Introduction
Most JWT-related security incidents don’t start with broken cryptography. They start with a quiet assumption: “The token is valid because it decoded correctly.”
And that assumption sneaks into production more often than teams like to admit. A JWT arrives, the signature checks out, exp looks fine, and the request goes through. No one notices the missing aud check. Or the issuer mismatch. Or the fact that the signing key rotated last night and half the services are now trusting stale keys.
JWTs are deceptively simple. Three dots. Some base64. A JSON payload that looks readable enough to lull even experienced engineers into a false sense of safety. That’s the trap. JWT validation is not decoding.
It’s not just signature verification either. Real-world JWT validation is a sequence of strict, opinionated checks that decide whether a token should be trusted in this exact context, by this exact service, right now.
Here’s where it gets interesting: most broken implementations aren’t missing advanced features. They’re skipping basics. iss is checked loosely or not at all. aud is assumed instead of enforced. JWKS rotation works fine… until it doesn’t.
Clock skew causes intermittent failures that get “fixed” by extending token lifetimes. And nonce? Often implemented once, then forgotten, then quietly bypassed when things get inconvenient.
This blog is a JWT validation checklist built from those failures. Not theory. Not specification quotes without consequences.
We’ll focus on the checks that actually matter in production: issuer and audience validation, JWKS and key rotation behavior, clock skew handling, and nonce verification, plus how all of this fits into JWT token authentication and JWT security best practices without turning your auth layer into a guessing game.
If you’ve ever wondered whether your current approach to validating JWT tokens would hold up under key rotation, multi-tenant issuers, or distributed systems with imperfect clocks, this is for you.
JWT Validation Is a Pipeline, Not a Single Function Call
Most JWT bugs don’t come from doing the wrong thing. They come from doing only one thing and assuming the rest will somehow work itself out. A token gets parsed. The signature verifies. The request moves on. Somewhere along the way, validation quietly stops being validation and turns into optimism.
Here’s how JWT validation actually works in practice: it’s a pipeline. A sequence of gates. Each step answers a different question. Is this token well-formed? Was it signed by someone we trust? Was it meant for us? Is it still valid right now? Miss one gate, and the whole model starts leaking trust in subtle, dangerous ways.
The mistake teams make is collapsing this pipeline into a single library call. Most JWT libraries will happily decode a token, verify a signature, and hand you a payload without enforcing issuer rules, audience boundaries, time drift policies, or contextual checks.
That’s not a bug in the library. That’s a design choice. The responsibility to define how to validate a JWT token belongs to your system, not the SDK.
At the center of JWT token validation are four distinct stages. First comes safe parsing, where malformed or unexpected token structures are rejected immediately. Next is signature verification, where cryptography confirms the token hasn’t been tampered with.
Then comes standard claim validation checks like iss, aud, exp, and nbf that define trust boundaries. Finally, there are contextual checks, such as nonce validation, token purpose, and usage constraints that depend on where and how the token is being used.
Here’s where teams usually go wrong: they stop after stage two. The token is signed correctly, so it must be valid. But signature verification only answers one question: who signed this token?
It says nothing about whether the token was issued for your service, whether it’s being replayed, or whether it’s still acceptable in the current execution context. That gap is where most jwt security best practices quietly fall apart.
Once you start thinking of validating JWT tokens as a pipeline instead of a checkbox, the rest of the checklist makes a lot more sense. Each step exists to close a specific failure mode. Skip one, and you’re no longer validating you’re just hoping.
Step 1: Know What You’re Validating (Access Token vs ID Token)
Before you validate anything, you need to answer a deceptively simple question: what kind of JWT is this supposed to be? Because access tokens and ID tokens may look similar on the surface, but treating them the same is one of the fastest ways to break JWT token authentication in subtle, long-lasting ways.
An access token exists for one reason: to authorize access to an API. It represents delegated permission and is meant to be consumed by a resource server. An ID token, on the other hand, exists to prove authentication to a client. It tells an application who the user is and how they authenticated. Mixing these roles is where validation logic starts drifting into dangerous territory.
Here’s where teams usually go wrong. An ID token is validated once during login, it looks trustworthy, and someone decides to reuse it for API calls. The signature is valid. The claims look fine.
But the token was never meant for that API. The aud doesn’t match the resource server. The nonce semantics don’t apply. Suddenly, JWT validation becomes context-blind, and attackers love context-blind systems.
This distinction matters even more when OpenID Connect enters the picture. ID tokens bring additional expectations, including nonce validation, that simply don’t apply to most access tokens.
If you enforce nonce checks on every JWT, you’ll break legitimate flows. If you skip nonce validation where it’s required, you open the door to replay and mix-up attacks. The only way to get this right is to know the token’s intended purpose before you start validating JWT standard claims.
At the center of how to validate a JWT token is intent. What was this token issued for? Who is supposed to consume it? And under what assumptions? If you don’t answer those questions upfront, no amount of cryptographic correctness later in the pipeline will save you.
Step 2: Lock Down Algorithms Before Anything Else
Algorithm handling is one of those things that feels solved until you look closely at how most systems actually do it. A JWT arrives, the library reads the alg value from the header, picks the verification method automatically, and moves on. Clean. Convenient. Also risky, if you don’t take control early.
Here’s the uncomfortable truth: the JWT header is attacker-controlled input. Treating it as a configuration instead of data is how algorithm confusion bugs are born. When a system implicitly trusts whatever alg shows up in the token, it hands decision-making power to the token itself, and that’s the opposite of JWT security best practices.
In a well-implemented JWT validation flow, algorithm choice is a policy decision, not a discovery step. You decide upfront which algorithms are acceptable for a given issuer and token type. If your system expects RS256, then anything else, HS256, none, or something unexpected gets rejected immediately. No fallback logic. No “try the next option.” Just a hard stop.
This matters even more in environments where multiple systems coexist. Some teams still support symmetric signing in legacy paths while newer services use asymmetric keys. Without strict algorithm enforcement, it becomes surprisingly easy to validate a token using the wrong method.
The signature may verify, but not under the trust model you intended. That’s how validating JWT tokens turns into validating anything that passes.
Locking down algorithms early simplifies everything that follows. Signature verification becomes deterministic. JWKS handling stays predictable. And most importantly, you eliminate an entire class of attacks before claims like iss or aud even enter the conversation. In jwt token validation, few checks are as foundational or as commonly underestimated as this one.
Step 3: Validate the Issuer (iss), Like It’s a Hard Security Boundary
The iss claim is often treated as background noise, something that’s “nice to check” but rarely enforced with real discipline. That’s a mistake. In JWT validation, the issuer is not metadata. It’s a trust boundary. If you get this wrong, you’re not validating tokens; you’re accepting them on faith.
At its core, the iss claim answers one question: who issued this token? But the real security question is sharper: do I explicitly trust tokens from this issuer for this purpose? Skipping that distinction is how tokens minted for one environment, tenant, or application end up being accepted somewhere they were never meant to reach.
Here’s where teams usually go wrong. They validate the signature, see that it checks out, and assume the issuer must be fine because the key was valid. But cryptographic validity doesn’t imply contextual trust.
A token can be perfectly signed by a legitimate issuer and still be completely wrong for your service. Without strict iss validation, JWT token validation quietly becomes “accept any token signed by someone we vaguely recognize.”
Issuer validation needs to be exact. Not “starts with.” Not “contains.” Not “looks close enough.” The iss value must match one of a known, explicit set of allowed issuers. This matters even more in multi-tenant systems, where the difference between two issuers may be a single path segment. One missed comparison, and you’ve just collapsed tenant isolation at the identity layer.
At the center of JWT security best practices is this idea: trust is scoped. The iss claim scopes trust to a specific authority, environment, and context. If you don’t enforce it strictly, every downstream check aud, scopes, even nonce starts from a compromised assumption. And once that happens, validating JWT tokens becomes a formality instead of a safeguard.
Step 4: Validate the Audience (aud) Never Assume Intent
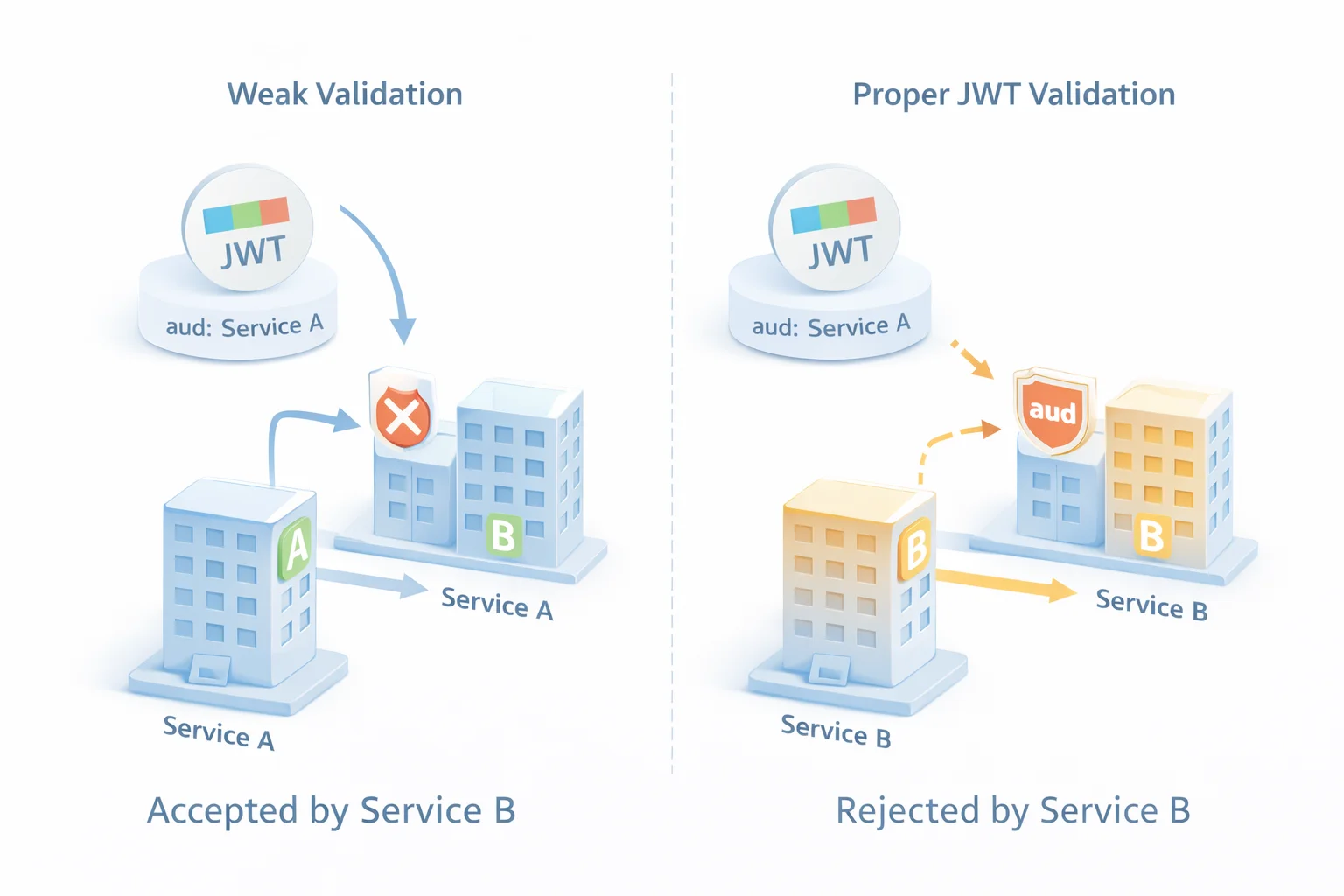
If the issuer tells you who created the token, the aud claim tells you who the token was meant for. And yet, audience validation is one of the most commonly skipped steps in JWT validation, usually because “it hasn’t caused problems so far.” That logic only holds until your system grows.
The aud claim exists to prevent token reuse across services. A JWT issued for one API, client, or resource should not automatically work for another, even if everything else about the token looks valid. Without strict audience checks, you’re effectively saying, “Any token from this issuer is good enough for us.” That’s not authorization. That’s hope.
Here’s where teams usually go wrong. They assume the audience implicitly matches because the issuer is shared. Or they check that aud exists, but don’t verify its value. Sometimes it’s worse they accept the first audience in a list and move on. In distributed systems, that’s how a token meant for Service A quietly gains access to Service B.
Audience validation needs to be explicit and intentional. Your service should know its own identifier and confirm that it appears in the token’s aud claim no substitutions, no approximations. If the token carries multiple audiences, your service still needs to prove that it is one of them. Anything else weakens the boundary between services and erodes the point of validating JWT tokens in the first place.
This is especially important in modern architectures where multiple APIs sit behind the same identity provider. In those setups, aud is often the only thing standing between clean separation and accidental overreach. Get it right, and jwt token validation enforces clear intent. Get it wrong, and you end up authorizing requests that were never meant to reach you at all.
Step 5: Signature Verification With JWKS (That Actually Survives Key Rotation)
Signature verification is the part most teams feel confident about until the day it breaks in production. Not because the math failed, but because keys changed and the system wasn’t ready. That’s the difference between verifying a signature once and building jwt validation that survives real-world key rotation.
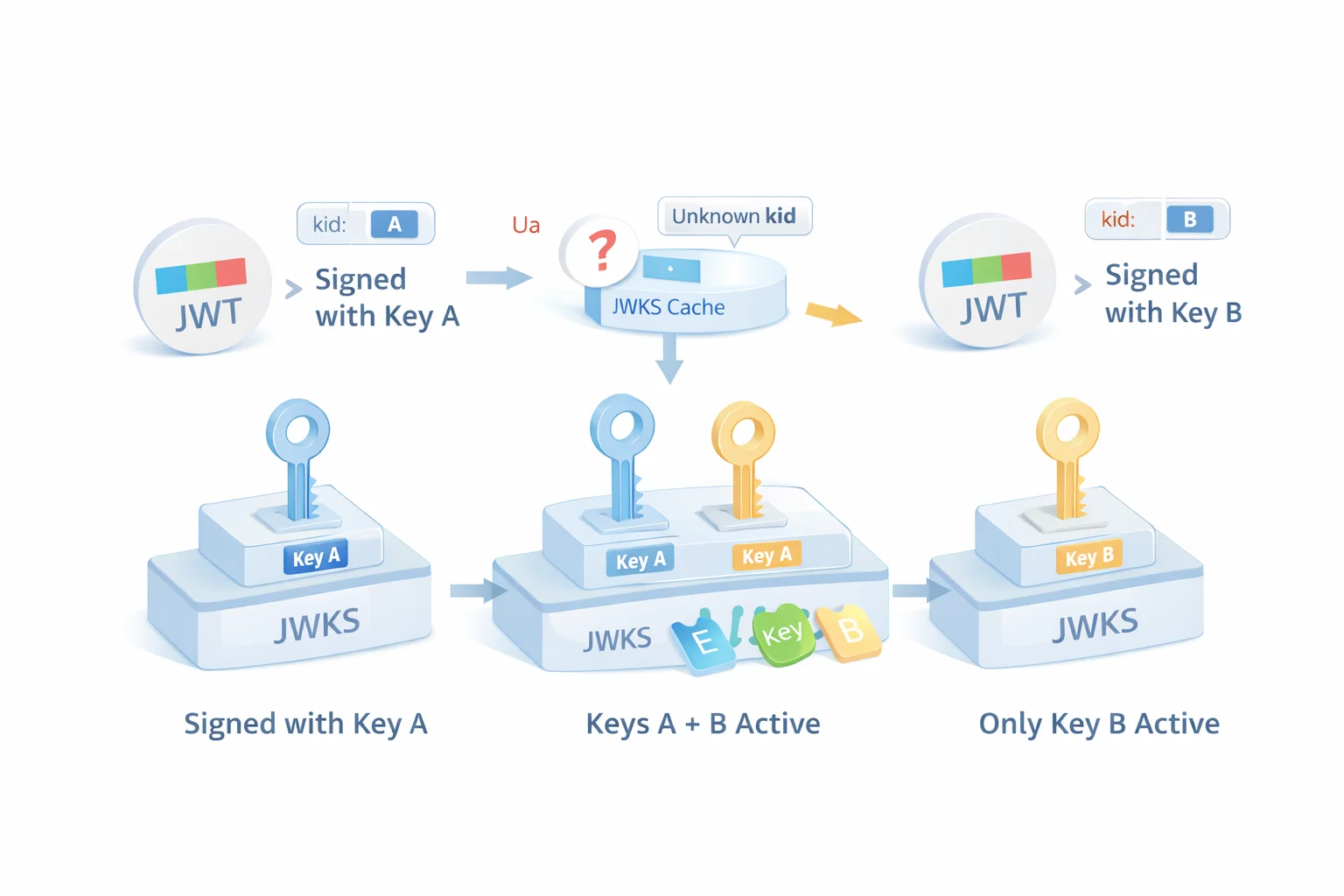
When asymmetric signing is involved, signature verification depends on JWKS a published set of public keys the issuer uses to sign tokens. Each JWT points to the correct key using the kid in its header. Sounds straightforward. But in practice, this step quietly fails when keys rotate, caches go stale, or services assume keys never change.
Here’s the pattern teams fall into. They fetch the JWKS once at startup, cache it forever, and move on. Everything works until the issuer rotates signing keys. Suddenly, perfectly valid tokens start failing validation. The quick “fix” is often to disable validation temporarily or relax checks. That’s how jwt security best practices unravel under pressure.
Proper jwt token validation treats JWKS as a living dependency, not a static configuration. Keys must be cached intelligently, refreshed periodically, and re-fetched when an unfamiliar kid appears. During rotation windows, multiple keys may be valid at the same time. Your validation logic needs to expect that, not panic when it happens.
This is where validating JWT tokens becomes an operational discipline. Signature verification isn’t just about cryptography; it’s about resilience. A system that can’t handle key rotation reliably will eventually choose availability over security in a crisis. And once that trade-off is made, JWT validation stops being a safeguard and starts being a liability.
Step 6: Time-Based Claims and Clock Skew (The Quiet Source of Flaky Auth)
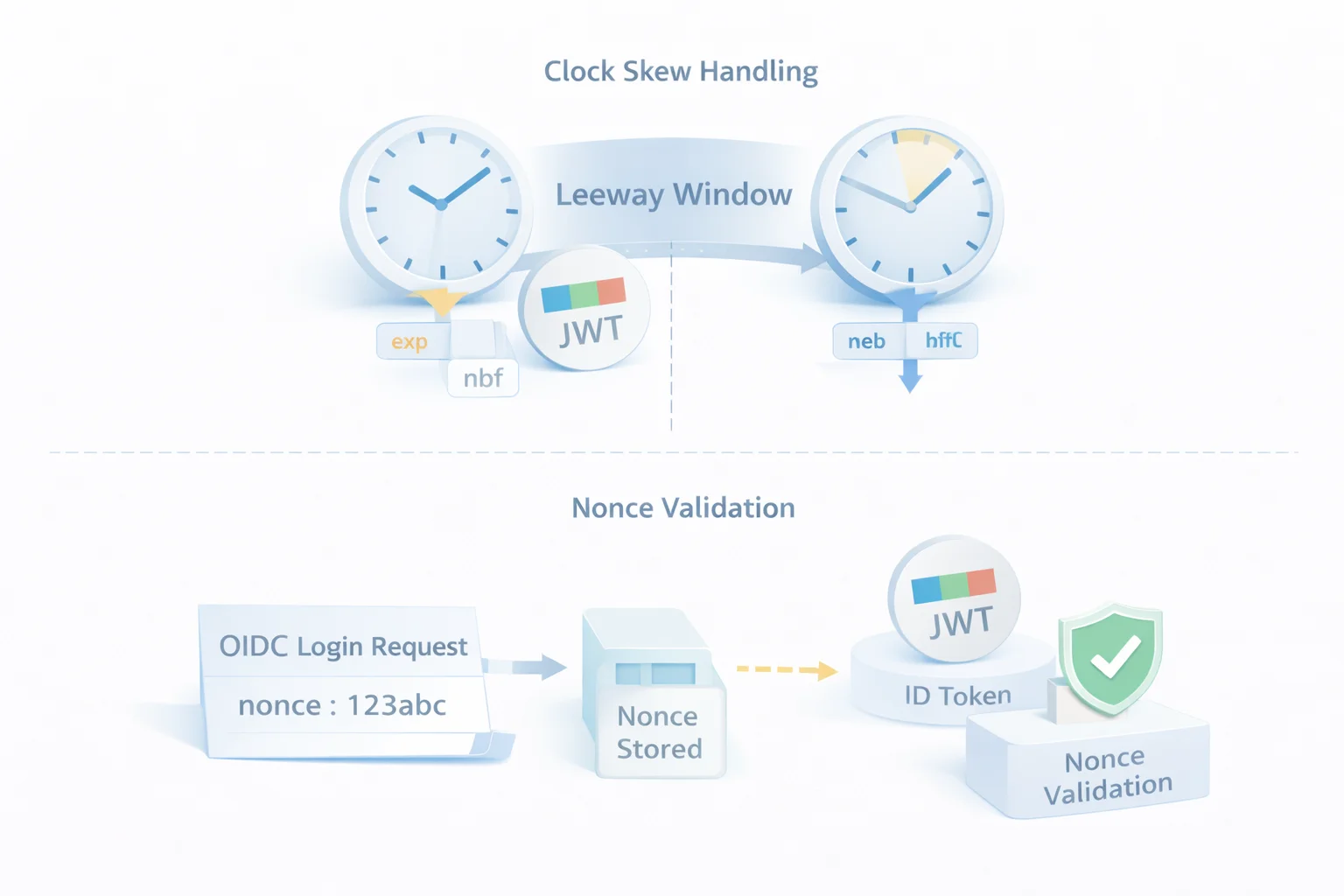
Time is the least trusted dependency in distributed systems, and yet JWT validation relies on it heavily. Claims like exp, nbf, and iat look simple on paper. In production, they’re responsible for some of the most confusing, intermittent authentication failures teams struggle to explain.
On a good day, clocks are in sync, and everything works. On a bad day, one container drifts a few seconds behind, a mobile device reports time slightly ahead, or a VM resumes with stale system time. Suddenly, valid tokens start failing JWT token validation for reasons that don’t reproduce consistently. That’s where panic-driven fixes usually begin.
Here’s where teams usually go wrong. Instead of addressing clock skew directly, they extend token lifetimes. Five minutes becomes an hour. An hour becomes a day. The system feels stable again, but at the cost of replay risk and longer exposure windows if a token is compromised. That’s not a fix. That’s trading security for silence.
Proper validation of JWT tokens acknowledges that a small time drift is inevitable. The answer is bounded leeway, not unlimited forgiveness. A controlled skew window applied consistently across services allows for real-world imperfections without weakening the overall trust model. Expired still means expired. Just not to the millisecond.
Time-based claim validation is a discipline check. If your JWT security best practices can’t tolerate minor clock differences, they’ll eventually be bypassed. And once time checks are treated as optional, JWT validation becomes unpredictable, sometimes strict, sometimes permissive, always fragile.
Step 7: Nonce Validation Critical in the Right Flows, Dangerous to Ignore
Nonce is one of those concepts that gets implemented once and then quietly misunderstood forever. Some teams validate it everywhere. Others skip it entirely. Both approaches miss the point. In jwt validation, nonce is not a universal rule; it’s a contextual safeguard that matters deeply in specific flows and not at all in others.
Nonce exists to prevent replay and mix-up attacks during authentication, particularly in OpenID Connect flows that involve browsers or redirects. When a client sends a nonce during authentication, it’s making a promise: “Only accept an ID token that proves it belongs to this exact login attempt.” That promise is fulfilled only if the nonce in the returned token is validated strictly.
Here’s where teams usually go wrong. The nonce is generated, sent, and then forgotten. Or it’s stored loosely and compared casually. Or worse, it’s validated once during development and silently bypassed later because “it was breaking logins.” At that point, nonce becomes a checkbox instead of a control, and JWT token validation loses one of its most important defenses in interactive flows.
It’s just as dangerous to apply nonce validation blindly. Most API access tokens don’t carry a nonce and don’t need one. Enforcing nonce checks where they don’t belong leads to brittle logic and broken integrations. Knowing when to validate nonce is just as important as knowing how.
At the center of JWT security best practices is intent. If a nonce was sent, it must be validated exactly. If it wasn’t, it shouldn’t be invented after the fact. Nonce is optional only until you use it; after that, it becomes non-negotiable.
Step 8: Standard Claims You Still Need to Validate (Even If They Feel Obvious)
By the time most systems reach this stage, there’s a dangerous sense of confidence. The signature is valid. The issuer and audience match. Time checks passed. It feels like the hard work is done. This is usually where teams stop paying attention and where small claim-level assumptions start causing big problems.
Standard JWT claims exist for a reason. They encode expectations about identity, lifespan, and uniqueness that your application shouldn’t have to guess. Take sub, for example. It’s meant to represent a stable subject identifier, not a display name or an email address that might change. Treating it casually creates identity drift that surfaces later as authorization bugs and audit gaps.
Then there’s jti. Many teams ignore it because they’re not actively tracking token reuse. That’s fine until they need replay awareness or traceability during an incident. Even if you don’t enforce uniqueness at runtime, validating the presence and format of jti gives you a hook for future controls without redesigning jwt token validation from scratch.
Claims like typ and custom application claims fall into a similar category. They’re signals, not trust anchors. Validating them helps confirm intent and structure, but trusting them blindly invites policy sprawl. In jwt validation, structure matters as much as content. A claim that exists but doesn’t match expected shape or values should be treated with the same skepticism as a missing claim.
This is the quiet work of validating JWT tokens properly. It’s not flashy. It doesn’t break loudly when done wrong. But over time, it’s what keeps jwt security best practices enforceable instead of theoretical especially as systems grow and assumptions age.
The JWT Validation Checklist
At this point, the patterns should be clear. JWT validation works when it’s systematic, repeatable, and boring in the best way. When teams rely on memory or tribal knowledge, checks get skipped. When validation is written down as a checklist, it actually gets enforced.
Think of this as the minimum bar. Not the most advanced setup. Not the most paranoid one either. Just the set of checks that keep JWT token validation honest as systems scale, keys rotate, and assumptions get challenged.
Start by rejecting tokens that don’t even meet structural expectations. A JWT that isn’t well-formed shouldn’t make it past the front door. From there, enforce algorithm policy explicitly, never by inference. Signature verification must use the correct key, selected via kid, with JWKS treated as a dynamic dependency rather than a static file.
Once cryptographic trust is established, validate intent. Confirm the issuer exactly. Confirm the audience deliberately. Apply time-based checks with bounded clock skew so real systems don’t break while attackers still get shut out. If a nonce was part of the authentication flow, validate it strictly, no shortcuts, no fallbacks.
Finally, validate the remaining claims that anchor identity and structure. Make sure required claims exist, match expected formats, and align with how your application actually makes authorization decisions. And log validation failures in a way that helps you debug without ever exposing raw tokens.
This checklist isn’t about perfection. It’s about consistency. When JWT validation becomes predictable, JWT security best practices stop being aspirational and start becoming part of the infrastructure you can rely on.
Where JWT Validation Usually Breaks
Most teams don’t ignore JWT validation. They just trust it too much. The logic exists, tests pass, and everything feels solid until traffic grows, integrations multiply, or something changes outside your control. That’s when the cracks show up, usually in places no one thought to revisit.
One common failure is treating signature verification as the finish line. The token is signed correctly, so it must be safe. But signature checks only confirm who signed the token, not whether your service should accept it. When issuer or audience validation is relaxed “just to get things working,” jwt token validation quietly loses its ability to enforce boundaries.
Another breaking point shows up during key rotation. JWKS caching worked fine when keys were static. Then rotation happens, tokens start failing, and pressure mounts. Instead of fixing refresh logic, teams disable validation temporarily or add broad fallbacks. That single shortcut often lives far longer than intended and weakens JWT security best practices long after the incident is over.
Time-based checks fail differently. Clock skew causes intermittent auth failures that are hard to reproduce, so teams widen token lifetimes instead of tightening validation rules. The system stabilizes, but only because the window of trust has expanded. Replay risk increases, and no one notices until it matters.
And then there’s nonce. Implemented early. Forgotten later. Sometimes removed because it “wasn’t really needed.” The problem isn’t skipping nonce everywhere; it’s skipping it where it was part of the original security contract. At that point, validating JWT tokens becomes selective, inconsistent, and fragile.
These failures don’t happen because teams don’t care. They happen because JWT validation logic is rarely treated as living infrastructure. When it isn’t reviewed, tested, and enforced consistently, it slowly drifts from protection into assumption.
JWT Validation by Environment: Same Rules, Different Failure Modes
JWT validation doesn’t break the same way everywhere. The rules stay consistent, but the environments don’t. What works cleanly in a single backend service can behave very differently in a browser, a mobile app, or a distributed microservices setup. Ignoring those differences is how “technically correct” validation turns into operational pain.
In API and microservice environments, the biggest risk is inconsistency. One service validates aud strictly, another assumes it. One refreshes JWKS properly, another relies on a warm cache. Over time, jwt token validation becomes uneven, and attackers only need to find the weakest link. Shared middleware and centralized validation policies are what keep this from happening.
Browser-based applications bring a different set of challenges. Redirect-based flows, third-party cookies, and front-channel interactions make nonce handling and token context especially important. Tokens may look valid, but without careful validation of issuer, audience, and nonce, JWT validation can be tricked into accepting responses from the wrong authentication flow altogether.
Mobile and distributed systems introduce time as a new adversary. Devices drift. Networks pause. Processes resume with stale clocks. Without thoughtful clock skew handling, validating JWT tokens becomes unpredictable, sometimes rejecting good tokens, sometimes accepting bad ones. The fix isn’t loosening rules arbitrarily. It’s applying bounded tolerance consistently.
Across all environments, the lesson is the same. JWT security best practices don’t change, but their failure modes do. When validation logic is designed with the environment in mind, it stays reliable under stress. When it isn’t, it becomes the first thing teams work around instead of the first thing they trust.
Conclusion
JWT validation isn’t where most teams focus their energy but it’s exactly where long-term security is decided. When done right, it fades into the background and just works. When done poorly, it becomes the kind of silent risk that only shows up when it’s too late.
The difference isn’t in the token, it’s in how consistently and correctly you validate it across your system.
That’s where platforms like LoginRadius make a real impact. Instead of stitching together validation logic across services, you get a centralized, standards-compliant approach to token issuance, validation, key rotation, and lifecycle management—built for scale from day one.
If you’re building APIs, microservices, or any distributed system where JWTs are part of the authentication flow, don’t treat validation as a one-time checklist.
Make it part of your infrastructure. Or better, let a platform designed for identity handle it for you.
Explore how LoginRadius can help you implement secure, scalable JWT authentication without the operational overhead.
FAQs
Q: How do you validate a JWT token correctly?
A: JWT validation requires more than decoding and signature checks. You must verify the signature, enforce iss and aud, validate time-based claims with clock skew, handle JWKS rotation, and apply context checks like nonce when required.
Q: What is the most common mistake in JWT validation?
A: Stopping after signature verification. A token can be cryptographically valid but still unsafe if issuer, audience, or time-based claims aren’t enforced strictly.
Q: How should JWKS rotation be handled in production?
A: JWKS keys should be cached with refresh logic and re-fetched when an unknown kid appears. Validation must expect multiple active keys during rotation without relaxing security rules.
Q: When is nonce validation required in JWTs?
A: Nonce validation is required in OpenID Connect authentication flows when a nonce was sent in the request. It’s not needed for most API access tokens and shouldn’t be enforced universally.



