region goes live, or users suddenly get 401 Unauthorized errors even though they just logged in. One engineer points at the session store. Another says, “This wouldn’t happen with JWT.” And just like that, a design decision becomes a production problem.
This isn’t a theoretical debate. It’s about how session-based and JWT-based authentication behave under real-world pressure, in distributed systems, with unpredictable traffic, and with multiple services talking to each other. Both approaches work well in simple setups. Both are widely adopted. But at scale, they fail in very different ways—and those failures can directly impact performance, reliability, and security.
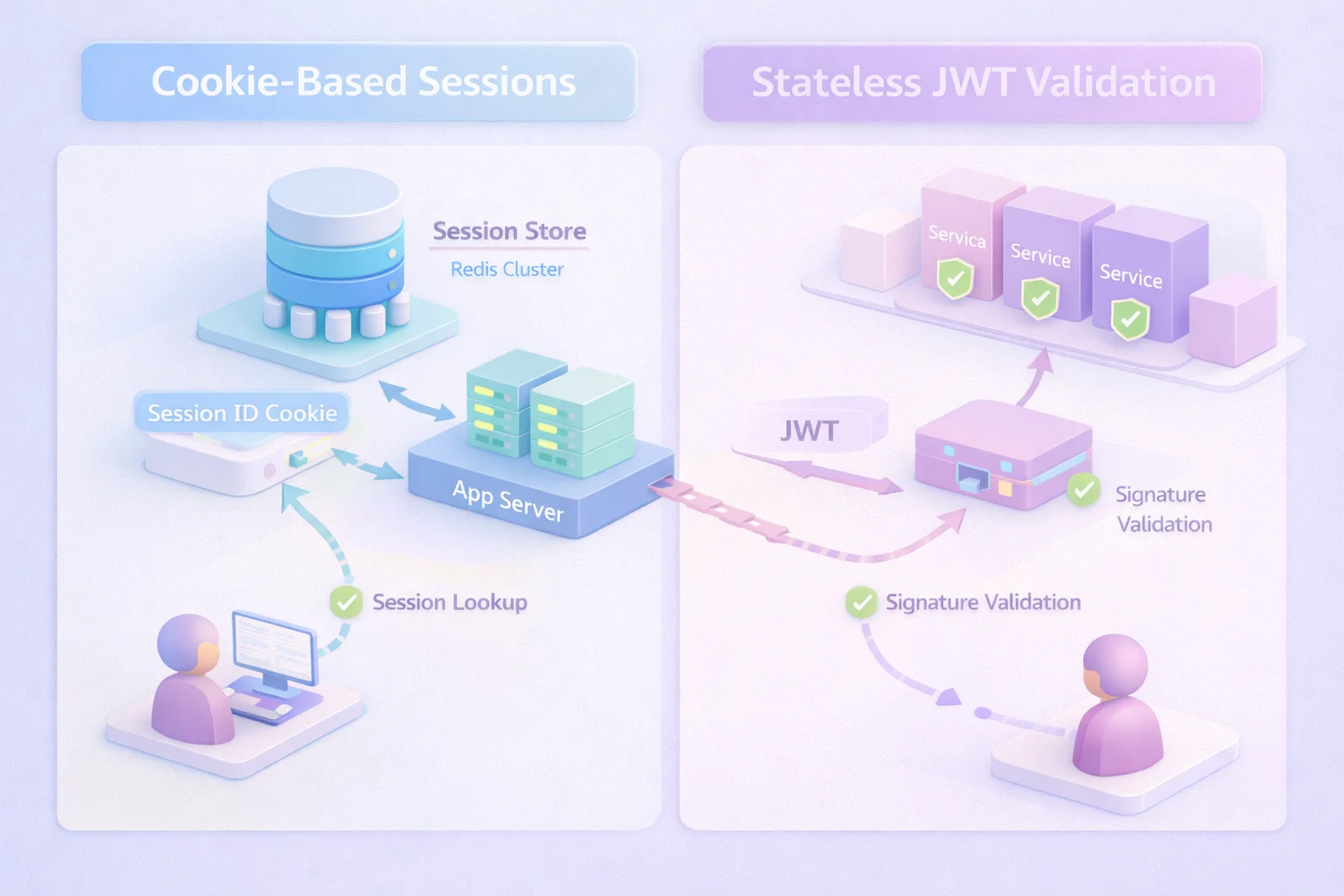
Session-based authentication feels intuitive. A user logs in, the server creates a session, stores it, and sends a session ID (usually in a cookie). Every request checks back with the server to validate that session. It’s centralized, controlled, and easy to reason about.
But as systems scale across load balancers, regions, and microservices, that centralized state becomes harder to manage. Session stores need to replicate, stay consistent, and respond quickly. Even basic flows like logout or session invalidation can become unreliable if the infrastructure isn’t designed for it.
On the other hand, JWT-based authentication built on standards like JSON Web Token (JWT) removes that server-side dependency. Instead of checking a session store, each request carries a signed token that can be validated independently. This makes JWTs a natural fit for APIs, mobile apps, and distributed architectures.
But that flexibility comes with trade-offs. Token expiration, refresh strategies, key rotation, and revocation are no longer simple backend concerns; they become system-wide responsibilities. When something goes wrong, it’s often harder to detect, isolate, and fix.
This is why discussions around token security often miss the point. It’s not about whether JWTs are more secure than sessions or whether sessions are outdated. It’s about how each model fails at scale. Sessions typically break due to infrastructure bottlenecks. JWTs tend to break as lifecycle and governance challenges. Both are valid. Both are common. And most teams encounter both just at different stages of growth.
If you’re evaluating which approach to use, the real question isn’t “Which one is better?” It’s:
Which authentication model will hold up when your system faces real traffic, real complexity, and real security pressure?
That’s what this guide answers clearly, practically, and without hype.
The two mental models teams rely on and why they start leaking under pressure
At the center of the JWT vs. session debate are two mental shortcuts most engineers carry around, often without realizing it.
Sessions are “stateful.” JWTs are “stateless.” That framing is convenient. It’s also incomplete.
With session-based authentication, the server remembers. After login, the system creates a server-side state and ties it to a session token the client sends back on every request. Authorization decisions depend on something the server already knows. If the server forgets or can’t reach what it remembers, the request fails.
With JWT-based authentication, the client carries proof. The server doesn’t need to look anything up; it verifies a signature, checks claims, and moves on. That’s why JWTs are often marketed as stateless, scalable, and cloud-native. No shared memory. No session store. Just math.
Although both models sound clean in isolation, real systems rarely stay that pure.
Here’s where it gets interesting. The moment you add logout, token revocation, device tracking, anomaly detection, or account risk controls, JWT stops being fully stateless.
Something somewhere needs to remember something. On the other side, the moment you distribute sessions across regions or push them behind caches and CDNs, sessions stop feeling simple and centralized.
So the real distinction isn’t stateful versus stateless. It’s where state lives and how much you depend on it.
Sessions centralize state by design. That makes enforcement, invalidation, and auditing straightforward but it also ties availability and performance to shared infrastructure. JWT shifts state outward.
That reduces synchronous dependencies, but pushes responsibility onto token lifecycles, validation discipline, and key management. When those drift, problems don’t show up immediately. They show up at scale.
This is why arguments framed as “JWT replaces sessions” or “sessions are outdated” miss the point. Most modern architectures quietly blend both models. Short-lived JWT access tokens backed by server-side controls. Session concepts layered on top of token flows. Hybrid systems that work well until assumptions collide.
Before asking which approach is better, it helps to understand this: neither model fails because it’s wrong. They fail because teams trust the mental shortcut longer than they should.
And that’s usually when production reminds everyone that authentication isn’t just about logging users in. It’s about what your system can survive when everything else starts to stretch.
Session-based authentication: what’s really happening under the hood
On the surface, session-based authentication feels refreshingly straightforward. A user logs in. The server validates credentials. A session is created. From that point on, the user doesn’t need to prove who they are again; every request just carries a reference to that session. Clean. Predictable. Easy to explain to new engineers.
But what’s actually happening is more nuanced.
When a session is created, the system generates a session token often an opaque identifier with no embedded meaning. That token is usually stored in a cookie and sent back with every request. The server uses it as a lookup key to fetch session data: user ID, roles, permissions, expiry time, maybe even device or IP context. Authorization decisions depend entirely on that lookup succeeding.
This design has a few quiet advantages that teams underestimate. Sessions are easy to revoke. Logging out is definitive. Kill the session record, and access stops immediately. From a security and compliance standpoint, that central control is comforting. You can answer questions like who is logged in right now or which sessions were active during an incident without guesswork.
The tradeoff shows up as soon as systems scale.
Sessions introduce a hard dependency on shared state. That state has to live somewhere memory, a database, a distributed cache and it has to be reachable on every authenticated request. As traffic grows, that lookup becomes part of your critical path. Latency spikes, cache evictions, replication lag, or a misconfigured failover can suddenly turn authentication into the bottleneck nobody expected.
This is where teams start adding band-aids. Sticky sessions to keep users pinned to one server. Aggressive caching to reduce lookups. Multi-region replication to stay close to users. Each fix helps, but each one also chips away at the simplicity that made sessions appealing in the first place.
The important thing to understand isn’t that sessions don’t scale they absolutely can. It’s that they scale as infrastructure. Their failure mode is operational. When something goes wrong, it’s usually loud, immediate, and visible. Requests slow down. Logins fail. Dashboards light up.
That visibility is both a weakness and a strength. You know when sessions are struggling. You just have to be ready for the moment your authentication system starts behaving like a distributed system because that’s exactly what it has become.
JWT-based authentication: how it actually works once theory meets production
JWT authentication often enters the conversation as the antidote to session sprawl. No shared state. No session store. No infrastructure bottleneck. Just a signed token that proves identity on every request. For teams moving toward APIs, microservices, or mobile clients, jwt based authentication sounds like the obvious upgrade.
And in many ways, it is.
With JWT token authentication, the server issues a token after login that contains claims about the user who they are, who issued the token, who it’s meant for, and when it expires. That token is signed using a secret or a private key. Every downstream service can verify the signature and make an authorization decision without calling back to a central store.
Here’s how it actually works in practice. The client sends the token with each request, usually as a bearer token in an Authorization header. The service checks the signature, validates critical claims like issuer and audience, confirms the token hasn’t expired, and proceeds. No lookup. No shared memory. Just verification.
That statelessness is powerful. It removes synchronous dependencies and plays well with horizontal scaling. Services can be added or removed without worrying about session affinity. Tokens work across regions, behind CDNs, and between independently deployed systems. For API-driven architectures, this flexibility is hard to ignore.
But this is also where the cracks start to form.
Although JWTs remove session lookups, they introduce lifecycle complexity. Tokens live for a fixed duration. If they live too long, revocation becomes nearly impossible. If they live too short, refresh logic becomes fragile and user experience suffers. Suddenly, authentication jwt isn’t just about signing and verifying it’s about expiration strategy, refresh token rotation, and key management.
There’s also an assumption hiding in plain sight: every service validates tokens the same way. In reality, inconsistencies creep in. One service checks audience claims strictly. Another doesn’t. One updates keys promptly. Another lags. At scale, these differences matter.
JWTs don’t usually fail loudly. They fail quietly. Access keeps working when it shouldn’t. Revoked users stay authenticated. Old tokens linger in logs, caches, or client storage. By the time the issue is visible, it’s already widespread.
That’s the tradeoff JWT brings. You gain architectural freedom, but you also take on the responsibility of discipline. Without tight controls around issuance, rotation, and validation, jwt authentication doesn’t break because of load—it breaks because of trust assumptions that no longer hold.
A practical JWT authentication example
Most explanations of JWT authentication example flows are too clean. They show a login, a token, and a happily authenticated request, and then stop right where real systems start getting interesting.
Here’s how it usually works in production.
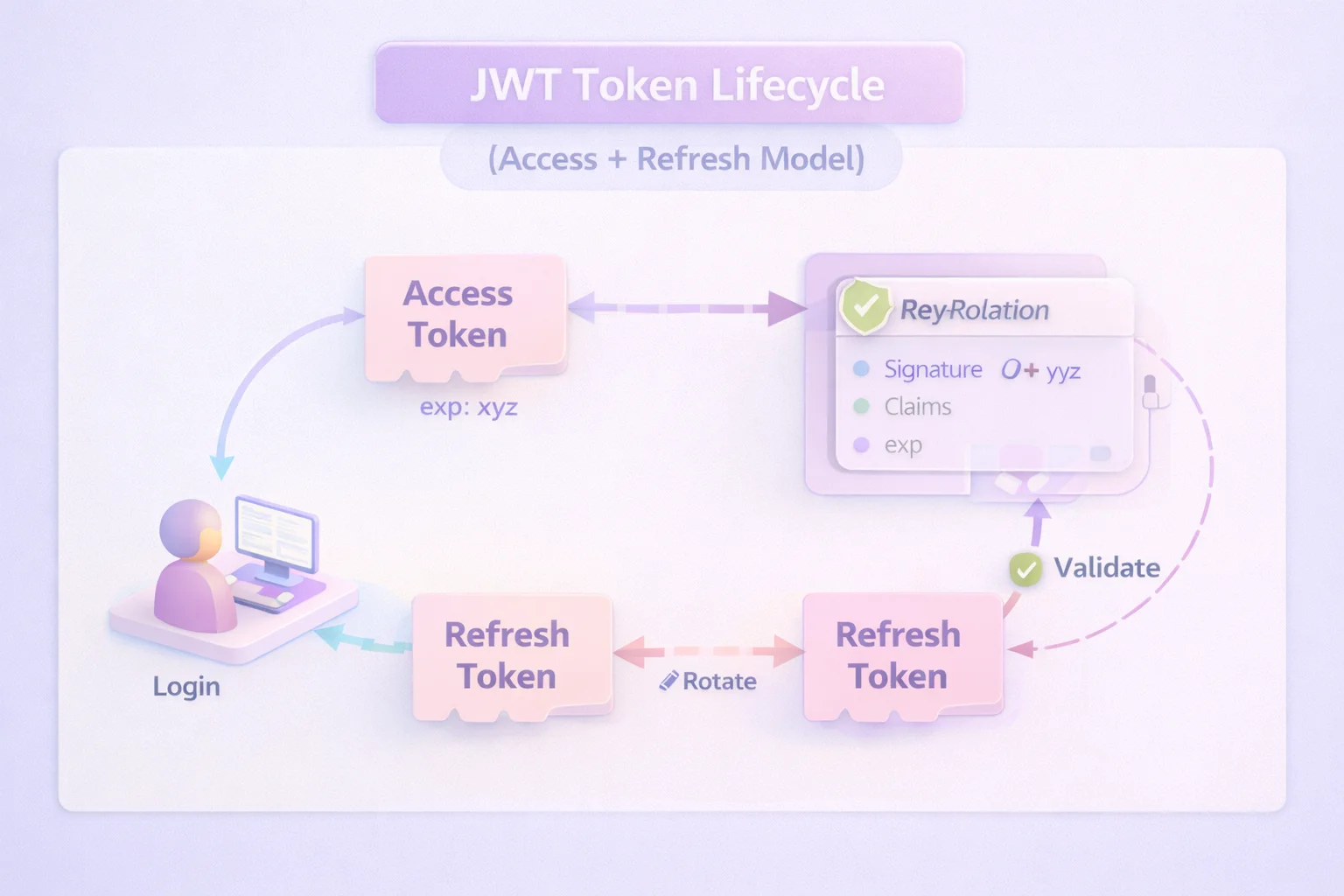
A user logs in. After credentials are verified, the system issues two things: a short-lived access token and a longer-lived refresh token. The access token is a JWT. It carries identity and authorization context and is used on every API request. The refresh token exists for one reason only to get a new access token without forcing the user to log in again.
When the client calls an API, it presents the JWT. The service verifies the signature, checks expiration, confirms issuer and audience, and allows the request. No database lookup. No session fetch. This is where jwt token authentication feels fast and elegant.
Then time passes.
The access token expires usually in minutes, not hours. The client uses the refresh token to request a new JWT. If refresh rotation is implemented correctly, the old refresh token becomes invalid and a new one is issued. If it’s not, attackers get a much larger window than intended. This is where many JWT implementations quietly weaken.
Logout exposes the biggest difference. With sessions, logout is definitive. With JWTs, logout is mostly advisory unless you’ve built revocation checks, token blacklists, or short expiry windows. Otherwise, a valid token remains valid until it expires, regardless of user intent.
This is the part many teams underestimate. JWT authentication works best when tokens are treated as short-lived, tightly governed credentials not long-term identity badges. The example only holds up if rotation, expiry, and validation are enforced consistently across every service that consumes the token.
When teams say “JWT doesn’t work for us,” it’s rarely because the mechanism failed. It’s because the example they implemented stopped one step short of reality—and scale exposed the gap immediately.
Which one breaks first at scale? The failure patterns teams actually hit
This is the moment where the jwt vs session debate stops being philosophical and starts becoming painfully specific. Neither model collapses overnight. They erode. And they erode in very different ways.
When session-based authentication starts to crack
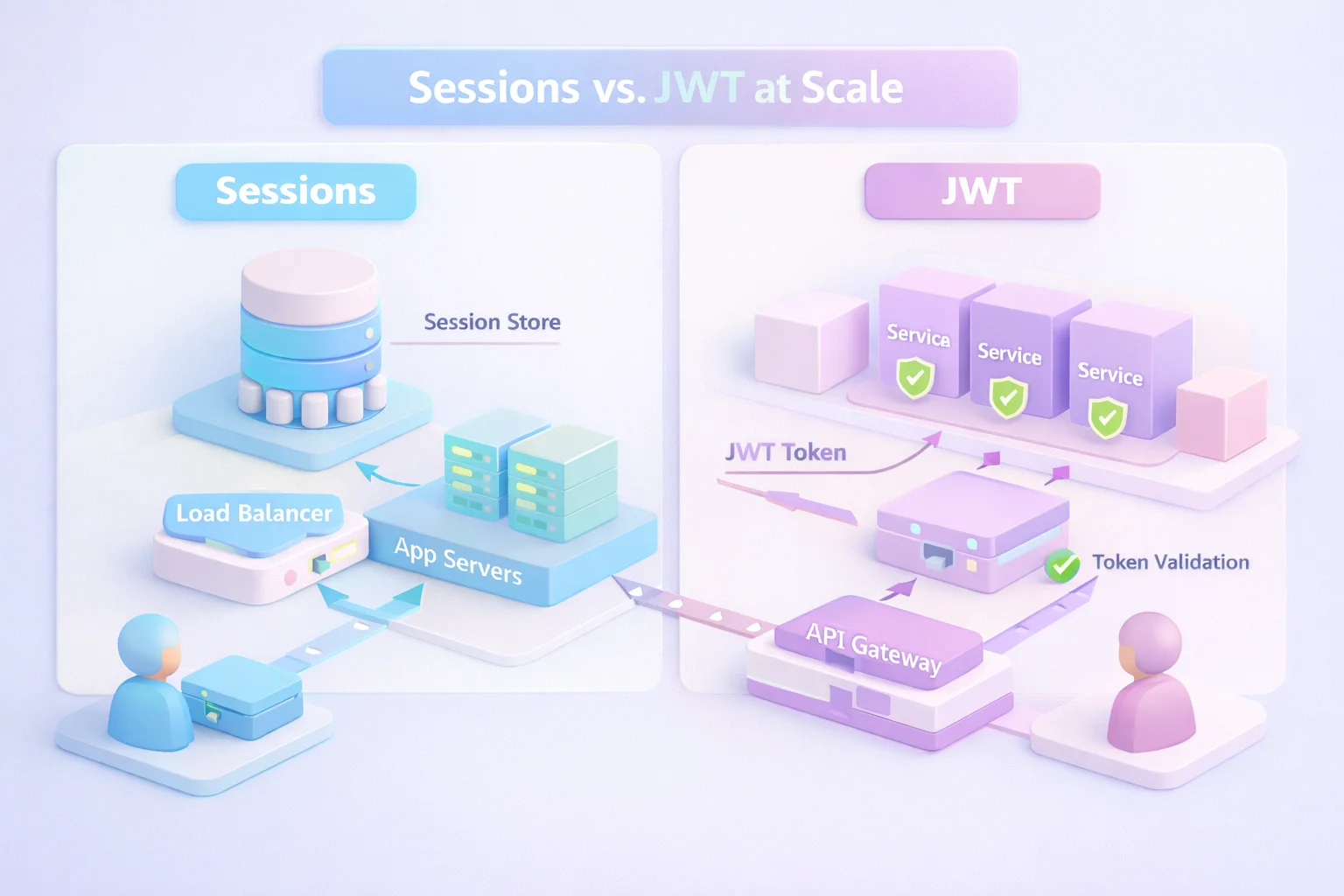
With session based authentication, the breaking point usually shows up as an infrastructure problem. Every authenticated request depends on a shared system remembering something. At small scale, that memory is cheap and fast. At large scale, it becomes a dependency you feel immediately.
Latency creeps in as session lookups stack up under load. Distributed session stores become hot spots. Failovers introduce inconsistency. In multi-region setups, replication lag turns “logged out” into “mostly logged out.” To compensate, teams add sticky sessions or aggressive caching and quietly trade resilience for stability.
The failure is obvious. Requests slow down. Users get kicked out. Dashboards light up. Incidents are noisy, but they’re also easier to trace. You can point to the session store and say, this is where things hurt.
When JWT-based authentication starts to crack
JWT rarely breaks because of traffic. JWT authentication breaks because of assumptions.
Tokens live longer than intended. Refresh rotation isn’t enforced everywhere. One service validates tokens strictly, another takes shortcuts. Keys don’t rotate cleanly. Revocation logic exists on paper but not in practice. The system keeps functioning until it shouldn’t.
These failures are quieter. A revoked user still has access. A compromised token works across services. Logs don’t clearly show why access was granted, only that it was. By the time the issue surfaces, it’s often spread across environments and teams.
This is why asking “which breaks first?” has an uncomfortable answer.
Sessions tend to break loudly and early as infrastructure scales. JWT tends to break silently and later as governance slips. One fails fast. The other fails deep.
Understanding that difference matters more than picking sides. Because when scale arrives and it always does you don’t get to choose whether something breaks. You only get to choose how visible the failure will be when it does.
Security reality check: what token security actually means in the real world
When teams ask what is token security, they’re often expecting a neat answer. Strong crypto. Signed tokens. Secure cookies. Problem solved. But security rarely fails because the primitives are weak. It fails because systems behave differently under pressure than they did on the whiteboard.
With sessions, security risk clusters around control of the session token. If that token is stolen, an attacker inherits the session. That’s why protections like httpOnly cookies, Secure flags, and SameSite settings matter so much. It’s also why session fixation and CSRF are still relevant threats. The upside is clarity: if you kill the session, access ends. Immediately.
JWT shifts the risk surface.
A JWT is usually a bearer token. Possession equals access. If it leaks through logs, browser storage, intercepted requests, or misconfigured clients, it can be replayed until it expires. That’s not a cryptographic failure. It’s a lifecycle failure. The math holds. The assumptions don’t.
This is where JWT token authentication exposes its sharp edges. Long-lived tokens increase blast radius. Short-lived tokens reduce it but only if refresh flows are tightly controlled. Miss one validation check. Skip one rotation rule. Store one token in the wrong place. At scale, those small gaps compound.
The uncomfortable truth is this: neither sessions nor JWTs are “more secure” by default. Sessions concentrate risk in infrastructure. JWT concentrates risk in governance. One relies on central control. The other relies on discipline everywhere.
Most real-world breaches don’t come from choosing the wrong model. They come from forgetting that authentication systems don’t just grant access they create artifacts that live, travel, and linger. If you don’t design for how those artifacts behave under stress, the security story looks solid right up until it doesn’t.
Debugging, incidents, and audits: where the pain actually shows up
When authentication fails in production, the real question isn’t what model you chose. It’s how quickly you can understand what just happened. This is where the operational differences between sessions vs JWT become impossible to ignore.
With sessions, debugging tends to be more direct. There’s a place to look. A session store. A record that says this user was active at this time, from this device, with these permissions. If something looks wrong, you can invalidate sessions in bulk, force re-authentication, and regain control fast.
From an incident-response perspective, that centralization is comforting. Auditors like it too. You can answer questions without stitching together half a dozen logs.
JWT flips that experience.
With JWT authentication, there’s no single source of truth once the token is issued. Access decisions are distributed across services, environments, and sometimes regions. When something goes wrong, the question becomes harder: Why was this token accepted here but rejected there? Was it claim validation? Clock skew? Key rotation? A stale JWKS cache? The answer usually lives across logs, not inside one system.
This is where teams start feeling the cost of loose discipline. If services validate tokens differently, debugging turns into archaeology. If revocation logic isn’t consistent, auditors ask uncomfortable questions about access after termination. If logs don’t capture token claims or decision context, post-incident reviews stall.
Sessions make failures visible and traceable. JWT makes systems flexible but demands better observability. Neither is free.
At scale, authentication isn’t just about allowing access. It’s about explaining access. If your system can’t clearly show why something was allowed or denied, every incident lasts longer than it should and every audit feels harder than it needs to be.
That’s often the moment teams realize the real cost of their choice wasn’t performance or scalability. It was operational clarity.
Choosing the right approach
This is usually the point where teams want a definitive answer. Sessions or JWT? Pick one. Move on. Unfortunately, that’s not how real systems behave and pretending otherwise is how architectures paint themselves into corners.
Here’s how it actually plays out.
Session-based authentication works best when control matters more than flexibility. Web applications with clear login and logout semantics. Systems where access needs to stop now, not “when the token expires.”
Environments with strict compliance, audit requirements, or centralized incident response. Sessions shine when you want visibility and authority in one place, even if that means carrying infrastructure weight.
JWT-based authentication earns its place when distribution is the priority. APIs are consumed by multiple services. Mobile apps that can’t afford frequent reauthentication. Systems that span regions, clouds, or partners. JWT reduces coupling and latency, and it scales naturally as long as token lifecycles are short, validation is strict, and rotation is non-negotiable.
Here’s where most mature platforms land, even if they don’t say it out loud: a hybrid model. Short-lived JWT access tokens for performance and scale, backed by server-side controls for revocation, risk checks, and logout. Not because it’s fashionable but because pure models don’t survive contact with real users, real threats, and real outages.
So the better question isn’t which model should we use? It’s where do we want failures to surface?
Sessions concentrate on failure in infrastructure. JWT concentrates on failure in governance. Both are manageable. Both are dangerous if ignored. The right choice is the one your team can explain, enforce, and debug when everything else is on fire.
If you can’t clearly answer how access is revoked, how tokens expire, and how decisions are logged, the model isn’t wrong, but the implementation probably is.
The “don’t regret it later” checklist teams wish they had upfront
This is the part most architects skip. Not because it’s hard, but because everything works fine at the beginning. The regret only shows up months later, when scale, security reviews, or incidents force uncomfortable rewrites.
If you’re using session-based authentication, a few things need to be true early, not eventually. Session tokens must live in secure, httpOnly cookies. SameSite and Secure flags shouldn’t be optional. Your session store needs a clear scaling and failover plan before traffic demands it. And logout must actually mean logout across regions, not “eventually consistent.”
If you’re using JWT authentication, discipline matters more than design diagrams. Access tokens should be short-lived by default. Refresh tokens must rotate, not linger. Key rotation needs to be automated and tested, not documented and forgotten. Every service must validate the same claims the same way, issuer, audience, and expiration, without exception.
For both models, some rules apply no matter what. Rate limiting protects authentication endpoints from becoming attack amplifiers. Logs must capture why access was granted, not just that it was. Token storage decisions, browser, mobile, and server deserve as much scrutiny as cryptography choices. This is where most what is token security conversations quietly fall apart.
None of this is glamorous. None of it shows up in demos. But these details decide whether your authentication system bends under scale or snaps in ways that take weeks to untangle.
If a checklist like this feels tedious, that’s usually a sign you’re still early. Once you’re operating at scale, it stops feeling optional and starts feeling overdue.
Final takeaway: it’s not about which one is better, it’s about how you fail
The JWT vs. session debate sticks around because both models work right up until they don’t. And when they stop working, the damage rarely comes from the mechanism itself. It comes from the assumptions teams carried forward without revisiting them as systems grew.
Sessions tend to fail as infrastructure. Latency, availability, replication, and state management eventually demand more than most teams planned for. The upside is visibility. When sessions struggle, everyone knows. The system slows down. Errors spike. You’re forced to respond.
JWT fails differently. JWT authentication keeps moving even when it shouldn’t. Tokens remain valid longer than intended. Revocation is incomplete. Validation drifts across services. The system appears healthy while access quietly exceeds intent. By the time the issue is discovered, it’s already woven into production behavior.
Neither failure mode is inherently worse. But they require different kinds of readiness.
If your team values immediate control, centralized enforcement, and clear audit trails, sessions remain a strong foundation. If your system demands flexibility across services, regions, and clients, JWT is hard to avoid but only if token lifecycles are treated as first-class infrastructure, not an afterthought.
The real mistake isn’t choosing sessions or JWT. It’s assuming the choice ends the conversation.
If you can’t clearly explain how access is granted, how it’s revoked, and how decisions are traced under stress, scale will force that explanation on you at the worst possible time.
And that’s usually when teams learn that authentication doesn’t break because it’s old or modern. It breaks because it wasn’t designed for the way the system actually grew.
FAQs
Q: Is JWT more scalable than session-based authentication?
A: JWT scales more easily across services and regions because it avoids server-side lookups, but it shifts complexity to token lifecycle management. Sessions can scale too, but they scale as infrastructure and require careful state management.
Q: Can JWT authentication support secure logout?
A: Yes, but only with short-lived access tokens, refresh token rotation, or revocation checks. Without these controls, logout in JWT is delayed until the token naturally expires.
Q: Are session tokens more secure than JWTs?
A: Neither is inherently more secure. Session tokens centralize risk in infrastructure, while JWTs distribute risk across token storage, validation, and governance. Security depends on how each is implemented, not the model itself.
Q: Should modern applications use both sessions and JWTs?
A: Many high-scale systems do. A hybrid approach—JWT access tokens backed by server-side controls balances performance, revocation, and operational clarity better than using either model alone.



