Introduction
The way we authenticate users is changing faster than ever. With attackers bypassing passwords, intercepting OTPs, and exploiting predictable login flows, the old model of “one password + one code” is no longer enough.
At the same time, customers expect login experiences to be instant, seamless, and invisible. Security teams need stronger protection, while growth and product teams need frictionless UX. This tension has pushed MFA into a new era, one where authentication must be smart, risk-aware, and adaptive rather than static and repetitive. That’s where Adaptive Multi-Factor Authentication (Adaptive MFA) comes in.
Traditional MFA still protects millions of accounts, but it wasn’t built for modern threat patterns, large-scale CIAM environments, or user journeys where every extra second impacts conversions. Adaptive MFA, on the other hand, brings intelligence, personalization, and real-time risk scoring into the authentication process, making it both more secure and more user-friendly.
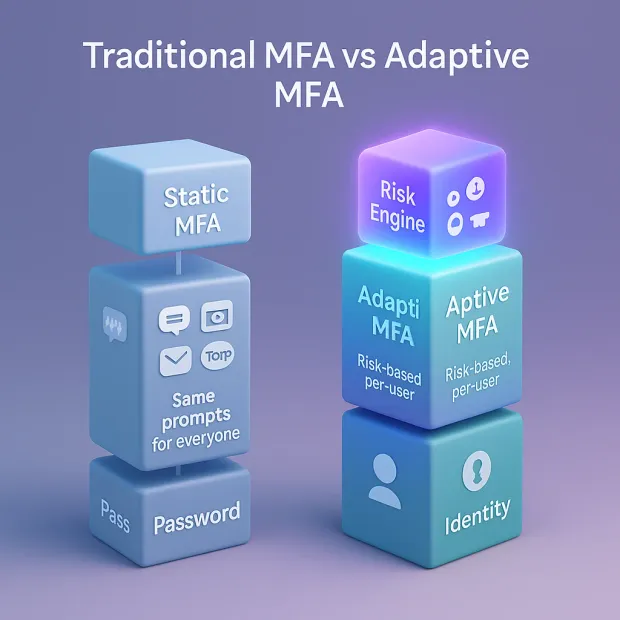
When teams compare adaptive MFA vs MFA, they’re really comparing two different security philosophies: static step-up for everyone versus risk-based decisioning that adapts per login attempt. This shift is powered by adaptive authentication, which evaluates context first and challenges only when signals indicate real risk.
In this blog, we’ll break down how both approaches work, compare their strengths and weaknesses, and help you determine which MFA model truly fits your product, your customers, and your security goals.
What Is Traditional MFA?
Traditional Multi-Factor Authentication (MFA) is the classic model most people know: you enter your password… then you enter a one-time code… and only then do you get in. It adds a second layer of security beyond the password, but it applies this same step to everyone every time. No intelligence. No context. No awareness of risk.
At its core, traditional MFA relies on combining:
-
Something you know → a password
-
Something you have → OTP, authenticator app, SMS code, email link
-
Something you are → biometrics (in some cases)
Traditional MFA supports multiple types of mfa, depending on the second factor used. In practice, most teams standardize a few multi factor authentication methods that balance usability, cost, and attack resistance across user segments.
And while this approach has helped reduce password-related breaches, it comes with friction and predictable patterns that attackers have learned to exploit.
How Traditional MFA Works?
The flow is fixed and static:
-
User enters a username and password
-
System sends a second factor (SMS OTP, authenticator app code, email OTP, push notification)
-
User enters/approves the second factor
-
Access granted
Whether you’re logging in from your personal laptop at home or a suspicious device in another country, traditional MFA still forces the exact same verification steps.
Why Traditional MFA Became So Popular
Traditional MFA exploded in adoption because:
-
It was easy to understand
-
Easy to roll out
-
Familiar to users
-
Supported by all major apps and platforms
-
Stronger than passwords alone
For years, this was the go-to method for boosting account security across banks, SaaS platforms, shopping apps, and employee portals.
These are common mfa methods used across consumer apps and enterprise platforms, and they also represent the baseline most mfa solutions offer out of the box.
Real-World Examples of Traditional MFA
Example 1: SMS OTP for Online Banking
You log into your banking app → it sends a 6-digit SMS code → you enter it → done. This is traditional MFA at its simplest. Effective, but vulnerable to SIM-swap attacks.
Example 2: Email OTP for eCommerce Checkout
An online shop sends you a verification code to confirm a purchase. Fast but easy for attackers to intercept if your email is compromised.
Example 3: TOTP Code on Google Authenticator
You open an authenticator app → copy the 6-digit rotating code → paste it to log in. More secure than SMS, but still a static step applied to everyone equally.
Limitations of Traditional MFA
While traditional MFA adds a crucial layer of protection, it has clear drawbacks:
-
Same experience for all users Whether the user is high-risk or low-risk, the system can’t tell the difference.
-
Friction-heavy login flow OTP fatigue, app switching, and slow SMS delivery cause abandonment.
-
Vulnerable to modern attacks Attackers now bypass static MFA using:
-
Man-in-the-middle phishing kits
-
SIM-swaps
-
OTP interception
-
Real-time phishing proxies
-
-
No contextual intelligence The system does not check device trust, behavior patterns, IP reputation, or anomalies.
This is why static MFA is struggling to keep up in today’s threat landscape—leading organizations to adopt more intelligent and adaptive models.
Also read: Explore the key benefits of MFA
What Is Adaptive MFA?
Traditional MFA treats every login the same. Adaptive Multi-Factor Authentication (Adaptive MFA) does the opposite; it adjusts authentication requirements based on how risky the login attempt appears.
Adaptive MFA is a modern form of adaptive multi factor authentication where authentication requirements change based on risk signals like device trust, location anomalies, IP reputation, and behavioral deviations. This is why the concept is frequently grouped under adaptive authentication, because the system “learns” what normal looks like and responds dynamically.
Instead of forcing every user to enter an OTP, Adaptive MFA analyzes context, user behavior, device trust, and real-time risk before deciding whether to challenge the user or let them in seamlessly.
Think of it as an authentication system that doesn’t just ask, “Do you have the right password?” It also asks, “Does this login look normal for this user?”
It’s intelligent, flexible, and built for modern CIAM platforms where friction can cost conversions and poor protection can lead to account takeovers.
How Adaptive MFA Works?
Adaptive MFA takes everything traditional MFA does and makes it smarter, faster, and more responsive. Instead of applying the same second factor to every login, Adaptive MFA evaluates risk signals in real time and adjusts the authentication process based on what it learns. Every login attempt becomes a mini security investigation happening in milliseconds.
It’s authentication that thinks before it challenges. And that’s exactly what modern CIAM environments need.
The Adaptive MFA Flow
Here’s how it works in practice:
Step 1: User Initiates Login
The user enters their credentials or begins a passwordless flow. Nothing unusual yet, just the start of a normal login attempt.
Step 2: Risk Engine Analyzes the Attempt
This is the heart of what is adaptive authentication: using context and threat signals to decide whether MFA is necessary, and if so, which factor is best for that moment.
This is where Adaptive MFA becomes powerful.
It evaluates signals such as:
-
Device fingerprint (Is this a trusted or new device?)
-
Location pattern (Is the user logging in from their usual region?)
-
IP reputation (Has this IP been flagged for abuse?)
-
Network trust (Public Wi-Fi, OR browser, VPN?)
-
Behavioral patterns (Is the user moving or typing differently?)
-
Login time consistency (Is this a usual login time?)
-
Threat intelligence feeds (Are bots involved?)
Each signal contributes to a risk score.
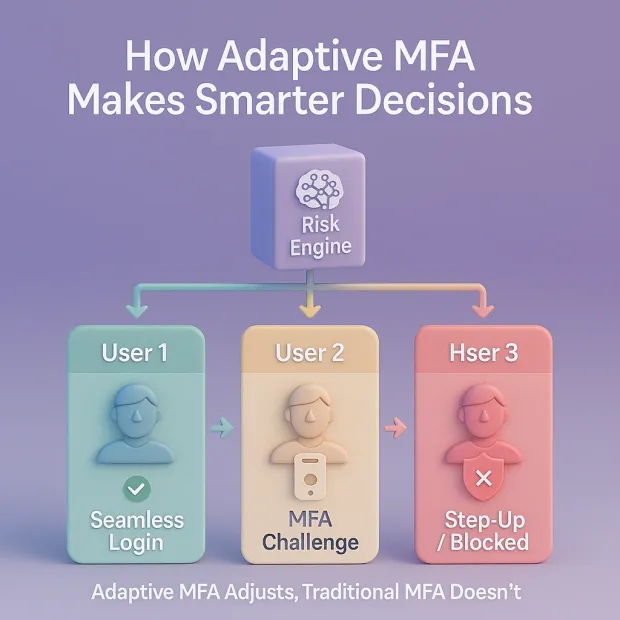
Step 3: System Assigns a Real-Time Risk Score
The authentication engine decides whether the login looks safe, suspicious, or outright malicious.
-
Low-risk → Fast, frictionless access
-
Medium-risk → Silent or passive checks
-
High-risk → Step-up authentication
-
Very high-risk → Deny the attempt
This is the opposite of traditional MFA, where everyone goes through the same steps regardless of risk.
Step 4: Adaptive MFA Responds Intelligently
The system adapts the authentication flow based on that risk score:
-
Seamless Login: If everything looks normal, the user gets in instantly no OTPs, no push delays.
-
Silent Checks: The system may perform extra background verification (like IP risk reevaluation).
-
Step-Up Authentication: When suspicious behavior is detected, the user must verify with TOTP, push, biometrics, or a security key.
-
Blocked Attempt: High-risk or malicious behavior is stopped before the login completes.
This provides security exactly when needed and stays invisible when not.
Real-World Examples of Adaptive MFA
Example 1: Logging In From Your Trusted Laptop at Home
You’ve logged in from this device 20 times in the past month.
Location matches your usual city. IP is clean.
Behavior is normal.
Adaptive MFA: “Low risk. No need for an OTP.”
You log in instantly, with no friction.
Example 2: Logging In From a New Device in a New Country
You’re in Singapore today, but you logged in from Canada two hours ago.
This looks like impossible travel.
IP reputation is medium risk.
Device unknown.
Adaptive MFA: “High risk. Trigger step-up authentication.”
The system requires biometric authentication or a security key.
Why Adaptive MFA Matters Today
Threats have shifted. Attackers now use real-time phishing kits, proxy tools, OTP bypass malware, and AI-driven attack automation. Traditional MFA cannot respond dynamically. Adaptive MFA can.
At the same time, customers are more impatient than ever. OTP delays, app switching, and friction lead to massive abandonment. Adaptive MFA solves this by reducing unnecessary steps for trusted users while increasing security controls only when real threats appear.
It delivers the perfect balance:
-
Stronger security
-
Less friction
-
Better conversions
-
Lower support load
Exactly what a modern CIAM platform needs.
Adaptive MFA vs Traditional MFA: Security Comparison
Security is where the difference between Adaptive MFA and Traditional MFA becomes impossible to ignore. While both offer protection beyond passwords, their ability to defend against modern attacks is vastly different. Traditional MFA adds a second step. Adaptive MFA adds intelligence.
Traditional MFA Security: Strong but Predictable
Traditional MFA blocks many basic attacks such as password spraying, simple credential theft, and low-effort breaches. But because the flow is static, attackers have learned how to exploit it.
Weaknesses include:
-
SMS OTP Vulnerabilities: SIM-swaps, SS7 attacks, OTP interception
-
Phishable Factors: Real-time phishing kits bypass OTPs easily
-
No Context Awareness: It can’t detect unusual devices or locations
-
Static Flow: Same challenge for every user, every time
-
Susceptible to AitM (Adversary-in-the-Middle) Attacks
Attackers don’t need to break MFA; they just need to trick it.
Adaptive MFA Security: Real-Time, Context-Aware Defense
Adaptive MFA evaluates context, behavior, and risk before it even decides which security method to use. This makes it significantly harder to manipulate.
Key advantages:
-
Phishing Resistance: Recognizes device-bound credentials & suspicious behavior
-
Risk Scoring: Blocks or challenges based on device, IP, location, and threat data
-
Bot Detection: Identifies automated attacks using velocity & behavior patterns
-
Continuous Monitoring: Doesn't trust a session forever—reevaluates risk
-
Dynamic Step-Up: Uses stronger factors only when the threat level rises
This means Adaptive MFA can detect and stop attacks before the user even sees a login screen.
Adaptive MFA vs Traditional MFA: User Experience Comparison
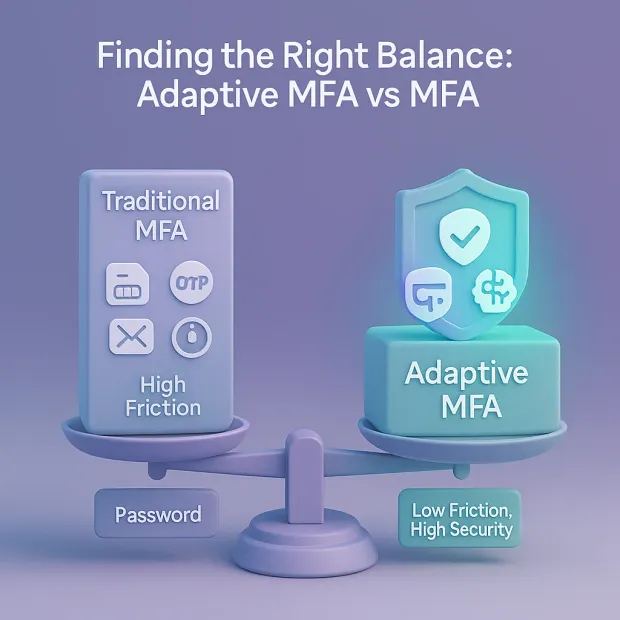
Security is critical but for customer-facing apps, user experience can make or break growth. This is exactly where Adaptive MFA creates a major advantage.
While Traditional MFA adds the same step for everyone, Adaptive MFA adjusts authentication based on trust, making the login journey smoother for legitimate users.
Traditional MFA UX: Necessary But Friction-Heavy
Traditional MFA forces all users into the same second step, even when the login attempt is completely safe. This leads to:
-
OTP fatigue Users get tired of entering 6-digit codes over and over.
-
Slow authentication SMS codes may delay or fail entirely.
-
High abandonment Many users drop off during signup or checkout if MFA feels tedious.
-
App switching Moving between apps (e.g., to Google Authenticator) adds resistance.
Traditional MFA protects accounts, but it often frustrates users especially in CIAM environments where millions of customers interact daily.
Adaptive MFA UX: Smooth, Personalized, and Intelligent
Adaptive MFA transforms the login flow into a user-friendly experience by challenging only when needed.
Here’s how it improves UX:
-
Seamless Logins for Trusted Users Known device + familiar location + normal behavior = no OTP required.
-
Silent, Background Verification Users don’t even notice security checks happening behind the scenes.
-
Step-Up Only When Risk Is High Reduces unnecessary friction by 60–80%.
-
Higher Conversion Rates & Fewer Drop-Offs Especially valuable for eCommerce, SaaS onboarding, and mobile apps.
-
Better Mobile Experience No app switching or copy-pasting codes for low-risk logins.
Adaptive MFA feels “invisible” to users when everything looks normal and “strict” when something seems risky. This balance builds trust without slowing people down.
Cost & Operational Comparison: Adaptive MFA vs Traditional MFA
Cost is one of the most overlooked but most decisive factors when choosing an authentication method. While both Adaptive MFA and Traditional MFA help secure accounts, their long-term operational impact is dramatically different.
Traditional MFA tends to look cheaper upfront, but it creates hidden costs over time. Adaptive MFA requires slightly more intelligence at the start, but it saves organizations money in the long run by reducing support needs, preventing fraud, and improving conversion.
Let’s break it down clearly.
Traditional MFA Costs: Lower Setup, Higher Operations
At first glance, Traditional MFA seems simple and cost-effective to implement. But because it challenges every user equally, it often increases operational and user-related expenses.
Where Traditional MFA Gets Expensive
-
SMS OTP Delivery Costs For large user bases, global SMS delivery becomes expensive fast, especially with international rates.
-
Support Tickets for OTP Failures Users frequently run into issues: “Didn’t receive the OTP,” “Authenticator app not working,” “Lost device.” These requests increase the support workload.
-
Friction → Lower Conversion Rates Every extra step in the login flow pushes users away—impacting revenue for eCommerce, SaaS, and consumer apps.
-
Higher Fraud Recovery Costs Static MFA is easier to bypass through real-time phishing or SIM-swaps, leading to expensive remediation.
Traditional MFA may start inexpensive, but for high-volume consumer environments, the operational costs quickly stack up.
Adaptive MFA Costs: Higher Intelligence, Lower Long-Term Spend
Adaptive MFA requires risk-based logic, device intelligence, and contextual analysis but this investment pays off.
Where Adaptive MFA Saves Money
-
Fewer OTPs = Lower SMS and Infrastructure Costs Because low-risk users skip step-up authentication, you send fewer OTPs, significantly cutting SMS delivery costs.
-
Massively Reduced Support Tickets No more constant OTP failures, app-sync issues, or “I didn’t get the code” problems.
-
Higher Conversion & Lower Drop-Offs Seamless login reduces friction, improves user experience, and keeps users from abandoning flows.
-
Better Fraud Prevention = Lower Remediation Costs Adaptive MFA blocks risky logins before they happen, reducing financial impact from account takeovers.
-
Scales Efficiently for CIAM Dynamic checks mean fewer manual interventions and reduced strain on backend systems.
Adaptive MFA is not just more secure it is more cost-efficient, especially for large-scale consumer identity platforms.
When Traditional MFA Is Enough
While Adaptive MFA is clearly the more advanced authentication method, Traditional MFA still has a place, especially for environments where simplicity matters more than dynamic intelligence. The key is understanding where predictable, fixed authentication steps are acceptable and where they’re not.
Traditional MFA works well in scenarios where risk is low, user volume is controlled, and friction is manageable.
Best Scenarios for Traditional MFA
1. Internal Workforce Applications
For small or mid-size teams logging into internal tools, traditional MFA is often sufficient. The user environment is familiar, controlled, and predictable. The friction created by OTP or authenticator apps is generally acceptable in an employee setting.
2. Low-Risk Applications
If an application doesn’t handle sensitive data and the impact of account compromise is low, static MFA can be a simple and effective security layer without requiring complex risk analysis.
3. Limited User Base or Small Apps
For startups, pilot projects, or tools with only a few dozen or few hundred users, the cost and complexity of deploying Adaptive MFA may not yet be necessary. Traditional MFA offers a quick and affordable security upgrade.
4. Compliance-Driven Environments
Some regulatory frameworks simply require MFA, not risk-based authentication. In such cases, traditional MFA meets the minimum compliance requirements without additional overhead.
5. Environments Where User Experience Is Not the Top Priority
Internal admin portals, controlled-access apps, or systems used by trained professionals can tolerate the friction of static MFA. If the user experience is less critical than access control, traditional MFA can be enough.
Traditional MFA Is Still Valuable, Just Not Everywhere
Traditional MFA remains meaningful for specific use cases, but it struggles in customer-facing, high-traffic, global environments where friction, SMS failures, and modern attack patterns create bigger issues. For those environments, Adaptive MFA offers a smarter, more scalable solution.
When Adaptive MFA Is the Better Choice
Adaptive MFA becomes the clear winner in any environment where security must be intelligent, and user experience must remain smooth. For modern CIAM—where millions of customers log in from different devices, regions, and networks adaptive authentication isn’t just an upgrade; it’s a necessity.
Here are the scenarios where Adaptive MFA delivers the greatest value.
1. High-Traffic Customer Applications (CIAM)
Consumer-facing platforms eCommerce, media, gaming, travel, streaming cannot afford friction. OTP delays or repeated MFA prompts directly impact revenue and user satisfaction.
Adaptive MFA ensures:
-
seamless login for trusted users
-
step up only when risk is detected
-
fewer drop-offs and authentication failures
Perfect for large user bases where UX and security need to coexist.
2. Apps Targeted by Modern Threats
If your application faces:
-
phishing campaigns
-
bot attacks
-
real-time MFA bypass tools
-
automated session hijacking
Then traditional MFA simply isn’t enough. Adaptive MFA’s risk scoring and contextual intelligence significantly reduce account takeover risks.
3. Global or Mobile-Heavy User Bases
Users log in from different devices, networks, and regions. Adaptive MFA shines by adjusting to each user's context:
-
Public Wi-Fi? → Stronger checks
-
Same home device? → Seamless login
-
New IP or country? → Step-up auth
-
Normal behavior? → Skip MFA
This flexibility is essential for global delivery.
4. Industries With Sensitive or Regulated Data
Industries that cannot afford compromised accounts:
-
Banking and fintech
-
Healthcare (PHI / HIPAA)
-
Government and public-sector apps
-
Education systems
-
SaaS platforms with admin access
Adaptive MFA offers the highest level of contextual protection with minimal disruption.
5. Businesses Prioritizing Conversion & Retention
Every additional login step affects:
-
sign-up completion
-
checkout success
-
returning user engagement
-
subscription renewals
Adaptive MFA reduces customer friction by removing unnecessary OTP flows for low-risk users while protecting businesses from fraud-related losses.
6. Organizations Moving Toward Zero Trust & Identity-First Security
Zero trust demands continuous verification, not one-time checks. Adaptive MFA fulfills this by analyzing risk throughout the session, not just at login. Traditional MFA cannot meet zero-trust requirements effectively.
Adaptive MFA Is Ideal When…
You serve millions of customers. You care about fast login & conversion rates You face modern threats. You operate globally You handle sensitive data. You follow zero-trust or identity-first security principles.
Wherever security and UX need to coexist, Adaptive MFA wins every time.
CIAM Perspective: Why Adaptive MFA Is Becoming the Standard
From a CIAM (Customer Identity and Access Management) standpoint, Adaptive MFA is no longer a “nice-to-have.” It has become the core of how modern digital platforms balance airtight security with frictionless customer experiences.
Traditional MFA worked well when threat patterns were simpler and user expectations were lower. But today’s CIAM needs to demand far more intelligence, personalization, and real-time decisioning.
Adaptive MFA delivers exactly that, making it the new standard for customer identity platforms across industries.
Security Alone Isn’t Enough. CIAM Must Also Protect User Experience
In customer environments, every extra second counts. A delayed OTP, a failed push notification, or an unnecessary MFA prompt can cause:
-
Abandoned sign-ups
-
Dropped logins
-
Checkout failures
-
Lost revenue
-
Poor user satisfaction
Adaptive MFA recognizes this and ensures low-risk users glide through login without friction, while high-risk scenarios receive stronger authentication. It’s a balance that traditional MFA simply cannot offer.
Adaptive MFA Reduces Account Takeovers at Scale
Consumer apps are high-value targets for attackers. Credential stuffing, phishing campaigns, device fraud, OTP interception these attacks hit millions of accounts at once.
Traditional MFA reacts the same way to all attempts. Adaptive MFA predicts and responds based on risk.
With contextual checks and behavioral analytics, Adaptive MFA:
-
Blocks automated bot attacks
-
Detects unusual travel patterns
-
Flags suspicious devices or IPs
-
Differentiates legitimate users from attackers
This proactive defense model aligns perfectly with CIAM requirements.
Global User Bases Need Dynamic Authentication
Customer-facing platforms often serve:
-
Users across multiple countries
-
Hundreds of device types
-
Varied network conditions
-
Different security expectations
Traditional MFA breaks under this complexity.
Adaptive MFA thrives in it by adjusting authentication based on:
-
Region
-
Network quality
-
Local regulations
-
Device capabilities
-
Risk levels
This makes it ideal for multinational brands, global eCommerce, and high-growth SaaS.
Aligns Perfectly With Zero Trust and Identity-First Security
Modern CIAM strategies increasingly lean toward zero trust, where identity not the network is the new security perimeter.
Adaptive MFA fits naturally into this model because it:
-
Continuously evaluates risk
-
Never assumes trust
-
Validates behavior during the session
-
Detects anomalies instantly
Traditional MFA authenticates a user once and assumes trust afterward—which is no longer acceptable in modern environments.
Better Conversion, Higher Retention, and Stronger Brand Trust
From the CIAM perspective, authentication is not just a security step; it’s a business driver.
The login experience influences:
-
User satisfaction
-
App engagement
-
Conversion rates
-
Revenue performance
Adaptive MFA removes unnecessary friction without weakening security creating a login journey that users actually enjoy.
Platforms that adopt adaptive MFA are perceived as:
-
More secure
-
More reliable
-
More user-friendly
This builds long-term brand trust and strengthens the customer relationship.
If you’re selecting between mfa solutions, your choice comes down to whether you need static enforcement across all logins or adaptive decisioning that optimizes security and UX in adaptive MFA vs MFA comparisons.
Decision Framework: Adaptive MFA or Traditional MFA?
Deciding between Adaptive MFA and Traditional MFA depends on your security requirements, user experience goals, application scale, and threat landscape. Traditional MFA is predictable and simple, while Adaptive MFA is intelligent and designed for modern CIAM environments where friction, global usage, and advanced threats are real concerns.
Below is a clear decision framework to help you choose the right approach.
Comparison Table: Adaptive MFA vs Traditional MFA
| Category | Traditional MFA | Adaptive MFA |
|---|---|---|
| Authentication Flow | Static, same steps for every user | Dynamic, risk-based & context-aware |
| User Experience | Higher friction (OTP every time) | Low friction (step-up only when needed) |
| Security Level | Good, but predictable | Exceptional, with real-time risk analysis |
| Resilience to Modern Attacks | Weak against phishing, SIM-swaps, AitM | Strong phishing resistance, anomaly detection |
| Risk Scoring | Not available | Core feature, evaluates every login |
| Behavioral Analysis | None | Evaluates deviations in behavior & patterns |
| Device & IP Intelligence | Not included | Deep device fingerprinting, IP reputation checks |
| Scalability for CIAM | Struggles at high scale | Built for millions of users & global traffic |
| Conversion Impact | High drop-offs due to OTP fatigue | Higher conversion = fewer interruptions |
| Cost Efficiency | Higher long-term costs (SMS OTP, support tickets) | Lower operational costs, fewer support needs |
| Compliance Alignment | Meets minimum MFA standards | Aligns with modern identity-first + zero-trust frameworks |
| Ideal Use Case | Workforce tools, low-risk apps | Customer-facing apps, high-risk use cases, global platforms |
| Friction Control | No control same for all users | Personalized friction based on trust & context |
| Bot & Credential-Stuffing Defense | Limited protection | Strong detection via risk analysis |
| Session Intelligence | None | Continuous monitoring & anomaly detection |
| Future-Readiness | Outdated in the evolving threat landscape | Modern, AI-ready model for CIAM |
How to Choose Out Of The Two:
Choose Traditional MFA if:
-
Your app has a small user base
-
Users are internal employees
-
Friction is acceptable
-
You only need to meet basic compliance requirements
-
Threat levels are low
-
You prefer a simple static flow
Choose Adaptive MFA if:
-
You serve millions of customers
-
Your platform is global and mobile-heavy
-
You face modern attacks: phishing, bots, credential stuffing
-
You want frictionless login experiences
-
UX, conversion, and retention matter
-
You follow zero-trust or identity-first security
-
You want to reduce SMS + support costs
-
You want security that scales intelligently
Conclusion
The way users authenticate has fundamentally changed. Traditional MFA played an important role in strengthening security beyond passwords, but digital threats have evolved, and so have user expectations.
Today’s customers want fast, seamless experiences, while organizations need stronger, more intelligent protection against increasingly sophisticated attacks. Adaptive Multi-Factor Authentication delivers exactly that.
By combining risk scoring, contextual intelligence, behavioral analysis, device trust, and real-time threat signals, Adaptive MFA creates a security model that adapts to each individual login attempt.
It protects users before a threat becomes dangerous and stays invisible when everything looks safe. This is the level of intelligence modern CIAM platforms demand.
Traditional MFA still has its place, especially in smaller, lower-risk environments, but it cannot match the balance of security, scalability, and low friction that Adaptive MFA offers. For high-traffic consumer applications, global user bases, enterprise SaaS platforms, and any business operating in a zero-trust or identity-first environment, Adaptive MFA is no longer optional. It’s the new standard.
Choosing Adaptive MFA doesn’t just improve security; it improves the entire user journey. It boosts login success rates, reduces abandonment, lowers support volume, and builds deeper trust with your customers. In the long run, it leads to a platform that is more secure, more resilient, and far more user-friendly.
If you want an authentication experience that feels effortless for users and uncompromising for attackers, Adaptive MFA is the clear winner.
Ready to Deliver Smarter, Context-Aware Authentication?
Your customers deserve an authentication system that’s as smart and dynamic as the threats they face. Book a Live Demo to see Adaptive MFA in action. Explore LoginRadius CIAM to build secure, frictionless identity journeys.
FAQs
Q: What is the main difference between traditional MFA and adaptive MFA?
A: Traditional MFA applies the same step-up challenge to every login, while adaptive MFA evaluates risk signals (device, IP, behavior, location) in real time and only challenges when needed. That makes adaptive MFA both smarter and more context-aware than static MFA.
Q: When should I choose adaptive MFA vs MFA for my applications?
A: Choose adaptive MFA when you have high login volumes, mixed-risk user groups, or sensitive data and want strong security without constant friction. Standard MFA is fine for smaller, low-risk apps, but adaptive MFA is better for modern CIAM and Zero Trust architectures.
Q: Does adaptive MFA really reduce user friction compared to traditional MFA?
A: Yes. With adaptive MFA, low-risk logins often pass with silent checks, while only risky sessions see extra prompts. Users experience fewer MFA challenges overall, improving authentication UX and conversion rates without weakening protection.
Q: Is adaptive MFA more secure than regular MFA?
A: Adaptive MFA adds an extra defense layer by combining MFA factors with continuous risk scoring, anomaly detection, and policy controls. This makes it more effective than traditional MFA alone at catching account takeover attempts, MFA fatigue attacks, and other modern threats.