Introduction
Passwordless authentication sounds like an easy win for a B2B SaaS product. Fewer passwords. Less friction. Better security. On paper, it should improve onboarding and retention at the same time.
Your engineering team ships it and the signups slow down, invite flows break, and first-time users hesitate. Not because passwordless is flawed, but because in B2B SaaS, authentication doesn’t live in isolation. It sits inside onboarding, org creation, invites, and those early product moments that decide whether a user continues or drops off.
Don’t treat passwordless authentication for B2B SaaS as a login upgrade, it is an onboarding decision. A magic link that feels seamless for one user can create friction for another. A passkey prompt that works for returning users can feel premature during signup.
Did you know that: churn often starts earlier than expected? Not months later but during onboarding. A confusing signup step, a clunky invite flow, or an authentication prompt too early in the journey: each of these can have a major impact on activation.
That’s why passwordless is not just a security upgrade. It must be part of your customer retention strategy. Done right, it reduces onboarding friction, speeds up access, and improves activation. Done poorly, it increases drop-offs especially in multi-tenant B2B SaaS environments with different user journeys.
This guide focuses on how to implement passwordless authentication in a B2B SaaS product without breaking onboarding, and how to use it to improve activation and reduce churn.
In B2B SaaS, Onboarding Friction Can Directly Lead to Churn
Most teams think churn happens weeks later, after pricing, features, or lack of engagement. That’s only half the story. In B2B SaaS, churn often starts during onboarding. Quietly.
A user signs up. They hit a confusing step. Maybe the invite link doesn’t behave as expected. Maybe authentication takes longer than it should. Maybe they’re asked to do too much before they see any value. They don’t complain. They just don’t come back.
If a user doesn’t complete onboarding smoothly, they have never really become a user. Everything that follows engagement, retention, and expansion depends on that first experience working without friction. Each of these paths has different expectations. But many products treat them the same, especially at the authentication layer. That’s where friction builds.
This is where onboarding optimization and customer retention strategy start overlapping. Reduce friction at the right points, and activation improves. Activation improves, and churn naturally drops. Not because you forced users to stay, but because you made it easier for them to start.
So before talking about how to implement passwordless authentication, it’s important to understand this: onboarding friction is not just a UX issue. It’s a retention problem in disguise.
Passwordless Authentication as a Customer Retention Strategy
Most teams approach passwordless authentication as just a security upgrade. Stronger login, fewer credentials, less exposure to phishing. All true. But that’s not where the biggest impact shows up in a B2B SaaS product. It shows up in onboarding.
Every extra step between “sign up” and “first successful login” increases the chance of drop-off. Password creation, verification emails, resets, MFA prompts each one adds friction. Remove or streamline them, and users move faster. They reach value sooner. That alone shifts activation.
Passwordless authentication for B2B SaaS doesn’t just remove passwords it reshapes the flow. A magic link can take a user from email to product in seconds. A passkey can turn the second and third login into a near-instant action. That speed matters more than it sounds when you’re trying to get users through their first meaningful interaction.
A surprising pattern we’ve seen: improving login speed often improves retention indirectly. Not because users care about authentication itself but because it removes interruptions at key moments. They can return to the product without friction. They don’t get stuck resetting passwords. They don’t abandon sessions halfway through.
Trust plays a role too. Phishing-resistant authentication methods, backed by standards like FIDO2 authentication and WebAuthn authentication, reduce the risk of compromised accounts. Users may not see the underlying cryptography, but they notice when things feel secure and consistent.
But there’s a catch. Apply passwordless blindly, and the gains disappear. A passkey prompt too early in onboarding can feel like friction. A poorly designed magic link flow can confuse users switching devices. Strong authentication needs to match the user’s stage, not just the system’s preference.
Get that balance right, and authentication stops being a hurdle. It becomes part of a smoother path from signup to activation and from activation to long-term retention.
Start With Onboarding Flows, Not Authentication Methods
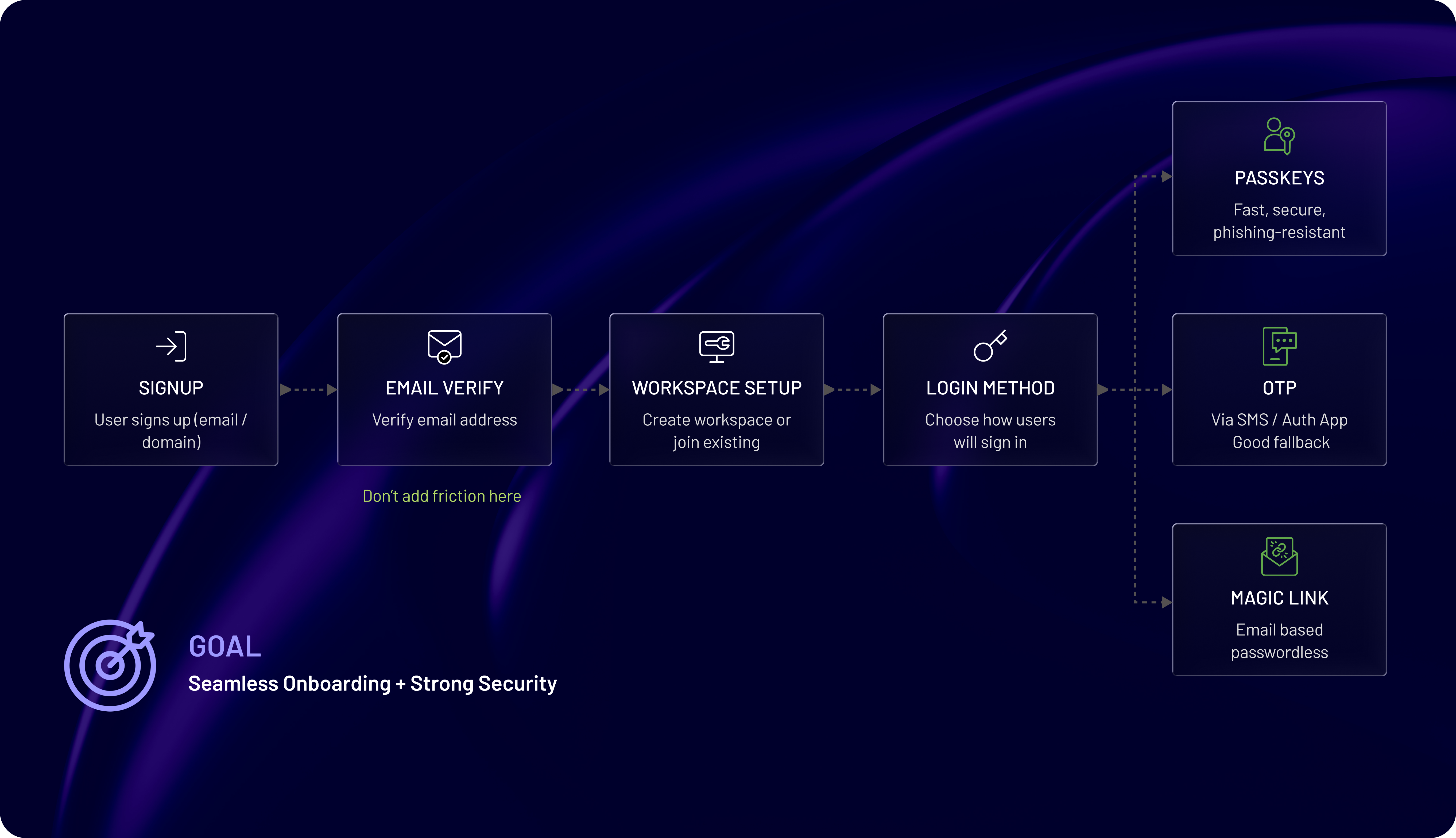
It’s tempting to begin with the method. Passkeys, magic links, OTPs pick one, integrate it, move on. That approach looks efficient. It usually backfires. They design authentication first and try to fit onboarding into it later. In B2B SaaS, that order creates friction because onboarding is not a single path.
Different users enter your product in different ways. The first user creates an organization. Invited teammates then join through links. Returning users just want quick access. Enterprise users may arrive through SSO. These are not variations of the same flow. They are different states with different expectations. Each of these states has a different tolerance for friction.
-
A first-time user is still exploring. They want speed and clarity. A long or unfamiliar authentication step here increases drop-off.
-
An invited user expects continuity, clicks the link, lands inside the right workspace, and gets started. Any extra step feels like a break in flow.
-
A returning user values speed above all. This is where passkeys or fast passwordless login shine.
-
Admins and sensitive actions may require stronger verification, but even there, timing matters.
We’ve observed that onboarding issues often get blamed on UX or product complexity, when the real problem lies in authentication flow mismatches. The method is not wrong, but the placement is. This is why onboarding optimization starts with mapping flows how a new organization is created, how users are invited and join, how returning users authenticate and how enterprise users transition into SSO
Once these paths are clear, choosing passwordless authentication methods becomes easier. You’re no longer guessing. You’re aligning authentication with real user behavior.
That shift changes everything. Instead of forcing users into a predefined auth model, the system adapts to the way they actually enter and use the product. And that’s where friction starts dropping.
Handling Multi-Tenant and Organization-Based Authentication
This is where many otherwise solid implementations fall apart. Login works. Security looks fine. But users still struggle to get into the right place.
In B2B SaaS, authentication is not just about verifying a user. It’s about placing them inside the correct organization, with the right context, at the right time. Teams separate authentication from tenant routing. The result? Users log in successfully but land in the wrong place or nowhere at all. That confusion shows up as support tickets, not clear errors.
To simplify: A user doesn’t just “log in.” They log into a workspace, a team, an account, or something tied to an organization. If that mapping is unclear or inconsistent, onboarding breaks even if authentication itself is smooth. Most onboarding friction in B2B SaaS comes from three moments:
-
creating the first organization
-
accepting an invitation
-
returning to the correct workspace
Each of these requires different logic.
-
The first user is straightforward; they create the organization and become the initial admin. But even here, small issues can appear. Duplicate org creation, unclear naming, or delays between signup and workspace access. These slow down activation.
-
Invited users expect a seamless experience. Click the link, land inside the correct organization, and start working. If they’re asked to authenticate separately, choose an org manually, or repeat steps, the flow feels broken. This is where invitation-based onboarding needs to stay tightly connected to authentication.
-
Returning users introduce another layer. They may belong to multiple organizations. The system needs to recognize them, route them correctly, and keep the experience consistent across devices. Tenant-aware authentication becomes critical here.
-
And then there’s enterprise. Domain-based discovery, SSO handoff, and organization mapping these flows need to integrate cleanly with passwordless authentication. Otherwise, enterprise onboarding becomes a separate, fragmented experience. So multi-tenant authentication is not just a backend concern. It directly impacts onboarding quality.
When this layer works, users don’t think about it. They click, they log in, and they’re exactly where they expect to be. That’s the outcome you want.
Choosing the Right Passwordless Method for Each Flow
This is where most implementations get oversimplified. One method gets picked. It gets applied everywhere. It works in some places and creates friction in others.
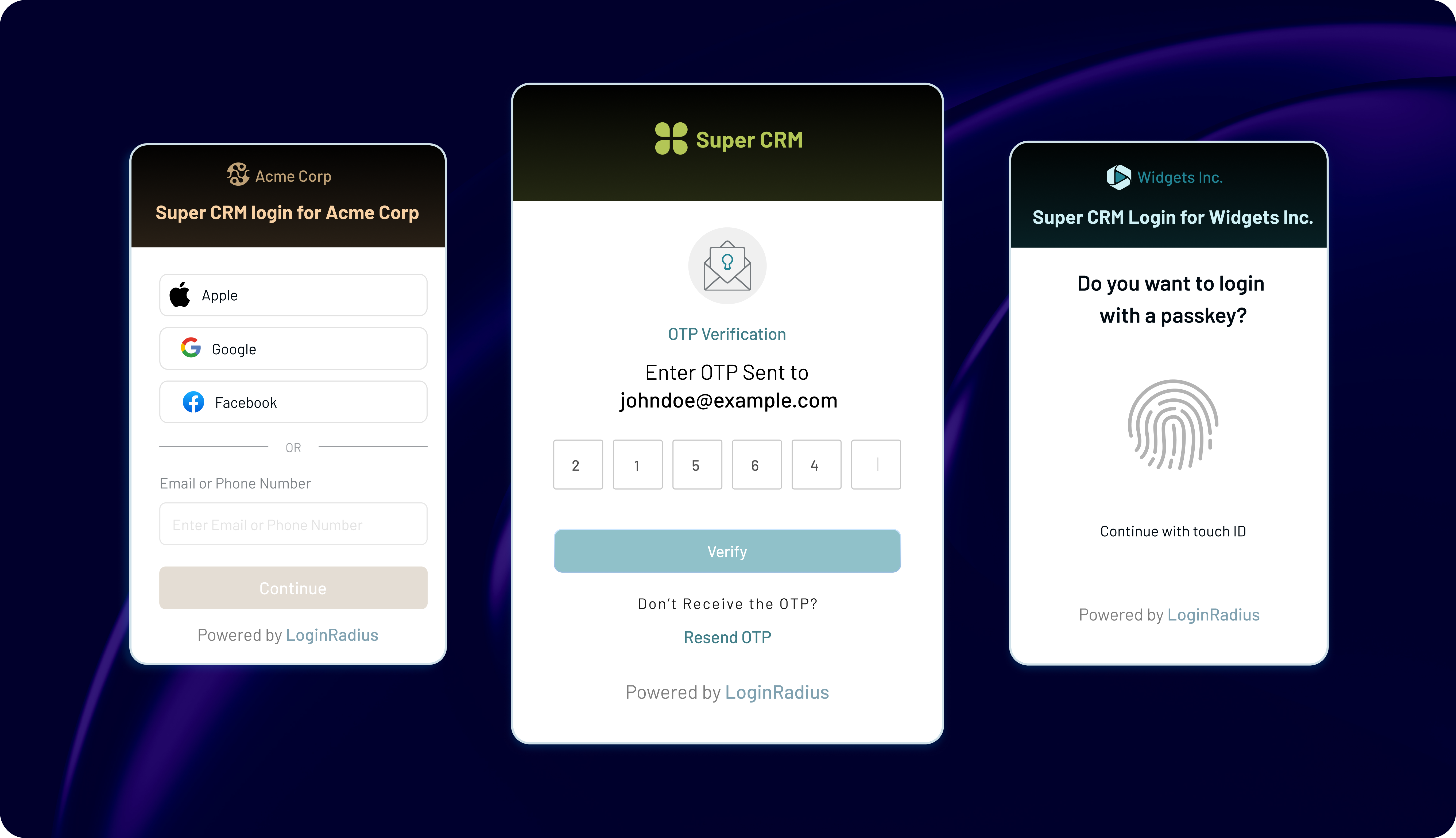
Passwordless authentication methods are not interchangeable. Each one carries a different balance of speed, security, and user expectation. The goal is not to find the “best” method. It’s to match the method to the moment.
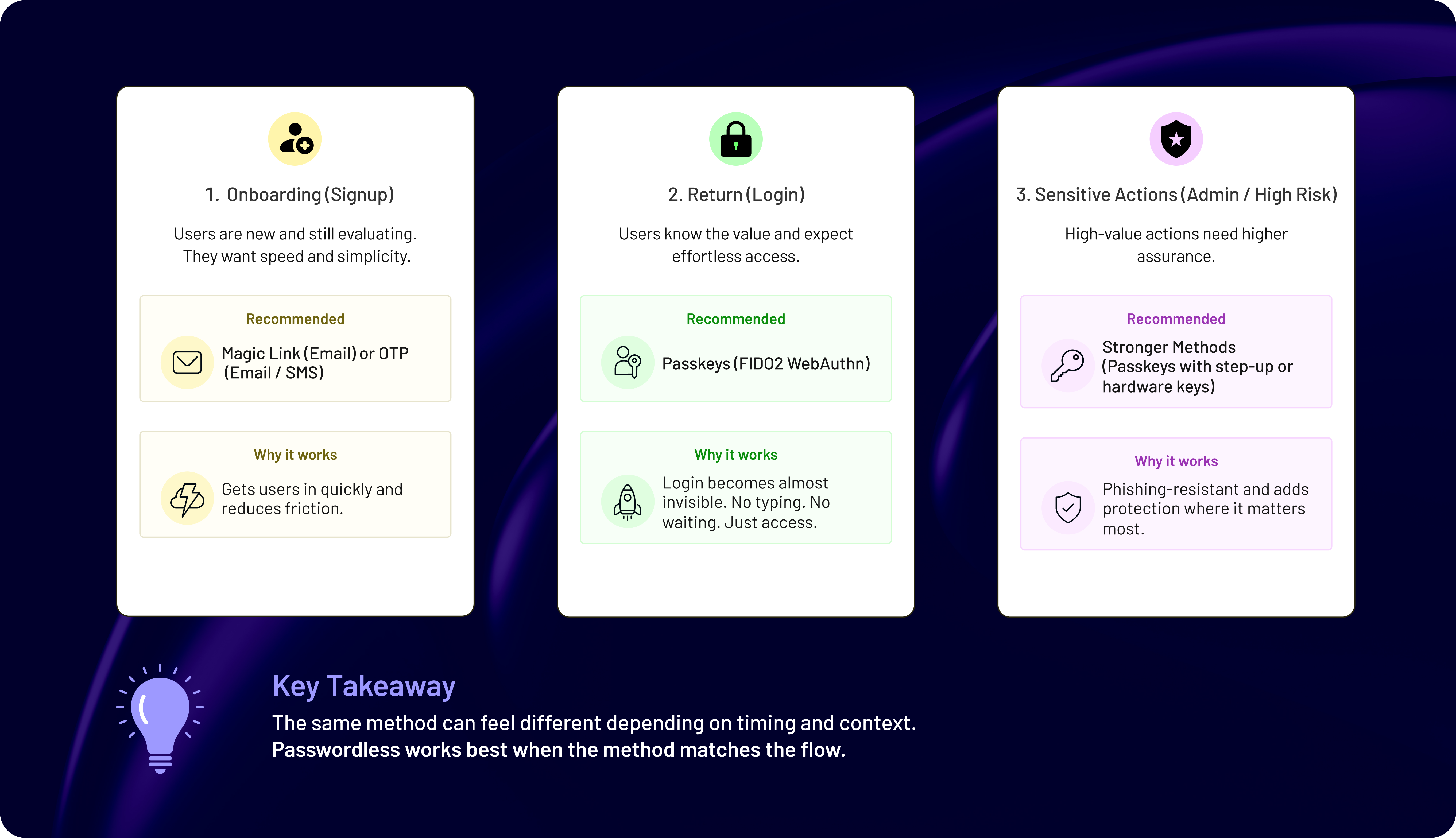
Different onboarding stages need different levels of commitment.
-
During signup, users are still evaluating. They want speed. A magic link or a lightweight OTP flow works well here because it removes password creation and gets them inside quickly. Add too much complexity at this stage, and drop-off increases.
-
Once users return, the expectation shifts. They’ve already seen value. Now they care about speed and convenience. This is where passkeys and FIDO2 authentication become powerful. Login becomes almost invisible. No typing. No waiting. Just access.
-
Admin actions and sensitive operations are different. This is where stronger, phishing-resistant authentication makes sense. Hardware-backed methods or stricter verification steps can be introduced without hurting the overall experience because the context justifies it.
The same method can feel completely different depending on timing. A passkey prompt during a repeat login feels smooth. The same prompt during first-time onboarding can feel like friction. A magic link works well on one device but can confuse users switching between devices mid-flow.
Teams optimize for the method, not the journey. They choose passkeys because they’re modern, or OTPs because they’re familiar, without mapping where each one fits best. That’s when onboarding starts feeling inconsistent. Passwordless works best when users don’t notice it. That only happens when the method matches the flow.
Designing Frictionless Signup Without Weakening Security
Signup is where intent is highest, and patience is lowest. If this step feels slow or confusing, users don’t stick around long enough to care about your features. The goal of signup is not to verify everything. It’s to get the user to their first meaningful action as quickly as possible without opening security gaps.
Most friction doesn’t come from a single step. It comes from stacking too many small steps together with email verification, password creation, confirmation screens, extra fields, MFA prompts. Each one feels reasonable. Together, they slow everything down.
Passwordless authentication can remove a big chunk of that friction. A magic link or lightweight OTP flow can take users from email to product in seconds. No passwords. No resets. Just access. But speed alone is not enough.
A surprising pattern we’ve seen: teams optimize for faster signup but overlook what happens right after. Users get in quickly but land in a confusing state. No clear workspace. No guidance. No connection between signup and actual product use. That gap hurts activation more than slow signup.
Security needs to be present, but placed carefully. Early-stage users are not ready for complex steps. Stronger controls like stricter verification or phishing-resistant authentication can be introduced later, when users perform sensitive actions or return to the product.
There’s also the question of abuse. Fast signup flows can attract bots or fake accounts if not handled properly. So while reducing friction, you still need basic verification to confirm identity, rate limiting and bot protection and controlled org creation logic. The balance matters. Too much friction, and users drop off. Too little control, and you introduce risk.
So the focus should be: reduce unnecessary steps at signup, connect signup directly to a usable product state, delay heavier authentication until it makes sense and keep security aligned with user intent, not forced upfront
When signup feels smooth and purposeful, users move forward. That’s where onboarding really begins.
Implementing Passwordless Without Breaking Existing Users
Rolling out passwordless in a live B2B SaaS product is different from building it from scratch. You already have users, sessions, credentials, and habits. Change too much too fast, and things break not technically, but experientially.
Existing users don’t want a new authentication system. They want continuity. If login suddenly behaves differently, or they’re forced into a new method without context, friction shows up immediately.
Don’t treat passwordless authentication implementation like a clean switch that you can turn on, phase out passwords, and move forward. In reality, rollout needs to be gradual.
Start by introducing passwordless as an option, not a replacement. Let users adopt it naturally during login or through prompts after successful sessions. This reduces resistance and avoids confusion.
Account linking is another critical piece. A user might already have an account tied to email and password. When they use a magic link or passkey for the first time, the system needs to recognize and merge that identity correctly. If not, duplicate accounts or access issues start appearing.
Migration problems don’t show up immediately. They appear when users switch devices, forget how they signed up, or try a different login method later. That’s when inconsistencies surface.
Backward compatibility matters too. Some users will stay on older methods longer especially in enterprise environments where device policies or workflows differ. Removing fallback options too early can block access rather than improve it.
Then there’s communication. Not long explanations just clear cues. What changed, what users should do, and what to expect next. Without that, even a well-designed flow can feel unfamiliar.
This approach keeps onboarding intact while gradually improving the authentication experience. When done right, users don’t feel a disruption. They just notice that login gets easier over time.
Using No-Code CIAM to Optimize Onboarding and Reduce Churn
At some point, the challenge stops being “what should we build” and becomes “how fast can we actually ship this without breaking things.”
That’s where no-code or low-code CIAM starts making a difference.
Implementing passwordless authentication for B2B SaaS is not just about login flows. It involves onboarding logic, org creation, invite handling, policy enforcement, recovery, and integrations. Doing all of this from scratch slows teams down and introduces inconsistencies.
A no-code CIAM platform changes that dynamic. Instead of stitching together custom logic across multiple systems, you get pre-built workflows that can be configured and adjusted without heavy engineering effort. The biggest advantage is not just speed, it's flexibility.
Onboarding flows evolve. What works today may need adjustment next month. Maybe invite flows need simplification. Maybe signup needs fewer steps. Maybe authentication methods need to change based on user behavior. With traditional implementations, each change requires development cycles. With no-code CIAM, those adjustments can be made faster and tested more easily.
Teams spend a lot of time building authentication, but much less time improving it after launch. That’s where friction stays. Not because the system can’t change but because changing it is slow.
Automation plays a role here, too. Identity workflow automation helps keep onboarding consistent as the product scales. User provisioning, role changes, policy updates these can be handled without manual intervention. That reduces operational overhead and prevents small inconsistencies from turning into larger problems.
There’s also a developer productivity angle. Instead of managing authentication logic across services, developers can rely on centralized identity workflows. Less duplication. Fewer edge cases. More focus on core product features.
And then there’s visibility. With built-in analytics, teams can see where users drop off during onboarding. Not just guesses, but actual data that shows how to optimize your onboarding.
So, no-code CIAM supports passwordless implementation in three ways:
-
faster rollout of authentication and onboarding flows
-
easier iteration as user behavior evolves
-
reduced friction through automation and consistency
It doesn’t replace good design decisions. But it makes it much easier to apply them and adjust when needed. That’s what helps turn a working onboarding flow into a scalable one.
Measuring Success: From Onboarding to Retention
Once everything is in place, the question shifts: From “is passwordless working?” to “is passwordless actually improving outcomes?”
Because smooth login alone doesn’t guarantee better onboarding. And faster onboarding doesn’t always translate to retention unless you’re measuring the right things.
You don’t need dozens of metrics. You need a few signals that reflect how users move from signup to real usage.
Start with activation. How many users complete onboarding and reach their first meaningful action? If passwordless authentication is reducing friction, this number should improve. If it doesn’t, the issue is likely somewhere in the flow, not the method itself.
Then look at the invitation acceptance rate. In B2B SaaS, growth depends on teams, not individuals. If invited users are not completing onboarding smoothly, it affects expansion. Authentication plays a role here, especially in how seamlessly invite flows connect to login.
Login success rate is useful but it can be misleading on its own. A high success rate doesn’t always mean a smooth experience. Users might retry multiple times before succeeding. That friction doesn’t always show up unless you look deeper.
We’ve also seen that recovery behavior often reveals more than login data. If users frequently fall back to recovery flows, something in the primary authentication path is not working as expected. That’s where onboarding optimization should focus.
Then there’s drop-off. Where do users stop progressing? During signup? After email verification? During the first login? These points matter more than overall conversion numbers.
For retention, look beyond day-one metrics. Are users returning easily? Are they logging in without friction? Are they staying active after the first session? Passwordless authentication should make returning to the product effortless. If it doesn’t, something is off.
When they move in the right direction, you know the system is doing more than just authenticating users. It’s helping them stay.
Common Mistakes That Break Onboarding and Increase Churn
Even well-planned implementations can drift off course. Not because the approach is wrong but because small decisions compound over time.
Here’s where teams usually go wrong. They optimize one part of the flow in isolation. Better login. Faster signup. Stronger security. Each improvement makes sense on its own, but the overall experience starts feeling inconsistent.
-
Forcing the same authentication method everywhere is one of the most common issues. Passkeys, for example, work great for returning users. Push them too early in onboarding, and they feel like friction. The problem isn’t the method it’s the timing.
-
Invite flows are another weak spot. In B2B SaaS, onboarding often depends on invitations. If users click an invite and land in a separate authentication step without context, the flow breaks. That disconnect shows up as drop-off, not errors.
-
Recovery paths quietly undermine everything. Teams focus on primary login flows and leave fallback options loosely defined. When users hit those paths, the experience feels inconsistent and sometimes less secure.
-
Then there’s account fragmentation. Without proper linking between authentication methods, users can end up with duplicate accounts. One created through email signup, another through a magic link or passkey. That confusion surfaces later, usually during login or access issues.
-
Removing passwords too early: while the goal is to go passwordless, forcing a complete switch before users and systems are ready can block access. Especially in enterprise environments, where device constraints and workflows vary.
-
And finally lack of iteration. Teams launch passwordless authentication and move on. No adjustments, no refinements based on user behavior. Over time, small friction points stay unresolved.
None of these are major failures on their own. But together, they create friction that slows onboarding and increases churn.
Avoiding them is less about perfect design and more about paying attention to how users actually move through the system.
Balancing Security and User Experience in B2B SaaS Authentication
Security and user experience often get framed as trade-offs. Make authentication stronger, and you add friction. Make it smoother, and you reduce control. That thinking holds teams back.
In practice, the balance is not about choosing one over the other. It’s about applying the right level of security at the right moment.
Not every action needs the same level of verification. A user signing up for the first time does not need the same controls as an admin changing critical settings. Treat them the same, and the experience feels either too heavy or too weak.
Modern passwordless authentication methods allow you to adjust security without constantly interrupting users. Passkeys and FIDO2 authentication provide strong, phishing-resistant authentication without adding visible steps during repeat login. Users move faster, while the system maintains a higher level of assurance.
Friction often comes from inconsistency, not strength. Users are willing to go through additional steps when the context makes sense. What frustrates them is when similar actions behave differently, or when security appears randomly.
That’s where policy design plays a role. Instead of applying static rules everywhere, authentication should respond to context user role and access level, device trust and environment and sensitivity of the action
This is where concepts like step-up authentication and conditional access come into play. A user might log in smoothly but face stronger verification when performing high-risk actions. That keeps onboarding simple while maintaining control where it matters.
There’s also a perception layer. Strong authentication builds trust when it feels intentional. If users understand why a step is required, they’re less likely to see it as friction.
When this works, users don’t feel like they’re navigating security. They just feel that the product works smoothly, reliably, and safely. That’s the point where authentication stops being a barrier and starts supporting the experience.
Final Thoughts: Build Authentication That Supports Onboarding, Not Slows It Down
By now, one thing should be clear: passwordless authentication for B2B SaaS is not just about removing passwords. It’s about shaping how users enter, experience, and return to your product.
The methods are already there. Passkeys, magic links, and FIDO2 authentication: they’re proven and widely supported. The real difference comes from how you apply them across onboarding flows, organization logic, and user journeys.
The teams that get this right don’t chase the “most secure” or the “most modern” method first. They focus on flow. They map how users sign up, how teams join, how access evolves. Then they apply authentication in a way that fits those paths.
The best implementations are the ones your users barely notice. Signup feels quick. Invites work without friction. Login becomes effortless over time. Security is there but it doesn’t interrupt the experience unless it needs to.
In contrast, when authentication is layered on without that context, it creates small points of resistance. Nothing dramatic. Just enough to slow onboarding, reduce activation, and quietly impact retention.
So the goal isn’t just to go passwordless. It’s to build an authentication system that adapts to different onboarding flows, supports multi-tenant and organization-based access, scales without adding operational overhead, and improves activation and reduces churn over time. That’s what makes it sustainable.
Ready to Implement Passwordless Without Breaking Your Onboarding?
If you’re looking to move fast without rebuilding your entire identity stack, this is where the right platform makes a difference.
Start building a frictionless, secure onboarding experience today. Book a demo and see how LoginRadius can help you scale passwordless authentication the right way.
FAQs
Q: What is passwordless authentication for B2B SaaS?
A: Passwordless authentication removes passwords and uses methods like passkeys, magic links, or OTPs to verify users. In B2B SaaS, it must also handle org-based access, invites, and multi-tenant flows. The goal is secure, low-friction onboarding and login.
Q: How do you implement passwordless authentication without breaking onboarding?
A: Start by mapping onboarding flows first signup, invites, and returning users. Then apply the right authentication method to each stage instead of using one approach everywhere. Roll it out gradually and monitor drop-offs.
Q: Which passwordless methods work best for B2B SaaS onboarding?
A: Magic links and OTPs work well for initial signup due to low friction. Passkeys and FIDO2 methods are better for returning users and stronger security. Most SaaS products use a combination based on user flow.
Q: How does passwordless authentication reduce churn?
A: It removes login friction, speeds up onboarding, and reduces password-related issues like resets. Faster access improves activation rates, which directly impacts retention. Less friction early = fewer users dropping off.
Q: What are the biggest challenges in passwordless onboarding?
A: Common issues include broken invite flows, poor account linking, and forcing strong methods too early. Multi-tenant routing and recovery flows also create friction if not handled properly. Most problems come from flow design, not the method itself.
Q: Can no-code CIAM help with passwordless implementation?
A: Yes, no-code CIAM platforms speed up implementation and allow teams to adjust flows without heavy engineering. They help automate identity workflows, reduce inconsistencies, and improve onboarding over time.
Q: How do you balance security and user experience in passwordless flows?
A: Apply stronger authentication only when needed like admin actions or sensitive access. Keep signup and early onboarding simple. Consistency across flows matters more than adding extra steps everywhere.



