Introduction
The shift to centralized login methods has been one of the biggest changes in authentication over the past decade. Instead of creating a new account for every application, users increasingly sign in with an existing identity on platforms like Google, Apple, or Facebook.
This shift is driven by user behavior. Across multiple studies on social login, around 86% of users report frustration when they are forced to create yet another new account, and 77% say they prefer social login or similar options over traditional username-and-password flows. Centralizing login through a single identity provider reduces this friction.
What’s less visible is the infrastructure that makes this possible. Identity Providers (IdPs) sit behind social login, single sign-on (SSO), and other modern authentication patterns, taking over much of the responsibility for storing identities and performing authentication.
In this article, we’ll explain what an identity provider (IdP) is, how IdP authentication works in common scenarios like SSO and social login, and how modern identity providers simplify identity management for both users and application teams.
What is an Identity Provider (IdP)?
An identity provider (IdP) is a system that creates, stores, and manages digital identities and performs authentication for them. Think of it as the central service that owns user accounts and confirms who a user is when they try to sign in.
An IdP maintains identities for “principals” such as users, devices, or services. It holds identifiers (like email or username), credentials, and profile data, and exposes IdP authentication flows that applications can call instead of handling passwords directly. After a successful login, the identity provider returns a trusted result (for example, a signed token or assertion) that the application uses to create a session and enforce authorization.
Identity providers work together with service providers (SPs) or relying parties, which consume those authentication results. The same product can be an identity service provider in one scenario and a service provider in another.
For example, your app is an identity provider if it manages its own usernames and passwords, but it acts as a service provider when B2B users sign in via SSO using an external IdP. Common identity providers include Google, GitHub, Facebook, Azure AD, and CIAM platforms that act as identity providers for SSO across many applications.
How Does an Identity Provider Work?
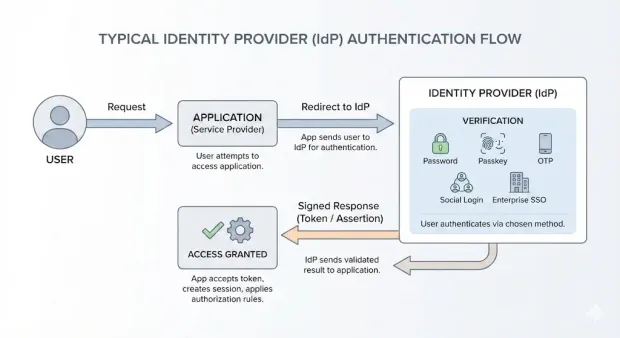
An identity provider manages identity data and handles the entire login process, while applications simply rely on its decisions. A typical IdP authentication flow looks like this:
-
Request : A user tries to access an application (the service provider or relying party). The application sees the user isn’t authenticated and redirects them to the identity provider (IdP).
-
Verification : The IdP runs its authentication flow—this could be a password, passkey, OTP, social login, or an enterprise SSO connection.
-
Access : If authentication succeeds, the IdP sends a signed response back to the application, which then validates it, creates a session, and applies authorization rules.
In this setup, the IdP acts as the central identity service provider. It stores identifiers (user IDs, emails, usernames), credentials, and attributes, so applications don’t need to function as standalone authentication providers. They simply trust the response the IdP returns.
How the IdP sends that “login success” back depends on the protocol :
-
A SAML identity provider issues a SAML assertion containing the user and optional claims.
-
With OpenID Connect, the IdP returns an ID token (and often an access token) that the application can verify with the IdP’s keys.
-
With OAuth 2.0, the IdP often acts as the authorization server, issuing access tokens that APIs can validate.
Also read : How Does SAML Authentication Work?
When all your applications use the same identity provider, you can enable identity providers for SSO with one set of policies and handle IdP integration in a single place instead of rebuilding authentication in every app.
Identity Provider vs. Service Provider/ Relying Party
An identity provider (IdP) is responsible for creating and authenticating digital identities, but it doesn’t operate alone. It works alongside applications that depend on its authentication output. Those applications are known as service providers (SPs) or relying parties (RPs).
Here’s the distinction in practical terms:
-
Identity Provider (IdP) : The system that verifies who the user is and issues a signed response (token or assertion). It owns the identity data and the authentication workflow.
-
Service Provider (SP) / Relying Party (RP) : The application the user wants to access. It does not authenticate the user directly, but trusts the IdP’s result. After receiving the IdP’s response, it establishes a session and enforces its own authorization logic.
This separation is what makes modern IdP authentication scalable. The IdP handles identity and login, and the service provider consumes the authentication result. The same application can play either role depending on the scenario. For example:
- Your app is an identity service provider when you manage your own user accounts.
- The same app becomes a service provider when B2B users authenticate through an external IdP using SSO.
This flexibility is central to identity federation and enables clean IdP integration across different systems without duplicating identity stores or authentication code.
Types and Examples of Identity Providers
Developers typically work with three broad categories, each serving a different part of the authentication landscape.
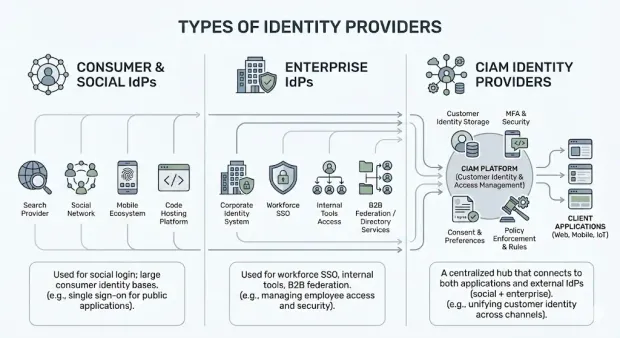
1. Consumer and Social Identity Providers
These are the public identity provider examples most users interact with daily. Examples are Google, Facebook, Apple, GitHub, X, and others. They maintain large consumer identity bases and expose standardized IdP authentication endpoints for use cases like social login. Apps rely on these providers to reduce friction and eliminate the need for users to create yet another password.
2. Enterprise Identity Providers
Enterprise IdPs manage identities within an organization. Common platforms include Azure AD (Entra ID), Okta, Ping, and Active Directory Federation Services. These providers are often used for workforce SSO, internal application access, and B2B federation. When a customer’s employees sign in to your product using their corporate SSO, your application is acting as the service provider, and the enterprise system is the identity provider.
3. CIAM Platforms as Identity Providers
Customer Identity and Access Management (CIAM) platforms, such as LoginRadius act as dedicated identity service providers for customer-facing applications. They handle identity storage, policy enforcement, MFA, consent, and token issuance. A CIAM platform can also integrate with social login and enterprise IdPs, effectively becoming the central identity provider for all of your applications.
These categories together form a broader identity providers list that developers use to support consumer login, B2B SSO, workforce authentication, or any combination of these. Choosing the right identity provider depends on your application’s audience, security requirements, and architecture.
Business and Security Benefits of Using an Identity Provider
Identity providers reduce complexity for developers while giving users a more consistent, predictable experience. For customer-facing systems, this directly improves conversion, reduces friction, and strengthens access controls.
Here are some business and security benefits:
Reduced Password Friction
Customers often struggle with account creation, password resets, and managing multiple credentials across apps. By delegating authentication to a single identity provider, either through local credentials, social login, or enterprise SSO, you simplify the entry point and remove unnecessary steps. This is one of the main reasons organizations adopt identity providers for SSO and social identity flows.
Consistent Authentication Policies
When applications each maintain their own authentication stack, enforcing MFA, password rules, or risk checks becomes inconsistent. With a centralized identity service provider, you define policies once and apply them across all applications. This keeps IdP authentication predictable and reduces the attack surface.
Centralized Identity Lifecycle Management
An identity provider maintains identifiers, profile attributes, and status for users. This makes onboarding, account linking, suspension, and deletion significantly easier. Instead of updating multiple systems, developers only interact with one identity authority.
Stronger Security Controls
Centralizing authentication allows the IdP to enforce MFA, monitor sign-in behavior, and apply contextual rules (such as device or IP checks). The IdP also becomes the source of audit logs and login telemetry, which is critical for compliance requirements and incident investigation.
Learn more about Data Auditing and Logging
Lower Operational Overhead
Without an IdP, each application becomes its own authentication provider, which leads to duplicated code, inconsistent security, and higher maintenance costs. Using one identity provider simplifies IdP integration, accelerates development, and reduces the long-term operational burden of managing identity at scale.
Identity Providers for SSO, SAML, and OIDC
Identity providers support several industry standards that allow applications to delegate authentication safely and consistently. These protocols determine how IdP authentication works, how tokens or assertions are formatted, and how trust is established between the identity provider and the service provider.
Identity Providers for SSO
Single sign-on (SSO) allows a user to authenticate once with an identity provider and access multiple applications without logging in again. Because all applications trust the same IdP, users move between properties seamlessly, and developers avoid maintaining separate authentication flows. This is one of the most common reasons organizations implement identity providers for SSO across their application ecosystems.
SAML Identity Provider
A SAML identity provider uses the Security Assertion Markup Language (SAML) to authenticate users and issue SAML assertions to service providers. These assertions contain the subject (the authenticated user) and any relevant attributes. SAML is widely used in enterprise SSO and remains a common integration requirement for B2B applications.
Here’s what a typical pattern looks like:
-
The user attempts to access an app.
-
The app redirects the user to the SAML IdP.
-
The IdP authenticates the user and returns a signed SAML assertion.
-
The application validates the assertion and grants access. \
OIDC and OAuth 2.0 Identity Providers
OpenID Connect (OIDC) is the modern, JSON-based protocol that many developers prefer for web and mobile applications. An IdP acting as an OpenID Provider issues ID tokens (and sometimes access tokens) that the application can verify using the IdP’s public keys. OIDC sits on top of OAuth 2.0, which defines how access tokens are issued and used to protect APIs.
Some common uses include:
-
OIDC for authentication (ID tokens).
-
OAuth 2.0 for API authorization (access tokens).
These protocols allow a single identity service provider to serve different applications consistently, making IdP integration more predictable and reducing the need for custom authentication logic in each system.
Also read: SSO Authentication: Complete Guide to OpenID, SAML & OAuth
Integrating an Identity Provider with a CIAM Platform
A CIAM platform often becomes the central identity provider for all customer-facing applications. Instead of each app managing its own user store and authentication logic, the CIAM layer handles identities, enforces policies, and exposes standardized IdP authentication endpoints. This creates a consistent, scalable model for customer login across web, mobile, API, and partner channels.
CIAM as the Identity Hub
In a typical architecture, the CIAM platform stores customer identities and acts as the primary identity service provider. Applications redirect users to the CIAM IdP for authentication, and the CIAM layer issues tokens or assertions the applications can validate. The same platform can also integrate upstream with social IdPs and enterprise IdPs, allowing developers to offer multiple login options without managing them directly.
Common IdP Integration Patterns
Developers usually connect applications to the CIAM IdP using either SAML or OpenID Connect. A high-level IdP integration flow looks like this:
-
Configure the application as a service provider (or relying party).
-
Register redirect URIs and establish trust with the CIAM IdP.
-
Map attributes or claims required by the application.
-
Test authentication flows (local login, social login, SSO, MFA, etc.).
Once this is in place, all authentication is centralized in the CIAM layer, and your applications rely on a single authority for user identity.
Also learn about Custom IdPs by LoginRadius
How LoginRadius Acts as an Identity Provider
LoginRadius operates as a fully managed identity provider for customer identities. It supports identity providers for SSO, SAML, OIDC, MFA, passwordless authentication, and account linking. Because it acts as both the identity store and the authentication provider, LoginRadius simplifies login flows across multiple applications while allowing developers to integrate external identity sources when needed.
With CIAM as the identity backbone, teams avoid building and maintaining authentication in every codebase, and instead rely on a single, standards-based platform to handle identity at scale.
Identity Provider Best Practices
A well-implemented identity provider (IdP) creates a consistent, secure authentication layer across all applications. The following best practices help developers maintain a reliable identity system while keeping IdP authentication predictable and easy to integrate.
Prefer Open, Standards-Based Protocols
Choose protocols such as SAML, OpenID Connect, and OAuth 2.0 when implementing an identity provider. Standards-based flows make IdP integration more consistent across applications and ensure that service providers can validate tokens or assertions without custom logic. Open standards also reduce dependency on proprietary authentication providers and give teams more flexibility as systems evolve.
Apply Strong and Consistent Authentication Policies
Centralizing authentication through an identity service provider allows you to enforce MFA, step-up authentication, passkeys, or risk-based checks across all applications. Because policies live in one place, i.e., the IdP, developers avoid duplicating authentication logic and maintain a uniform security posture.
Maintain a Single System of Record for Identity
Identity data should be stored and managed in one authoritative identity provider. Spreading identity across applications increases risk and operational overhead. Using one identity provider prevents fragmentation, keeps user attributes accurate, and simplifies lifecycle operations like account linking, deactivation, and recovery.
Monitor Authentication Flows and Adjust Policies
Since all authentication traffic passes through the IdP, you gain complete visibility into login attempts, failures, MFA prompts, and anomalies. This telemetry helps teams refine IdP authentication policies, troubleshoot issues, and maintain compliance requirements more effectively.
Centralizing these practices under a single identity provider ensures predictable security, easier integration, and a better overall experience for both users and development teams.
How LoginRadius Acts as a Modern Identity Provider
A CIAM platform like LoginRadius is designed to function as a centralized identity provider (IdP) for all customer-facing applications. Instead of maintaining separate identity stores, authentication logic, and security policies in each application, LoginRadius consolidates these responsibilities into a single, standards-based identity layer.
Central Identity Service Provider for All Applications
LoginRadius operates as an identity service provider, managing user identities, credentials, and authentication flows. Applications redirect users to LoginRadius for IdP authentication, and LoginRadius returns signed tokens or assertions that the applications can verify. This keeps identity data consistent across web, mobile, and API-driven systems.
Because LoginRadius supports multiple upstream identity providers, such as Google, Facebook, Apple, and enterprise SSO providers, it can serve as the hub connecting your applications to a broader identity providers without additional code or infrastructure.
Standards-Based SSO, SAML, and OIDC Support
LoginRadius supports identity providers for SSO through modern standards, including:
-
SAML, where LoginRadius acts as a SAML identity provider, issuing SAML assertions to service providers.
-
OpenID Connect, where LoginRadius issues ID tokens and access tokens applications can verify.
-
OAuth 2.0, where LoginRadius functions as an authorization server for API access.
These capabilities allow developers to integrate LoginRadius as the IdP for multiple applications while maintaining consistent authentication, token handling, and session behavior across all properties.
Learn about LoginRadius’ Purpose-Built IAM for B2B Customers, Partners, and Vendors
Consumer-Centric Capabilities That Improve ROI
LoginRadius offers features tailored for customer identity use cases, including MFA, passwordless authentication, progressive profiling, account linking, consent management, and built-in fraud controls. For development teams, this means:
-
No need to build or maintain custom authentication providers
-
Faster onboarding for new applications
-
A unified place to manage IdP integration and identity policy
-
Reduced operational overhead and improved security posture
By serving as the centralized identity provider, LoginRadius enables scalable, secure authentication across your entire application ecosystem while giving users a consistent experience everywhere they sign in.
Conclusion
As standards like SAML, OpenID Connect, and OAuth 2.0 continue to mature and as users increasingly expect seamless movement across devices and channels, the benefits of delegating authentication to a dedicated identity service provider become even clearer. Instead of maintaining scattered identity logic in each application, developers can focus on product features while the IdP handles verification, token issuance, and session consistency.
Platforms like LoginRadius extend this model into customer identity at scale. By acting as the central identity provider, supporting IdP authentication, and integrating with social and enterprise IdPs, LoginRadius positions teams for what comes next: broader SSO, stronger authentication methods, evolving privacy requirements, and identity experiences that feel effortless to users.
FAQs
1. What is an identity provider (IdP)?
An identity provider (IdP) is a system that creates, stores, and manages digital identities and performs authentication on behalf of applications. The IdP verifies the user and issues a trusted token or assertion that the application uses to grant access.
2. How does IdP authentication work?
IdP authentication works by redirecting the user to the identity provider, where credentials or alternative login methods are verified. If successful, the IdP returns a signed token to the application, which then establishes a session based on that result.
3. What is the difference between an identity provider and a service provider?
An identity provider (IdP) authenticates users and issues tokens. A service provider (SP) or relying party consumes those tokens to grant access. The IdP makes the authentication decision; the SP enforces authorization based on the IdP’s response.
4. What are examples of identity providers?
Common identity provider examples include Google, Facebook, Apple, GitHub, Azure AD, Okta, Ping, and CIAM platforms like LoginRadius. These providers manage identities and issue authenticated responses to applications.
5. What is a SAML identity provider?
A SAML identity provider uses the SAML protocol to authenticate users and issue SAML assertions. These assertions contain user details and claims that service providers validate to complete SSO.
6. How do identity providers support SSO?
Identity providers for SSO authenticate the user once and issue tokens that multiple applications can trust. This allows users to move between applications without repeated logins, with all authentication managed centrally by the IdP.
7. What is an identity service provider?
An identity service provider is another term for an identity provider. It stores user identities, manages credentials and attributes, and performs IdP authentication for applications that delegate login.
8. Can an application act as both an identity provider and a service provider?
Yes. An application can be an identity provider when managing its own user accounts, and a service provider when users authenticate through an external IdP via SSO. Many CIAM platforms support both roles depending on the integration.
9. How does IdP integration work with modern applications?
IdP integration typically involves configuring trust between the application and the identity provider using SAML or OIDC. The application redirects users to the IdP, validates the returned token or assertion, and creates a session based on that result.
10. Why use an identity provider instead of building authentication in every app?
Using a centralized identity provider avoids duplicating authentication code, ensures consistent security policies (like MFA), supports SSO, and provides a single system of record for identity. This reduces complexity and improves the overall authentication experience.



