Introduction
Authentication has come a long way from simple passwords and one-size-fits-all security checks. As cyberattacks grow more sophisticated and user expectations shift toward fast, frictionless experiences, organizations can no longer rely on static authentication methods especially when protecting millions of customer identities.
This is where Adaptive MFA (Adaptive Multi-Factor Authentication) steps in as one of the most strategic advancements in modern identity security.
Unlike traditional 2FA or static MFA, adaptive authentication doesn’t treat every login attempt the same. Instead, it evaluates context, behavior, and real-time risk signals to decide whether a user should be allowed in seamlessly, prompted for additional verification, or denied entirely. The result is stronger security and a smoother user experience, two outcomes that rarely coexist in traditional authentication models.
For developers, product leaders, and security architects, adaptive MFA represents a practical way to reduce account takeover risk, eliminate unnecessary friction, and align with a zero-trust, identity-first security approach. For everyday users, it feels effortless: no OTPs when the system knows the login is legitimate, and additional checks only when something seems off.
At its core, adaptive MFA represents a shift from static authentication toward intelligent, context-aware identity security. If you’re asking what is adaptive MFA or what is adaptive multi-factor authentication, the simplest answer is this: it dynamically adjusts authentication requirements based on real-time risk instead of forcing the same MFA challenge on every login.
As customer identity becomes central to business growth, trust, and compliance, adaptive MFA is quickly becoming the standard for modern CIAM environments. In this guide, we’ll break down what adaptive MFA is, how it works behind the scenes, and why it’s one of the most important upgrades organizations can make to their authentication strategy today.
What Is Adaptive MFA?
Often referred to as adaptive multi factor authentication, this approach is also closely tied to adaptive authentication, a broader security model where identity verification adapts continuously to user behavior, device trust, and environmental signals. In fact, when people ask what is adaptive authentication, they are usually referring to this same risk-based, context-driven decision-making applied across login and session activity.
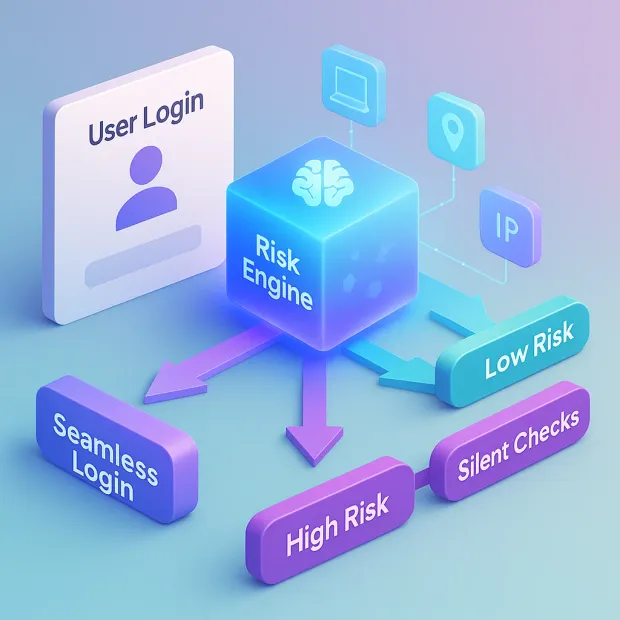
Adaptive Multi-Factor Authentication (Adaptive MFA) is an intelligent, context-aware approach to authentication that adjusts security requirements based on real-time risk. Instead of challenging every user with the same static factors like OTPs or push notifications, adaptive MFA analyzes the situation around each login attempt and decides whether additional verification is needed.
In simple terms, adaptive authentication asks: “Does this login look safe, or does something feel unusual?” Then it tailors the authentication process accordingly.
At a deeper level, adaptive MFA evaluates a wide range of contextual and behavioral indicators: user location, device reputation, IP risk level, login time patterns, behavioral deviations, and dozens of additional signals.
Based on these inputs, it assigns a risk score.
-
Low-risk users pass through seamlessly.
-
Medium-risk users may face a silent check or subtle challenge.
-
High-risk users are prompted to enter a step-up factor or are blocked entirely.
This dynamic approach not only improves security but also dramatically reduces unnecessary friction. Users no longer face OTP fatigue, slow SMS codes, or repetitive verification steps when everything about their login is normal.
What makes adaptive MFA powerful is its ability to blend risk-based authentication, contextual intelligence, and modern CIAM principles into a single workflow. It shifts authentication from something rigid and predictable into something smart, flexible, and user-aware—providing protection precisely when it’s needed, and staying invisible when it’s not.
Understanding what is adaptive multi-factor authentication requires looking beyond OTPs and static rules and focusing on how adaptive authentication engines assess trust dynamically before deciding whether additional verification is even necessary.
Also read: Adaptive Authentication- Is it the Next Breakthrough in Customer Authentication?
How Adaptive Authentication Works?
Adaptive MFA works by analyzing real-time context around every login attempt and making an intelligent decision about the level of verification required. Instead of forcing the same MFA challenge on every user, it evaluates risk first then adjusts the authentication flow accordingly. This creates a balance between strong protection and seamless usability.
This risk-based model is the foundation of modern adaptive MFA, where authentication flows are no longer fixed. Instead, adaptive authentication continuously evaluates context and can even integrate with adaptive SSO, allowing trusted users to move seamlessly across applications without repeated challenges.
Risk Evaluation Begins the Moment a User Tries to Log In
When a login attempt is made, adaptive authentication immediately gathers contextual and behavioral signals. These aren’t just basic checks; they include location patterns, device fingerprints, network quality, historical login behavior, time-of-day consistency, and known threat intelligence.
The system asks intelligent questions such as:
-
Is the user logging in from their usual device?
-
Does the IP address carry any known risk?
-
Has the user behaved differently compared to past sessions?
-
Is the request coming from a suspicious or impossible location?
These signals help form a foundational understanding of whether the attempt looks normal or suspicious.
Assigning a Risk Score to Determine Trustworthiness
Once the contextual data is collected, the authentication engine assigns a risk score. This score determines how much trust the system has in the login attempt. Low-risk sessions can continue without additional friction, while high-risk sessions trigger stronger verification mechanisms.
Adaptive MFA does not rely on static rules it uses dynamic logic, risk scoring algorithms, and sometimes even machine learning models to make smarter decisions over time. The more the system observes user behavior, the better it becomes at distinguishing legitimate patterns from unusual ones.
Responding with the Appropriate Authentication Action
Based on the risk score, the system chooses the correct next step. This is where adaptive MFA becomes truly powerful: it applies the right level of security at the right time, instead of relying on outdated one-size-fits-all challenges.
Typical adaptive responses include:
-
Allow the login with no interruption (low-risk)
-
Silently evaluate more factors in the background (medium-risk)
-
Trigger a step-up authentication challenge like TOTP, push, biometrics, or passkey (high-risk)
-
Deny the login if the activity appears malicious
The result is a system that strengthens security only when necessary while keeping the experience smooth for trusted users.
Continuous Evaluation Throughout the Session
Adaptive authentication doesn’t stop after login. In more advanced implementations, it continues monitoring user actions throughout the session. This means if behavior suddenly becomes suspicious, such as accessing sensitive resources from a risky network, the system can demand verification again or terminate the session entirely.
This continuous, risk-aware model aligns with zero-trust and identity-first security, ensuring that trust is earned and maintained, not assumed.
Risk Signals Used in Adaptive MFA
Adaptive MFA is effective because it analyzes a broad range of environmental, behavioral, and contextual signals to understand whether a login attempt is trustworthy. Instead of relying on a single factor, it evaluates multiple dimensions of user activity, creating a layered, intelligent picture of risk.
These signals allow the system to detect anomalies that traditional MFA or 2FA would completely overlook.
Device & Browser Intelligence
Adaptive authentication examines the device being used during login, checking whether it matches known patterns for that user. Everything from device ID to operating system, browser fingerprint, and security posture is evaluated. \
If the user is on a familiar device, the system builds trust. If the login originates from a new or suspicious device, risk levels increase immediately.
Signals it considers include:
-
New or unrecognized devices
-
Jailbroken or rooted devices
-
Browser fingerprint mismatches
Location & IP-Based Risk
User login locations tell a powerful story. Adaptive MFA identifies geographic consistency where a user usually logs in from and flags anomalies.
Risk signals include:
-
Sudden login from a new country
-
Impossible travel (e.g., two locations minutes apart)
-
Suspicious IP ranges, VPN abuse, TOR networks
-
High-risk or blacklisted IPs
These location-based checks help detect account takeover attempts that originate from hacked or remote servers.
User Behavior & Activity Patterns
Behavior acts as a digital fingerprint. Adaptive MFA evaluates how users typically behave — when they log in, how they navigate, and what actions they take.
Signals include:
-
Unusual login times
-
Fast, automated, or bot-like interactions
-
Abnormal click or navigation patterns
-
Sudden changes in typical behavior
Any deviation from normal behavior can trigger additional verification.
Also read: Fix Broken Authentication with Adaptive MFA
Network & Environmental Signals
The quality and type of network also impact risk. Adaptive MFA analyzes whether a user is connecting from a trusted or suspicious environment.
Signals include:
-
Public Wi-Fi or unsecured networks
-
Anonymous or masked connections
-
Repeated failed login attempts from the same network
These signals help filter out automated attacks, credential stuffing, and bot-driven intrusions.
Threat Intelligence & Historical Risk
Adaptive MFA leverages real-time and historical threat data to evaluate credibility. If previous sessions, devices, or IPs associated with the login attempt were risky, the system automatically tightens verification.
Signals include:
-
Known malicious sources
-
Accounts flagged for suspicious behavior
-
Repeated brute-force attempts
This ensures attackers are blocked even if they appear legitimate on the surface.
By combining these signals, adaptive MFA achieves a level of accuracy and sophistication that traditional MFA or 2FA cannot match. It moves authentication from a static “checklist” approach to a dynamic, intelligent system that responds to risk in real time.
Adaptive MFA Benefits
Adaptive MFA delivers a level of protection and user experience that traditional MFA and 2FA cannot match. By analyzing real-time context and responding intelligently, it enhances security while reducing friction a rare combination in the authentication world.
Below are the most important benefits, explained in an elaborated yet easy-to-follow format.
1. Stronger Security Through Real-Time Risk Analysis
Adaptive MFA evaluates multiple risk signals, including device behavior, IP reputation, user patterns, network trust, and threat intelligence, to determine whether a login attempt is legitimate.
This real-time risk analysis helps the system catch suspicious activity before a user even reaches the login screen. Attackers trying to bypass authentication, launch credential stuffing, or attempt account takeovers are intercepted instantly.
Because decisions are based on data and behavior rather than fixed rules, the system becomes smarter and more resilient over time.
2. Reduced Friction for Low-Risk Users
One of the biggest drawbacks of traditional MFA is the unnecessary friction it creates. Every login feels the same, even if the user is clearly authentic.
Adaptive MFA changes this by allowing low-risk users to authenticate seamlessly without extra steps. When the system recognizes a trusted device, familiar location, and normal behavior, it lets the user log in without OTPs, prompts, or secondary checks.
This creates a smoother user experience, reduces login fatigue, and significantly increases conversion rates, especially for consumer-facing applications.
3. Targeted Step-Up Challenges Only When Needed
Adaptive MFA provides step-up authentication only when a login attempt truly appears risky. Instead of forcing every user to complete a full MFA flow, the system challenges only those who exhibit unusual or suspicious patterns.
This targeted approach ensures that security is enforced where it matters most while legitimate users enjoy a hassle-free experience. It also reduces OTP dependency, SMS delivery failures, and push-notification fatigue.
4. Better Protection Against Modern Attacks
Traditional MFA struggles against advanced threats like real-time phishing, bot-driven attacks, SIM-swapping, and adversary-in-the-middle (AitM) scenarios.
Adaptive MFA uses risk intelligence and contextual signals to flag these anomalies instantly. If an attacker is trying to log in from a compromised IP, unusual region, or suspicious device, the system forces a strong step-up or blocks the attempt altogether.
This makes adaptive MFA one of the most effective defenses against modern account takeover attempts.
5. Improved Login Success Rates & Lower Abandonment
Every extra login step increases the risk of user abandonment, especially during signup or checkout. Adaptive MFA optimizes login and registration flows by minimizing obstacles for legitimate users.
This results in:
-
Higher login completion
-
Better onboarding success
-
Lower churn
-
A smoother authentication experience across devices
It’s a major advantage for high-traffic consumer applications where user experience directly impacts revenue.
6. Lower Support Costs & Reduced Operational Overhead
Most support tickets in authentication are due to MFA issues: lost devices, SMS delays, OTP errors, or inability to access codes.
Adaptive MFA reduces reliance on OTP-heavy flows, meaning fewer problems for users and fewer escalations for support teams. Organizations save time and resources because the system intelligently avoids unnecessary MFA challenges and reduces points of failure.
7. Seamless Global Compatibility for Diverse User Bases
In global apps, SMS delays, device limitations, and connectivity issues can drastically impact MFA performance. Adaptive MFA helps overcome these challenges by offering alternative paths and adjusting requirements based on device capability and network context.
Whether the user is on a high-end smartphone, a low-bandwidth network, or an unfamiliar region, adaptive MFA ensures the right authentication flow is delivered.
8. A Future-Proof Approach to Zero-Trust Security
Adaptive MFA aligns naturally with zero-trust principles: never trust, always verify.
It continuously evaluates user behavior and device signals, ensuring that authentication isn’t a one-time checkpoint but an ongoing assessment. This makes it ideal for modern CIAM architectures that require intelligent, dynamic, and user-first security.

Adaptive MFA vs Traditional MFA vs 2FA
Understanding the differences between Adaptive MFA, Traditional MFA, and 2FA is essential for choosing the right security model. Although these terms are often used interchangeably, they deliver very different levels of protection, user experience, and intelligence.
This section breaks down those differences in a clear, practical way for both beginners and experts.
How 2FA Works: A Static Second Step for Basic Security
2FA (Two-Factor Authentication) adds a second layer of security on top of a password, typically through SMS OTP, TOTP apps, email codes, or push notifications.
While it significantly improves security compared to password-only logins, 2FA is still a static process every login triggers the same challenge, regardless of context or risk.
Limitations include:
-
Vulnerability to SIM-swaps, OTP interception, and phishing
-
Extra friction for every user, even trusted ones
-
High dependency on reliable devices or networks
-
No real intelligence about unusual login behavior
2FA strengthens security, but it does not adapt to evolving threats or user context.
How Traditional MFA Works: More Factors, but Still Static
Traditional MFA expands on 2FA by offering multiple factor types passwords, OTPs, security keys, or biometrics but the logic remains similar: All users must complete the same MFA steps every time.
While it’s more flexible and secure than basic 2FA, it still follows rigid rules:
-
Every login triggers MFA
-
No evaluation of risk or behavior
-
No contextual adjustments
-
More friction for high-volume consumer apps
Traditional MFA improves security but sacrifices user convenience by treating every login attempt equally regardless of whether the user is safe or suspicious.
How Adaptive MFA Works: Intelligent, Context-Aware, User-Friendly
Adaptive MFA is the evolution of MFA. Instead of using fixed rules, it evaluates risk signals in real time device trust, location anomalies, behavior deviations, IP reputation, and threat intelligence.
Based on these insights, the system decides whether to allow the user through seamlessly or require additional verification.
Key advantages:
-
Step-up challenges only when something looks risky
-
Seamless, frictionless experience for trusted users
-
Blocks or challenges suspicious activity instantly
-
Continuous learning and behavior analysis
-
Ideal for modern CIAM, zero-trust, and high-scale consumer apps
Adaptive MFA brings balance: maximum security with minimum friction.
The Clear Difference: Static vs Smart Authentication

The biggest distinction comes down to intelligence:
-
2FA = static second step
-
Traditional MFA = multiple static steps
-
Adaptive MFA = dynamic, risk-based decisions
Organizations choosing between them should consider their user base, threat landscape, and long-term authentication strategy. While 2FA and traditional MFA remain useful, only adaptive MFA meets the demands of today’s identity-first, phishing-heavy, high-risk digital environment.
Adaptive MFA in CIAM
Adaptive MFA becomes even more valuable when viewed through the lens of Customer Identity and Access Management (CIAM). Unlike workforce identity, where users are internal and controlled, customer identity environments serve millions of unpredictable, diverse, global users. This scale and unpredictability make static authentication models inefficient, expensive, and often frustrating for real customers.
In advanced CIAM implementations, adaptive MFA often works alongside adaptive SSO, enabling frictionless access across multiple applications while still enforcing step-up authentication whenever risk thresholds are crossed.
Adaptive MFA solves these challenges by offering security that grows smarter without disrupting the user journey.
Designed for High-Volume Consumer Login Flows
Consumer applications experience unpredictable login spikes from flash sales to seasonal peaks. Traditional MFA introduces friction that can choke conversion during these high-traffic moments.
Adaptive MFA ensures that trusted customers pass through login quickly, reducing queue times, OTP delays, and other bottlenecks. It keeps authentication fast even during peak usage.
This is especially important for industries like retail, media, gaming, travel, and eCommerce where every second counts during login.
Reduces Abandonment and Improves Conversion Rates
Customer-facing platforms live or die by smooth user journeys. Static MFA creates friction every time a user logs in, increasing the likelihood of drop-offs during registration, checkout, or everyday access.
Adaptive MFA challenges users only when necessary, meaning more seamless sign-ins and fewer reasons for users to abandon the flow. This directly boosts conversion, retention, and session completion rates.
Protects Against Account Takeovers (ATO) at Scale
Large user bases are prime targets for account takeover attacks. Credential stuffing, bot assaults, password reuse, and phishing campaigns can hit millions of accounts at once.
Adaptive MFA doesn’t just add a second factor it uses real-time intelligence to identify anomalous activity and block, challenge, or flag suspicious attempts automatically.
This proactive, dynamic defense is critical for CIAM environments, where user trust and brand reputation are at stake.
Customizable for Global, Diverse User Groups
Not all users have the same devices, capabilities, or connectivity. OTPs might fail for users in certain regions. Push notifications might not work for others.
Adaptive MFA adjusts the authentication flow based on user context, making global compatibility far more achievable. It can even tailor authentication methods based on local regulations, device types, or risk levels.
This flexibility makes it ideal for multinational platforms with varied user behavior.
Aligned with Modern Identity-First & Zero-Trust Strategies
CIAM has evolved from simply managing user accounts to becoming the first line of security in a zero-trust environment. In a world where threats bypass infrastructure and target users directly, adaptive authentication ensures verification happens intelligently and continuously.
Instead of assuming trust after login, adaptive MFA keeps evaluating context throughout the session perfect for modern, identity-first security designs.
Real-World Use Cases & Industry Scenarios
Adaptive MFA is not just a theoretical improvement it solves real challenges across industries where user behavior, risk patterns, and customer expectations vary widely. Because it balances strong protection with low friction, adaptive authentication fits naturally into any sector that prioritizes secure and seamless customer experiences.
1. Banking and Financial Services
Financial services face some of the highest levels of fraud, credential stuffing, phishing, and account takeover attempts. Adaptive MFA helps banks distinguish between trusted customers and suspicious behavior instantly.
For example, if a user logs in from their usual device and city, the system grants access without extra steps. But if the same account is accessed from a risky network or a new country, adaptive MFA automatically enforces stronger step-up checks like biometrics or security keys.
This preserves user convenience while maintaining airtight protection across digital banking, mobile apps, and fintech platforms.
2. Retail & eCommerce
Checkout friction kills conversions. For online retailers, adding extra MFA steps at the wrong moment can directly impact revenue.
Adaptive MFA keeps trusted shoppers moving quickly by allowing seamless logins during everyday purchases. When something seems off, such as an unusual shipping address, a suspicious IP address, or an impossible travel route, the system triggers additional verification.
This approach reduces abandoned carts, lowers fraud, and helps retailers maintain a smooth buying experience across global markets.
3. SaaS Platforms & Enterprise Applications
SaaS platforms serve diverse user personas from everyday employees to high-privilege admin accounts, each with different risk levels. Adaptive MFA allows SaaS providers to tailor authentication based on user roles, device types, and behavior patterns.
High-risk admin actions can require stronger verification, while routine user logins can remain frictionless. This creates a balanced security model across self-service portals, dashboards, and multi-tenant SaaS environments.
4. Healthcare & Regulated Industries
Healthcare systems must balance strict compliance requirements with real-world usability for doctors, staff, and patients. Adaptive MFA helps maintain HIPAA- and PHI-compliant access without constantly interrupting workflows.
It ensures sensitive data access requires strong verification, while low-risk sessions like checking appointment schedules or accessing patient portals remain smooth and fast.
5. Media, Gaming & High-Traffic Consumer Apps
Apps with millions of users face unique challenges: bot attacks, massive login surges, and global usage patterns. Static MFA cannot scale efficiently in this environment.
Adaptive MFA intelligently handles spikes by reducing unnecessary steps for legitimate users and focusing computational effort on suspicious activity. This creates a secure and high-performance login experience for platforms built around entertainment, video streaming, or gaming.
6. Government Services & Public Portals
Government applications require strong authentication due to sensitive citizen data. Adaptive MFA provides security without overwhelming users.
By analyzing risk context location, behavior, and device trust it allows low-risk routine tasks to be completed smoothly while protecting sensitive interactions behind stronger verification layers.
The Future of Adaptive Authentication
Adaptive MFA is not just a trend; it is the foundation of the next generation of digital identity security. As threats evolve and user expectations rise, authentication must become smarter, more context-aware, and less intrusive.
As identity ecosystems mature, adaptive authentication combined with adaptive MFA will become the default security model for customer identity, replacing static MFA entirely in high-scale, zero-trust environments.
The future of adaptive authentication reflects this shift, blending intelligence, automation, and seamless user experience into a unified security model.
AI-Driven Risk Engines Will Power Authentication Decisions
As cyberattacks become more sophisticated, static rules will no longer be enough. The next wave of adaptive MFA will rely heavily on AI and machine learning to analyze patterns, detect anomalies, and predict malicious activity before it happens.
These AI-driven risk engines will learn from millions of signals across devices, behaviors, and environments, offering more accurate and real-time threat assessments than manual interventions ever could.
Continuous Authentication Will Replace One-Time Verification
Today’s authentication often ends at login. Once a user gains access, the session is trusted until manually revoked. Future adaptive systems will continuously evaluate user behavior, device stability, and environmental trust not just at the moment of login, but throughout the entire session.
This continuous evaluation will reduce lateral movement attacks, insider threats, and hijacked session exploits without increasing user friction.
Passwordless + Adaptive MFA Will Become the New Standard
Passwordless authentication solves a major portion of today’s security challenges, but when combined with adaptive MFA, it becomes significantly more powerful.
Passkeys, WebAuthn, and device-bound biometrics already provide high security and low friction. Adaptive intelligence elevates them further by deciding when a user needs additional verification or when the device alone is enough. This combination creates a seamless, phishing-resistant, future-proof authentication model.
Identity-First Security Will Drive Authentication Architecture
The industry is shifting from network-centric to identity-centric security. Instead of relying on firewalls or VPNs as the primary defense, authentication becomes the first and most critical checkpoint.
Adaptive MFA aligns perfectly with this philosophy: it treats every login attempt as a potential risk, evaluates context dynamically, and enforces trust step by step.
Regulatory Pressure Will Push Organizations Toward Smarter MFA
Global privacy and security standards are becoming increasingly stringent. Regulations such as GDPR, PSD2, and HIPAA, as well as industry best practices, increasingly require risk-based authentication for sensitive operations.
Adaptive MFA satisfies these expectations by identifying risky scenarios automatically and enforcing the right level of verification without bottlenecking users.
Adaptive authentication represents the ideal balance between protection and usability. As the digital ecosystem continues to expand and identity threats become more complex, adaptive MFA will evolve into the backbone of modern CIAM an intelligent, predictive system that continuously adjusts security in ways users barely notice.
Conclusion
Adaptive MFA represents the natural evolution of authentication in a world where threats are unpredictable and user expectations demand speed. Unlike traditional MFA or 2FA, which apply static rules to every login, adaptive authentication intelligently adjusts to context, behavior, and real-time risk.
The result is a system that protects users with precision while keeping their experience as smooth as possible.
For organizations operating at scale, whether in retail, finance, SaaS, gaming, or global consumer environments, adaptive MFA offers the best of both worlds: stronger defense against account takeovers and dramatically reduced friction for trusted users. It aligns perfectly with identity-first security models, zero-trust frameworks, and modern CIAM strategies that prioritize both security and usability.
As cyberattacks grow more sophisticated and digital identity becomes a core part of brand trust, adaptive MFA isn’t just a nice-to-have, it's a competitive advantage. Platforms that adopt risk-based, context-aware authentication will deliver safer, smarter, and more user-friendly experiences that stand out in crowded markets.
Ready to Deliver Smarter, Adaptive Authentication?
LoginRadius helps organizations transition from static MFA to a fully intelligent, adaptive security model without sacrificing user experience.
With LoginRadius, you can enable:
-
Adaptive MFA with real-time risk scoring
-
Phishing-resistant authentication (WebAuthn, biometrics, passkeys)
-
Seamless passwordless login flows
-
Device intelligence, IP risk analysis, and behavioral signals
-
Scalable CIAM built for global consumer applications
-
Low-friction authentication that boosts conversion and trust
If you're ready to see how adaptive authentication can transform your customer experience:
Book a quick demo with LoginRadius and explore the future of secure, frictionless login.
FAQs
Q: What is Adaptive Multi-Factor Authentication?
A: Adaptive multi-factor authentication (Adaptive MFA) uses contextual and behavioral signals—like device, location, and IP risk—to decide whether a user needs additional verification. It strengthens security while reducing friction for trusted users.
Q: How is Adaptive MFA different from traditional MFA?
A: Traditional MFA challenges every user the same way, while Adaptive MFA intelligently adjusts verification based on real-time risk. Users only face step-up checks when something looks suspicious, making the login flow smoother.
Q: What signals does Adaptive MFA analyze?
A: It evaluates device fingerprints, location consistency, network trust, behavior patterns, IP reputation, and threat intelligence. These signals help determine whether a login should be seamless, challenged, or blocked.
Q: Is Adaptive MFA better than 2FA?
A: Yes. 2FA adds a static second step, but Adaptive MFA uses dynamic context and real-time risk scoring to protect users more accurately. It offers stronger security with minimal user friction.




