Introduction
Most teams don’t start by debating RBAC vs ABAC. They arrive there after something breaks. A user sees data they shouldn’t. An auditor asks a question no one can answer cleanly. Or a product scales just enough that permissions stop behaving the way everyone assumed they would.
That’s when access control stops being theoretical.
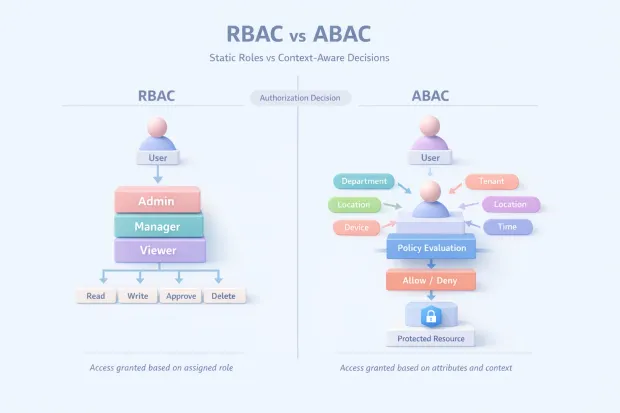
On paper, the choice looks simple: role-based access control vs attribute-based access control. One uses roles. The other uses attributes. In reality, the decision shapes how secure, flexible, and explainable your system becomes over time.
And that’s where the confusion begins, especially when terms like RBAC authentication or what is RBAC in security get mixed into conversations where authorization is the real issue.
RBAC feels familiar. It mirrors how organizations think job titles, responsibilities, teams. The RBAC model works well when access lines are stable and predictable. ABAC, on the other hand, reflects how modern systems actually behave.
Access depends on context: who the user is, what resource they’re touching, where they’re coming from, and under what conditions. That’s why attribute-based access control vs role based access control is not just a technical comparison it’s a design decision.
Here’s where it gets interesting. Beginners usually want clarity: Which one should I use? Experts want control: How do I avoid role explosion, policy sprawl, or audit chaos? This guide is written for both.
No textbook definitions. No oversimplified “one is better” claims. Just a clear breakdown of RBAC and ABAC, how they actually behave in production systems, where each one shines, and where teams usually misjudge them.
If you’re designing access for a SaaS product, an enterprise platform, or anything that has grown beyond a single user type, this isn’t an abstract debate. It’s a decision that quietly determines whether your access layer stays manageable or becomes the thing everyone is afraid to touch.
What Is RBAC in Security
When people ask what RBAC is in security, they usually expect a clean definition. In practice, RBAC is less about theory and more about how organizations choose to simplify access decisions.
Role-Based Access Control works by grouping permissions into roles and assigning users to those roles. Instead of deciding access one permission at a time, systems decide based on membership.
If you’re an Admin, you get admin permissions. If you’re a Viewer, you don’t. That’s the core idea behind the RBAC model, and it’s why RBAC still remains widely used across enterprise systems and SaaS platforms.
Where RBAC shines is consistency. It reflects how businesses already think about responsibility. Job functions, team boundaries, and operational duties map cleanly to roles.
This makes RBAC easy to reason about, easy to audit, and easy to explain especially during compliance reviews. When someone asks why a user has access, the answer is usually straightforward: because of their role.
But RBAC in practice is not just about assigning roles and walking away. The real work is deciding how many roles exist, how stable those roles are, and how much variation they’re allowed to absorb. This is where RBAC often starts to stretch.
As products evolve, exceptions creep in. Temporary access becomes permanent. Roles multiply to handle edge cases. What started as a clean system slowly turns into something fragile.
Another important clarification: RBAC is not authentication. Despite how often the term rbac authentication appears in search queries, RBAC does not verify identity; it governs authorization. It answers what this user can do after they’re logged in, not who they are. Confusing the two leads to poorly designed access layers and misplaced security controls.
Used intentionally, RBAC creates order. Used without guardrails, it becomes a permission dumping ground. The difference lies in how closely roles align with real responsibility and how often they’re reviewed.
Attribute-Based Access Control (ABAC): When Context Decides Access
Attribute-Based Access Control enters the picture when roles stop being enough.
ABAC shifts the access decision away from static role membership and toward attributes properties associated with the user, the resource, the action, and the environment. Instead of asking “What role does this user have?”, ABAC asks “Under these conditions, should this action be allowed?”
This is where attribute-based access control vs role based access control becomes a meaningful distinction. ABAC handles nuance. It allows access decisions to adapt based on context: tenant ownership, data sensitivity, time of access, device posture, geographic location, or even real-time risk signals.
In systems where access depends on what is being accessed and under what circumstances, ABAC feels natural.
In practice, ABAC reduces the need for endless roles. Instead of creating separate roles for every variation, attributes and policies express rules dynamically. This is especially valuable in multi-tenant SaaS platforms, data-heavy environments, and systems where permissions depend on metadata rather than job titles.
But ABAC is not inherently simpler. The complexity doesn’t disappear, it moves. Attributes need sources of truth. Policies need structure. And decisions need transparency. Without discipline, ABAC can become difficult to debug.
When access is denied, someone eventually asks “why?” If the answer involves tracing multiple attributes across systems, teams quickly realize that flexibility comes at a cost.
ABAC works best when attributes are reliable, consistently populated, and governed as carefully as roles once were. When that foundation exists, ABAC enables fine-grained access without bloated role hierarchies. When it doesn’t, access control becomes unpredictable.
RBAC vs ABAC: The Real Differences That Matter
The RBAC vs ABAC debate often gets framed as old versus new, or simple versus advanced. That framing misses the point.
The real difference lies in how access decisions are expressed and enforced.
RBAC answers access questions through structure. Roles act as a proxy for trust. If the system trusts the role, it trusts the user. This makes RBAC fast, understandable, and stable ideal for environments where access patterns don’t change frequently and responsibilities are well defined.
ABAC answers access questions through evaluation. Each request is checked against a set of conditions. Trust becomes contextual rather than assumed. This allows for precision and adaptability, especially in systems where access depends on data attributes or environmental factors.
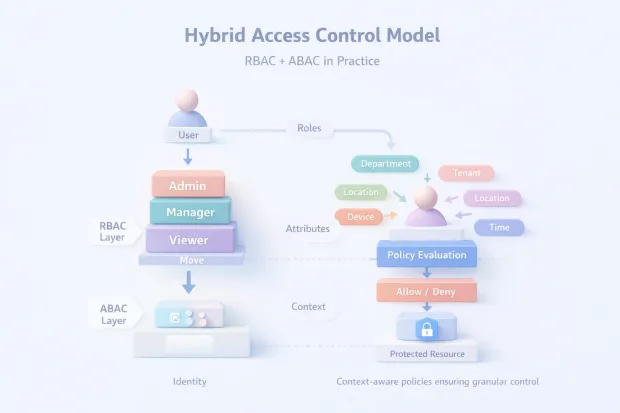
From an operational perspective, RBAC fails when variation increases. ABAC fails when governance weakens. One struggles with scale through rigidity, the other through sprawl. That’s why most real-world systems don’t choose one exclusively. They combine them.
In a hybrid approach, RBAC establishes baseline access to who belongs where in the system. ABAC refines that access under what conditions those permissions apply. This combination avoids role explosion while keeping policies anchored to understandable roles.
So when evaluating rbac and abac, the better question isn’t which one is superior. It’s which model matches the shape of your access decisions. If your system relies on stable roles, RBAC will feel intuitive. If it relies on context, ABAC becomes essential. And if it relies on both as most modern platforms do, the smartest design is knowing where one should end and the other should begin.
That’s where access control stops being theoretical and starts holding up under real pressure.
Role-Based Access Control Example
A good role-based access control example shouldn’t feel theoretical. It should feel like something you’ve already seen or maybe inherited.
Imagine a SaaS analytics platform. Users log in and immediately fall into one of a few familiar roles: Admin, Manager, Analyst, Viewer. Each role comes with a predictable set of permissions. Admins manage users and settings. Managers create reports and export data. Analysts run queries and dashboards. Viewers can only see what’s been published to them.
This works because the access model mirrors how teams already operate. Responsibility flows downward. Trust is implied by role assignment. No one needs to think too hard about why an Analyst can run queries but can’t manage users, it's obvious.
This is the strength of RBAC in practice. Access decisions feel intuitive. Admins can explain permissions without opening documentation. Auditors can trace access paths without decoding policies. For a large portion of systems, this model handles day-to-day access cleanly.
Where it starts to crack is not in the core roles but in the exceptions. The moment you need “Analyst, but only for this tenant,” or “Manager, but no exports,” or “Temporary Admin for two days,” RBAC begins to stretch. Teams either over-permission users or create more roles to patch the gap. That’s usually the first sign that RBAC alone is carrying more weight than it was designed for.
Pros and Cons of RBAC
RBAC’s biggest advantage is clarity.
It simplifies authorization by grouping permissions into roles that humans can understand. That simplicity makes RBAC fast to implement, easy to audit, and relatively low-risk in stable environments. It’s also why RBAC remains a default choice when teams first ask what RBAC is in security because it aligns well with compliance expectations and organizational thinking.
RBAC also reduces decision fatigue. Once roles are defined, access decisions become mechanical. Assign the role, inherit the permissions. No runtime evaluation. No attribute juggling. This predictability matters in large organizations where access reviews and approvals need to move quickly.
The downside appears over time. RBAC struggles with nuance. It doesn’t handle context well. Every exception becomes a structural problem. Temporary access, resource-specific permissions, tenant boundaries all push teams toward either role explosion or silent over-permissioning.
Another hidden cost is drift. Roles tend to accumulate permissions long after the original intent fades. Without regular cleanup, RBAC systems slowly grant more access than anyone realizes. At that point, the model still looks clean on paper, but the reality underneath is far less controlled.
RBAC works best when roles stay stable. When they don’t, the cracks show fast.
Pros and Cons of ABAC
ABAC exists to handle everything RBAC finds awkward.
Its strength lies in precision. Instead of granting access based on a label, ABAC evaluates attributes and context at the time of the request. Who is the user? What resources are they trying to access? What environmental conditions apply right now? This allows for fine-grained access control without inventing new roles for every variation.
ABAC scales better in systems where access depends on metadata rather than hierarchy. Multi-tenant platforms, data-driven applications, and environments with strict data segmentation benefit most. Policies can express intent directly, rather than encoding it indirectly through role names.
But ABAC is not inherently safer just because it’s more flexible. Its biggest risk is complexity. Attributes need to be accurate. Policies need to be readable. Debugging access decisions requires visibility into why a rule evaluated the way it did. Without strong governance, ABAC can feel unpredictable even when it’s technically correct.
There’s also a human factor. RBAC is easy to explain. ABAC requires better tooling, better logging, and better discipline. When teams underestimate that operational overhead, ABAC becomes difficult to maintain.
ABAC excels when systems demand precision. It fails when teams treat flexibility as a substitute for structure.
RBAC and ABAC Together: How Real Systems Actually Work
Most real systems don’t live entirely in one model. They layer.
RBAC establishes the baseline. It answers the broad question: What kind of user is this? Roles define the outer boundaries of access and keep the system understandable. This is where onboarding, admin assignment, and high-level authorization decisions happen.
ABAC refines that access. It answers the harder question: Under what conditions should this permission apply? Attributes narrow scope without redefining identity. A user may have permission in theory, but attributes determine whether that permission applies right now, to this resource, in this context.
This hybrid approach avoids the worst failure modes of both models. Roles don’t explode. Policies don’t float without anchors. Access decisions remain explainable without becoming rigid.
In practice, this is how modern access control survives scale. RBAC provides stability. ABAC provides control. Together, they reflect how real products grow incrementally, unevenly, and with constant edge cases.
Where Teams Usually Go Wrong
The biggest mistake teams make isn’t choosing the “wrong” model. It’s choosing a model without understanding what problem it’s solving.
Some teams force RBAC to handle context it was never meant to manage. They keep adding roles until no one remembers why half of them exist. Others jump into ABAC without treating attributes as first-class citizens. Policies pile up. Debugging becomes guesswork. Access reviews lose meaning.
Another common failure is skipping governance entirely. No role ownership. No attribute validation. No policy testing. Access control becomes something no one wants to touch because touching it feels risky.
Finally, teams often delay these decisions until access incidents force the issue. By then, the system has already grown around assumptions that are hard to undo.
Access control works best when it’s designed to reflect how decisions are actually made not how teams wish they were made. Get that alignment right early, and both RBAC and ABAC stay manageable. Get it wrong, and even the most sophisticated model becomes a liability.
Conclusion
The real takeaway from the abac vs rbac discussion isn’t that one model replaces the other. It’s that each solves a different kind of access problem and most mature systems eventually need both.
RBAC works when access can be expressed cleanly through roles. It’s easy to understand, easy to audit, and easy to explain to humans. That’s why it’s still widely used and why a solid role-based access control example often feels reassuringly simple. But simplicity has limits.
As soon as access decisions depend on data sensitivity, tenant boundaries, device trust, or time-based rules, roles alone start bending in uncomfortable ways.
ABAC steps in where RBAC strains. It gives you precision. It lets attributes and context decide access instead of forcing every exception into a new role. But that power comes with responsibility. Without disciplined attribute management and clear policies, ABAC can become opaque, fast hard to debug, harder to explain, and frustrating to govern.
This is why most real-world architectures don’t choose sides. They layer. RBAC defines who you are in the system. ABAC defines when and how that access applies. Together, they reduce over-permissioning without turning access control into an unsolvable puzzle.
If you’re early in your journey, start with RBAC but design it knowing where it will break. If you’re scaling, ABAC isn’t an upgrade; it’s a necessity for fine-grained authorization. And if you’re already struggling with either, the fix usually isn’t a new model, it's clarity around what decisions roles should make, and what decisions attributes should handle.
Access control doesn’t fail because teams choose the wrong acronym. It fails when the model doesn’t match how the product actually works. Get that alignment right, and both RBAC and ABAC become tools not obstacles in building secure, scalable systems. Book a Demo today with experts.
FAQs
Q: Is ABAC more secure than RBAC?
A: ABAC isn’t automatically more secure. It allows finer control by evaluating context and attributes, but without strong governance it can become harder to manage. Security comes from correct implementation, not the model itself.
Q: Can RBAC and ABAC be used together?
A: Yes, and most modern systems do exactly that. RBAC defines baseline access through roles, while ABAC applies conditions and context to refine those permissions at runtime.
Q: Why does RBAC fail at scale?
A: RBAC struggles when access depends on context or resource-level rules. As exceptions grow, teams create more roles, leading to role explosion and over-permissioning.
Q: When should a team move from RBAC to ABAC?
A: When roles no longer capture access accurately and permissions depend on attributes like tenant, data sensitivity, or environment. That’s usually a sign RBAC alone has reached its limit.



