Descope has earned attention for making authentication approachable. Its drag-and-drop workflows, prebuilt components, and fast setup appeal to teams that want to ship login and signup experiences quickly without deep identity expertise. For early-stage products or straightforward consumer use cases, that simplicity can be a real advantage.
However, as applications grow, identity requirements tend to outpace low-code abstractions. Teams supporting millions of users, complex B2B or partner models, strict compliance mandates, or global performance expectations often find that widget-first approaches start to impose limits. Custom UI flows become harder to implement, orchestration logic is constrained by predefined patterns, and architectural control over hosting, data residency, and scalability becomes increasingly important.
That’s why many engineering and security teams eventually evaluate Descope alternatives. The goal isn’t just “more features,” but a CIAM platform that remains easy to adopt while offering total control when identity becomes mission-critical. In this guide, we compare the top Descope alternatives, focusing on platforms built for developer-first CIAM, enterprise-scale performance, and long-term flexibility as identity complexity increases.
Evaluation criteria: What makes a great CIAM platform
Choosing a Descope alternative isn’t about finding a platform with more features; it’s about finding one that fits how your product, users, and security requirements evolve over time. As identity becomes a core part of your architecture, the right CIAM platform should scale technically, operationally, and organizationally.
Below are the key criteria teams typically use when evaluating enterprise-ready CIAM solutions.
Use case fit: CIAM vs workforce vs B2B identity
Not all identity platforms are built for the same purpose. Workforce IAM tools are optimized for employee access, internal directories, and corporate controls. CIAM platforms, by contrast, must support millions of external users, unpredictable traffic spikes, and frictionless onboarding at internet scale.
As identity requirements mature, many organizations also need B2B and partner identity capabilities, including tenant isolation, delegated administration, role hierarchies, and account-level policies. These models introduce complexity that workforce-first or low-code platforms often struggle to represent cleanly.
A strong CIAM platform should support B2C, B2B, or hybrid identity models natively, without forcing architectural workarounds, parallel identity stores, or custom logic as business requirements evolve.
Security & user experience
Security can no longer be treated as a trade-off against user experience. Modern CIAM platforms must deliver strong protection while minimizing friction for legitimate users.
This requires built-in MFA depth, including push-based authentication, FIDO2 passkeys, WebAuthn, and multiple second-factor options. Passwordless authentication is no longer experimental; it has become a baseline expectation for modern consumer and business applications.
Equally important is contextual security enforcement. Leading CIAM platforms apply risk-based controls dynamically, reducing friction for trusted users while escalating protection when signals change, such as new devices, unusual locations, or anomalous behavior.
Architecture & scalability
CIAM platforms must be cloud-native, highly available, and proven at scale. This includes true multi-tenant architecture, regional deployment options, strong SLAs, and predictable performance during peak traffic events such as product launches or seasonal demand spikes.
Legacy architectures often struggle in this area, particularly when customization, orchestration, or complex policy logic is layered on top. At scale, architectural limitations surface quickly as latency, reliability, or operational overhead.
Also learn how to Build User Workflows with No-code Orchestration Engine
Data residency & compliance
Customer identity data is regulated data. For global brands and regulated industries, CIAM platforms must provide clear data residency controls, regional hosting options, and alignment with regulatory frameworks such as GDPR, CCPA, HIPAA, and SOC 2.
Lack of transparency or flexibility around where identity data is stored and processed can become a blocker during security reviews, procurement, or geographic expansion.
Developer experience & migration effort
CIAM implementations live or die by developer adoption. Clear APIs, well-maintained SDKs, modern documentation, sandbox environments, and migration tooling all reduce time-to-value and long-term friction.
Platforms that rely heavily on professional services for routine changes often slow teams down as requirements evolve. In contrast, developer-first CIAM platforms enable teams to own identity as part of their core architecture, not as an external dependency.
Best Descope Alternatives for Customer Identity to Consider in 2026
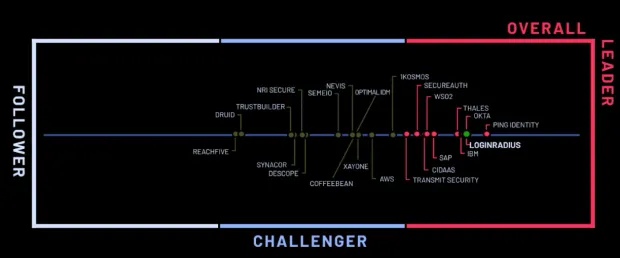
Below are the leading CIAM alternatives to Descope, evaluated based on CIAM feature depth, implementation agility, developer experience, scalability, and long-term operational overhead for customer-facing identity.
1. LoginRadius
LoginRadius is a CIAM platform designed specifically for high-volume B2C, B2B SaaS, and public-sector identity, rather than adapted from workforce IAM or low-code authentication tooling. Its design prioritizes consumer-scale traffic, identity-specific security controls, flexible UX orchestration, and global deployment without introducing custom engineering overhead as scale increases.
Where LoginRadius works especially well
-
CIAM-native architecture: LoginRadius is purpose-built for customer identity at scale, with multi-region cloud hosting, high-availability SLAs, geo-isolated tenancy options, and native multi-tenant organization support. These capabilities are foundational to the platform, not layered on through external services or custom glue code.
-
Headless identity without orchestration limits: Teams can implement fully custom login, registration, MFA, verification, and recovery flows using APIs, webhooks, and configurable workflows. Unlike widget-first platforms, LoginRadius does not constrain UI or logic to predefined patterns as requirements evolve.
-
Broad authentication coverage out of the box: LoginRadius supports passwords, OTPs, magic links, passkeys (WebAuthn), passwordless flows, social login, adaptive MFA, and enterprise federation through unified APIs and configuration, without fragmenting identity logic across multiple tools.
-
Modern CIAM security stack: Security features such as breached password detection, anomaly scoring, bot protection, IP velocity checks, and DDoS mitigation are native to the platform and designed specifically for consumer identity threat models.
-
Low- and no-code identity orchestration: Hosted templates, conditional workflows, and real-time theming allow product and CX teams to adjust identity experiences without creating engineering backlogs or redeploying backend services.
Ideal for
-
Consumer brands requiring elastic global scale (retail, media, gaming)
-
B2B SaaS platforms with multi-tenant identity and delegated administration
-
Public-sector and regulated organizations needing region-of-choice data residency
-
Teams iterating frequently on signup, login, and verification experiences
2. Auth0
Auth0 is one of the most widely adopted developer-oriented CIAM platforms and is frequently evaluated by teams that want more programmability than low-code or cloud-native identity services provide. It appeals strongly to engineering-led organizations that prefer to script identity logic directly.
Where Auth0 performs well
-
Developer-first extensibility: Rules, Actions, hooks, and SDKs across multiple languages give developers fine-grained control over tokens, claims, authentication logic, and downstream integrations.
-
Large integration ecosystem: Auth0 offers a broad marketplace of integrations for analytics platforms, fraud detection tools, marketing systems, CMS platforms, and enterprise identity providers.
-
Strong fit for B2B SaaS onboarding: Supports SAML, OIDC, RBAC, tenant-level configuration, and enterprise SSO scenarios that simpler CIAM platforms struggle to model cleanly.
CIAM fit analysis: Auth0 works well for teams that value maximum programmability and are comfortable owning identity logic as code. However, organizations scaling into very large consumer populations often encounter rising costs, rate limits, and increasing configuration complexity as more CIAM workflows are stitched together through custom logic.
Ideal for
-
Early-stage to mid-market SaaS companies
-
Teams with strong identity and security engineering expertise
-
Products that depend heavily on third-party integrations
Trade-offs
-
Pricing increases quickly as MAUs and extensibility usage grow
-
Rate limits can impact very high-volume B2C traffic
-
Many CIAM workflows require ongoing custom code ownership
3. Microsoft Entra External ID (formerly Azure AD B2C)
Microsoft Entra External ID is commonly evaluated by organizations already invested in Microsoft’s cloud and identity ecosystem, similar to how AWS-first teams gravitate toward Amazon Cognito.
Where Entra External ID performs well
-
Microsoft ecosystem alignment: Integrates closely with Azure services, Microsoft Entra, and enterprise Active Directory environments.
-
Baseline CIAM capabilities: Supports customer authentication, federation, and social login for relatively straightforward consumer and external user scenarios.
CIAM fit analysis: Like many workforce-origin identity platforms, Entra External ID inherits a policy-heavy configuration model. Teams often report friction around UX customization, slow iteration cycles, and complexity when adapting workforce-style controls to consumer-facing applications that change frequently.
Ideal for
-
Microsoft-centric organizations
-
Enterprises with existing Entra and Azure investments
-
Low-variation CIAM requirements
Trade-offs
-
Complex custom policy management
-
Limited consumer-grade UX flexibility
-
Identity changes often require IT-managed workflows
4. FusionAuth
FusionAuth positions itself as a developer-focused CIAM platform with flexible deployment options, making it a common alternative for teams that want more control than low-code platforms offer.
Where FusionAuth performs well
-
Deployment flexibility: Supports self-hosted, private cloud, and managed cloud models, appealing to organizations with strict infrastructure or compliance requirements.
-
CIAM-oriented feature set: Provides authentication, MFA, social login, and JWT-based identity flows designed for customer-facing use cases rather than workforce IAM.
-
Predictable pricing model: Avoids some of the MAU-driven pricing volatility seen in hyperscale CIAM platforms.
CIAM fit analysis: FusionAuth gives teams control and predictability, but typically requires more hands-on configuration and operational ownership. Compared to fully managed CIAM platforms, teams may need to invest additional effort in scaling, UX tooling, and long-term maintenance.
Ideal for
-
Engineering-led teams seeking infrastructure control
-
Organizations with strong DevOps maturity
-
Cost-sensitive teams with predictable identity volumes
Trade-offs
-
Greater operational responsibility
-
Less emphasis on no-code UX orchestration
-
Fewer built-in analytics and threat detection signals
5. Transmit Security
Transmit Security is a CIAM platform focused on passwordless-first authentication, adaptive risk analysis, and fraud prevention, often evaluated by enterprises that want to reduce login friction while strengthening security posture.
Where Transmit Security performs well
-
Passwordless and risk-based authentication: Transmit Security emphasizes passkeys, biometric authentication, and adaptive risk signals to minimize reliance on passwords. Authentication decisions can dynamically adjust based on device, behavior, and contextual risk.
-
Fraud-aware identity layer: The platform integrates identity with fraud detection signals, helping teams reduce account takeover risk and automate step-up authentication when anomalies are detected.
-
Enterprise security orientation: Designed with large enterprises in mind, Transmit Security aligns well with organizations prioritizing security outcomes over rapid low-code implementation.
CIAM fit analysis: Transmit Security excels when identity is tightly coupled with fraud prevention and risk analysis. However, teams looking for broad CIAM primitives—such as deep B2B tenant models, no-code UX orchestration, or generalized identity workflows—may need to complement it with additional tooling.
Ideal for
-
Enterprises prioritizing passwordless-first strategies
-
Organizations with elevated fraud and ATO risk
-
Security-led teams focused on adaptive authentication
Trade-offs
-
Less emphasis on full CIAM lifecycle management
-
Limited low-code UX customization
-
May require integration with additional CIAM components
6. Ping Identity
Ping Identity is an enterprise IAM vendor with strong roots in federation, access control, and hybrid identity architectures, commonly deployed in complex, regulated environments.
Where Ping Identity performs well
-
Enterprise-grade federation and policy control: Ping excels at complex authentication policies, federation scenarios, and hybrid deployments spanning on-prem and cloud environments.
-
Flexible deployment models: Supports cloud, on-premises, and hybrid deployments, making it suitable for organizations with legacy infrastructure or strict compliance requirements.
-
Mature IAM capabilities: Well-suited for enterprises with sophisticated identity governance and access management needs.
CIAM fit analysis: While Ping Identity offers CIAM capabilities, its heritage as an enterprise IAM platform can introduce complexity for consumer-facing use cases. CIAM teams often face longer implementation timelines and heavier configuration overhead compared to CIAM-native platforms.
Ideal for
-
Large enterprises with hybrid or legacy identity environments
-
Regulated industries with complex access policies
-
Organizations standardizing across workforce and customer IAM
Trade-offs
-
Higher implementation and operational complexity
-
Less optimized for rapid CIAM iteration
-
Consumer UX customization can require significant effort
7. Amazon Cognito
Amazon Cognito is AWS’s native CIAM service and is frequently evaluated by teams already building on AWS infrastructure.
Where Amazon Cognito performs well
-
Native AWS integration: Deep integration with AWS services makes Cognito appealing for teams committed to the AWS ecosystem.
-
Basic CIAM capabilities: Supports user authentication, federation, MFA, and social login for relatively simple identity requirements.
-
Cost-effective entry point: Often attractive for early-stage teams due to low initial cost and infrastructure familiarity.
CIAM fit analysis: Cognito’s customization model relies heavily on Lambda triggers and event-driven logic, which can become difficult to manage as CIAM complexity grows. Teams scaling to large consumer audiences frequently encounter limitations around UX flexibility, orchestration, and operational overhead.
Ideal for
-
AWS-first development teams
-
Simple CIAM requirements
-
Early-stage products with limited customization needs
Trade-offs
-
Heavy reliance on custom Lambda logic
-
Limited UX and orchestration flexibility
-
Operational complexity at scale
8. Frontegg
Frontegg focuses on embedded user management for B2B SaaS platforms, positioning itself as a product-led growth accelerator rather than a general-purpose CIAM platform.
Where Frontegg performs well
-
B2B SaaS-native features: Provides built-in support for organizations, roles, permissions, and self-serve administration tailored to SaaS products.
-
Fast time-to-market: Enables teams to ship common B2B identity features quickly without building them from scratch.
-
Product-led onboarding support: Designed to support trials, upgrades, and in-app user management flows.
CIAM fit analysis: Frontegg works well for SaaS products with predictable B2B patterns, but it is not designed for large-scale B2C identity or highly customized CIAM architectures. Teams with broader identity needs often pair it with another CIAM solution.
Ideal for
-
B2B SaaS platforms
-
Product-led growth teams
-
Companies prioritizing speed over deep customization
Trade-offs
-
Limited support for large-scale B2C identity
-
Less flexible outside standard SaaS patterns
-
Not a full CIAM replacement for complex use cases
9. WorkOS
WorkOS specializes in enterprise SSO, directory sync, and compliance tooling for SaaS vendors rather than full CIAM lifecycle management.
Where WorkOS performs well
-
Enterprise SSO enablement: Simplifies SAML and OIDC integrations with customer enterprise identity providers.
-
Developer-friendly APIs: Designed for fast integration with minimal configuration overhead.
-
Focused product scope: Avoids complexity by concentrating on enterprise readiness rather than full CIAM breadth.
CIAM fit analysis: WorkOS is best viewed as a complementary identity layer rather than a Descope replacement. Teams typically pair WorkOS with a CIAM platform to handle authentication, MFA, and user lifecycle management.
Ideal for
-
SaaS vendors selling into enterprise accounts
-
Teams needing fast SSO enablement
-
Products adding enterprise features incrementally
Trade-offs
-
Not a full CIAM platform
-
Limited consumer identity capabilities
-
Requires pairing with another identity solution
Why People Switch From Descope to LoginRadius
Teams rarely move away from Descope because it fails at basic authentication. Most switches happen later, when identity stops being a “login feature” and becomes a core platform dependency tied to scale, compliance, and product differentiation.
From simple orchestration to enterprise-grade workflows
Descope is designed to make authentication easy to get started with, particularly for straightforward login and verification flows. That simplicity works well early on, but it can become limiting as identity logic grows more complex.
LoginRadius offers a similarly low-friction starting point, while providing deeper orchestration capabilities through APIs, webhooks, and configurable workflows. Teams can model advanced identity logic, such as progressive profiling, conditional MFA, tenant-aware policies, and region-specific flows, without rebuilding or working around predefined patterns. This allows identity to scale in complexity without forcing a platform change later.
From widget-first UX to fully headless identity control
Descope takes a widget-first approach, which can accelerate initial implementation but often constrains long-term flexibility. As products mature, teams frequently need tighter control over UX, branding, localization, accessibility, and channel-specific experiences.
LoginRadius is headless by design. Teams can build fully custom frontends or use hosted pages where it makes sense, without sacrificing control. Real-time branding, multi-language support, and channel-specific customization allow identity experiences to evolve alongside the product, rather than lag behind it.
From limited developer control to CIAM-native extensibility
Descope prioritizes simplicity through prebuilt components, but this often comes at the cost of granular control. As identity requirements expand, engineering teams may find themselves constrained by what can and cannot be customized cleanly.
LoginRadius provides full SDK coverage, REST APIs, and fine-grained extensibility hooks, backed by detailed developer documentation. This allows teams to treat identity as part of their core architecture, versioned, testable, and adaptable rather than a black box that limits iteration.
From fixed hosting to flexible deployment models
Hosting and data residency are increasingly non-negotiable for enterprises and regulated industries. Descope offers limited control over where and how identity services are deployed, which can create friction during procurement, compliance reviews, or geographic expansion.
LoginRadius supports public cloud and private cloud deployments, enabling organizations to meet regional data residency requirements, align with internal infrastructure standards, and support hybrid architectures when needed. For many teams, this flexibility becomes a deciding factor as identity data volumes and regulatory exposure increase.
LoginRadius vs Descope: CIAM Capability Comparison
| Capability | LoginRadius | Descope |
|---|---|---|
| Primary focus | CIAM-native platform built for B2C, B2B, and public-sector identity at scale | Low-code authentication and flow orchestration for simple CIAM use cases |
| Architecture model | Cloud-native, multi-tenant CIAM architecture designed for high-volume external users | Workflow- and component-driven abstraction layer |
| Scalability profile | Proven support for 100M+ users and very high request volumes | Best suited for smaller-scale and moderate traffic patterns |
| B2B & partner identity | Native support for organizations, tenants, roles, and delegated administration | Limited depth for complex B2B identity models |
| UI & UX control | Headless by default with optional hosted pages and real-time branding | Widget-first approach with constrained customization |
| Identity orchestration | APIs, webhooks, conditional workflows, and no-/low-code configuration | Drag-and-drop flow builder with predefined patterns |
| Authentication methods | Passwords, OTPs, magic links, passkeys (WebAuthn), passwordless, social login, enterprise federation | Passwordless-focused with limited extensibility beyond core flows |
| Adaptive & risk-based security | Built-in CIAM security controls including anomaly detection and adaptive MFA | Limited contextual and risk-based controls |
| Deployment options | Public cloud and private cloud deployments | Fixed SaaS hosting model |
| Data residency control | Region-of-choice hosting and geo-isolated tenancy options | Limited control over data location |
| Developer experience | Full SDKs, REST APIs, granular hooks, and detailed documentation | Simplified developer experience with less granular control |
| Customization ownership | Product and engineering teams retain full control over identity logic | Customization constrained by platform abstractions |
Conclusion
Descope succeeds at what it sets out to do: simplifying authentication for teams that want to move fast with minimal configuration. For straightforward login and passwordless flows, its low-code approach can reduce early friction and shorten time to first release. But as applications grow and identity becomes more central to security, compliance, and product experience those same abstractions often become constraints.
Teams supporting large consumer audiences, B2B or partner identity models, or regulated workloads typically need more than drag-and-drop flows. They need a CIAM platform that can scale predictably, support complex identity relationships, adapt to regional and regulatory requirements, and give engineering teams long-term ownership over identity logic and UX.
That’s where platforms like LoginRadius stand out. Built specifically for customer identity at enterprise scale, LoginRadius offers the flexibility, performance, and architectural control required when identity is no longer just an onboarding feature, but a core part of the product and security strategy. For teams evaluating Descope alternatives, the decision ultimately comes down to whether identity will remain simple or whether it needs to evolve into a durable, enterprise-grade platform as the business grows.
If you’re comparing CIAM platforms for scale, compliance, or long-term flexibility, explore a detailed LoginRadius vs Descope comparison or speak with our team to review your identity requirements and migration options in depth.



