Clerk has earned strong adoption among modern development teams by making authentication fast to implement and easy to embed into frontend-heavy applications. Its prebuilt UI components, clean developer experience, and quick time-to-value make it especially attractive for startups and small teams building consumer-facing products. For basic sign-up, sign-in, and session management, Clerk does exactly what it promises.
However, as applications mature, identity requirements tend to expand beyond simple authentication. Teams begin to support multiple customer segments, introduce B2B or partner use cases, and face stricter security, compliance, and reliability expectations. At this stage, many organizations discover that Clerk functions more like an authentication layer than a full customer identity and access management (CIAM) platform. Limitations around MFA depth, federation, fraud detection, orchestration, and enterprise controls can quickly become blockers rather than trade-offs.
This is typically the inflection point where teams start evaluating Clerk alternatives. Not because Clerk “fails,” but because their identity needs now demand advanced MFA, adaptive and risk-based security, scalable architecture, and support for complex customer and partner identity journeys. In this guide, we examine what to look for in a CIAM platform and compare the top Clerk alternatives to help teams choose a solution that can scale securely alongside their business.
Evaluation Criteria: What Makes a Great CIAM Platform
Choosing a Clerk alternative requires looking beyond surface-level authentication features and evaluating whether a platform can support long-term customer identity needs. Below, we break down the most important CIAM evaluation criteria, with each dimension explained in depth to reflect real-world scaling, security, and architectural considerations.
Use Case Fit: CIAM vs Workforce vs B2B/Partner Identity
A foundational question when evaluating any identity platform is what problem it was designed to solve. Some tools are optimized for workforce IAM, others for lightweight developer authentication, and only a subset are purpose-built for customer identity. CIAM platforms must handle external users at scale, unpredictable traffic patterns, and a wide variety of customer journeys without exposing internal IAM assumptions.
As products evolve, identity use cases often expand into B2B SaaS, partner portals, and multi-tenant organizations, where requirements such as organization hierarchies, delegated administration, and role-based access become critical. Clerk works well for straightforward consumer authentication, but it provides limited native support for these more complex identity models. Teams building beyond single-tenant or purely consumer use cases often need a CIAM platform explicitly designed for these scenarios.
Security and User Experience
In CIAM, security and user experience are inseparable. Strong security controls that introduce unnecessary friction can hurt conversion and retention, while overly permissive authentication increases the risk of account takeover and fraud. A mature CIAM platform must allow teams to apply the right level of security at the right time, rather than enforcing static rules for every user and every login.
Key capabilities include advanced MFA options such as push-based authentication, TOTP, and out-of-band verification, as well as adaptive and risk-based authentication that responds to device signals, behavior anomalies, or location changes. Clerk offers basic MFA, but its limited factor support and lack of advanced risk controls can restrict how teams evolve their security posture. CIAM platforms should enable stronger protection without forcing blanket friction across all users.
Architecture, Scalability, and Reliability
Customer identity is core infrastructure. When authentication or identity services fail, users cannot access applications, leading to immediate business impact. For this reason, CIAM platforms must be built on cloud-native, highly available architectures that can handle sudden spikes in traffic, seasonal demand, and global user bases.
Beyond raw scale, architecture must also support multi-tenant organizations, federation, and extensibility without brittle custom workarounds. Teams should look for clearly defined SLAs, resilient APIs, and proven performance at scale. Tools that perform well for early-stage applications may struggle as traffic grows or identity flows become more complex, making architectural maturity a key differentiator when evaluating Clerk alternatives.
Data Residency and Compliance
As applications expand across regions and industries, data handling and privacy requirements become increasingly complex. Many organizations must comply with regional regulations, customer contractual requirements, or industry standards that dictate where identity data is stored and how it is managed.
A strong CIAM platform should support regional data residency options, along with built-in privacy and consent management features such as versioning, audit trails, and user preference tracking. These capabilities are often limited or entirely absent in developer-first authentication tools but become essential for enterprises, regulated industries, and global deployments. CIAM platforms must be able to evolve alongside changing compliance expectations without forcing architectural redesigns.
Developer Experience and Migration Effort
Developer experience remains critical, especially when teams are migrating away from an existing authentication solution like Clerk. CIAM platforms should provide well-documented APIs, SDKs, and clear integration patterns that allow developers to implement identity without excessive frontend coupling or proprietary abstractions.
Equally important is the migration path. Teams should evaluate how easily users, credentials, and sessions can be migrated, as well as the level of tooling and support available during transition. Responsive support, clear documentation, and proven migration strategies can significantly reduce risk and downtime. The best CIAM platforms balance flexibility with structure, giving developers control while minimizing long-term maintenance overhead.
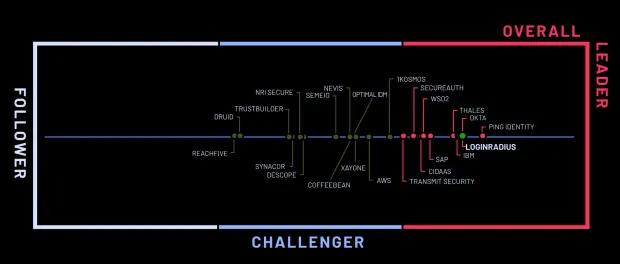
Top 7 Clerk Alternatives to Consider in 2026
Below are the most commonly evaluated alternatives when teams reassess Clerk and look for a more comprehensive CIAM foundation as their applications scale.
1. LoginRadius
LoginRadius is a CIAM platform designed specifically for high-volume consumer, B2B SaaS, and partner identity use cases. Unlike frontend-first authentication tools, LoginRadius is designed to support complex identity journeys, advanced security controls, and enterprise-scale reliability without requiring teams to assemble multiple services.
Where LoginRadius Works Especially Well
CIAM-native architecture built for scale : LoginRadius is built for customer identity from the ground up, with cloud-native multi-region deployments, high-availability SLAs, and native support for multi-tenant organizations. These capabilities are foundational rather than inherited from workforce IAM models.
Advanced MFA and adaptive security out of the box : Native push, TOTP, and out-of-band MFA via the LoginRadius Authenticator enable strong security without degrading UX. Adaptive and risk-based controls allow teams to apply step-up authentication only when risk is detected.
Enterprise-grade federation and identity orchestration : Support for SAML, OIDC, and multi-IDP federation enables enterprise and partner identity use cases. Visual, low-/no-code orchestration tools allow teams to design and iterate on identity journeys without engineering bottlenecks.
Modern CIAM security and experience layer : Built-in fraud detection, breach screening, privacy policy versioning, and AI-powered theming help balance security, compliance, and user experience at scale.
Ideal For
-
Consumer brands operating at high traffic volumes
-
B2B SaaS platforms with multi-tenant identity and delegated administration
-
Partner portals and ecosystem-driven platforms
-
Organizations requiring advanced MFA, federation, and compliance controls
-
Teams expecting identity complexity to grow over time
2. Transmit Security
Transmit Security is an identity security platform commonly evaluated by organizations with high fraud exposure that need advanced risk-based authentication and behavioral analysis layered into their CIAM strategy.
Where Transmit Security Performs Well
-
Risk-based authentication and fraud intelligence : Uses behavioral biometrics, device fingerprinting, and contextual signals to assess login risk in real time.
-
Strong account takeover prevention : Focuses heavily on detecting anomalous behavior, bot activity, and credential abuse across authentication flows.
-
Composable security architecture : Can be integrated alongside existing identity providers to enhance security posture without replacing core systems.
CIAM Fit Analysis : Transmit Security works best where fraud mitigation and risk intelligence are the primary drivers. It is less focused on full CIAM lifecycle management, UX orchestration, or multi-tenant identity modeling, which often require complementary platforms.
Ideal For
-
Financial services and fintech platforms
-
High-risk consumer applications
-
Organizations prioritizing fraud prevention and adaptive authentication
Trade-Offs
-
Not a full CIAM platform on its own
-
Limited native identity orchestration and UX management
-
Often requires pairing with another CIAM or authentication system
3. Auth0 (Okta Customer Identity Cloud)
Auth0 is a developer-oriented CIAM platform commonly evaluated by teams outgrowing the customization limits of legacy CIAM or cloud-native IAM tools.
Where Auth0 Performs Well
-
Developer-first extensibility : Rules, Actions, hooks, and SDKs provide engineers deep control over tokens, claims, and authentication logic.
-
Large integration ecosystem : A broad marketplace of connectors for analytics, fraud prevention, marketing platforms, and enterprise IdPs.
-
B2B SaaS enablement : Supports SAML, OIDC, RBAC, enterprise SSO, and tenant-level configuration.
CIAM Fit Analysis : Auth0 works best where engineering teams want maximum programmability. At very large consumer scale, cost growth, rate limits, and operational complexity can become friction points.
Ideal For
-
Early-stage to mid-market SaaS companies
-
Engineering-led organizations
-
Products with heavy third-party integrations
Trade-Offs
-
Pricing scales aggressively with MAUs and extensibility usage
-
Rate limits can affect high-volume consumer traffic
-
Long-term CIAM logic ownership stays with engineering
4. Microsoft Entra ID (External ID)
Microsoft Entra External ID (formerly Azure AD B2C) is often evaluated by organizations already standardized on Microsoft infrastructure and security tooling.
Where Microsoft Entra External ID Performs Well
-
Microsoft ecosystem integration : Native alignment with Azure services, Entra ID, and Microsoft security and compliance tooling.
-
Baseline CIAM capabilities : Supports customer authentication, social login, and federation for straightforward identity scenarios.
-
Enterprise familiarity : Appeals to IT teams already managing Microsoft-based identity environments.
CIAM Fit Analysis: Originally derived from workforce IAM concepts, Entra External ID can struggle with the UX flexibility and rapid iteration required for consumer-facing CIAM use cases.
Ideal For
-
Azure-first organizations
-
Enterprises with existing Microsoft identity investments
-
Use cases with stable, low-variation identity flows
Trade-Offs
-
Complex custom policy management
-
Limited consumer-grade UX customization
-
Identity changes often require IT-heavy workflows
5. Amazon Cognito
Amazon Cognito is a cloud-native authentication service commonly considered by teams building applications entirely within the AWS ecosystem.
Where Amazon Cognito Performs Well
-
AWS-native integration : Tight alignment with AWS services such as IAM, Lambda, API Gateway, and Amplify.
-
Core authentication coverage : Supports user pools, identity pools, federation, and basic MFA.
-
Infrastructure alignment : Fits well for teams standardizing fully on AWS tooling.
CIAM Fit Analysis : Cognito provides foundational authentication but lacks many CIAM-native features such as advanced orchestration, flexible UX control, and deep B2B identity modeling.
Ideal For
-
AWS-native applications
-
Teams with simple authentication requirements
-
Products prioritizing infrastructure consistency
Trade-Offs
-
Limited customization of login and registration experiences
-
Advanced CIAM features require custom development
-
Steeper learning curve outside AWS-centric teams
6. FusionAuth
FusionAuth is an identity platform often evaluated by teams seeking self-hosted or hybrid deployment control over their CIAM infrastructure.
Where FusionAuth Performs Well
-
Deployment flexibility : Supports self-hosted, private cloud, and hybrid identity deployments.
-
Direct control over identity infrastructure : Appeals to teams wanting ownership over configuration and data handling.
-
CIAM feature breadth : Covers core authentication, MFA, and federation capabilities.
CIAM Fit Analysis : FusionAuth offers flexibility at the cost of operational responsibility. Scaling, availability, and ongoing maintenance remain the customer’s responsibility rather than being fully managed.
Ideal For
-
Organizations with strict infrastructure or data control requirements
-
Teams comfortable managing identity infrastructure in-house
-
Hybrid or on-prem CIAM use cases
Trade-Offs
-
Operational overhead for scaling and maintenance
-
Requires internal expertise to ensure reliability and security
-
Less turnkey than fully managed CIAM platforms
7. WorkOS
WorkOS is commonly evaluated by B2B SaaS teams that need to add enterprise SSO and directory sync capabilities on top of an existing authentication system.
Where WorkOS Performs Well
-
Enterprise SSO enablement : Simplifies SAML SSO and directory sync for enterprise customers.
-
Fast enterprise feature adoption : Allows SaaS teams to meet customer SSO requirements quickly.
-
Developer-friendly APIs : Easy to integrate alongside existing auth solutions.
CIAM Fit Analysis : WorkOS focuses narrowly on enterprise access features rather than full CIAM lifecycle management, and is typically paired with another authentication or CIAM platform.
Ideal For
-
B2B SaaS platforms selling to enterprise customers
-
Teams needing SAML SSO and directory sync quickly
-
Products augmenting existing authentication systems
Trade-Offs
-
Not a complete CIAM solution
-
Requires pairing with another platform for MFA and UX
-
Limited support for consumer-scale identity journeys
Why People Switch from Clerk to LoginRadius
Organizations that move away from Clerk often point to a consistent set of challenges that emerge as their applications scale, security requirements mature, and identity use cases expand beyond basic authentication. While Clerk works well for getting started, many teams eventually need a CIAM platform that offers deeper security controls, enterprise readiness, and long-term flexibility.
Advanced MFA and Modern Authentication
Clerk offers limited multi-factor authentication options, with no native push notifications and no proprietary authenticator app. As security requirements evolve, particularly around account takeover prevention and regulatory expectations, teams often need to layer on additional tools or accept security gaps.
LoginRadius provides native push-based MFA, TOTP, and out-of-band authentication through the LoginRadius Authenticator, along with adaptive and risk-based controls. This allows organizations to strengthen authentication and introduce modern, low-friction security without re-architecting their identity stack.
Fraud Detection and Risk Management
Clerk provides minimal built-in fraud detection and limited visibility into suspicious activity. Teams have little control over breach monitoring, anomaly detection, or policy-driven responses to elevated risk scenarios.
LoginRadius includes advanced fraud detection, real-time alerts, breach screening, and configurable risk signals as part of the CIAM platform. These capabilities help organizations proactively identify threats and apply step-up security only when it is truly needed.
Credential and Access Control Depth
Credential management in Clerk is intentionally lightweight, with limited support for advanced controls such as knowledge-based authentication, password generation, or credential lifecycle policies. For teams managing sensitive customer or partner data, this can restrict how identity policies evolve over time.
LoginRadius offers centralized credential lifecycle management, including knowledge-based authentication, password generators, rotation policies, and fine-grained access controls. This gives security and compliance teams the tools they need without compromising user experience.
Federation and Enterprise Identity Support
Clerk has limited federation capabilities, with no native SAML support, restricted risk-based authentication, and no multi-IDP federation. This can become a blocker when serving enterprise customers, partners, or regulated environments.
LoginRadius delivers full SAML and OIDC support, multi-IDP federation, and SLA-backed APIs designed for enterprise workloads. Organizations can integrate customer, partner, and enterprise identities through a single CIAM platform.
Orchestration and Identity Journey Flexibility
Clerk does not offer drag-and-drop orchestration or real-time flow monitoring, making it difficult to adapt identity journeys across regions, brands, or business models without custom development.
LoginRadius enables visual, no-code identity orchestration with real-time monitoring and event-driven workflows. Teams can rapidly iterate on registration, login, verification, and recovery flows without creating engineering backlogs.
Experience Customization and Intelligence
Clerk’s frontend experience is largely static, with limited customization options and no intelligence layer to adapt experiences dynamically based on user context or behavior.
LoginRadius provides AI-powered theming, adaptive registration flows, and fully customizable hosted login pages. This allows product and CX teams to optimize conversion, security, and consistency across channels without sacrificing control.
LoginRadius vs Clerk: Feature Comparison
| Capability | Clerk | LoginRadius |
|---|---|---|
| Primary Focus | Frontend-first authentication components | Full CIAM platform for B2C, B2B, and partner identity |
| CIAM Architecture | Authentication layer | CIAM-native, cloud-scale architecture |
| Multi-Factor Authentication (MFA) | Limited factors, no native push | Native push, TOTP, out-of-band MFA via LR Authenticator |
| Passwordless & Passkeys | Partial support | Full passwordless flows and FIDO2 passkeys |
| Risk-Based & Adaptive Auth | Not supported | Built-in adaptive and risk-based authentication |
| Fraud Detection & Breach Protection | Minimal | Breach screening, anomaly detection, real-time alerts |
| Federation & Enterprise SSO | Limited, no SAML | Full SAML, OIDC, and multi-IDP federation |
| B2B / Multi-Tenant Identity | Basic | Native multi-tenant orgs, roles, delegated admin |
| Identity Orchestration | Static flows | Visual, no-code orchestration with real-time monitoring |
| Customization & Branding | Limited UI customization | Headless, hosted, and fully custom UI options |
| Data Residency & Compliance | Limited | Regional data residency, GDPR, CCPA, SOC 2 |
| APIs & SLAs | No formal SLAs | SLA-backed APIs for enterprise workloads |
| Scalability & Performance | Startup-scale | Designed for high-volume consumer traffic |
Conclusion
Clerk is a strong starting point for modern applications that need fast, frontend-friendly authentication. For early-stage products or teams with simple identity requirements, its developer experience and UI components can accelerate time to market. However, as applications grow, identity quickly becomes more than just sign-in and session management. Security expectations rise, customer and partner use cases expand, and reliability, compliance, and flexibility move from “nice to have” to business-critical.
For organizations looking for a long-term CIAM foundation, LoginRadius stands out as a platform purpose-built for customer and B2B identity at scale. With advanced MFA, adaptive security, enterprise-grade federation, visual orchestration, and global compliance support built in, it allows teams to evolve their identity strategy without constantly re-architecting. Rather than simply replacing Clerk, many teams use this evaluation process to choose a CIAM platform that can support their product, security posture, and customer experience as they grow.
If you’re evaluating whether Clerk can continue to meet your requirements, the next step is to compare platforms based on your future identity needs, not just your current ones.
Talk with our team about how to plan a CIAM architecture that scales with your product and your customers.



