Introduction
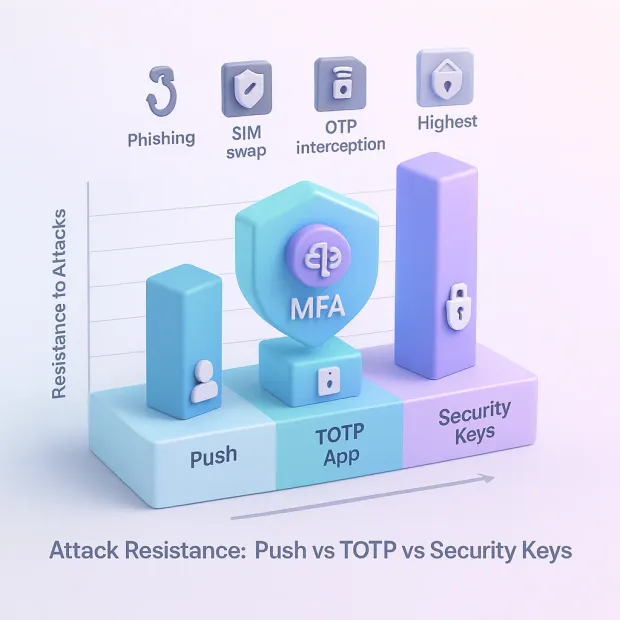
The MFA landscape has changed dramatically. Methods that once felt “secure enough” like TOTP apps or push notifications are now being pressured by increasingly sophisticated attacks such as real-time phishing (AITM), OTP interception, session hijacking, and push fatigue.
At the same time, user expectations have shifted. People want stronger security, but not at the expense of convenience, performance, or privacy.
Amid this evolution, one question has become impossible to ignore: Which MFA method is truly the strongest Security Keys, TOTP, or Push?
As teams evaluate MFA today, they’re also weighing newer passwordless options, which is why comparisons like passkey vs 2fa and passkey vs security key keep coming up. Push authentication often sits in the middle: smoother than OTP-based flows and easier to roll out than hardware-first deployments, but only as strong as the safeguards behind it.
Understanding the answer isn’t just a technical exercise. It directly impacts:
-
How safe your users are
-
How much friction they face during login
-
How effectively you can reduce account takeovers
-
How quickly you can scale authentication for millions of users
-
How well your product aligns with Zero Trust and phishing-resistant standards
Each method, whether it’s TOTP authentication, push authentication, or security key authentication, brings its own blend of usability, risk, cost, and real-world resilience. And while they all improve security compared to passwords alone, they’re not equally strong.
In this blog, we’ll break down the strengths and weaknesses of each MFA method, compare their resistance to phishing and AITM attacks, evaluate usability and friction levels, and help you understand why some methods are considered weak 2FA factors while others qualify as phishing-resistant MFA under the latest security standards.
The Three MFA Methods Compared
Before diving into strengths, weaknesses, and real-world attack resistance, it’s helpful to understand what each MFA method actually is and why they behave so differently under threat.
Here’s a simple, high-level breakdown of Security Keys, TOTP, and Push Authentication, along with how they stack up at first glance.
1. Security Keys (FIDO2 / WebAuthn)
Security keys are physical hardware devices like YubiKeys that use public-key cryptography to authenticate users. They bind authentication to the device and domain, making them extremely hard to phish or intercept.
Why they matter:
-
They are considered the strongest MFA method available today.
-
They are fully phishing-resistant and immune to AITM attacks.
-
They enable passwordless authentication and Zero Trust alignment.
Also read : The Role of Passwordless Authentication in Securing Digital Identity
2. TOTP Authentication (Authenticator Apps)
TOTP (Time-Based One-Time Password) MFA uses an authenticator app such as Google Authenticator or Authy that generates a 6-digit code every 30 seconds. It’s one of the most widely adopted 2FA methods.
If you’re wondering what is totp authentication, it’s a time-based OTP method where the server and authenticator app generate the same rotating code using a shared secret and the current time. Understanding how does totp work matters because attackers can still steal or relay the code in real-time phishing scenarios.
Why it matters:
-
Easy to deploy
-
Familiar to users
-
Better than SMS OTP
-
Not phishing-resistant (attackers can trick users into sharing OTPs)
3. Push Authentication
Push MFA sends an approval request to a user’s enrolled mobile device. Users tap “Approve” to sign in. Modern push MFA may also support number matching or device binding for added security.
Why it matters:
-
Very user-friendly
-
Great for mobile-first apps
-
Vulnerable to push fatigue attacks if not implemented carefully
-
Moderate phishing resistance, depending on the implementation

At-a-Glance Comparison Table
| MFA Method | Security Strength | Phishing Resistance | User Friction | Cost | Best Use Case |
|---|---|---|---|---|---|
| Security Keys | Very High | Very High | Low | Medium | High-security apps, Zero Trust, CIAM |
| Push MFA | High | Excellent | Very Low | Medium | Consumer apps, mobile-first onboarding |
| TOTP | Excellent | Moderate | Medium | Low | General-purpose MFA, fallback methods |
Understanding TOTP: How Time-Based One-Time Passwords Work
To restate it clearly for readers: what is totp authentication is essentially a rotating, time-synced code system, commonly called totp authentication, used as a second factor in many MFA deployments.
TOTP (Time-Based One-Time Password) is one of the most widely used MFA methods in modern applications. It’s simple, familiar, and easy for users to adopt, but its security strength is often misunderstood. To evaluate whether TOTP stands up against modern attacks, we need to understand how it works and where it falls short.
What TOTP Is & How It Works
TOTP authentication uses a mobile app like Google Authenticator, Authy, or Microsoft Authenticator to generate a 6-digit code that refreshes every 30 seconds.
How it works:
-
When a user enrolls, the app and server share a secret seed.
-
Both use the current timestamp to generate matching OTP codes.
-
The user enters the code during login to verify their identity.
This makes TOTP more secure than SMS OTP, because the code is generated locally on the device rather than sent over a network.
Strengths of TOTP MFA
Despite its weaknesses, TOTP offers several advantages:
1. Works Offline:
The app does not require Internet or cellular connectivity.
2. Easy to Deploy:
Most applications support TOTP out of the box through standard MFA APIs.
3. Cost-Effective:
No SMS delivery costs or push infrastructure.
4. Familiar to Users:
Many users already understand how TOTP codes work.
5. More Secure Than SMS OTP:
Not vulnerable to SS7 attacks or SIM swap in the same way SMS-based codes are.
Learn more: Advantages of Time-Based One-Time Passwords (TOTP)
Weaknesses & Attack Vectors
This is where TOTP becomes problematic, especially for CIAM, enterprise-grade security, or modern Zero Trust models.
1. Not Phishing-Resistant:
Users can be tricked into entering their code on a fake login page.
2. Real-time phishing tools (AITM kits):
intercept OTPs instantly and replay them to the real service.
3. Vulnerable to Man-in-the-Middle (MITM) Attacks:
Attackers can capture OTP codes during malicious redirects or spoofed login flows.
4. OTP Interception & Malware Risks:
Malicious apps or malware can read OTP codes from compromised devices.
5. Shared Secret Exposure:
If the secret seed is exposed or backed up insecurely, attackers can generate valid codes indefinitely.
6. Brute-Force Attempts:
The short OTP length and time window can still be exploited through rapid guessing.
In today’s threat landscape, TOTP is no longer considered a strong authentication factor but it remains widely used due to its convenience and low cost.
Understanding Push Authentication: How Push MFA Works
Push authentication has rapidly grown in popularity because it provides a nearly frictionless login experience. Instead of typing codes, users simply tap “Approve” on their mobile devices. But while Push MFA improves usability, its security strength depends heavily on how it’s implemented and whether it includes modern protections like number matching or device binding.
What Push MFA Is & How It Works
Push authentication sends a secure notification to a user’s enrolled mobile device after they enter their username and password. The user taps Approve to complete authentication.
A push MFA flow typically includes:
-
User enters credentials
-
Server sends a push request to the user’s trusted device
-
The device shows an approval prompt
-
User taps Approve or Deny
-
Authentication completes
Some modern implementations add:
-
Number matching
-
Device-bound cryptographic checks
-
Geolocation or IP context
These additional layers significantly influence how secure push authentication actually is.
This is the core of push authentication: instead of typing OTPs, the user confirms identity by approving a secure prompt ideally enhanced with number matching or device-bound verification to reduce social engineering risk.
Strengths of Push Authentication
Push MFA has several strong advantages, especially for consumer-facing applications:
1. Extremely Low Friction:
Users only need to tap a button no codes, no typing.
2. Ideal for Mobile-First Apps:
Most users already have smartphones, making push easy to adopt.
3. Reduces Login Drop-Offs:
Its simplicity improves conversion rates and overall user experience.
4. Can Be Strengthened With Modern Enhancements:
Features like number matching and device binding make push MFA harder to socially engineer.
5. Faster Than TOTP:
Push avoids the extra step of manually entering a 6-digit code.
Weaknesses & Attack Vectors
Despite its convenience, push MFA has unique vulnerabilities that attackers exploit.
1. Push Fatigue Attacks:
Also called “MFA bombing.” Attackers repeatedly send push requests until the user clicks Approve out of frustration or confusion.
2. Social Engineering:
Attackers trick users into approving a push by pretending to be IT support or security teams.
3. Device Compromise:
A rooted or infected phone can approve push requests without the user noticing.
4. Notification Spoofing:
Malicious apps can generate confusing notifications to trick users.
5. Phishing via Real-Time Proxies:
If push MFA does not use device binding or number matching, attackers can initiate approval prompts after capturing the victim’s password.
Push MFA offers the best user experience, but not the strongest security unless paired with advanced protections like device-bound credentials, biometrics, or number-matching challenges.
Understanding Security Keys: Why They’re the Strongest MFA Method
For readers asking what is a security key, it’s a hardware authenticator that uses public-key cryptography (FIDO2/WebAuthn) to prove user presence and origin binding. This is also why the debate around passkey vs security key exists: both are phishing-resistant, but passkeys are often synced across devices while security keys remain physically held and controlled.
Security keys (FIDO2/WebAuthn hardware authenticators) represent the highest standard of modern authentication. They use cryptographic operations instead of shared secrets or user-entered codes, making them immune to phishing, replay attacks, and real-time AITM interception.
In a world where attackers exploit human error and bypass traditional MFA methods, security keys are the only truly phishing-resistant authentication factor.
What Security Keys Are & How They Work
Security keys are small hardware devices like YubiKey, Google Titan Key, or Feitian keys that authenticate users using public-key cryptography.
How they work:
-
During enrollment, the device creates a unique public/private key pair.
-
The public key is stored on the server; the private key stays on the device.
-
When the user logs in, the device signs a cryptographic challenge.
-
The signature only works for the legitimate domain (origin binding).
There are no codes to steal, no secrets to intercept, and nothing users can be tricked into typing.
Strengths of Security Keys
Security keys outperform TOTP and Push MFA across every security dimension.
1. Completely Phishing-Resistant:
Because the private key never leaves the device and only signs challenges from the correct domain, attackers cannot intercept or replay anything, even with AITM kits.
2. Immune to OTP Theft & Interception:
There is no shared secret or one-time code.
3. Resistant to Real-Time Phishing (AITM):
Security keys reject authentication attempts that do not originate from the correct website URL.
4. Fast, Frictionless Authentication:
Just tap or insert the key; no typing, no codes, no fatigue.
5. Works with Passkeys:
Security keys form the foundation for passwordless authentication, combining strong MFA with frictionless UX.
6. Device-Bound Cryptographic Keys:
Credentials are stored on the key itself, not in the cloud, removing entire categories of attack.
7. Perfect for Zero Trust:
Security keys enforce the strongest form of identity verification for high-risk actions, privileged users, and sensitive resources.
Weaknesses & Limitations
Even the strongest MFA method has some tradeoffs, though none impact its security.
1. Hardware Cost:
Keys range from $20–$70 each, depending on brand and features.
2. Physical Loss:
If a user loses the key, they require backup keys or alternate recovery methods.
3. Slightly Higher Initial Learning Curve:
Users must understand how to enroll and use their key (though UX is extremely simple once understood).
Security keys combine usability, speed, phishing resistance, and cryptographic strength, making them the strongest authentication method available today, and the recommended standard for modern CIAM and enterprise identity systems.
Final Phishing-Resistance Ranking
From weakest to strongest:
| MFA Method | Phishing Resistance | Real-World Security |
|---|---|---|
| SMS OTP | Very Low | Weak |
| TOTP App Codes | Low | Moderate |
| Push MFA | Medium | Strong with safeguards |
| Security Keys (FIDO2/WebAuthn) | Very High | Excellent |

Performance, Cost, and User Experience Comparison
Now that we’ve compared security strength, it’s equally important to understand how each MFA method impacts your application’s performance, operational cost, and UX, three areas that directly affect user adoption and conversion rates.
Cost Comparison: Deployment, Maintenance, and Scaling
Cost varies dramatically depending on delivery infrastructure and support complexity.
TOTP MFA
Cost: Low
-
No SMS costs
-
No push delivery infrastructure
-
Minimal backend complexity
Hidden Costs: Support tickets for lost devices or failed code syncs.
Push MFA
Cost: Medium
-
Requires push delivery infrastructure
-
OS restrictions may affect reliability (battery optimization, offline mode)
-
Support cost for push fatigue, device change, app reinstall
Hidden Costs: Higher support load compared to TOTP and hardware solutions.
Security Keys
Cost: Medium–High
-
Hardware keys cost $20–$70 per user
-
Organizations may need backup keys
-
Training and onboarding requirements
Hidden Costs: Key replacement; procurement at scale.
But long-term cost is significantly lower than recovering from phishing or ATO attacks — which is why financial institutions and enterprises choose FIDO2.
User Experience: Which MFA Method Do Users Prefer?
TOTP MFA
UX Level: Medium
-
Requires manual code entry
-
Easy to misunderstand or mistype
-
Leads to login fatigue over time
-
Higher abandonment rates on mobile apps
Push Authentication
UX Level: High
-
One-tap login
-
No codes or typing
-
Best for everyday consumer logins
-
Vulnerable to user confusion during MFA bombing
Security Keys
UX Level: Very High
-
Simple tap → login
-
No reading or typing
-
Works across mobile and desktop
-
Best UX once users are onboarded
Security keys consistently rank highest in UX surveys across Google, Microsoft, and NIST studies.
Comparison Table (Performance + Cost + UX)
| Factor | TOTP | Push Authentication | Security Keys (FIDO2/WebAuthn) |
|---|---|---|---|
| Performance | Medium | Fast | Very Fast |
| User Experience | Moderate | High | Very High |
| Phishing Resistance | Low | Medium | Very High |
| Cost to Deploy | Low | Medium | Medium–High |
| Maintenance Cost | Medium | Medium | Low |
| Scalability | High | Medium | Very High |
| Best For | Budget-conscious apps | Consumer apps | High-security, enterprise, CIAM |
Security Keys vs TOTP vs Push: Which Should You Use?
Choosing the strongest MFA method isn’t just about comparing security strengths — it’s about matching the right method to your users, your threat landscape, your compliance requirements, and your conversion goals.
There is no single “one-size-fits-all” solution. Instead, the best MFA strategy is tiered, combining usability with phishing-resistant authentication for the areas where it matters most.
Below is the definitive guidance used by modern SaaS companies, financial institutions, global enterprises, and consumer platforms.
1. When to Use TOTP MFA
TOTP is ideal for applications needing affordable MFA with moderate security needs.
Use TOTP if you are:
-
Running a cost-sensitive application
-
Securing low-risk user accounts
-
Supporting a global user base where SMS/push may not work reliably
-
Prioritizing ease of deployment over phishing resistance
Avoid relying solely on TOTP if:
-
Your app handles payments, transactions, healthcare data, or PII
-
Phishing is a major attack vector
-
Your user base is vulnerable to fraud or social engineering
TOTP is better than SMS but not strong enough for modern threats.
2. When to Use Push Authentication
Push is the sweet spot between security and usability. It’s ideal for consumer-facing apps where convenience is critical.
Use Push MFA if you are:
-
Running a mobile-first product
-
Trying to reduce login friction and improve session success rates
-
Supporting a young/general audience that prefers simple flows
-
Implementing adaptive MFA or contextual risk checks
-
Operating in sectors where experience matters (gaming, eCommerce, OTT, social apps)
Push is strong IF enhanced with:
-
Number matching
-
Biometric confirmation
-
Device binding
-
Contextual checks (IP, location, device fingerprint, user behavior)
Avoid relying solely on Push if:
-
Users are frequently targeted with MFA bombing
-
You do not support modern protections like number matching
-
Compliance mandates phishing-resistant MFA (government, healthcare, finance)
Push MFA is great for UX but vulnerable if users are easily tricked.
3. When to Use Security Keys (FIDO2/WebAuthn)
Security keys are the strongest authentication method and the only one immune to phishing, AITM, OTP theft, and fatigue attacks.
Use Security Keys if you are:
-
A financial services, fintech, or banking platform
-
A healthcare or government provider
-
A SaaS platform with enterprise and admin roles
-
Following Zero Trust or compliance frameworks (NIST, CISA, FedRAMP)
-
Handling high-risk actions: payouts, password changes, admin access, privilege elevation
-
Operating a large-scale CIAM environment where ATO and fraud are costly
Also ideal for:
-
Developer tools
-
B2B platforms
-
High-value corporate accounts
Security keys deliver the highest security + best UX of all factors.
The Ultimate Recommendation Based on Global Best Practices
For Consumer Applications
If your roadmap includes passwordless, evaluate passkey vs 2fa alongside push authentication. Many teams adopt passkeys for primary login, then keep push as a step-up factor for risky actions.
-
Push MFA (with number matching + biometrics)
-
Optional TOTP fallback
-
Avoid SMS as a primary factor
-
Add adaptive MFA for risky logins
For B2B SaaS & Workforce Access
-
Security Keys (mandatory for admins)
-
Push or Passkeys for general users
-
TOTP as an emergency fallback
-
Adaptive MFA for session re-checks
For High-Risk Industries (Finance, Healthcare, Government)
-
Security Keys as primary
-
Passkeys for frictionless strong authentication
-
Adaptive MFA is layered across all channels.
-
No SMS (too weak)
For Platforms Battling Fraud
-
Security keys + adaptive MFA
-
Device fingerprinting
-
Behavioral ML detection
-
Push fatigue protections
Which MFA Method Is the Strongest?
| Ranking | MFA Method | Strength Level |
|---|---|---|
| 1 | Security Keys (FIDO2/WebAuthn) | Strongest, phishing-resistant |
| 2 | Push MFA with Number Matching / Device Binding | Strong, high UX |
| 3 | TOTP App-Based Codes | Moderate security, good fallback |
Security keys are the strongest and the future of MFA. Push MFA offers the best balance of security and UX. TOTP is a good fallback, but not secure enough on its own.
Conclusion
The MFA landscape is changing faster than ever. Attackers now use real-time phishing kits, MFA fatigue attacks, session hijacking, and sophisticated MITM tools designed specifically to defeat outdated authentication methods. In this environment, your MFA strategy cannot rely on legacy OTPs or user-dependent security behaviors.
For any organization handling sensitive data, operating in regulated industries, or fighting credential attacks at scale, strong MFA is no longer optional; it is foundational.
This layered model balances security, usability, cost, and scalability and aligns perfectly with Zero Trust and modern CIAM standards.
Ready to Implement Strong, Phishing-Resistant MFA That Scales?
LoginRadius gives you everything you need in one CIAM platform. Whether you're securing millions of consumer accounts or protecting enterprise access, LoginRadius helps you deploy modern, phishing-resistant MFA at scale without compromising user experience. Explore Adaptive MFA. Book a Demo with Our Identity Experts
FAQs
Q: What is the most secure MFA method: Security Keys, TOTP, or Push?
A: Security keys (FIDO2/WebAuthn) are the most secure because they provide strong, phishing-resistant authentication and cannot be intercepted or replayed.
Q: Is TOTP authentication safe enough for modern applications?
A: TOTP is moderately secure, but still vulnerable to phishing, real-time AitM attacks, and malware. It works best as a fallback factor, not the primary one.
Q: Are push notifications more secure than TOTP codes?
A: Yes especially when combined with number matching. Push MFA reduces manual input and prevents most phishing attacks by confirming access within the device.
Q: Why are security keys considered the strongest MFA factor?
A: Security keys use hardware-bound cryptography and origin binding, making them immune to phishing, OTP theft, SIM swaps, and man-in-the-middle attacks.
Q: Which MFA method is best for SaaS platforms?
A: Security keys and passkeys are ideal for admin and high-risk users, push MFA is best for everyday customer logins, and TOTP serves as a secure fallback option.




