FusionAuth has earned a strong reputation among developer-led teams that value flexibility, control, and self-hosted identity infrastructure. Its API-first design and deployment freedom make it appealing for organizations that want to own every layer of their authentication stack.
However, as digital products scale and identity becomes a core business dependency, many teams begin to question whether managing CIAM infrastructure in-house is still the right long-term strategy. Operating identity systems isn’t just about authentication anymore; it now includes uptime guarantees, global scale, security hardening, regulatory compliance, and ongoing maintenance.
That’s why more teams are evaluating FusionAuth alternatives that deliver CIAM as a fully managed service. In this guide, we break down what to look for in a modern CIAM platform and explore the top alternatives to FusionAuth.
Evaluation criteria: What makes a great CIAM platform
Before comparing vendors, it’s important to understand what separates a basic authentication tool from a true CIAM platform. Below are the criteria we see most teams use when reassessing FusionAuth or similar self-managed CIAM solutions.
Use case fit: CIAM, workforce IAM, and B2B identity
A great CIAM platform is purpose-built for external identities, not retrofitted from workforce IAM. CIAM systems must support millions of consumer or customer users, unpredictable traffic spikes, and diverse authentication journeys, all while maintaining a seamless user experience. Platforms originally designed for employees often struggle when extended to customers or partners, especially as scale and complexity increase.
B2B and partner identity introduces an additional layer of requirements, including multi-tenant organizations, delegated administration, role hierarchies, and tenant-level policies. CIAM platforms should support these use cases natively, rather than forcing teams to build custom logic on top of generic IAM primitives. The closer a platform aligns with your real-world identity use cases, the less technical debt you accumulate over time.
Security & user experience
Security and user experience are inseparable in modern CIAM. Strong authentication controls, such as multi-factor authentication, passwordless login, and passkeys, must be implemented in ways that reduce friction rather than increase it. If security measures feel intrusive or inconsistent, users abandon logins, reset passwords unnecessarily, or bypass safeguards entirely.
Leading CIAM platforms also incorporate adaptive and risk-based authentication, adjusting security requirements dynamically based on context, behavior, and risk signals. This allows organizations to enforce stronger protection when needed, without applying the same friction to every login. The goal is not just to secure access, but to do so in a way that preserves conversion rates and user trust.
Architecture, scalability, and reliability
CIAM infrastructure sits directly on the critical path of your digital experience. If authentication fails, users cannot access your product, no matter how well everything else works. As a result, scalability and reliability are not optional features; they are foundational requirements.
A strong CIAM platform is cloud-native, auto-scales to handle traffic surges, and includes clear uptime guarantees backed by SLAs. Teams should not have to manually provision infrastructure, manage databases, or design high-availability architectures just to keep authentication online. Offloading these responsibilities to a managed CIAM provider reduces operational risk and frees engineering teams to focus on product development instead of identity infrastructure.
Data residency & compliance
As privacy regulations expand globally, CIAM platforms must support data residency, compliance, and privacy by design. Many organizations now operate across regions with different legal requirements, making it essential to control where identity data is stored and processed.
A mature CIAM provider offers regional hosting options, documented compliance certifications such as SOC 2 and ISO, and clear guidance on shared responsibility. When compliance is embedded into the platform itself, teams avoid costly retrofits and audits later. This is especially important for regulated industries and enterprises operating across multiple jurisdictions.
Developer experience & time to value
Developer experience has a direct impact on how quickly teams can launch and iterate on identity features. Clear documentation, well-maintained SDKs, and intuitive APIs reduce onboarding time and prevent implementation errors. When identity systems are hard to configure or poorly documented, teams compensate with custom code that becomes difficult to maintain.
Beyond initial setup, teams must also consider long-term operational effort. Migration tooling, versioned APIs, backward compatibility, and vendor support all influence the total cost of ownership. A great CIAM platform minimizes time to value not just on day one, but throughout the lifecycle of your application as requirements evolve.
Top 7 FusionAuth Alternatives to Consider in 2026
Below are the leading alternatives teams commonly evaluate when moving away from FusionAuth.
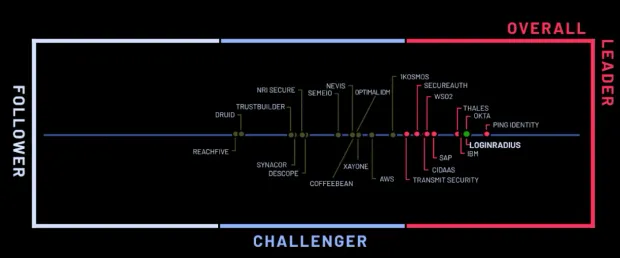
1. LoginRadius
LoginRadius is a CIAM platform designed specifically for high-volume B2C, B2B SaaS, and regulated enterprise identity use cases. Unlike FusionAuth, which emphasizes developer control through self-managed and self-hosted deployments, LoginRadius is purpose-built for customer identity as a fully managed infrastructure layer, designed to scale securely across regions, tenants, and compliance boundaries.
While FusionAuth works well for engineering-led teams that want to own and operate their identity stack, LoginRadius is designed for organizations that need enterprise-grade security controls, compliance readiness, and long-term architectural flexibility without taking on infrastructure ownership or operational overhead as identity requirements grow.
Where LoginRadius Works Especially Well
CIAM-native, enterprise-ready architecture: LoginRadius is built from the ground up for customer and partner identity at scale. The platform supports multi-region cloud deployments, geo-isolated data residency, SLA-backed availability, and native multi-tenant organization models. These capabilities are foundational to the platform and fully managed by LoginRadius, whereas FusionAuth requires teams to design, deploy, and maintain these architectural elements themselves as they scale.
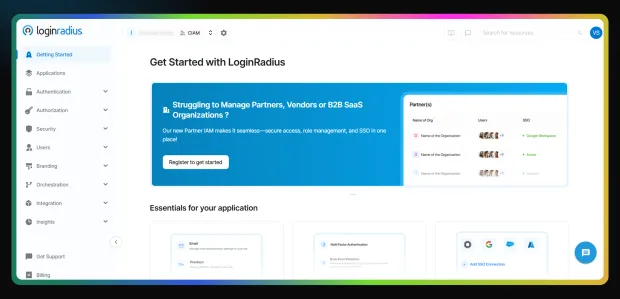
Enterprise MFA and passwordless authentication: LoginRadius provides native support for push notification MFA, adaptive risk-based authentication, passkeys, WebAuthn, hardware-backed keys, OTPs, magic links, and step-up authentication flows. FusionAuth supports many core authentication methods, but advanced adaptive controls, push-based MFA, and risk-driven policies typically require additional configuration and ongoing operational management by the customer.
Compliance-ready by default: LoginRadius comes with SOC 2 Type II, ISO 27001, GDPR, and CCPA compliance built in, along with configurable regional data residency options. This simplifies approvals from security, legal, and procurement teams. With FusionAuth, compliance is largely a shared responsibility, requiring customers to manage infrastructure, controls, and audit readiness on their own environments.
Proven scalability with SLA-backed APIs: LoginRadius is designed to support millions of identities with predictable performance during traffic spikes such as product launches, seasonal demand, or large enterprise onboardings. APIs are SLA-backed and supported by globally distributed infrastructure. FusionAuth can scale effectively, but performance, uptime, and resilience depend heavily on how the customer provisions and operates their infrastructure.
Low-code identity orchestration for faster iteration: Hosted login experiences, configurable workflows, progressive profiling, conditional MFA policies, and theming tools allow teams to evolve authentication and onboarding journeys without continuous engineering effort. In contrast, FusionAuth often requires deeper customization and hands-on development to achieve similar flexibility, increasing long-term maintenance effort.
Enterprise-grade migration and support model: LoginRadius provides structured migration tooling, professional services, and dedicated customer success managers to support large-scale or regulated deployments. FusionAuth’s support model is well-suited for self-sufficient teams but can become a limitation for organizations that need hands-on migration guidance, SLAs, and enterprise-level operational support.
Ideal For
-
B2B SaaS platforms that need multi-tenant identity, delegated administration, and enterprise security
-
Consumer brands operating at global scale with peak traffic volatility
-
Regulated industries requiring certifications and regional data residency
-
Organizations that want fully managed CIAM and expect identity complexity to grow over time without replatforming
2. Auth0
Auth0 is a cloud-based identity platform widely adopted by developer teams building modern web and mobile applications. It is often evaluated as a FusionAuth alternative by teams that want a managed service with strong developer tooling and extensibility.
Where Auth0 Performs Well
-
Developer-friendly APIs and SDKs: Broad language and framework support with well-documented APIs.
-
Extensible authentication flows: Rules and actions enable custom logic and integrations.
-
Large integration ecosystem: Marketplace of prebuilt integrations with SaaS and infrastructure tools.
CIAM Fit Analysis: Auth0 works well for teams that want a managed IAM service with strong developer ergonomics. However, as CIAM usage scales, pricing complexity and add-on driven feature access can become friction points. For larger B2C or B2B deployments, cost predictability and advanced CIAM controls may require careful planning.
Ideal For
-
Developer-led product teams
-
Startups and mid-market SaaS companies
-
Applications needing rapid IAM integration
Trade-Offs
-
Pricing escalates quickly at scale
-
CIAM features often gated by higher tiers
-
Limited flexibility around certain data residency needs
3. Microsoft Entra ID (Azure AD B2C)
Microsoft Entra ID is Microsoft’s identity platform, extending Azure Active Directory to external users through Entra ID for customers. It is most often considered by organizations already standardized on Microsoft infrastructure.
Where Microsoft Entra ID Performs Well
-
Native Microsoft ecosystem integration: Deep alignment with Azure, Microsoft 365, and enterprise IT tooling.
-
Enterprise security foundation: Built on Microsoft’s security and identity stack.
-
Scalable global infrastructure: Backed by Azure’s worldwide footprint.
CIAM Fit Analysis: Entra ID can support customer identity scenarios, but it is fundamentally an extension of a workforce IAM system. CIAM implementations often require significant configuration and compromise on user experience. It is better suited for IT-led environments than product-driven CIAM teams.
Ideal For
-
Enterprises standardized on Microsoft and Azure
-
IT-led identity programs
-
Organizations extending internal IAM to external users
Trade-Offs
-
CIAM UX limitations
-
Complex configuration for customer journeys
-
Less flexibility outside the Microsoft ecosystem
4. Amazon Cognito
Amazon Cognito is AWS’s native identity service for application authentication and authorization. It is frequently evaluated by teams building entirely within the AWS ecosystem.
Where Amazon Cognito Performs Well
-
Tight AWS integration: Works seamlessly with other AWS services.
-
Basic CIAM capabilities: User pools, federation, and token management.
-
Usage-based pricing: Attractive for simple, low-scale use cases.
CIAM Fit Analysis: Cognito is suitable for basic authentication needs but lacks many advanced CIAM features out of the box. As requirements grow—especially around UX, B2B identity, or adaptive security—teams often find themselves building significant custom logic on top of the service.
Ideal For
-
AWS-native applications
-
Lightweight consumer apps
-
Teams with strong AWS expertise
Trade-Offs
-
Limited CIAM depth and flexibility
-
Heavy developer customization required
-
Minimal enterprise support and governance tooling
5. Descope
Descope is a modern authentication platform focused on no-code and low-code identity workflows. It is commonly evaluated by teams looking to move fast without deep IAM expertise.
Where Descope Performs Well
-
Visual authentication flows: No-code tools for designing login journeys.
-
Modern passwordless options: Strong support for passkeys and magic links.
-
Fast onboarding: Quick setup for prototypes and MVPs.
CIAM Fit Analysis: Descope excels at speed and ease of use but is less suited for complex CIAM deployments. As organizations introduce multi-tenant B2B identity, compliance requirements, or advanced security policies, Descope’s abstraction can become limiting.
Ideal For
-
Startups and early-stage products
-
Teams prioritizing speed over depth
-
Simple consumer-facing apps
Trade-Offs
-
Limited enterprise governance features
-
Less flexibility for complex CIAM architectures
-
Not optimized for regulated environments
6. Clerk
Clerk is a developer-first authentication platform designed primarily for frontend-heavy SaaS applications. It is often favored by startups and product teams focused on fast UI integration.
Where Clerk Performs Well
-
Excellent frontend experience: Prebuilt UI components and SDKs.
-
Fast implementation: Minimal setup for common auth flows.
-
Modern developer tooling: Designed for contemporary web stacks.
CIAM Fit Analysis: Clerk is well-suited for early-stage and product-led teams but lacks depth for enterprise CIAM scenarios. As identity needs expand to include B2B tenants, compliance, or complex security policies, teams may outgrow the platform.
Ideal For
-
Startups and early SaaS products
-
Frontend-focused development teams
-
Simple authentication requirements
Trade-Offs
-
Limited enterprise CIAM capabilities
-
Weak B2B and partner identity support
-
Scaling constraints for large user bases
7. ForgeRock
ForgeRock is a long-standing identity platform focused on complex enterprise IAM and large-scale digital identity programs. It is often evaluated by organizations with sophisticated security requirements, legacy IAM investments, or national-scale identity initiatives.
Where ForgeRock Performs Well
-
Advanced IAM and CIAM capabilities: Strong support for authentication, authorization, identity governance, and orchestration across complex environments.
-
Highly customizable identity flows: Powerful scripting and policy engines for bespoke authentication and user journeys.
-
Deployment flexibility: Supports on-premises, private cloud, and hybrid architectures.
CIAM Fit Analysis: ForgeRock is capable of supporting large-scale CIAM deployments, but implementations are typically complex, resource-intensive, and slow to deliver. The platform is best suited for organizations with dedicated IAM teams and long project timelines.
Ideal For
-
Large enterprises with complex IAM requirements
-
Government and public-sector identity programs
-
Organizations with dedicated IAM engineering teams
Trade-Offs
-
High implementation and operational complexity
-
Long deployment and customization cycles
-
Significant ongoing maintenance and cost
Why people switch from FusionAuth to LoginRadius
While FusionAuth offers flexibility, we consistently see teams switch to LoginRadius as their CIAM requirements mature.
Fully managed from day one
FusionAuth requires teams to host, scale, and maintain their own infrastructure. That responsibility increases with traffic growth and regulatory demands.
LoginRadius is fully managed in the cloud, with built-in scalability, uptime guarantees, and zero operational maintenance.
Faster time to value
Getting started with FusionAuth begins with downloading and deploying your own instance.
With LoginRadius, teams can go live in minutes—no downloads, no servers, and no manual configuration required.
Enterprise-grade support included
FusionAuth’s free tier relies on community support, with SLAs available only on paid plans.
LoginRadius includes 24/7 expert support and SLAs with enterprise accounts, ensuring help is available when it matters most.
Easier onboarding and administration
FusionAuth’s UI can feel unfamiliar and complex for teams new to CIAM.
LoginRadius offers a modern, intuitive dashboard with guided setup, clear documentation, and a shorter learning curve for both developers and administrators.
FusionAuth vs LoginRadius: Feature comparison
| Capability | FusionAuth | LoginRadius |
|---|---|---|
| Deployment model | Self-hosted | Fully managed cloud |
| CIAM focus | General IAM | Purpose-built CIAM |
| Auto-scaling | Customer-managed | Built-in |
| MFA & passwordless | Available, manual setup | Native and adaptive |
| B2B / partner IAM | Custom implementation | Native support |
| Data residency | Customer-managed | Multiple regions |
| Compliance | Shared responsibility | SOC 2, ISO included |
| Support & SLAs | Paid tiers | Enterprise included |
Conclusion
FusionAuth remains a capable solution for teams that want maximum control over their identity infrastructure. But as CIAM requirements evolve, driven by scale, compliance, and user expectations, many organizations find that managing authentication systems internally slows them down.
Modern CIAM platforms must deliver security, reliability, and compliance as built-in capabilities, not ongoing engineering projects. That’s why more teams are shortlisting fully managed solutions when evaluating FusionAuth alternatives.
LoginRadius offers a compelling path forward for organizations that want enterprise-grade CIAM without the infrastructure overhead, making it easier to scale, secure, and support identity across consumer and B2B use cases.
Explore FusionAuth vs LoginRadius CIAM in detail or talk to our team about moving from FusionAuth to a fully managed identity platform.



