Introduction
Access problems rarely announce themselves as security incidents. They show up as unanswered questions.
Why does this user still have access? Who approved it? Was this role ever meant to include that permission? This is where identity governance and administration stop being an abstract concept and become operationally uncomfortable.
Most organizations already use roles. RBAC exists in some form across applications, directories, and cloud platforms. But inside identity governance and administration, roles aren’t just a convenience; they’re the unit of accountability. They’re what access reviews rely on. They’re what auditors expect to see. And they’re often the weakest link in the entire governance chain.
The problem isn’t that RBAC is outdated. The problem is that RBAC is rarely governed with the same rigor as the identities it’s meant to control.
As organizations scale, access patterns drift. Teams change. Projects overlap. Temporary access stretches longer than intended. Over time, what began as a clean role model turns into a collection of exceptions no one feels confident removing.
This is exactly where identity access governance starts to erode, not because the tools are missing, but because the structure underneath them can no longer explain itself.
Modern IGA security depends on more than enforcing least privilege at a single moment in time. It depends on being able to prove repeatedly that access is intentional, reviewed, and still justified. And that proof almost always flows through roles.
In this blog, we’ll look at what identity governance and administration really expect from RBAC, where roles tend to fail inside IGA programs, and how teams can design RBAC models that survive access reviews, lifecycle changes, and real-world complexity without turning governance into an administrative burden.
What Is Identity Governance and Administration (IGA)?
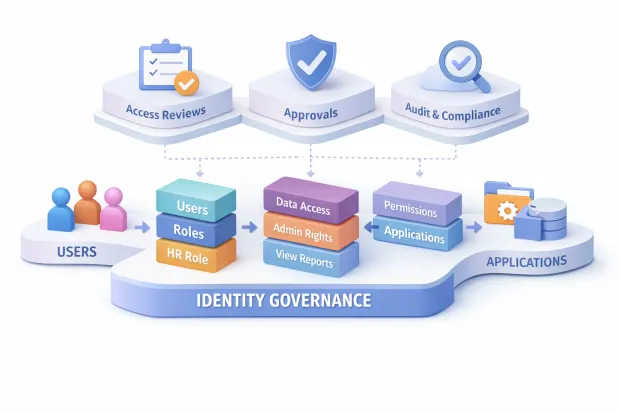
Identity Governance and Administration (IGA) is the discipline responsible for controlling, reviewing, and proving who has access to what and why. It sits at the intersection of identity management, security, and compliance, focusing less on how users log in and more on whether their access still makes sense over time.
At its core, identity governance and administration answers a few uncomfortable but necessary questions: Who approved this access? Is it still required for this role or responsibility? And can the organization demonstrate that oversight clearly to auditors or regulators?
These questions become harder to answer as organizations grow, adopt more SaaS tools, and allow access to change dynamically across teams and projects.
Unlike authentication or authorization systems that make access decisions in real time, IGA operates across the identity lifecycle. It governs onboarding, role changes, temporary access, and offboarding, ensuring access evolves alongside the user, not independently of them.
This lifecycle focus is what makes identity access governance essential in environments where access decisions accumulate quietly and risk increases without obvious signals.
What Is IGA Security and Why RBAC Sits at the Center of It
IGA security is not primarily about blocking attackers at the perimeter. It is about preventing excessive, unjustified, or forgotten access from becoming a long-term risk. Most governance failures don’t come from external threats; they come from internal access that was once valid and never revisited.
This is where Role-Based Access Control becomes foundational. RBAC provides a structure that allows access to be grouped, reviewed, and reasoned about at scale. Without roles, governance teams are forced to evaluate access at the entitlement level, an approach that quickly becomes unmanageable and opaque.
With roles, access can be reviewed in units that reflect business responsibility rather than technical configuration.
RBAC also enables accountability. When access is tied to roles, approvals and reviews can be traced back to intent. That traceability is what allows IGA security programs to move beyond “we think access is correct” to “we can prove it is.”
In practice, this is why most IGA frameworks, tools, and audit processes assume the presence of roles even when they also support policies, attributes, or contextual controls.
Why RBAC Is Everywhere in Identity Governance and Administration
RBAC persists in identity governance and administration because it creates a shared language between technical systems and business oversight.
Governance depends on human decision-making managers, application owners, auditors, and roles are the most understandable way to express access without forcing those stakeholders to interpret raw permissions.
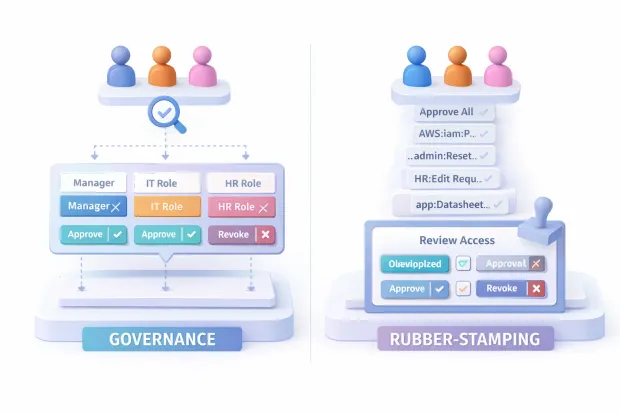
In IGA programs, roles serve as compression layers. They reduce thousands of granular entitlements into manageable access bundles that can be approved, reviewed, and revoked with confidence. This is especially important during access reviews, where time pressure and cognitive overload often lead to rubber-stamped approvals if access is not presented clearly.
Even as organizations adopt more advanced controls, RBAC remains the anchor that keeps governance workflows usable. Identity governance and administration solutions rely on roles to structure access requests, automate approvals, and generate audit evidence. Without RBAC, governance processes either slow down dramatically or lose reliability altogether.
Where RBAC Starts Breaking Inside IGA Programs
RBAC usually breaks not because it is conceptually flawed, but because it is stretched beyond what it was designed to represent. As organizations evolve, roles often become static while access needs remain fluid. Teams collaborate across functions, projects introduce temporary privileges, and exceptions accumulate faster than roles are revisited.
Inside IGA programs, this mismatch shows up as role sprawl, unclear ownership, and access reviews that no longer reflect reality. Roles begin to include permissions added “just this once,” and those permissions rarely get removed. Over time, the role stops representing a job function and starts representing historical convenience.
This breakdown is especially damaging in governance contexts. When roles lose meaning, access reviews lose effectiveness, and identity access governance turns procedural rather than corrective. Reviewers approve what they no longer trust enough to challenge, and security teams struggle to enforce least privilege without disrupting operations.
The issue isn’t that RBAC can’t scale inside identity governance and administration. It’s that RBAC must be governed with the same discipline as identities themselves. Without lifecycle management, ownership, and regular scrutiny, roles quietly become the weakest link in an otherwise well-designed IGA program.
RBAC and Access Reviews: The Difference Between Governance and Rubber-Stamping
Access reviews are where identity governance either proves its value or quietly collapses. On paper, they exist to validate access and enforce least privilege. In practice, their effectiveness depends almost entirely on how access is presented to reviewers. This is where RBAC becomes the deciding factor between meaningful governance and routine approval.
When access is grouped through well-defined roles, reviews become about intent. Reviewers can evaluate whether a role still aligns with a user’s responsibilities instead of deciphering individual permissions they don’t recognize. That shift matters. It reduces cognitive overload and forces accountability back to business context rather than technical detail.
Without RBAC or with poorly governed roles access reviews degrade into volume exercises. Reviewers approve access not because it is correct, but because it is incomprehensible or time-consuming to challenge.
At that point, the review exists only to satisfy process requirements, not to correct risk. RBAC doesn’t just support access reviews; it determines whether they function as a control or a formality.
The RBAC Components That Actually Matter in IGA
In identity governance and administration, RBAC succeeds or fails based on a small set of components that are often overlooked. The most important of these is role ownership. Roles without clear ownership quickly lose relevance, because no one is accountable for keeping them aligned with reality.
Equally important is the distinction between business intent and technical execution. Roles should describe responsibility first and permissions second. When roles are built purely from entitlement groupings, they become opaque to reviewers and difficult to govern over time. The role lifecycle also matters more than initial design. Roles must be reviewed, adjusted, and sometimes retired as organizations evolve.
What matters less than teams often assume is role granularity perfection. Identity governance does not require roles to be flawless; it requires them to be understandable, reviewable, and defensible. When RBAC is treated as a living structure rather than a static configuration, it becomes a stabilizing force inside IGA rather than a maintenance burden.
IGA Implementation: Making RBAC Survive Joiners, Movers, and Leavers
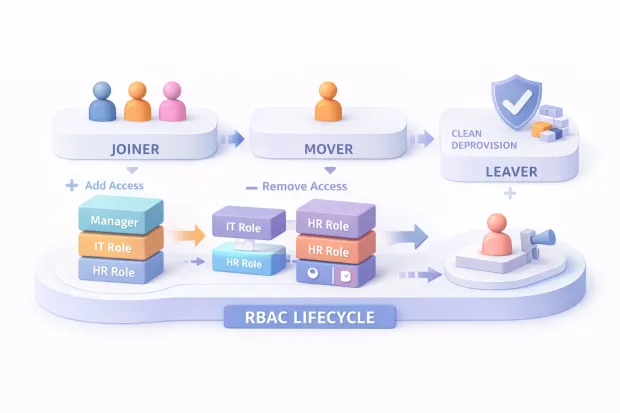
IGA implementation exposes RBAC to its most demanding conditions. Access changes constantly, and every lifecycle event tests whether roles reflect reality or merely document history. Joiners, movers, and leavers are not edge cases in governance; they are the primary workload.
For new users, RBAC determines whether onboarding is controlled or chaotic. Roles must provide enough access to be productive without embedding long-term risk. For role changes, RBAC must support subtraction as reliably as it supports addition. Many governance failures stem from access that accumulates instead of transitioning cleanly when responsibilities change.
Offboarding is where weak RBAC models become most visible. If roles are unclear or inconsistently assigned, deprovisioning becomes uncertain and verification becomes difficult. A resilient IGA implementation treats RBAC as the backbone of lifecycle enforcement, ensuring access changes are predictable, traceable, and reversible at every stage.
Role Mining and Cleanup: Fixing RBAC Without Rebuilding Everything
Role mining exists because RBAC models rarely age gracefully. Over time, access patterns drift away from original assumptions, and roles absorb exceptions that were never meant to be permanent. The goal of role mining is not to automate role creation blindly, but to reveal how access is actually being used.
In mature IGA programs, role mining functions as a diagnostic tool. It highlights inconsistencies, over-privileged patterns, and roles that no longer represent a coherent responsibility. This insight allows teams to refine roles incrementally rather than replace them wholesale.
Cleanup works best when it is governed, not rushed. Removing access is more sensitive than granting it, and RBAC cleanup must balance security improvements with operational stability.
When role mining is paired with ownership and review workflows, RBAC can be corrected gradually without disrupting users or governance processes.
Choosing Identity Governance and Administration Solutions: What to Look for in RBAC Support
RBAC support in identity governance and administration solutions is less about feature checklists and more about how roles are treated across governance workflows. Effective platforms treat roles as first-class governance objects, not static containers.
This means roles can be reviewed, certified, modified, and retired with the same visibility as users and entitlements. Strong solutions also integrate RBAC into access requests, approvals, and lifecycle automation, ensuring roles are consistently enforced rather than bypassed through exceptions.
Equally important is audit visibility. Governance platforms should make it easy to explain who has access, through which role, and why that role exists. When RBAC is deeply embedded into governance workflows, identity governance and administration solutions shift from managing access to managing trust.
Common Failure Patterns That Stall IGA Programs
IGA programs rarely fail because of missing controls. They fail because those controls lose credibility. RBAC is often at the center of this erosion. Roles are created quickly, rarely revisited, and slowly disconnected from how access is actually used.
Another common pattern is treating governance as a security-only responsibility. When business ownership is absent, roles stop reflecting operational reality, and reviews become procedural. Exceptions accumulate, manual approvals become the norm, and governance workflows exist largely to document decisions rather than improve them.
Perhaps the most damaging failure is assuming RBAC is “done.” Identity governance and administration is continuous by nature. When RBAC is not maintained with the same discipline as identities themselves, governance stalls not dramatically, but quietly until access reviews lose meaning and risk becomes invisible.
Conclusion
Identity governance and administration isn’t about perfect access models. It’s about defensible ones.
At scale, governance only works when access decisions can be understood, reviewed, and corrected without guesswork. That’s why RBAC continues to sit at the center of identity governance and administration, even as policies, attributes, and automation evolve around it.
Roles give structure to access. They give reviewers something to reason about. And they give governance teams a way to draw clear lines between what was intended and what simply accumulated over time.
But RBAC only supports IGA security when roles themselves are treated as governed objects not static artifacts created once and forgotten. Roles need owners. They need lifecycle controls. They need regular scrutiny, especially when they carry the permissions that auditors care about most.
What we see repeatedly is this: organizations don’t fail at IGA because they lack tooling. They fail because roles lose meaning. When roles stop reflecting how access is actually used, access reviews become procedural, exceptions pile up, and identity access governance turns into a compliance exercise rather than a security control.
Strong identity governance and administration solutions don’t eliminate RBAC. They make it visible, reviewable, and correctable across joiners, movers, leavers, and everything in between.
If there’s one practical takeaway, it’s this: don’t start by redesigning every role. Start by examining the ones that show up most often in access reviews and exceptions. That’s where governance pressure is already telling you what needs attention.
RBAC doesn’t have to be perfect to work in IGA. It just has to remain explainable.
And in identity governance, that’s the difference between control and chaos. Book a Demo today.
FAQs
Q: What is identity governance and administration (IGA)?
A: Identity governance and administration is the practice of managing, reviewing, and auditing user access across systems to ensure it is appropriate, approved, and compliant throughout the identity lifecycle.
Q: Why is RBAC important in identity governance and administration?
A: RBAC provides structure to access by grouping permissions into roles, making access reviews, approvals, and audits understandable and scalable within identity governance and administration programs.
Q: What is IGA security focused on?
A: IGA security focuses on preventing excessive or outdated access, ensuring least privilege, and providing provable oversight over who has access, why it was granted, and whether it still makes sense.
Q: Why do RBAC-based IGA programs fail over time?
A: RBAC fails in IGA when roles are not maintained, owned, or reviewed regularly, causing access drift and turning governance processes into routine approvals rather than meaningful controls.



