Amazon Cognito is often one of the first identity services teams encounter when building on AWS. It’s tightly integrated with the AWS ecosystem, relatively easy to spin up for basic authentication, and works well for teams already invested in AWS IAM and related services.
However, as applications mature, especially customer-facing B2C, B2B SaaS, and partner portals, many teams begin to feel friction. Cognito was not designed as a full-fledged Customer Identity and Access Management (CIAM) platform. Instead, it functions primarily as a gateway into AWS Workforce IAM, which creates gaps when organizations need advanced authentication, flexible UX customization, or identity-specific security controls.
This is where teams start evaluating Amazon Cognito alternatives, platforms purpose-built for CIAM that offer richer authentication methods, better developer experience, and scalability aligned with real-world customer identity use cases.
Evaluation Criteria: What Makes a Great CIAM Platform
Before comparing alternatives to Amazon Cognito, it’s important to define what actually matters when choosing a CIAM platform. Not every identity solution is designed for customer identity, and the differences become more pronounced at scale.
Use Case Fit: CIAM vs Workforce vs B2B Identity
A strong CIAM platform is designed for external users, customers, partners, and tenants, not employees. This means support for high-volume consumer logins, delegated administration, self-service flows, and multi-tenant architectures. Workforce IAM tools, including Cognito’s underlying AWS IAM alignment, often struggle in these scenarios.
Security & User Experience
Security should not come at the expense of user experience. Modern CIAM platforms support passwordless authentication, passkeys (FIDO2/WebAuthn), adaptive MFA, and risk-based controls out of the box. Platforms that rely on custom Lambda logic or extensive configuration to reach this baseline increase both security risk and operational burden.
Learn more about Intelligent MFA that Adapts to Real-Time Threats
Architecture & Scalability
CIAM systems must handle unpredictable traffic patterns, seasonal spikes, marketing campaigns, and global user bases. Cloud-native, multi-tenant architectures with clear SLAs and global performance are essential. Identity should not become a bottleneck during peak traffic.
Data Residency & Compliance
Customer identity data is highly regulated. A CIAM platform should support regional data residency, compliance with GDPR, SOC 2, ISO standards, and provide identity-specific protections such as compromised credential detection. Inheriting cloud-provider compliance alone is not sufficient.
Developer Experience & Migration
Identity touches every part of an application. Clear documentation, mature SDKs, APIs, hosted UIs, and migration tooling directly impact time-to-market. Platforms that require heavy customization for basic functionality increase long-term maintenance costs.
Best Amazon Cognito Alternatives for Customer Identity to Consider in 2026
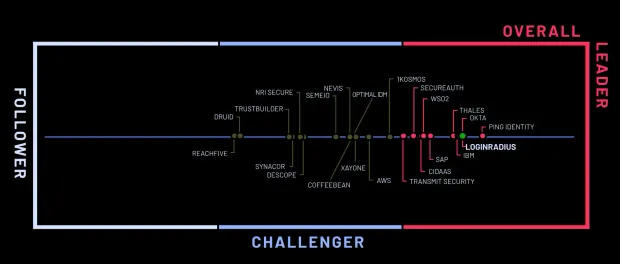
Below are the leading CIAM alternatives to Amazon Cognito, evaluated based on CIAM feature depth, implementation agility, developer experience, scalability, and long-term operational overhead for customer-facing identity.
1. LoginRadius
LoginRadius is a CIAM platform designed specifically for high-volume B2C, B2B SaaS, and public-sector identity, not adapted from workforce IAM or cloud provider tooling like Amazon Cognito. Its design prioritizes consumer-scale traffic, identity-specific security controls, flexible UX orchestration, and global deployment without custom engineering overhead.
Where LoginRadius Works Especially Well
-
CIAM-native architecture: LoginRadius is built for customer identity at scale, with multi-region cloud hosting, high-availability SLAs, geo-isolated tenancy options, and native multi-tenant organization support. These capabilities are foundational, not layered on through custom services or cloud glue code.
-
Rapid deployment without Lambda dependency: Teams implement authentication, MFA, social login, progressive profiling, passkeys, and branded login experiences without writing custom Lambda triggers. This reduces operational risk and accelerates time-to-market compared to Cognito’s event-driven customization model.
-
Broad authentication coverage out of the box: LoginRadius supports passwords, OTP, magic links, WebAuthn passkeys, passwordless flows, social login, adaptive MFA, and enterprise federation through unified APIs and configuration, not fragmented flows.
-
Modern CIAM security stack: Capabilities such as breached password detection, anomaly scoring, bot protection, IP velocity checks, and DDoS mitigation are native to the platform rather than inherited indirectly from cloud infrastructure.
-
Low-/no-code identity orchestration: Hosted templates, journey builders, conditional workflows, and theming allow product and CX teams to adjust identity flows without creating engineering backlogs or touching backend logic.
Ideal For
-
Consumer brands requiring elastic global scale (retail, media, gaming)
-
B2B SaaS platforms needing multi-tenant identity and delegated admin
-
Public-sector and regulated orgs requiring region-of-choice data residency
-
Teams iterating frequently on signup, login, and verification flows
2. Auth0 (Okta Customer Identity Cloud)
Auth0 remains one of the most extensible developer-oriented CIAM platforms and is often evaluated by teams outgrowing Cognito’s customization constraints. It appeals strongly to engineering-led organizations that want to script identity logic directly.
Where Auth0 Performs Well
-
Developer-first extensibility: Rules, Actions, hooks, and SDKs across multiple languages give engineers fine-grained control over tokens, claims, authentication logic, and integrations.
-
Large integration ecosystem: Auth0’s marketplace includes connectors for analytics, fraud tools, marketing platforms, CMS systems, and enterprise identity providers.
-
Strong fit for B2B SaaS onboarding: Supports SAML, OIDC, RBAC, tenant-level configuration, and enterprise SSO scenarios that Cognito handles less elegantly.
CIAM Fit Analysis: Auth0 is well suited for teams that want maximum programmability. However, organizations scaling into very large consumer populations often encounter rising costs, rate limits, and growing configuration complexity as more CIAM logic is stitched together through custom code.
Ideal For
-
Early-stage to mid-market SaaS companies
-
Teams with strong identity engineering expertise
-
Products dependent on deep third-party integrations
Trade-Offs
-
Pricing increases quickly with MAUs and extensibility usage
-
Rate limits can affect very high-volume B2C traffic
-
Many CIAM workflows require ongoing custom code ownership
3. Azure AD B2C (Microsoft Entra External ID)
Azure AD B2C is frequently considered by teams already invested in Microsoft cloud infrastructure, similar to how Cognito appeals to AWS-first organizations.
Where Azure AD B2C Performs Well
-
Microsoft ecosystem alignment: Integrates cleanly with Azure services, Microsoft Entra, and enterprise directories.
-
Baseline CIAM functionality: Supports customer authentication, federation, and social login for straightforward use cases.
CIAM Fit Analysis: Like Cognito, Azure AD B2C originates from workforce IAM foundations. Teams often report friction around policy-heavy configuration, limited UX flexibility, and slow iteration cycles—especially for consumer-facing applications that evolve rapidly.
Ideal For
-
Microsoft-centric organizations
-
Enterprises with existing Entra investments
-
Low-variation CIAM requirements
Trade-Offs
-
Complex custom policy management
-
Limited consumer-grade UX flexibility
-
Identity changes often require IT-managed workflows
4. FusionAuth
FusionAuth positions itself as a developer-focused CIAM platform that can be self-hosted or deployed in the cloud, making it a common alternative for teams seeking more control than Cognito offers.
Where FusionAuth Performs Well
-
Deployment flexibility: Supports self-hosted, private cloud, and managed cloud models, appealing to teams with strict infrastructure control requirements.
-
CIAM-oriented feature set: Provides authentication, MFA, social login, and JWT-based identity flows designed for customer use cases.
-
Transparent pricing model: Avoids MAU-based pricing surprises that can accompany hyperscale CIAM platforms.
CIAM Fit Analysis: FusionAuth gives teams control and predictability, but often requires more hands-on configuration and operational ownership. Compared to fully managed CIAM platforms, teams may need to invest additional effort in scaling, UX tooling, and ongoing maintenance.
Ideal For
-
Engineering-led teams wanting infrastructure control
-
Organizations with DevOps maturity
-
Cost-sensitive reminders with predictable identity volumes
Trade-Offs
-
Greater operational responsibility
-
Less emphasis on no-code UX orchestration
-
Fewer built-in identity analytics and threat signals
5. Ping Identity
Ping Identity is a federation-forward IAM suite that some enterprises evaluate when Cognito no longer meets governance or federation needs.
Where Ping Performs Well
-
Federation maturity: Strong SAML, OAuth, and OIDC capabilities for complex enterprise environments.
-
Hybrid and legacy readiness: Supports cloud, on-prem, and hybrid identity architectures.
CIAM Fit Analysis: Ping excels at enterprise IAM but often requires third-party tools or custom development to deliver modern consumer onboarding experiences. For CIAM teams, this frequently translates into higher cost and slower iteration.
Ideal For
-
Large enterprises with hybrid identity estates
-
Organizations prioritizing federation over UX agility
Trade-Offs
-
Heavy implementation footprint
-
Limited native consumer UX tooling
-
Slower CIAM iteration cycles
6. WorkOS
WorkOS is not a full CIAM platform, but it is commonly evaluated alongside Cognito by B2B SaaS teams.
Where WorkOS Performs Well
Turnkey enterprise SSO: Provides SAML, OIDC, SCIM, directory sync, and audit logs with minimal engineering effort.
Fast time-to-value: Clear APIs and documentation allow teams to ship enterprise SSO quickly.
CIAM Fit Analysis: WorkOS solves a specific problem, B2B enterprise SSO, but does not address broader CIAM needs such as consumer authentication, MFA orchestration, passkeys, or UX customization.
Ideal For
-
SaaS platforms selling into enterprise accounts
-
Teams offloading SAML and SCIM complexity
Trade-Offs
-
Not a complete CIAM solution
-
No consumer-grade authentication journeys
-
Must be paired with another identity system
Why People Switch From Amazon Cognito to LoginRadius
Below are the most common reasons organizations tell us they explore migrating from Amazon Cognito to LoginRadius.
1. Difficulty Delivering Consumer-Grade UX and Branding
A consistent theme from product and growth teams is that Cognito’s hosted UI offers only surface-level branding and limited control over the end-user experience. While teams can build custom UIs on top of Cognito, doing so shifts responsibility for security, validation, and edge cases entirely onto application teams. Cognito was designed as an AWS service abstraction, not as a consumer-facing experience layer.
LoginRadius provides fully customizable hosted pages, headless authentication options, and no-code theming. Teams can design branded signup and login journeys that align with conversion goals and brand standards, without reimplementing authentication logic or maintaining parallel UI stacks.
2. Lambda-Heavy Customization Slows Identity Iteration
Cognito relies extensively on Lambda triggers to support even common CIAM requirements such as adaptive MFA logic, progressive profiling, conditional authentication, or custom validation. Over time, identity flows become fragmented across pre-auth, post-auth, and token-generation triggers, increasing debugging effort and operational risk.
LoginRadius centralizes identity orchestration within the CIAM platform itself. Journey builders, conditional workflows, and configuration-driven controls allow teams to modify identity flows quickly, adding fields, changing MFA rules, or introducing new login methods, without touching serverless code or redeploying infrastructure.
3. Passwordless and Passkeys Require Custom Engineering
Although Cognito can technically support passwordless patterns, implementations require custom authentication challenges, bespoke Lambda logic, and ongoing maintenance. Teams frequently report that rolling out passkeys or modern passwordless experiences becomes a multi-sprint engineering project rather than a configuration decision.
LoginRadius delivers passkeys (FIDO2/WebAuthn), magic links, OTP, and one-tap passwordless flows as native CIAM features. These options are unified under consistent APIs and admin controls, making it easier to adopt modern authentication without rebuilding identity infrastructure.
4. Limited Identity-Specific Security Beyond Basic MFA
Cognito supports SMS and TOTP-based MFA, but deeper CIAM security signals—such as breached password detection, anomaly scoring, behavioral risk analysis, or bot mitigation—are not native to the service. Teams must integrate additional AWS services or third-party tools to close these gaps.
LoginRadius includes identity-specific security controls directly in the platform. Features such as compromised credential intelligence, adaptive risk evaluation, IP velocity checks, and bot protection are built into CIAM workflows rather than bolted on afterward.
5. Cognito Is an AWS IAM Gateway, Not a CIAM Platform
At its core, Cognito is designed to bridge external users into AWS IAM roles and services. While this works well for AWS-centric architectures, it introduces limitations for organizations managing rich customer identity lifecycles, multiple brands, B2B tenants, delegated administration, and complex profile data.
LoginRadius is purpose-built for customer and partner identity. Its identity model, orchestration engine, and multi-tenant capabilities are designed for B2C and B2B CIAM use cases from day one, rather than adapted from workforce IAM assumptions.
6. Operational Complexity Grows with Scale
As Cognito deployments grow, teams often report increasing operational overhead: managing scattered Lambda logic, troubleshooting inconsistent behaviors across regions, and tracing authentication failures across multiple AWS services. Identity becomes harder to reason about, especially during peak traffic or incident response.
LoginRadius reduces this complexity through predictable APIs, centralized logging, consistent behavior across environments, and support teams focused exclusively on CIAM. This allows engineering teams to spend less time maintaining identity plumbing and more time building product features.
7. Need for a CIAM Platform That Evolves with the Product
The underlying reason teams ultimately move away from Cognito is strategic. CIAM is no longer just authentication, it’s a growth, security, and customer experience layer that evolves continuously alongside the product.
LoginRadius is built to support that evolution. From passkey-first authentication and adaptive MFA to multi-tenant B2B identity and region-of-choice data residency, the platform is designed to help organizations modernize identity without inheriting cloud-provider IAM constraints.
Amazon Cognito vs LoginRadius: CIAM Capability Comparison
| Capability | Amazon Cognito | LoginRadius |
|---|---|---|
| Primary focus | AWS IAM gateway for external users | Purpose-built CIAM for B2C, B2B, and partner identity |
| CIAM readiness out of the box | Limited – requires custom Lambda logic for many CIAM features | High – CIAM-native features enabled through configuration |
| Passwordless authentication | Possible, but requires custom auth flows and maintenance | Native support for passkeys, magic links, OTP, and passwordless |
| Passkeys (FIDO2 / WebAuthn) | Not native; requires custom implementation | Native, first-class support |
| Multi-factor authentication (MFA) | Basic SMS and TOTP | Adaptive MFA, push MFA, risk-based controls |
| Adaptive / risk-based authentication | Requires custom Lambda logic | Built-in and configurable |
| Hosted login UI customization | Very limited branding | Fully customizable hosted pages and themes |
| No-code / low-code identity orchestration | Not available | Journey builders, workflows, conditional logic |
| Social login setup | Manual and fragmented configuration | Centralized configuration with broad provider support |
| Progressive profiling | Custom implementation required | Native progressive profiling workflows |
| B2B / multi-tenant identity | Limited and manual | Native multi-tenant orgs and delegated admin |
| Identity-specific security | Relies on AWS services | Built-in breached password detection, bot protection, anomaly signals |
| Compliance & privacy posture | AWS compliance inheritance | GDPR, SOC 2, ISO + CIAM-specific protections |
| Data residency flexibility | Region fixed to AWS deployment | Contractual region-of-choice hosting |
| Developer experience | AWS-centric, Lambda-heavy | CIAM-focused APIs, SDKs, and tooling |
| Operational overhead at scale | Increases with custom logic | Centralized, predictable CIAM operations |
| Best fit for | AWS-first, low-complexity identity | Consumer, B2B SaaS, and regulated CIAM use cases |
Conclusion
Amazon Cognito serves a clear role within the AWS ecosystem, particularly for teams building simple authentication flows tightly coupled with AWS services. However, it was never designed to be a comprehensive CIAM platform.
As organizations grow, common pain points emerge, limited passwordless options, heavy reliance on custom Lambda logic, constrained UX customization, and gaps in identity-specific security. These challenges are reflected consistently in user feedback and real-world implementation experiences.
For teams building customer-facing platforms, B2B SaaS applications, and partner ecosystems, choosing a CIAM platform should be about more than basic authentication. It should support modern security standards, seamless user experiences, global scalability, and long-term maintainability.
LoginRadius is built specifically for these scenarios. By focusing exclusively on customer identity, we help teams move faster, reduce complexity, and deliver secure authentication experiences that scale with their business.
If you’re evaluating alternatives to Amazon Cognito, our team is happy to walk through your use case, review migration considerations, and help you determine whether LoginRadius is the right fit.



