Introduction
Securing a SaaS platform today is radically different from securing a traditional application. Your users can log in from anywhere, on any device, at any time, and attackers can too. As SaaS adoption accelerates across every industry, the login page has quietly become the single most targeted entry point for cybercriminals.
Credential stuffing, brute-force attempts, bot-driven abuse, MFA fatigue attacks, and phishing kits designed to bypass OTPs now operate at a massive scale.
This is why Multi-Factor Authentication (MFA) is no longer a “nice to have” for SaaS platforms; it's the baseline for survival. But not all MFA is equal, and not every method works for every SaaS model.
For B2B product teams, this conversation becomes even more specific. The reality is that mfa best practices for b2b saas require stronger controls for admins, tenant isolation, auditability, and reliable enforcement across SSO and partner access flows—without breaking onboarding or daily login velocity.
In this guide, we’ll break down the best MFA strategies for SaaS platforms, comparing methods like TOTP, push, security keys, biometrics, passkeys, and adaptive multi-factor authentication.
What Makes MFA for SaaS Different?

Multi-factor authentication isn’t one-size-fits-all and SaaS platforms experience a completely different set of pressures compared to traditional software. Unlike internal workforce systems, SaaS applications deal with unpredictable user behavior, diverse device ecosystems, and massive global traffic patterns. This makes MFA choices far more strategic than simply “adding an extra step.”
Read more : What is Multi Factor Authentication (MFA) and How does it Work?
Multi-Tenant Architecture Changes Everything
SaaS platforms must secure multiple tenants, each with unique roles, permissions, and risk levels. A single MFA approach cannot protect:
-
admin accounts
-
standard users
-
external collaborators
-
API/service accounts
This requires flexible MFA policies that adapt to each tenant, each user group, and each sensitive action.
SaaS Platforms Can’t Afford Friction
Every additional login step increases drop-offs. Unlike corporate systems, SaaS platforms must preserve conversion funnels, meaning MFA must:
-
add minimal friction
-
work across all devices
-
support fast onboarding
-
avoid breaking login flows
This is especially true in B2C SaaS, where user patience is extremely low.
Your Users Log In From Everywhere
A global SaaS platform must support authentication across:
-
unstable networks
-
older devices
-
shared devices
-
different operating systems
-
unfamiliar locations
This requires MFA methods that remain reliable under inconsistent conditions, something SMS, email OTP, and even TOTP often struggle with.
SaaS Platforms Face Higher Attack Volumes
Because SaaS serves broad user bases, it attracts:
-
large-scale credential stuffing
-
bot-driven login attempts
-
phishing campaigns
-
brute force automation
This makes basic MFA insufficient. SaaS needs strong MFA factors like WebAuthn, FIDO2 security keys, and adaptive policies that can detect suspicious behavior automatically.
Developer-Friendly MFA Matters for SaaS Growth
SaaS products thrive on integrations, APIs, SDKs, partner tools, and developer ecosystems. MFA must be:
-
easy to embed
-
API-first
-
compatible with automation
-
simple to configure
-
support CLI & service account flows
This is where many traditional MFA methods fail.
This is also why “SaaS authentication” must be treated as a product capability, not just a security checkbox. When teams design saas authentication correctly, MFA becomes a growth enabler reducing fraud while preserving conversion.
Core MFA Methods Every SaaS Platform Should Consider
Not all MFA methods deliver the same balance of security, usability, and reliability, especially in SaaS environments. Below is a clear, modern breakdown of the most relevant MFA factors, how they work, and where they fit into a SaaS authentication strategy.
In modern mfa saas deployments, organizations often combine factors depending on risk level and tenant needs, especially in enterprise plans where sso mfa enforcement becomes essential for secure access across federated identity providers.
TOTP (Time-Based One-Time Passwords)
TOTP is one of the most widely used MFA factors, generated via apps like Google Authenticator or Authy. A new 6-digit code appears every 30 seconds.
Pros
-
Works offline
-
Low cost
-
Easy to deploy
-
Familiar to users
Cons
-
Not phishing-resistant
-
Vulnerable to real-time MITM attacks
-
Manual entry introduces friction
-
Code drift and device mismatch issues
Best suited for: General-purpose SaaS applications needing simple, affordable MFA.
Push Notifications
Push MFA sends a login approval request to the user’s mobile device often with options like number matching or biometrics.
Pros
-
Extremely low friction
-
Fast and convenient
-
Ideal for mobile-first apps
-
Can be combined with biometrics
Cons
-
Vulnerable to MFA fatigue (push bombing)
-
Dependent on device availability
-
Requires stable Internet on the device
Best suited for: Consumer SaaS platforms where smooth UX is critical.
SMS & Email OTPs
Still common in SaaS apps, but weaker than other MFA factors.
Pros
-
Universal device support
-
No app installation needed
Cons
-
Prone to SIM-swap, SS7, and phishing attacks
-
High cost for global SMS delivery
-
Not acceptable for high-risk industries
Best suited for: Backup factors, recovery flows, or very low-risk SaaS use cases.
Security Keys (FIDO2 / WebAuthn)
Hardware-based authentication using cryptographic signatures.
Pros
-
Highest security
-
Fully phishing-resistant
-
Passwordless compatible
-
Fast and frictionless
Cons
-
Requires hardware keys
-
Requires user education/training
Best suited for: B2B SaaS, enterprise tiers, admin accounts, and high value actions.
Also read: Securing B2B SaaS: How Identity Management Leads the Charge Against Top 5 Security Challenges
Passkeys / Passwordless MFA
Device bound cryptographic credentials synced via iCloud, Google, or device TPM.
Pros
-
Frictionless authentication
-
Biometric login
-
Strong phishing resistance
-
No passwords at all
Cons
-
Requires modern device ecosystem
-
Account recovery design must be robust
Best suited for: High-growth SaaS platforms prioritizing UX + strong security.
Biometrics (Device-Driven)
FaceID, TouchID, Windows Hello, Android biometrics.
Pros
-
Very fast
-
No typing
-
Extremely low user effort
-
Secure if paired with FIDO2/WebAuthn
Cons
-
Device-dependent
-
Privacy concerns in some regions
Best suited for: Mobile-first SaaS apps and passwordless SaaS experiences.
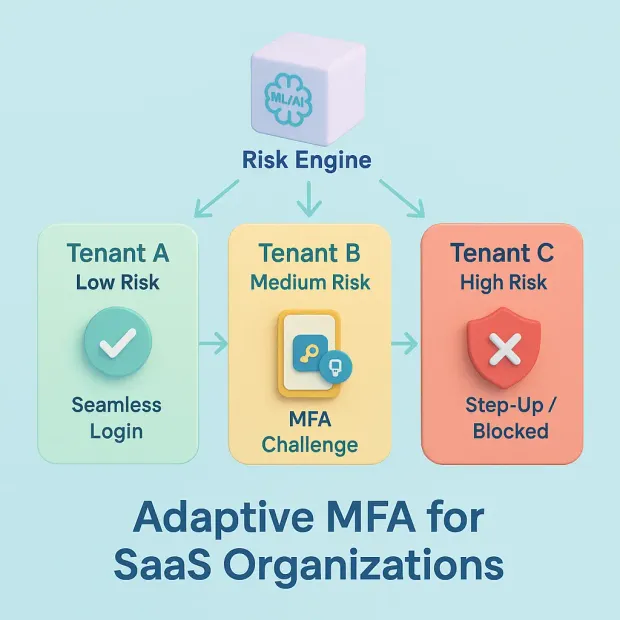
Adaptive MFA: The Winning Strategy for Modern SaaS
Traditional MFA treats every login the same. Whether a user is signing in from their usual device at home or a suspicious new location in another country, the same static MFA challenge appears. This creates friction for legitimate users and leaves dangerous gaps for attackers who learn to bypass predictable patterns.
Adaptive MFA solves this by making authentication dynamic. Instead of forcing additional challenges every time, it analyzes real-time risk signals and decides whether the login should be:
-
frictionless,
-
silently verified,
-
stepped up with stronger MFA, or
-
blocked entirely.
This is why top SaaS companies are replacing static MFA with adaptive, context-aware authentication.
How Adaptive MFA Works
Adaptive MFA continuously evaluates login context using signals such as:
-
Device fingerprint (new, jailbroken, untrusted?)
-
Geo-location (unexpected country?)
-
IP risk reputation (proxy, TOR, botnet?)
-
Behavioral patterns (typing speed, mouse movement, login times)
-
Network attributes (public Wi-Fi, suspicious routing)
-
User history (is this normal for this user?)
Each signal contributes to a real-time risk score. Based on that score, the system automatically decides the outcome.
Why Adaptive MFA Is Essential for SaaS
Reduces Friction Without Weakening Security
Most SaaS users log in from the same devices and IP ranges. Adaptive MFA avoids unnecessary MFA prompts for these “safe” patterns, dramatically improving login success rates.
Detects Anomalies Static MFA Misses
Attackers often pass username/password verification using credential dumps. Adaptive MFA identifies unusual activity in real time before the session is completed.
Perfect for High-Traffic Global SaaS
Adaptive MFA ensures:
-
fewer MFA prompts
-
less stress on backend authentication
-
faster login times
-
reduced operational burden on support teams
Ideal for Zero Trust Security Models
Zero Trust requires continuous verification. Adaptive MFA aligns perfectly by enforcing context-based checks on every session.
Best Strategy for Preventing MFA Fatigue Attacks
Since the system only triggers MFA when risk is high, users avoid excessive push prompts reducing chances of mistakenly approving fraudulent requests.
Adaptive MFA is not just “better MFA” it is the foundation of modern SaaS security.
Machine Learning’s Role in SaaS MFA (Modern CIAM Approach)
As credential attacks become more automated and sophisticated, traditional MFA alone cannot keep SaaS platforms safe. Attackers now use AI-driven phishing kits, large-scale botnets, and real-time AITM proxies that dynamically adapt to user behavior. To counter this, modern SaaS security must incorporate machine learning (ML) into MFA decisions not as an add-on, but as a core authentication layer.
Machine learning allows SaaS platforms to move from static verification to predictive, adaptive, and continuously evolving authentication.
What Machine Learning Adds to MFA
ML enhances SaaS authentication by analyzing millions of micro-signals in real time far beyond what static rules can catch. Instead of relying solely on passwords or login factors, ML evaluates patterns, behavior, and anomalies to determine if the user is real or an attacker.
ML helps MFA by:
-
Detecting suspicious login patterns
-
Identifying bots and automated tools
-
Spotting behavioral anomalies
-
Recognizing impossible travel events
-
Flagging risky devices or networks
-
Intercepting ATO attempts before MFA triggers
-
Scoring risk continuously throughout a session
Static MFA answers “Did the user enter the right factor?”
Machine learning answers “Does this look like the real user?”
Critical ML Signals Used in SaaS Authentication
1. Device Intelligence
-
New device
-
Jailbroken/rooted phones
-
Emulator or virtual device
-
Inconsistent device fingerprint
2. Geo-Location & Travel Patterns
-
Login from unusual regions
-
Impossible travel (e.g., India → US within minutes)
-
High-risk countries
3. Network & IP Reputation
-
TOR exit nodes
-
Proxy/VPN usage
-
Botnet IP clusters
-
Datacenter IPs pretending to be home networks
4. Behavioral Biometrics
-
Typing cadence
-
Touch pressure
-
Mouse velocity
-
Typical login times
-
Navigation patterns
5. Session Behavior
-
Sudden changes in usage
-
Rapid failed login attempts
-
Suspicious resource access
-
High-risk admin actions
All of these signals feed directly into a dynamic real-time risk score.
How ML Improves MFA Decisions
1. Reduces Unnecessary MFA Prompts
If everything looks normal, the user logs in without friction.
2. Detects Sophisticated Attack Patterns
Phishing kits and AITM proxies often mimic legitimate pages but they cannot perfectly mimic real user behavior.
3. Prevents MFA Fatigue Attacks
ML determines if a push approval is suspicious before sending it.
4. Auto-Blocks High-Risk Sessions
Instead of prompting MFA, the system can immediately deny access.
5. Enables Granular, Context-Aware Step-Up Authentication
Admins, finance teams, and privileged roles get stronger MFA checks automatically.
Learn about Step-Up Authentication by LoginRadius
Why ML Is Essential for SaaS Platforms
1. High User Volume Requires Automation
Large SaaS platforms receive millions of login attempts too many for rule-based systems.
2. Attackers Use AI Too
Modern threat actors leverage ML to adapt phishing pages and brute-force patterns in real time.
3. SaaS Must Balance UX & Security
ML helps maintain strong authentication while keeping the login experience frictionless.
4. Compliance-Driven Industries Demand Intelligent Authentication
Financial, healthcare, and enterprise SaaS often require behavioral analytics and continuous risk assessment.
5. Zero Trust Requires Continuous Verification
Machine learning enables ongoing session evaluation, not just at login.
ML + Adaptive MFA = Modern SaaS Security
When adaptive MFA is combined with machine learning, SaaS platforms gain:
-
real-time risk scoring
-
contextual decision-making
-
behavior-based authentication
-
phishing-resistant responses
-
continuous authentication beyond login
This is the level of intelligence needed to protect SaaS platforms in 2025 and beyond.
Passwordless for SaaS: The Future of MFA
The SaaS industry is rapidly moving beyond traditional MFA toward passwordless authentication, driven by the need for stronger security, smoother user experience, and reduced support overhead. Passwords have become the weakest link in the identity chain. Users reuse them, attackers steal them, and SaaS platforms end up dealing with continuous account takeover attempts.
Passwordless authentication removes passwords entirely, replacing them with cryptographic credentials, biometrics, or hardware-backed methods like passkeys and security keys. For SaaS platforms focused on growth, global reach, and security, passwordless isn’t just the future it’s becoming the new default.
What Passwordless Authentication Means for SaaS
Passwordless MFA uses device-bound credentials instead of passwords, making authentication:
-
faster
-
more secure
-
frictionless
-
phishing-resistant
Examples include:
-
Passkeys
-
FIDO2/WebAuthn security keys
-
Biometric device authenticators (FaceID, TouchID, Windows Hello)
-
Magic links (less secure, but popular in early SaaS onboarding)
These methods eliminate the risks associated with memory-based passwords and user-dependent security behavior.
Why Passkeys Are Becoming the Standard
Passkeys (Apple, Google, Microsoft ecosystem) offer the best combination of:
-
phishing resistance
-
frictionless UX
-
cross-device syncing
-
biometric convenience
-
device-bound cryptography
For SaaS platforms, passkeys allow:
-
instant onboarding
-
high login success rates
-
consistent authentication across devices
This is why major SaaS brands are actively transitioning to passkey-first login.
Combining MFA + Zero Trust for SaaS Security
Zero Trust has become the guiding framework for modern SaaS security — and MFA plays a central role within it. In a Zero Trust environment, no user, device, network, or session is trusted by default, even if they have already authenticated. Every action must be verified continuously, and every request must be evaluated against real-time context and risk.
For SaaS companies, combining MFA with Zero Trust principles transforms authentication from a one-time checkpoint into a dynamic, ongoing protection layer across the entire user session.
Why Zero Trust Matters for SaaS Platforms
SaaS platforms face threats that traditional access models were never designed for:
-
Global, unpredictable user behavior
-
Session hijacking and cookie theft
-
Credential stuffing at massive scale
-
Compromised devices accessing business-critical data
-
Insider threats in multi-tenant environments
-
Real-time phishing and AITM attacks
Zero Trust ensures that access is never assumed — it is continuously validated.
Also read : A Beginner's Guide to Zero Trust Security Model
How MFA Fits Into Zero Trust
MFA strengthens identity verification, but Zero Trust extends it by enforcing continuous and contextual checks throughout the session.
Zero Trust Enhances MFA By Adding:
Continuous Session Monitoring
User behavior, location, device posture, and network changes are constantly analyzed.
Contextual Access Controls
Access decisions adapt based on:
-
device health
-
IP risk
-
geo-velocity
-
resource sensitivity
-
user privileges
Just-in-Time & Just-Enough Access
MFA can be required dynamically for:
-
privilege elevation
-
sensitive data exports
-
financial transactions
-
admin panel entries
High-Risk Events Trigger Step-Up MFA
Security keys, biometrics, or passkeys are prompted only when needed.
Why MFA Alone Is Not Zero Trust
Many SaaS companies mistakenly believe adding MFA = Zero Trust.
But MFA alone only verifies identity at login.
Attackers can still bypass MFA through:
-
session theft
-
token replay
-
push fatigue attacks
-
device compromise
-
phishing proxies
-
OAuth token abuse
Zero Trust closes these gaps by evaluating every request—not just the login.
UX & Conversion: How MFA Impacts SaaS Growth
For SaaS platforms, security cannot come at the cost of user experience. MFA isn’t only a technical decision it’s a business decision that affects activation rates, login success, product adoption, and long-term customer satisfaction. Poorly implemented MFA can create friction, slow down onboarding, and cause drop-offs during critical conversion points.
The challenge is balancing strong authentication with a frictionless user experience. The good news: with the right strategy, SaaS companies can achieve both.
MFA Directly Impacts Onboarding & Activation
The onboarding flow is your SaaS product’s first impression. If MFA adds too many steps or appears too early, users abandon the signup process.
Common UX problems in SaaS MFA:
-
Overusing TOTP during account creation
-
Confusing QR code setup flows
-
Push notifications failing on certain devices
-
SMS OTP delays or non-delivery
-
MFA enforced before user trust is established
Best practices:
-
Offer passwordless onboarding (passkeys/magic links)
-
Delay MFA until email verification or first sensitive action
-
Provide multiple MFA options (TOTP, push, passkeys)
-
Keep setup short and highly visual
Friction Is the #1 Reason Users Abandon MFA
SaaS users expect instant access. Each extra step increases cognitive load and reduces the likelihood of successful login.
Friction sources include:
-
Requiring users to install an authenticator app
-
Entering codes manually
-
Poorly timed MFA prompts
-
Repeated MFA challenges on recognized devices
Adaptive MFA solves this by triggering MFA only when risk is high not every time.
Push, Biometrics & Passkeys Improve Conversion Rates
Modern authentication methods dramatically improve SaaS UX.
Why they work:
-
Push MFA = one tap to approve
-
Biometrics = instant login (FaceID/TouchID/Windows Hello)
-
Passkeys = passwordless, frictionless authentication
These methods reduce login drop-offs, especially on mobile.
MFA for Multi-Tenant SaaS: Customizing Experience Per Tenant
Different tenants require different MFA rules.
For example:
-
A healthcare client may require FIDO2 keys for all users
-
A tech startup may want push + biometrics only
-
A global client may need TOTP fallback for remote regions
SaaS platforms must offer configurable MFA per tenant without hurting other customers’ UX.
MFA for Mobile-First SaaS Platforms
Mobile SaaS experiences need MFA methods that work reliably on all devices.
Best MFA for mobile apps:
-
Mobile push
-
Passkeys
-
Device binding
-
TOTP (fallback)
SMS OTP remains unreliable and should only be used for recovery.
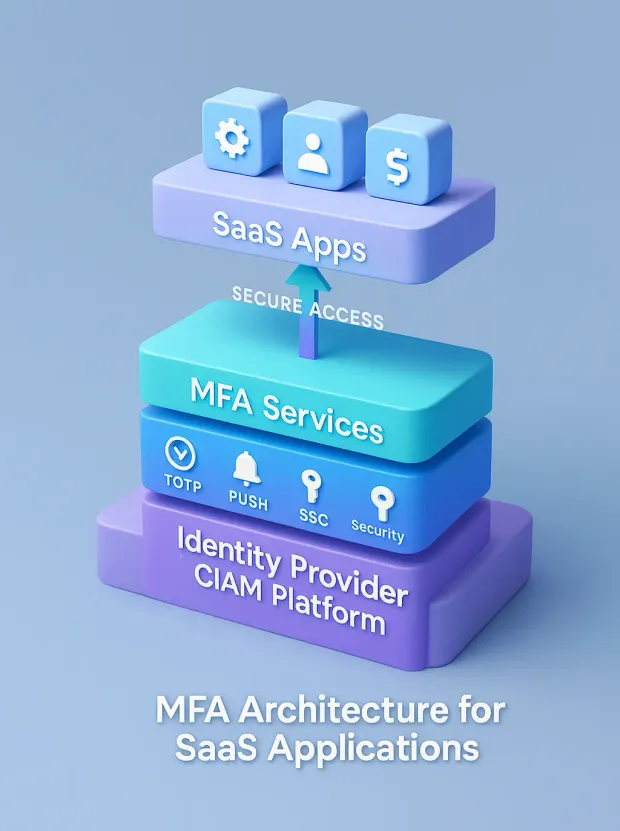
How SaaS Platforms Should Implement MFA
Designing MFA for a SaaS platform isn’t just adding a second factor it’s engineering an identity architecture that performs reliably across millions of users, multi-region deployments, complex tenants, high traffic, and unpredictable authentication patterns.
A poorly designed MFA architecture increases latency, introduces downtime risk, and disrupts user experience. A well-designed one strengthens security while staying nearly invisible to users.
Below is a structured approach to architecting MFA specifically for SaaS applications.
Before implementing MFA, teams should be clear on one key question: what is the objective of using multi-factor authentication? The objective is not just adding a second step—it is reducing account takeover probability, enforcing access assurance for privileged actions, and ensuring stolen passwords alone cannot unlock customer or tenant data.
Identity Layer: Your Foundation for MFA
Your identity layer determines what your MFA system can or cannot do.
A scalable identity layer should include:
-
Unified user store for all tenants
-
Attribute-based profiles to support risk checks
-
API-first identity operations
-
Session & token management for continuous authentication
-
Support for OIDC, OAuth 2.0, SAML, FIDO2/WebAuthn
This foundation is mandatory before implementing any strong authentication workflow.
Authentication Gateway: The Enforcement Layer
This gateway becomes the “traffic cop” between users and applications.
It should handle:
-
MFA trigger conditions
-
Device identification
-
Risk evaluation
-
Centralized login flows
-
Token issuance & refresh logic
A centralized gateway eliminates inconsistent MFA behavior across your product surfaces.
The MFA Orchestration Layer
This layer defines how MFA actually behaves especially in multi-tenant SaaS.
Capabilities needed:
-
Multiple MFA factors (OTP, TOTP, push, biometrics, WebAuthn, security keys)
-
Per-tenant policies
-
Per-role or per-action enforcement
-
Step-up MFA triggers (payment, admin actions, exports)
-
Fallback and recovery flows
This layer ensures strong security without overloading users with friction.
Learn more : Build User Workflows with No-code Orchestration Engine
Risk Engine: The Brain of Adaptive MFA
Static MFA isn't enough for SaaS. You need real-time risk decisioning.
Risk engine inputs should include:
-
Device identity
-
IP reputation
-
Geo-velocity
-
Browser fingerprint
-
Behavioral analytics
-
Login anomalies
-
Impossible travel
-
Known compromised credentials
The risk engine determines when MFA is needed, reducing unnecessary prompts.
Multi-Region Deployment & Latency Optimization
SaaS platforms with global users need ultra-low latency authentication.
Best practices:
-
Deploy MFA endpoints across multiple regions
-
Keep risk computations close to the user for speed
-
Cache low-risk decisions where possible
-
Avoid global synchronous database calls
MFA Recovery Architecture
Account recovery is the most overlooked part of MFA architecture and the #1 source of support tickets.
Your recovery stack must include:
-
Secure backup codes
-
Device re-enrollment flows
-
Phone/email fallback
-
Administrative override (with audit logs)
-
Fraud-resistant lost-device workflows
A secure and user-friendly recovery system reduces friction and improves retention.
Checklist: Best MFA Strategy for SaaS Platforms
Use this checklist as a blueprint to evaluate whether your MFA approach is modern, scalable, and SaaS-ready. Each item aligns with industry best practices used by leading CIAM and IAM vendors.
Security Requirements Checklist
-
MFA supports strong phishing-resistant methods (WebAuthn, FIDO2, passkeys).
-
Sensitive actions (admin, exports, payments) require step-up MFA.
-
Risk-based, adaptive policies evaluate IP, device, geo-velocity, behavior.
-
System defends against MFA fatigue, SIM swap, and OTP interception.
-
MFA logs include device history, anomalies, ATO attempts, and admin changes.
User Experience Checklist
-
Onboarding uses low-friction options like passwordless or push.
-
“Trusted device” and device binding reduce repeated challenges.
-
MFA enrollment is visual, mobile-friendly, and takes under 30 seconds.
-
Multiple MFA choices available (push, biometrics, passkeys, TOTP, fallback OTP).
-
Adaptive MFA ensures low-risk users glide through the login process.
Scalability Checklist
-
Multi-region MFA deployment ensures low latency for global tenants.
-
The risk engine can evaluate millions of events with minimal delay.
-
MFA is API-first and ready for integration across web, mobile, CLI, and partner apps.
-
Supports multi-tenant SaaS with per-tenant MFA policies.
-
High availability and failover protect login flows during outages.
Operational & Developer Checklist
-
Clear SDKs and APIs (JavaScript, iOS, Android, Node, Python, etc.).
-
Sandbox environment enables easy testing of MFA logic.
-
Centralized orchestration layer defines MFA flows without code rewrites.
-
Strong admin tooling for enrollment, resets, auditing, and compliance.
-
Monitoring + alerting catches abnormal patterns in real time.
Compliance & Governance Checklist
-
MFA methods align with PCI-DSS, SOC2, HIPAA, PSD2, GDPR standards.
-
Audit logs stored securely and retained per region-specific rules.
-
Fallback methods (email OTP, backup codes) are secure & compliant.
-
Roles and permissions are separated for admins, auditors, and operators.
Future-Proofing Checklist
-
Passwordless readiness: passkeys, WebAuthn device-bound credentials.
-
Continuous authentication models replace static sessions.
-
AI/ML-enhanced risk assessments detect subtle behavioral anomalies.
-
Support for emerging standards (FIDO2, CTAP, OIDC extensions).
-
Modular architecture allows adding new factors without re-engineering.
Like any security control, MFA has tradeoffs. The pros and cons of multi factor authentication depend on the factor type, recovery flows, and how aggressively challenges are enforced. When designed correctly, multi factor authentication benefits outweigh friction by reducing takeover risk, and the multi factor authentication advantages become even clearer in B2B SaaS where admin access and tenant data demand higher assurance.
Conclusion
Modern SaaS platforms live in an environment where security threats scale as quickly as user adoption. Passwords alone are no longer enough, and simple MFA while helpful cannot keep up with credential stuffing, phishing, session hijacking, and MFA fatigue attempts targeting large user bases.
That’s why the most successful SaaS companies are shifting toward a multi-layered MFA strategy that blends strong authentication (security keys, passkeys, biometrics), user-centric experiences (push, passwordless, device binding), and intelligent decisioning (adaptive MFA powered by risk signals and behavioral analytics).
This is where the value becomes measurable. It’s not hard to see how MFA improves security over single-factor authentication: even if an attacker steals a password, MFA blocks access by requiring an additional factor they don’t control. This is the foundational reason why multi factor authentication is important for SaaS platforms with customer data, tenant resources, billing access, and admin consoles.
The result? A login system that is secure by design, frictionless by default, and capable of supporting millions of global customers without slowing them down.
This is the architecture that keeps users safe and keeps your product experience competitive.
Ready to Modernize MFA for Your SaaS Platform?
If you want stronger security, higher conversion rates, and a future-proof authentication experience, LoginRadius can help.
Book a personalized demo with our identity experts. Learn how global SaaS companies scale MFA with LoginRadius. Your users deserve secure, effortless access and your platform deserves an MFA foundation that can grow with you.
FAQs
Q: What is the best MFA strategy for SaaS platforms?
A: A layered approach works best: phishing-resistant factors (security keys, passkeys), push MFA with number matching, and adaptive MFA that triggers challenges only when risk is high.
Q: Which MFA methods should SaaS platforms avoid?
A: Avoid relying on SMS OTP as the primary factor—it's vulnerable to SIM swaps, SS7 attacks, and OTP interception. Use it only as a fallback recovery method.
Q: Why is adaptive MFA important for SaaS platforms?
A: Adaptive MFA evaluates risk signals like device, IP, behavior, and location to show MFA only when needed reducing friction while strengthening security for global SaaS users.
Q: How can SaaS platforms reduce MFA friction without weakening security?
A: Use passwordless options (passkeys/biometrics), push MFA, device binding, and risk-based policies to minimize prompts while still blocking high-risk attempts.
Q: What’s the strongest MFA factor for SaaS admin and privileged accounts?
A: Security keys (FIDO2/WebAuthn) offer the strongest protection with phishing-resistant, hardware-rooted authentication that cannot be intercepted or replayed.




