Introduction
In the modern digital landscape, the moment a customer interacts with your brand, a clock starts ticking. Every second spent navigating a clunky login screen, resetting a password, or re-entering profile details across different brand properties pushes them closer to abandonment. You already know this. Most directors and authentication leaders live this pain every day.
Here’s the part many teams still underestimate: authentication does not carry the experience.
Authentication answers “Who are you?” once. The customer journey needs something else to stay consistent across apps, portals, and channels.
That “something else” is your authorization service, the layer that determines where a user can go, what they can access, and how smoothly they can move between your digital properties without getting forced into repeat identity moments.
And when that authorization service sits on shaky foundations, multiple logins, fragmented profiles, disconnected apps every new product launch creates another identity island.
Customers feel it immediately. They stop trying. Your CX teams see bounce rates. Your support teams see tickets. Your growth teams see stalled conversion.
LoginRadius built its CIAM Authorization Service to solve this exact “single login access predicament.”
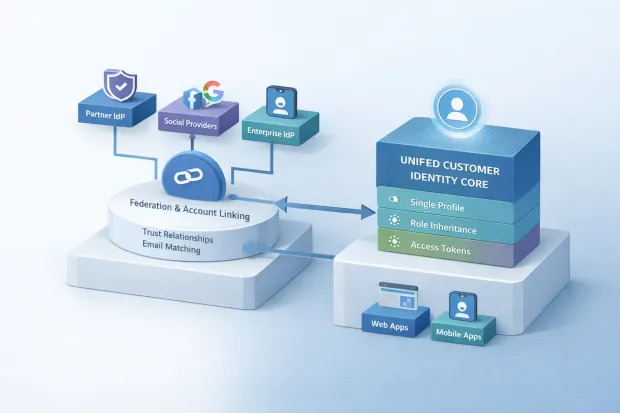
It gives organizations a unified way to enable seamless access across multiple web properties and mobile apps using Single Sign-On and federation, with additional capabilities like role-based authorization, account linking, and social network access to strengthen the customer profile and extend engagement.
That’s not a list of features. That’s the operating system for modern customer access.
The Single Login Access Predicament in Digital Businesses
Most businesses did not plan to create a messy login ecosystem. It happened through growth.
A new web property launched for a new market. A mobile app shipped for loyalty. A separate portal appeared for a partner program. A customer community spun up. Each team picked its own registration and login approach because it felt faster in the moment.
Now you run multiple registration/login touchpoints across multiple web and mobile properties. Customers see your brand as one company, but your identity layer forces them to behave like strangers each time. That fragmented user experience translates into the outcomes nobody wants: lower engagement, weaker retention, and reduced conversion.
This problem looks deceptively small when you view it from the inside. “It’s just a login.” From the outside, it feels like friction and repetition. Customers stop trusting the experience.
And it doesn’t stay isolated to UX.
-
Your customer data spreads across systems.
-
Your teams lose a unified profile view.
-
Your personalization efforts hit a ceiling because identity does not connect across properties.
-
Your access strategy becomes reactive instead of designed.
The most telling signal? You keep shipping “new experiences” while the login journey keeps getting worse.
This is where a strong authorization service changes the game. It does not just authenticate. It reduces friction at every point where customers interact with your brand. That’s the part that compounds.
What a CIAM Authorization Service Actually Does
Let me make this simple.
-
Authentication proves a user’s identity.
-
Authorization governs what happens after the identity becomes known.
Directors and top authentication and authorization experts already understand this conceptually. The problem starts in real systems because teams treat authorization like an afterthought. They bolt it onto each application separately. They copy-paste role checks. They create inconsistent token rules. They rebuild the same logic again and again.
A modern CIAM Authorization Service needs to do something more structured:
-
Connect multiple web and mobile properties so customers can use one identity across them.
-
Propagate identity and profile data so every app sees the same customer.
-
Enforce access decisions through roles when you want controlled experiences (gamification, tiered access, loyalty).
-
Enable federation so users can leverage partner-issued identities without creating yet another account.
-
Support account linking and social permissions so the customer profile becomes richer, not more fragmented.
LoginRadius frames this as an Authorization Service with five distinct features designed to streamline customer access and align with specific user flows.

Single Sign-On as the Backbone of Customer Authorization
If you strip everything down, Single Sign-On sits at the center of this system.
LoginRadius positions Single Sign-On as the backbone of the service, connecting multiple web and mobile properties under one SSO grouping and allowing users to create one identity that works across assets.
This matters because SSO does not just reduce password prompts. It unlocks a consistent identity footprint across the ecosystem.
What SSO enables in this model
1. One identity across multiple properties
Customers register once (in coordination with the Registration Service) and then use the same identity across all apps.
2. Customer profile propagation across all assets
LoginRadius propagates the same identity and associated customer profile to all web and mobile apps under the SSO grouping. That means customer context moves with the customer.
3. Real-time profile synchronization
Any changes made to the customer profile on one property reflect across all properties. That is how you stop your profile data from splitting into competing “versions of truth.”
And yes this directly supports the single customer view outcome
How LoginRadius deploys SSO in real deployments
The PDF spells out practical deployment characteristics that directors care about:
-
SSO for web and mobile apps under one grouping, with API access through the JavaScript SSO SDK.
-
Deploy SSO alongside Standard Login and Social Login without disrupting either.
-
LoginRadius acts as the Identity Provider (IdP) and the client app acts as the Service Provider (SP).
-
Support for widely used standards: SAML, JSON Web Tokens (JWT), and Multipass.
-
Support for Single Logout, plus both IdP-initiated and SP-initiated login process flows.
-
Support for custom attributes and the ability to customize the JWT response.
-
Direct Multipass support for platforms like Desk.com and Shopify.
That combination matters because it gives you architectural flexibility. You can keep your existing login patterns. You can unify them under one access experience.
If your teams search “sso single sign on” because they want cross-application continuity, this is the underlying outcome they actually want: one identity, one experience, many properties
Role-Based Authorization That Scales With Customer Journeys
After SSO stabilizes identity across properties, the next question becomes unavoidable:
What should each customer be allowed to do?
That’s where role-based authorization becomes a practical control layer. LoginRadius supports creating a role-based access system by assigning roles to each customer, which the PDF calls particularly helpful for companies using a gamification model.
Gamification represents one common use case, but the idea extends further. Role-based access enables structured customer experiences:
-
You gate premium content.
-
You create loyalty tiers.
-
You limit early access features.
-
You enforce “member-only” experiences across apps.
And here’s where many systems fail: they implement roles per app. One app tags the user as “Gold.” Another app uses “Premium.” Your support staff starts patching exceptions. Your reporting becomes unreliable. Your customers get inconsistent experiences.
LoginRadius avoids that by supporting roles alongside SSO so roles carry across assets with the identity.
Admin control without scripting sprawl
This part hits home for directors managing scale: LoginRadius enables creating workflows directly from the dashboard without scripting. Teams can assign roles directly to individual customers when needed.
When you pair that with role hierarchy support and the ability to create, edit, and assign multiple roles to a single customer, you get an authorization strategy that keeps control centralized.
That’s how role-based authorization stays manageable as your product portfolio expands.
Federation: Letting Trusted Partner Identities In Securely
Now let’s talk about federation, because this is where ecosystems win.
Many organizations do not operate as isolated digital worlds anymore. You run partner ecosystems. You share customers. You integrate with platforms where users already hold identities. You want frictionless access while maintaining control.
Federation solves that by allowing users to leverage identities issued by trusted partners. LoginRadius provides federation capabilities so companies can accept partner-issued identities and deliver a better customer experience.
This matters for directors because the federation removes redundant registration. It allows customers to start the journey immediately using an identity they already trust.
Standards and protocol support that actually fits enterprise reality
LoginRadius supports federation and SSO with popular standards such as:
-
SAML
-
Multipass
The sub-component list expands federation protocol support even further:
-
SAML 1.1 and 2.0
-
JSON Web Tokens
-
Multipass
-
Support for any Identity Provider that conforms to OAuth 2.0 protocol standards
This stack matters because enterprise environments rarely run on one protocol. You need compatibility. You need a federation approach that slots into partner relationships without rewriting the world.
LoginRadius also supports deploying Single Sign-On for internal applications, which adds flexibility for hybrid environments.
So if your architecture includes customer apps plus internal portals, federation and SSO support becomes more than customer convenience. It becomes ecosystem coherence.
From Fragmented Profiles to a Single Customer View
Now we hit the outcome executives and directors keep asking for: the single customer view.
The PDF calls it directly: propagate a single identity across all properties to get the Single Customer View.
So, what is a single customer view in this context?
It is a unified customer profile across all assets, web and mobile properties included, where identity and profile updates sync across the ecosystem. It means the customer does not turn into five versions of themselves depending on where they interact.
If your identity layer stays fragmented, you cannot build that view. You can’t even fake it reliably, because every system keeps its own customer representation.
LoginRadius addresses this by propagating the identity and associated customer profile across all properties under the SSO grouping and reflecting profile changes everywhere.
Why a single customer view changes outcomes
This goes beyond personalization. Directors look at this through risk, operational efficiency, and growth.
-
Experience consistency: the customer gets recognized across touchpoints.
-
Data integrity: fewer duplicates, fewer conflicting fields, fewer “who owns the truth?” battles.
-
Operational efficiency: teams stop wasting time reconciling identity records.
-
Engagement lift: customers complete journeys when they don’t hit identity walls.
And when you extend that with account linking, the single customer view becomes richer.
Account Linking: Connecting Social Identities to One Profile
Account linking looks like a “nice-to-have” until you see what happens without it.
Without account linking, customers create multiple accounts with different providers. One day they log in with Google. Another day with Facebook. Then they try Standard Login. Your system treats them like three different people. That wrecks analytics, personalization, and support.
LoginRadius supports linking multiple social accounts to one customer profile to extract more social data points, while also pushing data the other way after obtaining necessary permissions.
The account linking sub-component details are very explicit:
-
Customer-initiated linking and unlinking of multiple social accounts to one customer profile.
-
Support for social account linking when the customer profile was created using Standard Login.
-
Auto-link social accounts with common email addresses.
-
Prioritize profile data extracted from any of the linked social accounts.
That “auto-link with common email” detail matters. It prevents duplicate identity creation at scale. It reduces “ghost accounts.” It improves the consistency of the customer profile—the foundation of the single customer view.
This also aligns with directors’ priorities around data quality. Clean identity data drives clean downstream decisions.
Download the PDF to reference the account linking capabilities list, including auto-linking via common email and profile data prioritization.
Key Business Benefits of the LoginRadius Authorization Service
Directors don’t buy a feature list. They buy outcomes.
The PDF states the benefits clearly, and they map directly to what authentication and authorization leaders measure:
1. Improve customer experience and reduce bounce rates
LoginRadius improves customer experience by enabling low friction access to multiple apps with one identity. That reduces bounce rates because customers stop hitting repeated login walls.
2. Propagate a single identity to get the Single Customer View
A single identity across properties creates the single customer view, making customer profiles consistent across assets.
3. Improve loyalty and engagement with role-based hierarchical authorization
Role based authorization drives loyalty and engagement through hierarchical access. This supports gamification models and tiered experiences.
4. Increase social reach and engagement
LoginRadius enables increased social reach and engagement on social networks, supported by account linking and social network access components.
Those benefits don’t require you to invent a new experience strategy. They strengthen what you already try to do retention, loyalty, conversions by removing identity friction.
Punch-line: Better access control creates better business results.
Why Enterprises Trust LoginRadius for CIAM Authorization
Enterprise trust comes from two things: deployment reality and proven scale.
The data sheet positions LoginRadius as a leading provider of cloud-based Customer Identity and Access Management solutions for mid-to-large sized companies, serving over 3,000 businesses with a monthly reach of over 1 billion users worldwide.
That scale matters because authorization and SSO break in production when systems can’t handle real traffic and real complexity.
The Authorization Service itself includes sub-components designed for enterprise deployment patterns:
-
SSO deployment alongside Standard Login and Social Login without disruption.
-
Standards support: SAML, JWT, Multipass.
-
Support for custom attributes and JWT customization.
-
Support for IdP/SP initiated login flows and Single Logout.
-
Federation support across SAML 1.1/2.0, JWT, Multipass, and OAuth 2.0-conformant IdPs.
That combination reflects an enterprise-ready authorization service built to fit modern identity standards.
When Should You Evaluate a Dedicated Authorization Service?
Some signals show up early. Others hit after a painful incident. Either way, teams reach the same conclusion: “We need a real authorization service.”
You should evaluate a dedicated authorization service like LoginRadius when:
-
You run multiple web properties and mobile apps and customers jump between them. (Your apps need single sign on that actually works across the ecosystem.)
-
Your customer experience suffers from multiple login touchpoints and identity fragmentation.
-
You need role based authorization to support tiered access, loyalty models, or gamification at scale.
-
You need federation capabilities to accept partner-issued identities and remove re-registration friction.
-
Your organization wants a single customer view, but identity and profile data stays trapped inside each application.
-
You want to support account linking so customers can connect multiple social identities to one profile and you stop managing duplicates.
This isn’t about chasing a trend. It’s about building a foundation that allows your digital ecosystem to behave like one coherent product.
Conclusion
Most organizations obsess over login because login creates the first impression.
But the real customer experience lives after that first step.
Customers don’t measure identity success by whether authentication works once. They measure it by whether the journey stays smooth across every web property, every mobile app, and every interaction that happens next. They notice when they feel recognized. They notice when they don’t.
That’s why an authorization service matters so much.
LoginRadius designed its CIAM Authorization Service to tackle the single login access predicament with a unified, standards-based approach:
-
Single sign on connects your ecosystem under one identity and propagates profiles across properties.
-
Role based authorization enables hierarchical access control that supports loyalty and engagement models without turning authorization into a code jungle.
-
Federation allows customers to leverage partner-issued identities using widely adopted protocols, including SAML, JWT, Multipass, and OAuth 2.0-conformant Identity Providers.
-
Account linking connects multiple social accounts to a single customer profile, supports auto-linking via common email, and improves customer data consistency.
This combination creates the outcome leaders keep pushing for: the single customer view one unified profile, consistent across assets, synced across experiences.
If you run multiple digital properties, authorization becomes the difference between a connected customer journey and a fragmented identity mess.
And if you want your organization to lead with experience, you need authorization designed as a system not patched as an afterthought.
Download the LoginRadius CIAM Authorization Service Data Sheet.
Get the complete breakdown of Single Sign-On, federation protocols, role hierarchy support, account linking capabilities, and social network access organized for architecture and stakeholder reviews.
FAQs
Q: What is an authorization service in CIAM?
A: An authorization service controls what an authenticated customer can access across your apps pages, features, and resources—based on defined rules like roles and trust relationships. It keeps access consistent as users move across properties.
Q: How does Single Sign-On support a single customer view?
A: Single sign on propagates one identity and customer profile across all web and mobile properties in the SSO grouping. Profile updates sync across assets, which enables a single customer view.
Q: What does role based authorization mean for customer-facing apps?
A: Role based authorization assigns roles to customers so you can control access hierarchically like tiered loyalty access or gamification experiences. LoginRadius supports creating and managing roles from the dashboard and carrying roles across assets via SSO.
Q: What is federation and when should you use it?
A: Federation lets customers sign in using identities issued by trusted partner Identity Providers, reducing registration friction. LoginRadius supports federation with standards like SAML, JWT, Multipass, and OAuth 2.0 conformant IdPs.




