Microsoft Entra ID is a natural starting point for organizations already invested in the Microsoft ecosystem. It delivers strong workforce identity, tight Azure integration, and a familiar administrative model for IT teams. But when brands begin scaling consumer identity (CIAM) or B2B/partner-facing experiences, they quickly discover gaps that slow down product velocity, limit UX control, and complicate modern authentication strategies.
A recurring theme we hear from engineering, product, and CX teams is that Entra ID’s workflows feel Azure-centric, not consumer-centric. Passwordless and passkey support is tied to Azure user flows and policies. Branding is limited to predefined templates. Social providers are supported, but integration requires navigating Azure’s configuration sprawl. Even small experimentation—like changing a signup field, updating a progressive profile step, or testing a new authenticator—often requires policy edits, approvals, and handoffs between product and IT.
The frustration expressed in public feedback mirrors what we see in migrations:
-
“Incomplete product with frustrating user and admin experiences”
-
“SMB nightmare—too complex for small teams”
-
“It breaks often, and support feels slow”
-
“Hard-to-debug Azure AD dependencies”
These experiences don’t invalidate Entra ID as a workforce IAM leader, but they highlight why teams seeking consumer-grade identity often evaluate alternatives built for product-led teams, rapid iteration, and flexible UX.
In this guide, we break down the evaluation criteria for selecting a CIAM platform, explore the top Entra ID alternatives, and detail why so many brands ultimately migrate to LoginRadius.
Evaluation Criteria: What Makes a Great CIAM Platform
Choosing a CIAM platform requires a different mindset from selecting workforce IAM. CIAM must balance security, customer experience, scale, and developer velocity, often across multiple digital channels. Below are the core dimensions modern teams evaluate.
1. Use Case Fit: CIAM vs Workforce IAM
Workforce IAM tools like Entra ID excel at:
-
Managing employees and contractors
-
Enforcing corporate security policies
-
Integrating with Microsoft apps
But CIAM requires:
-
Durable, portable identities across consumer apps
-
High-volume sign-in flows (millions of MAUs)
-
Tolerant UX (minimal friction, no enterprise constraints)
-
Flexible social login and passwordless authentication
-
Multiple brands, environments, and apps under one identity fabric
Teams building B2B SaaS also need multi-tenant org management, delegated admin, and partner directory integrations, features workforce IAM platforms rarely optimize for.
2. Security & User Experience
CIAM security must support enterprise-grade protection while delivering low-friction UX:
-
Passkeys / WebAuthn
-
One-tap passwordless options
-
Adaptive and risk-based authentication
-
Fraud detection and bot mitigation
-
Fine-grained MFA enrollment and fallback logic
-
Configurable recovery flows
In Entra ID, many of these capabilities exist but are tightly coupled to Azure policies, making UX iterations slow and complex for product teams.
3. Architecture & Scalability
Modern CIAM must operate in high-volume, latency-sensitive environments: eCommerce, media streaming, consumer apps, municipal portals, and B2B SaaS tenants onboarding thousands of users.
Criteria include:
-
Global availability and multi-region hosting
-
Multi-tenant B2B/partner org management
-
Event-driven extensibility and webhook performance
-
Zero-downtime migration and deployment
-
SLAs beyond Microsoft’s generalized Azure availability
Entra ID’s architecture is robust for workforce IAM but becomes rigid when consumer identity requires loosely coupled microflows, custom orchestration, and fast rollout cycles.
4. Data Residency & Compliance
Customer identity must meet jurisdictional, contractual, and sector-specific requirements:
-
Region-of-choice hosting
-
Regional tenancy isolation
-
Ability to migrate between regions
-
Certifications (ISO, SOC, GDPR, etc.)
-
Fine-grained consent and privacy management
In Entra ID, residency is tied to your chosen Azure geography, and shifting later is operationally challenging. For global brands or those entering new markets, this becomes a long-term constraint.
5. Developer Experience
CIAM success depends on developer velocity and clarity:
-
API-first architecture
-
Clean SDKs in major languages
-
Clear migration tooling
-
Sandbox environments
-
Orchestration to test new flows without policy sprawl
-
Event hooks and extensibility
Entra ID’s developer path often requires juggling Azure AD B2C policies, app registrations, identity providers, and multiple layers of configuration, slowing down iteration.
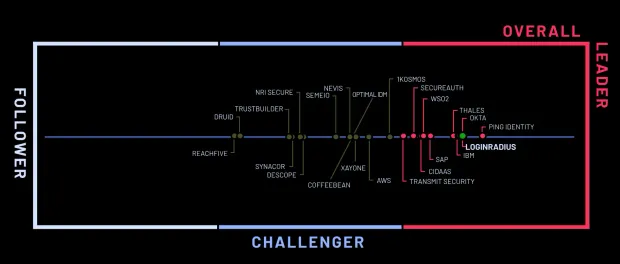
Top 7 Microsoft Entra ID Alternatives to Consider in 2026
Below are the leading CIAM alternatives based on feature completeness, implementation agility, security posture, and developer experience.
1. LoginRadius
LoginRadius is a pure CIAM platform designed specifically for high-volume B2C, government, and B2B SaaS identity, not adapted from workforce IAM like Microsoft Entra ID. Its foundation prioritizes consumer-scale traffic, rapid experimentation, deep UX control, and flexible cloud deployment models across global regions.
Where LoginRadius Works Especially Well
-
CIAM-native architecture: Multi-region cloud hosting, high-availability SLAs, geo-isolated tenancy options, and built-in multi-tenant organization support deliver the scalability consumer and B2B SaaS environments require.
-
Rapid deployment: Teams integrate authentication, MFA, social login, progressive profiling, passkeys, and branded pages without relying on custom policies or professional services.
-
Broad authentication coverage: Passwords, OTPs, WebAuthn passkeys, one-tap passwordless flows, social login, adaptive MFA, and enterprise federation—all unified under consistent APIs.
-
Modern security stack: Bot detection, anomaly scoring, breached password intelligence, IP velocity checks, and platform-level DDoS protection are native capabilities—not add-ons or separate product lines.
-
Low-/no-code orchestration: Journey builders, hosted templates, conditional workflows, and theming let product and CX teams adjust identity flows without engineering backlog.
Ideal For
-
Retail, media, fintech, and gaming needing elastic global scale
-
B2B SaaS platforms requiring multi-tenant identity with delegated admin
-
Government and public sector requiring strict region-of-choice residency
-
Fast-moving teams that iterate identity flows weekly
2. Auth0 (Okta Customer Identity Cloud)
Auth0 is one of the most extensible developer-oriented CIAM platforms on the market. Teams choose it when they need deep programmability and a large integration ecosystem. It remains a strong option for SaaS companies that want to script authentication logic through code.
Where Auth0 Performs Well
-
Developer-first flexibility: Rules, Actions, hooks, pipelines, and SDKs across many languages give engineers granular control over claims, tokens, flows, and side effects.
-
Large marketplace ecosystem: Offering plug-ins for analytics, fraud detection, marketing systems, CMS tools, enterprise SAML providers, and more.
-
Strong fit for B2B SaaS: Supports SSO, SAML, OIDC, RBAC, and tenant-level controls that align with enterprise onboarding requirements.
CIAM Fit Analysis: Auth0 excels when developers want maximum extensibility. However, teams scaling to tens of millions of users often encounter rate limits, expanding configuration overhead, or rising costs, especially when stitching together custom user flows.
Ideal For
-
Early-stage to mid-market SaaS companies
-
Teams with strong engineering bandwidth
-
Products dependent on third-party integrations
Trade-Offs
-
Pricing climbs rapidly with MAUs, extensibility usage, or multi-tenant workloads
-
Rate limits impact very high-volume B2C traffic
-
Some CIAM capabilities (e.g., attribute workflows, profiling) require custom code
3. Amazon Cognito
Cognito is best suited for teams deeply invested in AWS. It fits scenarios where identity is one component of a highly integrated AWS backend.
Where Cognito Performs Well
-
AWS-native integration: Seamless alignment with Lambda, API Gateway, CloudFront, DynamoDB, and IAM roles simplifies cloud-native architectures.
-
Cost-efficient for early scale: For early-stage applications and internal tools, Cognito can appear cost-effective relative to other hosted CIAM platforms.
-
Serverless event extensibility: Pre-auth, post-auth, and token lifecycle triggers provide hooks for customized logic using Lambda.
CIAM Fit Analysis: Cognito works best when development teams want to build identity flows themselves. However, consumer-facing brands often outgrow its limited UX customization, multi-tenant support gaps, and manual social login setup.
Ideal For
-
AWS-first engineering teams
-
Developer-led products willing to custom-build UX and flows
-
Internal apps or low-volume identity workloads
Trade-Offs
-
Very limited UI/UX branding
-
Social login configuration is manual and fragmented
-
Passwordless, progressive profiling, and orchestration require custom engineering
-
Large-scale CIAM deployments often hit maintenance and complexity issues
4. ForgeRock
ForgeRock remains a preferred choice for highly regulated enterprise environments undergoing identity modernization.
Where ForgeRock Performs Well
-
Enterprise identity depth: Strong policy engines, large-scale directories, hybrid environments, and legacy federation modernization.
-
Flexible deployment models: On-premises, cloud, and hybrid options meet strict regulatory or infrastructure mandates.
-
High configurability: Suitable for orgs whose identity flows must closely mirror complex internal systems.
CIAM Fit Analysis: ForgeRock can deliver CIAM, but its operational footprint, implementation cycles, and ongoing maintenance requirements are considerably heavier than modern cloud-native CIAM platforms. It is often too slow-moving for consumer-facing digital teams.
Ideal For
-
Regulated industries (finance, healthcare, government)
-
Organizations maintaining significant on-prem legacy systems
-
Enterprises needing custom IAM governance layers
Trade-Offs
-
Long implementation timelines
-
Requires specialized expertise or SI partners
-
Not optimized for rapid, iterative CIAM UX changes
5. Ping Identity
Ping is a federation-forward identity suite suited for workforce and hybrid enterprise use cases. Companies choose Ping when they need strong enterprise SSO and identity bridging for legacy or regulated systems.
Where Ping Performs Well
-
Federation maturity: Robust SAML, OAuth, OIDC, and enterprise SSO capabilities across complex infrastructures.
-
Hybrid readiness: Supports blend of cloud, on-prem, and legacy systems which large enterprises depend on.
-
Policy flexibility: Capable of handling intricate governance, access, and authentication logic.
CIAM Fit Analysis: Ping delivers strong enterprise identity, but CIAM teams frequently report the need to bolt on third-party UX layers, threat tools, or custom logic to support consumer onboarding flows—resulting in higher cost and engineering overhead.
Ideal For
-
Enterprises with significant hybrid/on-prem identity systems
-
Organizations prioritizing federation consistency over modern UX
-
Teams with IAM engineers capable of managing Ping’s complexity
Trade-Offs
-
Lacks native consumer-facing UX and orchestration
-
Heavier professional services involvement
-
Slow to iterate compared to cloud-native CIAM vendors
6. WorkOS
WorkOS is not a traditional CIAM platform. It is purpose-built to help B2B SaaS companies offer enterprise SSO and directory integrations without complex engineering.
Where WorkOS Performs Well
-
Turnkey B2B enterprise onboarding: SAML, OIDC, SCIM, directory sync, and access logs offered as ready-to-integrate services.
-
Fast implementation: Developer-friendly APIs and clear documentation help teams ship enterprise SSO in days.
-
Strong admin experience: The WorkOS dashboard gives tenants and admins clear visibility into connections, syncs, and provisioning.
CIAM Fit Analysis: WorkOS solves a narrow but important identity problem: B2B enterprise SSO. It’s not intended for consumer identity workflows, high-scale authentication, social login, passkeys, or journey orchestration.
Ideal For
-
SaaS products selling into enterprise accounts
-
Teams needing to offload SAML and SCIM work
-
Companies not needing full CIAM features
Trade-Offs
-
No CIAM journey builder, progressive profiling, or customer MFA flows
-
No consumer-grade UX tools
-
Not suitable as a complete identity layer
7. Keycloak
Keycloak is an open-source identity platform offering complete control for engineering teams willing to own CIAM infrastructure.
Where Keycloak Performs Well
-
Full autonomy: Teams can customize, self-host, and modify authentication logic at the deepest levels.
-
Cost flexibility: No per-MAU pricing, making it attractive for companies with large user populations and strong internal DevOps capabilities.
-
Extensibility: Open-source plug-ins and community modules allow for bespoke identity workflows.
CIAM Fit Analysis: Keycloak gives maximum control but requires significant engineering investment, especially for scaling, failover, patching, migration, and building modern UX layers. For teams wanting rapid CIAM iteration, this overhead becomes a long-term cost center.
Ideal For
-
Engineering teams that prefer full self-hosting
-
Organizations with strict data-control mandates
-
Companies with DevOps maturity and 24/7 uptime ownership
Trade-Offs
-
High operational burden
-
Upgrades and HA/DR require dedicated staff
-
Native CIAM UX is limited; teams must build their own interfaces
Why People Switch From Microsoft Entra ID to LoginRadius
Below are the most common reasons organizations tell us they explore migrating from Microsoft Entra ID (Azure AD B2C) to LoginRadius:
1. Difficulty Delivering Consumer-Grade UX and Branding
A consistent theme from product and CX teams is that Entra ID’s templated pages and Microsoft-patterned UI constrain their brand expression. Even when companies attempt deeper customization through custom policies, the process is tedious and brittle. Because Entra ID was engineered with enterprise workforce identity in mind, its UX layer prioritizes security uniformity, not the carefully crafted signup and login experiences that consumer applications require.
LoginRadius offers fully customizable hosted pages, headless authentication options, and no-code theming. Teams can tailor flows to precise brand guidelines and experiment with design changes without relying on IT-managed policy updates.
2. Slow, Policy-Heavy Iteration Cycles
Entra ID’s reliance on user flows, custom policies, and Azure resource dependencies often leads to slow turnaround times for even minor adjustments. Many teams describe “policy paralysis,” where modifying authentication journeys becomes a risk because debugging is complex, dependencies are unclear, and updates can inadvertently break downstream systems.
By contrast, LoginRadius equips teams with versatile orchestration, drag-and-drop journey editors, and clean API-first controls. This enables rapid experimentation—adding fields, adjusting MFA logic, or introducing progressive profiling—without running every change through Azure governance processes.
3. Azure-Centric Passwordless and Social Login That Doesn’t Fit Consumer Apps
While Entra ID supports passkeys, passwordless, and social providers, these capabilities must be configured through Azure user flows and app registrations. Developers frequently report friction when trying to align these flows with consumer expectations—particularly for mobile-first onboarding, multi-brand applications, or regionally specific providers.
LoginRadius centralizes passkeys, passwordless login, OTP, and social providers in unified CIAM-native flows. This simplifies both implementation and ongoing optimization, especially for brands operating across multiple digital properties.
4. Overhead Connecting Identity to Product, Not Just IT
Entra ID workflows are optimized for IT administrators. For many companies, this means product managers, growth teams, and marketing teams cannot make identity changes themselves. Every adjustment becomes an IT ticket, which slows down product innovation.
LoginRadius is built so product and CX teams can participate directly in shaping identity journeys. Its consoles, no-code builders, and extensibility patterns give technical and non-technical teams shared control without compromising security.
5. Rigid Data Residency and Region Constraints
Several organizations migrating from Entra ID cite region lock-in as a major operational limitation. Because an Azure AD B2C tenant’s region is fixed at creation, expanding into new markets, particularly those with strict data localization requirements, often requires spinning up entirely new directories or executing complex migration projects.
LoginRadius offers contractual region-of-choice hosting across multiple global data centers, along with cleaner migration paths. This is important for companies entering new geographies or unifying customer identities across brands and markets.
6. Engineering Burden and Troubleshooting Complexity
Your uploaded unhappiness data highlights patterns that we also hear during migrations: confusing error messages, unclear Azure AD dependencies, unreliable user flows, and difficulty identifying root causes when something breaks. Teams often mention spending disproportionate time navigating policy debugging rather than building product features.
LoginRadius reduces this burden through predictable APIs, transparent logs, consistent behavior across environments, and support teams that specialize specifically in CIAM—not the full breadth of Azure services.
7. Need for a CIAM Platform, Not a Workforce IAM Tool Repurposed
The underlying reason teams ultimately shift is philosophical: Entra ID is architected for managing employees and contractors, whereas CIAM requires a different approach entirely—high-volume traffic, elastic scale, rich profiling, multi-brand flexibility, and UX experimentation.
LoginRadius is purpose-built for customer and partner identity. This manifests in everything from its identity model to its orchestration engine, from its multi-tenant B2B capabilities to its passkey-first design. Organizations looking to modernize digital identity without inheriting enterprise IAM complexity find that LoginRadius aligns more closely with their needs.
Comparison Table: Microsoft Entra ID vs LoginRadius
| CIAM Capability | LoginRadius | Microsoft Entra ID |
|---|---|---|
| Passkeys / WebAuthn | Native support, unified flows | Supported via Azure user flows; policy-heavy |
| Passwordless Options | Multiple: email, magic link, OTP, WebAuthn | Limited to Azure-configured methods |
| Branding & UI Control | Fully customizable | Template-bound, limited styling |
| Orchestration | Drag-and-drop workflow builder | Requires editing policies and flows |
| Social Login | One-click activation | Complex multi-step Azure configuration |
| Multi-Tenant B2B | Built-in org management | Requires custom engineering |
| Data Residency | Region-of-choice hosting | Tied to Azure region; hard to relocate |
| Developer Experience | API-first, clean SDKs | Azure-centric, steep learning curve |
| Migration Flexibility | Structured migration tooling | Region and policy constraints |
| Support Model | Developer-first support | Primarily IT-admin-oriented |
Conclusion and Next Steps
Microsoft Entra ID remains a strong component of the Microsoft ecosystem, especially for enterprises centralizing workforce identity. But when organizations need modern CIAM, scalable, customizable, consumer-first, and iterative, Entra ID often imposes friction that slows down growth and UX innovation.
The most common reasons teams look elsewhere include policy complexity, Azure-centric UX, limited branding, slow iteration processes, and rigid data residency constraints. These issues can be manageable at small scale but become painful as brands expand into new markets, multi-app ecosystems, or B2B SaaS environments.
Selecting the right CIAM platform requires weighing use case fit, security depth, architectural flexibility, compliance posture, and developer experience. LoginRadius consistently ranks among the top shortlisted candidates because our platform is purpose-built for customer identity and aligns cleanly with product, security, development, and CX requirements.
If you're evaluating Microsoft Entra ID alternatives, our team can help you:
-
Map your CIAM requirements
-
Review architectural options
-
Provide a personalized technical demo
-
Explore migration processes and timelines
Explore our documentation, or speak to our engineers about your identity roadmap. Together, we can design a customer identity foundation that supports long-term growth and digital innovation.



