Introduction
Authentication rarely feels like a scaling problem until it suddenly is.
At the start, everything works. Users log in, sessions are created, requests are validated, and the system behaves exactly as expected. There’s no urgency to rethink anything. But as your application grows—more users, more APIs, mobile clients, multiple regions, and microservices—the cracks start to appear. What once felt simple begins to slow down, break under load, or demand workarounds that weren’t part of the original plan.
This is where the conversation shifts to session-based vs token-based authentication.
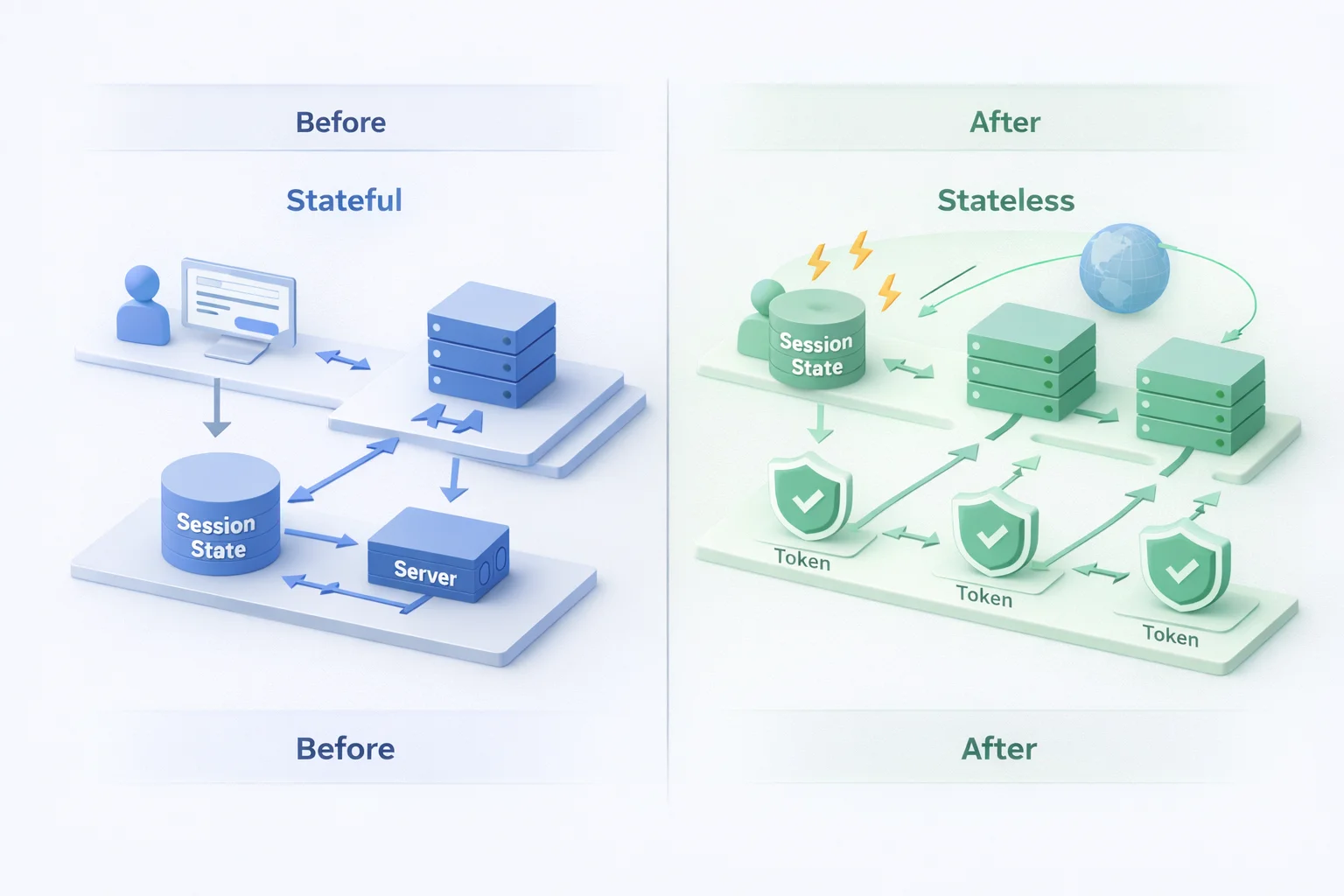
On the surface, both approaches solve the same problem: verifying identity and controlling access. But at scale, their differences become very real. Session-based authentication can introduce challenges like centralized state, session store bottlenecks, and cross-service complexity. Token-based authentication, often powered by standards like JWT, brings flexibility and statelessness—but also introduces its own considerations around token security, expiration, and revocation.
Here’s the key insight most teams discover a little late: authentication choices made early—often based on familiarity—directly impact performance, scalability, and security later. Sessions feel straightforward. Tokens feel modern. But neither is inherently “better” unless it aligns with how your system actually evolves.
So when someone asks, what is token-based authentication, they’re not just looking for a definition. They’re asking whether it can handle distributed systems, APIs, and global traffic without adding operational complexity. And when they revisit sessions, they’re really questioning how long a stateful approach can keep up in a system that’s no longer centralized.
This guide breaks it down clearly, no hype, no trend bias. Just a practical, engineering-first answer to the question that matters in production:
Which authentication model actually scales and why?
Session based authentication: how it actually works in production
Session based authentication is usually the first thing teams ship. Not because it’s trendy, but because it’s straightforward and it makes sense when you’re building a single application with a single backend.
A user logs in. The server validates credentials. A session token is created and stored server-side. The browser carries a reference to that session, usually as a cookie, and every request after that quietly says, “It’s still me.” From the application’s point of view, this feels controlled. Familiar. Safe.
That’s the theory.
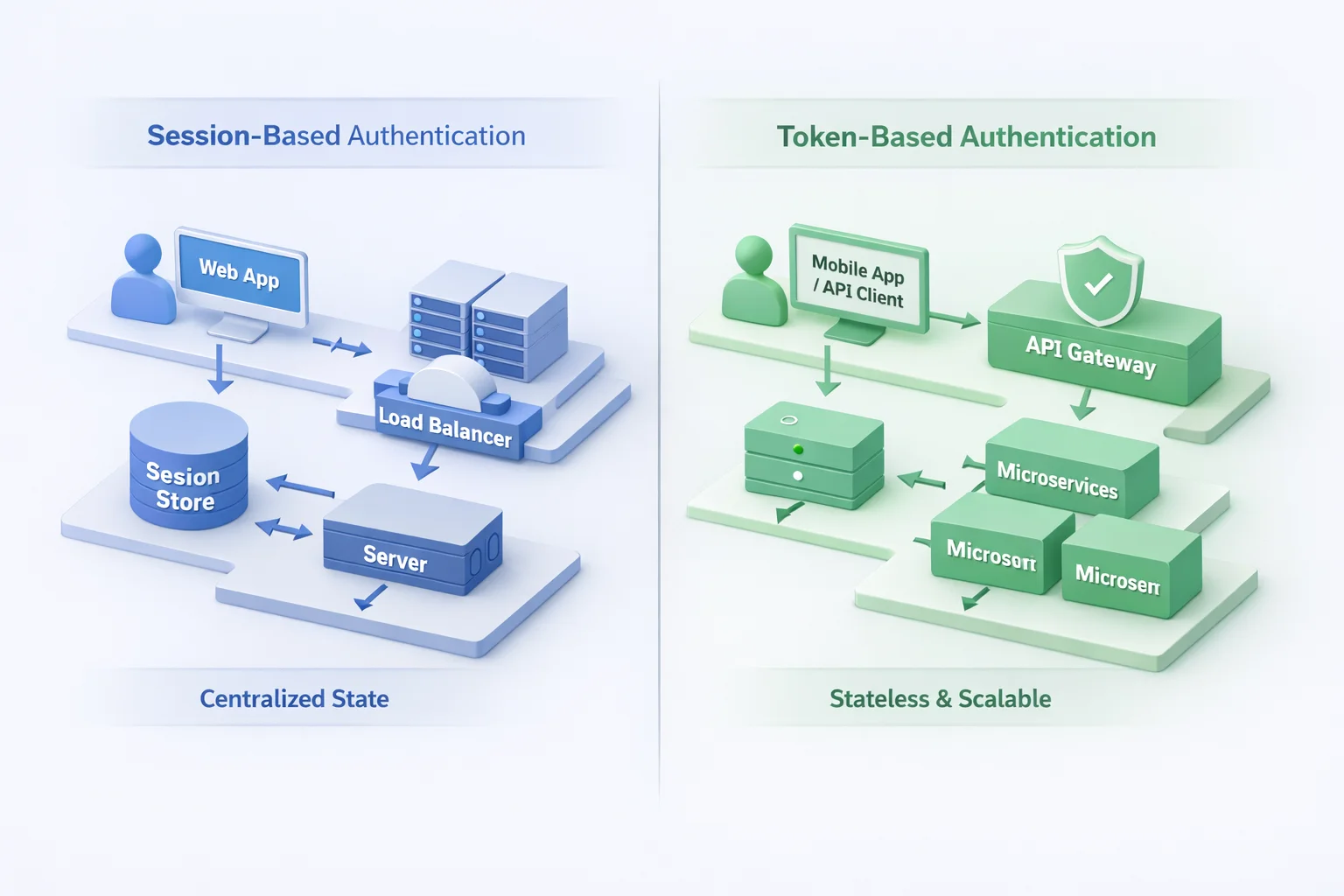
In production, session based authentication is really about state. Every active user creates state that has to live somewhere in memory, a database, Redis, or a dedicated session store. And every request depends on that state being reachable, consistent, and fast. As long as there’s one server, or a tightly coupled cluster, this holds up well.
The appeal is obvious. Server-side control is strong. You can invalidate sessions instantly. Logout actually means something. Security teams like that level of authority. Developers like how little guesswork is involved.
But here’s where teams usually go wrong: they underestimate how quickly session management becomes infrastructure.
The moment you add a load balancer, you’re forced to answer questions you didn’t have before. Sticky sessions or shared storage? What happens when a node restarts? How do session tokens behave across regions? Suddenly, authentication isn’t just a login flow; it’s a dependency that every request leans on.
And none of this is visible in local development. Session based authentication rarely fails loudly. It degrades quietly. A bit more latency here. A cache miss there. An occasional “why did this user get logged out?” that no one can reproduce.
This is why sessions work beautifully at the start and why they demand discipline as systems grow. Not because the model is flawed, but because the state always has a cost once scale enters the picture.
What is token-based authentication, and why systems behave differently when you use it
Token-based authentication starts from a very different assumption: the server doesn’t want to remember you.
Instead of holding session state, the system issues an authentication token after login and expects the client to present that token with every request. If the token checks out, access is granted. If it doesn’t, the request goes nowhere. No session lookup. No shared memory. No “do I still know this user?” moment on the backend.
That single shift changes a lot.
When people ask what is token based authentication, they often picture JWTs flying around in headers. That’s part of it, but it’s not the point. The point is statelessness. The server validates the token, not a stored session. The identity travels with the request instead of living on the server.
This is why token-based auth shows up so naturally in APIs, mobile apps, and microservices. Requests don’t care which server receives them. Load balancers don’t need sticky rules. Services don’t need shared session stores. As long as the token is valid, the system moves on.
It feels lighter. Faster. More flexible.
But here’s the catch most teams discover late: token based authentication shifts responsibility instead of removing it. Session logic doesn’t disappear; it moves into token design. Expiration rules matter. Rotation matters. Revocation suddenly becomes a decision instead of a built-in behavior.
And while sessions ask, “Is this user still active?”, tokens ask something more rigid: “Is this token still allowed to exist?”
That distinction is subtle, but it shows up quickly in real systems. Long-lived tokens feel convenient until one leaks. Short-lived tokens feel safer until refresh logic goes wrong. Stateless systems scale cleanly, but they demand discipline where sessions quietly enforced it for you.
So token authentication isn’t “better” by default. It’s different pressure in different places.
In contrast to sessions, token based authentication removes server-side memory and replaces it with lifecycle management. And whether that trade-off helps or hurts depends entirely on how your system grows next.
Token-based authentication vs sessions: what actually breaks first at scale
This is the point where diagrams stop helping and production traffic takes over.
Both models work beautifully when the load is predictable and the architecture is simple. The difference shows up the moment requests stop behaving politely.
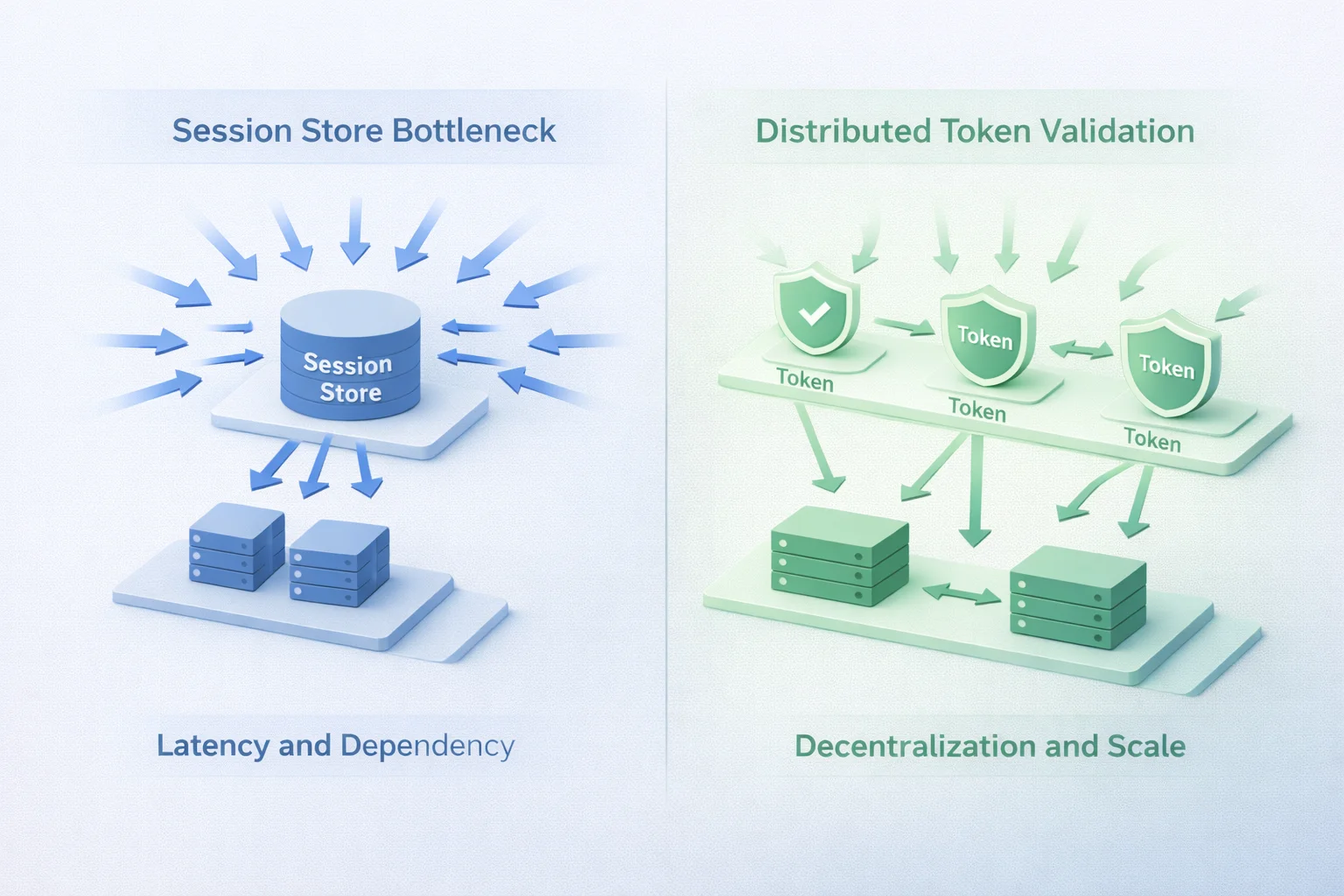
With session-based authentication, the first cracks usually appear in coordination. Sessions depend on shared state, and shared state doesn’t love being stretched. Add a load balancer and you’re choosing between sticky sessions or a centralized store.
Add another region, and you’re dealing with replication delays. Add more services and suddenly everything depends on the health of the session layer, even requests that shouldn’t.
Nothing explodes. It just slows down. Logouts feel inconsistent. Some users get logged out randomly. Latency creeps in where authentication used to be invisible. And debugging becomes uncomfortable because nothing is technically broken.
Token-based authentication fails differently.
Stateless validation scales cleanly across servers, regions, and services. Requests land anywhere and still work. APIs don’t care who handled the last call. That part feels great until lifecycle mistakes surface.
Long-lived tokens turn into silent security risks. Short-lived tokens increase refresh traffic. Revocation becomes a design problem instead of a switch you flip. When something goes wrong, it’s rarely the validation it’s the policy around the token.
Here’s the subtle difference that matters: Sessions tend to break operationally. Tokens tend to break logically. One struggles with infrastructure coordination. The other struggles with governance and control.
And this is why debates around token based authentication versus sessions get messy. Teams argue models, when the real issue is where failure shows up first. Sessions centralize risk. Tokens distribute it.
Neither choice is wrong. But both make trade-offs that become impossible to ignore once systems grow beyond a single application pretending it’s still small.
The security trade-offs teams usually misunderstand
This is where conversations around authentication quietly drift off course.
Ask most teams why they chose sessions or tokens, and the answer sounds confident. Sessions feel safer because the server stays in control. Tokens feel modern because they don’t rely on shared state. Both assumptions are only half true.
With session based authentication, security feels centralized. If something looks suspicious, you kill the session and you’re done. That control is real but it’s also fragile. Session hijacking doesn’t announce itself. Misconfigured cookies turn into silent vulnerabilities. And when session stores are shared across systems, a single weak point becomes everyone’s problem.
Tokens flip that model.
In token-based authentication, the server trusts what it can verify, not what it remembers. That’s powerful. But it also means mistakes live longer. A leaked token keeps working until it expires. A poorly scoped authentication token can authorize far more than intended. And if refresh logic isn’t airtight, rotation becomes theoretical instead of protective.
Here’s the part teams rarely plan for: browser security and API security behave very differently.
Sessions shine in browser-heavy environments because cookies handle transport naturally if configured correctly. Tokens dominate APIs because headers travel cleanly across services. But crossing those boundaries without thinking through storage, expiration, and renewal is where trouble starts.
A surprising pattern we’ve seen: teams move to token authentication for scale, then accidentally rebuild session behavior on top of it without the guardrails sessions gave them for free.
Security doesn’t come from choosing sessions or tokens. It comes from how carefully you manage authentication tokens, session lifetimes, invalidation paths, and access scope. The model sets the pressure points. Your implementation decides whether those points hold.
What actually scales better by use case, not ideology
This is where teams usually want a clean answer. Sessions or tokens. One choice. One rule. Done. That’s not how it plays out.
Session-based authentication scales best when the system itself remains tightly bounded. Classic web apps. Same domain. Same backend. Clear login and logout expectations. When you need immediate server-side control, sessions behave predictably. You know where identity lives. You know how to shut it off. For a lot of internal tools and web-first products, that still works, and it still remains effective.
But the moment identity needs to travel, sessions start resisting.
APIs don’t want to ask a central store for permission on every call. Mobile apps don’t behave like browsers. Microservices don’t share memory naturally. And global systems don’t enjoy synchronizing state across regions. This is where token-based authentication earns its place.
Tokens scale when identity needs to move independently of infrastructure. A request can hit any service, in any region, and still be authenticated without coordination. That’s why token-based auth shows up so consistently in APIs, SaaS platforms, mobile backends, and SSO-driven ecosystems.
Although both models authenticate users, they optimize for different realities. Sessions optimize for control. Tokens optimize for distribution. And most modern systems don’t live entirely in one reality.
So what happens in practice? Hybrid models. Web apps backed by sessions. APIs protected by authentication tokens. Access tokens for services. Short-lived tokens for users. Central policies that govern both, even if enforcement looks different.
This isn’t indecision. It’s alignment.
Looking to choose the right approach? Start with how identity needs to move through your system not how familiar the model feels. Scale doesn’t care what you prefer. It only responds to what your architecture demands.
Token-based authentication example you interact with every day
Most people picture something abstract when they hear token based authentication. In reality, you probably used it this morning without thinking twice.
Open a mobile app. Log in once. Close it. Come back hours later. You’re still authenticated. No visible session. No browser cookie prompt. Just access.
Here’s how that actually works.
After login, the system issues an authentication token, usually an access token with a short lifespan, often paired with a refresh token. Every API call the app makes includes that token in the request header. The backend doesn’t ask the session store who you are. It validates the token and moves on.
That’s the core token authentication loop:
-
Client presents token
-
Server validates token
-
Request succeeds or fails
No shared state. No dependency on which server handled your last request. This is a textbook token based authentication example, but what makes it scale is what happens next. When the access token expires, the app silently uses the refresh token to get a new one. The user doesn’t re-authenticate. The system stays responsive. Identity keeps flowing without server-side memory.
You see the same pattern across SaaS dashboards, “Sign in with Google,” enterprise SSO portals, and API-driven platforms. These are everyday examples of token based authentication, even if users never see the tokens themselves.
Now contrast that with a session flow.
In a traditional web app using session tokens, every request relies on the server recognizing a stored session ID. That works well when requests always return to the same environment. It feels deliberate. Controlled. Predictable.
But once requests start coming from different devices, services, or regions, tokens pull ahead. They don’t ask the system to remember. They ask it to verify.
And that difference, remembering versus verifying, is what allows token-based authentication to scale naturally in distributed systems.
The scaling checklist most teams skip (and pay for later)
This is the part that doesn’t make it into architecture diagrams. Most authentication failures don’t come from choosing the “wrong” model. They come from skipping the unglamorous work that makes that model survivable at scale.
With session based authentication, the risk usually hides in assumptions. Sessions are created, but not rotated. Cookies exist, but aren’t locked down properly. Session tokens live in memory until a restart wipes them out or worse, live forever because no one defined an expiry strategy. Everything works… until it doesn’t.
If sessions are in play, scaling means treating session management like infrastructure, not glue code. Centralized stores need to be resilient. Cookie settings need to be deliberate. Invalidation paths need to exist for more than just logout buttons.
Token-based authentication has its own version of this problem.
Tokens feel lightweight, which makes them easy to under-design. Long-lived authentication tokens get issued “temporarily” and never revisited. Refresh logic works in happy paths but fails under load. Revocation is assumed to be rare, until it suddenly isn’t.
Here’s where teams usually go wrong: they focus on validating tokens, but ignore managing them.
Short-lived access tokens matter. Rotation matters. Storage decisions matter more than people admit. And once multiple services start trusting the same tokens, governance becomes as important as cryptography.
The uncomfortable truth is this: both models scale only as far as their weakest lifecycle decision.
If you design sessions casually, they turn into a bottleneck. If you design tokens casually, they turn into a liability.
So, what actually scales and how should you decide?
By the time systems reach real scale, the session-versus-token debate usually feels less dramatic than it did at the start. Not because the differences disappear, but because the priorities change.
Session-based authentication continues to work when identity stays close to the application. When control, immediate invalidation, and tightly scoped user flows matter, sessions do their job well. They’re predictable. They’re authoritative. And in the right environments, they remain the simplest way to keep identity grounded.
Token-based authentication earns its value when identity needs to move. Across APIs. Across services. Across regions. It scales not because it’s lighter, but because it doesn’t ask the system to remember. It asks it to verify. That shift is what allows distributed systems to grow without dragging shared state behind every request.
What actually scales isn’t the model, it's the discipline behind it.
Teams run into trouble when sessions are treated like shortcuts instead of infrastructure, or when authentication tokens are issued without thinking through lifespan, scope, and control. Both approaches fail quietly when lifecycle decisions are postponed.
The more useful question isn’t sessions or tokens? It’s where identity needs to travel, and how much control do you need when it gets there?
Once that’s clear, the choice usually makes itself. And more often than not, the answer isn’t exclusive. It’s a deliberate combination that respects the realities of modern systems.
Scale doesn’t reward familiarity. It rewards alignment.
Choose the authentication model that matches how your system actually behaves, not how you hope it will stay.
Ready to scale authentication without having to rebuild it later?
If your product is growing beyond a single app, a single region, or a single login flow, authentication stops being a detail and starts becoming architecture. Sessions, tokens, or a hybrid approach, getting this decision right early saves teams from painful rewrites, security gaps, and operational overhead down the line.
If you’re evaluating how token-based authentication, session management, or modern CIAM patterns fit into your system as it scales, it’s worth looking at platforms built for distributed identity from day one.
Explore how LoginRadius helps teams design authentication that scales cleanly across web, mobile, APIs, and multi-service architectures without forcing you into a one-size-fits-all model.
Because scaling identity shouldn’t mean fixing the same problems twice.
FAQs
Q: What is token-based authentication?
A: Token-based authentication is a method where users receive an authentication token after login, which is sent with every request to verify identity. The server validates the token instead of storing session state, making it easier to scale across APIs and services.
Q: How is session based authentication different from token based authentication?
A: Session-based authentication relies on server-side session tokens stored in a session store, while token-based authentication uses self-contained tokens sent with each request. The key difference lies in state management and how well each approach scales in distributed systems.
Q: What is an authentication token, and how is it used?
A: An authentication token is a credential issued after successful login that proves a user’s identity. It’s typically included in request headers and validated on every request to control access without maintaining a server-side session.
Q: When should you use session tokens instead of authentication tokens?
A: Session tokens work best for traditional web applications where immediate logout, centralized control, and browser-based flows matter. Authentication tokens are better suited for APIs, mobile apps, and microservices where stateless scaling is required.



