Introduction
Let’s be honest, no one likes creating yet another username and password just to access a website. As users, we’ve all been there hovering over the “Sign Up” button, only to abandon the form because it asks for too much information, or worse, forces us to verify through yet another email. This friction is exactly what social login plugins are designed to eliminate.
In today’s digital-first world, convenience drives engagement. Whether it’s an ecommerce store, a community forum, or a membership-based site, WordPress users are increasingly opting for social media login plugins to provide visitors with a faster, easier way to sign in using accounts they already trust, like Google, Facebook, GitHub, or LinkedIn.
That’s where the power of a good WordPress social plugin comes in. With just a few clicks, you can integrate seamless authentication into your site, cut down drop-offs, and even enrich user profiles with verified social data, all without compromising security or performance.
But with dozens of options in the plugin marketplace, how do you find the best social login plugin for WordPress? Should you prioritize the number of social providers, compatibility with WooCommerce, or GDPR readiness? And more importantly, can a WordPress plugin social option scale with your growing user base?
This blog is your comprehensive guide to the top WP social media plugin solutions out there. We’ll cover what social login is, why it matters for your WordPress site, and which plugins deliver the best mix of functionality, user experience, and scalability. Whether you're building a small blog or a high-traffic SaaS product, there’s a social login plugin built for you and we’re here to help you find it.
![]()
What Is a Social Login Plugin in WordPress?
Imagine visiting a website and instead of typing your full name, email, creating a password (twice!), and verifying through email, you just click “Continue with Google” and you’re in. That’s social login in action. It’s quick, frictionless, and exactly what modern users expect.
A social login plugin in WordPress enables this one-click experience by integrating third-party social platforms like Google, Facebook, Apple, LinkedIn, GitHub, and others into your site’s login and registration process. Instead of forcing users to create a new account from scratch, they can sign in using credentials they already trust and use daily.
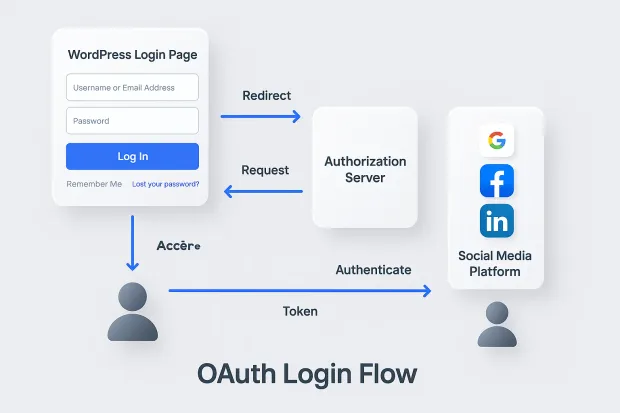
Technically speaking, these plugins work through secure authorization protocols like OAuth 2.0 and OpenID Connect (OIDC). When a user clicks a social login button, they’re redirected to the selected provider (like Google or Facebook), which authenticates them and returns a token to your WordPress site.
That token confirms the user’s identity, allowing your site to log them in or create a new account on the fly, no extra passwords, no wasted time.
What makes a WordPress social media plugin especially powerful is how easy it makes all of this. You don’t need to write a single line of code. Whether you're a beginner blogger or a developer managing a multi-site WooCommerce network, the right plugin WordPress social tool can plug-and-play into your workflow.
Most social media plugin WordPress options also offer customization features like choosing which providers to show, styling the buttons to match your branding, and even mapping user profile data (like name, email, or avatar) to your site’s user database. And if you go with a more robust solution like LoginRadius, you also get enterprise-grade features like identity security, user analytics, and consent management baked in.
In short, a wp social plugin bridges the gap between what users want and what your website offers, delivering instant access while making your registration process smarter and simpler.
Why Add a Social Media Login to WordPress?
Think about the last time you signed up for something online. If you saw 10 fields asking for your name, email, password, confirmation, and maybe even your birthdate, did you go through with it? Or did you silently close the tab and move on?
That hesitation is real, and it’s one of the biggest reasons users drop off during registration.
Now imagine replacing that lengthy form with a simple, familiar button: “Continue with Google” or “Sign in with Facebook.” Click. Done. You’re in. That’s the magic of social login and why it’s become a must-have for modern websites.
Adding a social login plugin to your WordPress site isn’t just a trend. It’s a direct response to how people browse, interact, and make decisions online. Here’s why it matters:
1. Reduced Friction - Higher Conversions
Long registration forms are conversion killers. Social login shortens the signup process to just a click, no password creation, no email verification. For ecommerce sites, membership platforms, or forums, that means fewer bounces and more signups.
2. Mobile-First Experience
Typing on mobile is painful. A WordPress social media plugin ensures that mobile users can register and log in effortlessly, improving the overall user experience on smartphones and tablets.
3. More Accurate User Data
When users sign up using social accounts, you get access to verified profile data like name, email, profile picture, and even location (depending on permissions). This not only helps personalize the experience but also reduces fake signups and bots.
4. Fewer Password Resets
No more forgotten passwords or endless reset emails. Since users rely on their existing social accounts, the need for managing yet another password is eliminated.
5. Builds Trust Through Familiarity
Seeing options like “Login with Google” or “Continue with LinkedIn” adds a layer of trust. Users are more likely to log in when they recognize and trust the provider handling their data.
In a nutshell, adding a WordPress social media plugin is one of the smartest ways to meet your users where they are on platforms they already use daily. Whether you run a WooCommerce store, a membership site, or a niche blog, a social media login plugin streamlines the experience and keeps users coming back.
And the best part? With today’s top plugin WordPress social tools, setting this up is easier than ever, even if you’re not a developer.
Best Social Login Plugins for WordPress
Now that we know why social login is a game-changer, let’s get into the real reason you're here: finding the best social login plugin for WordPress.
The WordPress plugin ecosystem is massive, and while that's great for variety, it can also be overwhelming. Some plugins are lightweight and free, ideal for bloggers or small businesses.
Others are full-fledged identity solutions meant for growing ecommerce brands or high-traffic membership sites. And then there are tools that try to do everything sometimes at the cost of simplicity or performance.
To save you hours of research, we’ve curated this list of the top WordPress social plugin options based on key criteria:
-
Ease of setup (especially for non-tech users)
-
Number of supported social platforms
-
GDPR/compliance features
-
Compatibility with other plugins (WooCommerce, BuddyPress, Elementor)
-
Design flexibility and branding options
-
Scalability and support
Whether you're looking for a lightweight wp social media plugin or a robust social media plugin WordPress solution that can scale with your user base, you’ll find your match below.
1. LoginRadius Social Login Plugin
Enterprise-grade authentication with a developer-first experience.
-
Supports: 40+ social platforms (Google, Facebook, Apple, GitHub, etc.)
-
Key Features:
-
Hosted login pages + customizable branding
-
Consent management, GDPR/CCPA-ready
-
Advanced analytics and fraud prevention
-
Pros: Developer-friendly APIs, fast performance, secure
-
Cons: Might be overkill for smaller blogs
-
Best For: SaaS platforms, large businesses, regulated industries
-
Pricing: Free tier available; premium features for enterprise
2. Nextend Social Login
A crowd-favorite with an easy setup process.
-
Supports: Google, Facebook, Twitter, Microsoft, Apple (Pro)
-
Key Features:
-
One-click login on registration/login forms
-
WooCommerce and BuddyPress compatibility
-
Drag-and-drop UI customization
-
-
Pros: Beginner-friendly, decent free features
-
Cons: Limited platform support unless upgraded
-
Best For: Bloggers, personal brands, small business sites
-
Pricing: Free with paid extensions
3. Super Socializer (Heateor)
An all-in-one solution for social login, sharing, and commenting.
-
Supports: 10+ platforms
-
Key Features:
-
Social share buttons
-
Commenting with social profiles
-
-
Pros: Lightweight and versatile
-
Cons: UI feels slightly outdated
-
Best For: Publishers, content-heavy blogs
-
Pricing: Free; premium add-ons available
4. MiniOrange Social Login
Powerful plugin with flexible identity features.
-
Supports: 30+ platforms (incl. gaming, dev tools, etc.)
-
Key Features:
-
Multiple login methods (QR code, OTP, etc.)
-
Role-based redirection
-
Customizable UI and button placements
-
-
Pros: Highly configurable
-
Cons: Can be complex for beginners
-
Best For: Multi-role platforms, communities
-
Pricing: Free basic version; premium for full features
5. OneAll Social Login
Privacy-first plugin built for compliance.
-
Supports: 20+ platforms
-
Key Features:
- GDPR/CCPA compliance
- Auto-linking existing accounts
- Central user dashboard
-
Pros: Trusted by big brands; secure data handling
-
Cons: UI customization could be better
-
Best For: Data-conscious organizations, publishers
-
Pricing: Free up to 2500 users/month; paid plans after
6. WP Social (by QuadLayers)
Modern design meets WooCommerce compatibility.
-
Supports: Google, Facebook, Twitter, LinkedIn
-
Key Features:
- Button shortcode generator
- WooCommerce login form integration
- Simple admin panel
-
Pros: Great design, easy to use
-
Cons: Fewer supported providers
-
Best For: Ecommerce stores
-
Pricing: Free with Pro upgrade
7. Youzify (BuddyPress Add-on)
Builds complete social profiles + login.
-
Supports: Google, Facebook, Instagram
-
Key Features:
-
Custom user profile builder
-
Followers, posts, media uploads
-
Member directories
-
-
Pros: Great for community building
-
Cons: Requires BuddyPress; heavier load
-
Best For: Online communities, clubs, forums
-
Pricing: Paid only
8. PeepSo Social Login
Niche plugin for PeepSo-powered communities.
-
Supports: Facebook, Google
-
Key Features:
- Easy onboarding
- Syncs with PeepSo profile fields
-
Pros: Tight integration
-
Cons: Limited to PeepSo framework
-
Best For: Sites already using PeepSo
-
Pricing: Paid only
Social Login Plugin Comparison Table
| Plugin | Free Version | ## of Social Providers | GDPR Compliant | WooCommerce Support | Best For |
|---|---|---|---|---|---|
| LoginRadius | Yes | 40+ | Yes | Yes | Enterprise sites, SaaS platforms |
| Nextend Social Login | Yes | 3 (Free) / 5+ (Pro) | Partial | Yes | Bloggers, small business sites |
| Super Socializer | Yes | 10+ | Yes | Yes | Publishers, content-heavy blogs |
| MiniOrange | Yes | 30+ | Yes | Yes | Complex user flows, community platforms |
| OneAll | Yes (limit) | 20+ | Yes | Yes | Privacy-first organizations |
| WP Social | Yes | 4 | Partial | Yes | Ecommerce brands, WooCommerce sites |
| Youzify | No (Paid) | 5+ | Yes | Yes (via BuddyPress) | Social communities, member platforms |
| PeepSo Social Login | No (Paid) | 2 | Yes | No | PeepSo community-based sites |
What are the real benefits of social login to WordPress?
We’ve all heard the phrase “don’t make me think,” and that perfectly sums up what users want when signing into a website. They don’t want to remember another password. They don’t want to fill out lengthy registration forms. They just want to get in, fast.
That’s exactly why adding a social login plugin to your WordPress site isn’t just a “nice-to-have” feature anymore; it’s a competitive advantage.
Here’s how a WordPress social media plugin actually helps your site win, both on the frontend (user experience) and backend (site performance and marketing).
1. Instant Login - Happier Users
Social login removes the barriers between interest and action. With one click, your users do not need to create a new account or verify anything. Whether it's an ecommerce checkout, forum signup, or membership access, a plugin WordPress social tool lets users skip the hassle and dive straight into the experience.
2. Mobile-First Convenience
On mobile, even typing an email feels like a chore. But tapping “Continue with Google” or “Login with Facebook”? That’s effortless. A good wp social plugin ensures your mobile visitors can access your content with zero friction, boosting engagement across devices.
3. Reduced Drop-Offs at Registration
Abandoned registrations are often caused by long forms, password fatigue, or distrust. A social media login plugin builds trust through familiar providers and speeds up onboarding, leading to higher conversion rates.
4. Better Data, Cleaner Profiles
When users register through social login, your site gains access to verified, up-to-date profile information like name, email, and avatar. This helps you personalize the user experience, reduce spam signups, and clean up your database. Many of the best social plugin for WordPress options even let you customize which fields to pull in.
5. Lower Support Load (Bye-Bye Password Reset Tickets)
Forget password recovery emails and support tickets. With social login, your users rely on their existing credentials, meaning fewer forgotten passwords, less downtime, and lower admin overhead.
6. Stronger Personalization and Marketing
By accessing social profile data (ethically and with consent), you can better segment your audience, send targeted campaigns, and deliver experiences that feel tailored without asking users to fill out endless forms.
Whether you’re running a WooCommerce store, a digital product site, a gated content portal, or a community forum, a good social media plugin for WordPress integration enhances usability and drives better results. It's not just about login, it’s about building smarter, faster, and more human-first digital experiences.
Conclusion
In a world where users have endless choices and zero patience, giving them a fast, secure, and seamless way to log into your site is no longer optional; it’s essential. That’s the power of a good WordPress social plugin.
Whether you're managing a content-heavy blog, a high-converting ecommerce site, or a thriving online community, the right social media login plugin simplifies onboarding, builds trust, and improves user engagement across every touchpoint.
But remember: not all plugins are created equal. Some are great for lightweight use cases. Others, like LoginRadius, are designed for businesses that need more than just login buttons. If you’re looking for a plugin WordPress social solution that scales with you, protects user data, and gives you complete control over your brand experience, LoginRadius is built for that.
From instant Google/Facebook login to GDPR-compliant identity management, LoginRadius offers a powerful WP social plugin that’s easy to implement and ready for enterprise scale.
Ready to simplify your login experience? Try the LoginRadius WordPress Social Login Plugin and turn casual visitors into loyal users—no passwords required.
FAQ’s
1. Why should I use a social login plugin on my WordPress site?
A: Using a social login plugin simplifies the login and signup process for your users, reducing friction and boosting conversions. It eliminates the need for passwords, speeds up registration, and enhances the overall user experience, especially on mobile.
2. Do social login plugins support multiple social networks?
A: Yes, most modern WordPress social media plugins support multiple providers like Google, Facebook, Apple, LinkedIn, and GitHub. Depending on the plugin, you can enable several options to let users choose their preferred login method.
3. Can I customize the login buttons or design?
A: Absolutely. Many WordPress social plugin tools allow you to customize the appearance, size, placement, and even the branding of social login buttons so they blend seamlessly with your site's theme and UI.