Introduction
Authorization used to be simple. You logged in. You got a role. The role decided what you could do.
That model worked when applications were small, teams were internal, and data lived in one place. Most systems didn’t question who you were beyond your job title. If you were an “Admin,” you were an Admin everywhere.
That world doesn’t exist anymore.
Modern systems deal with partners, APIs, temporary access, cross-tenant users, shared resources, AI agents, and constantly shifting risk signals. A support engineer might need access to production data for ten minutes. A partner user might see only one slice of a shared dataset. A single user might act as an admin in one tenant and a viewer in another, sometimes in the same session.
This is where the conversation around rbac vs abac vs pbac becomes unavoidable.
Role-based access control is still widely used, and for good reason. It gives structure. It’s easy to explain. Auditors understand it. But on its own, it starts to strain when access decisions depend on context rather than titles.
Attribute-based access control brings that missing context. Device posture. Location. Subscription tier. Risk signals. Ownership. But teams often discover that ABAC logic, when scattered across services, becomes difficult to govern and nearly impossible to reason about at scale.
Then there’s policy-based access control, often misunderstood, sometimes treated as a buzzword, but increasingly central to how large systems make consistent authorization decisions without hardcoding logic everywhere.
So the real question isn’t RBAC or ABAC or PBAC. It’s how these authorization models work together inside real systems.
In this blog, we’ll break down authorization methods the way teams actually encounter them in production not as theory, but as patterns. You’ll see where each model fits, where it breaks, and how dynamic authorization emerges when RBAC provides structure, ABAC adds context, and PBAC keeps everything governable.
Whether you’re designing access control for a growing SaaS product or trying to untangle permissions that have quietly grown out of control, this will help you understand what’s happening and why.
Authentication Isn’t the Problem Authorization Is
Most teams don’t lose sleep over login anymore.
Authentication has matured. Between SSO, MFA, passkeys, and managed identity providers, verifying who someone is has become predictable and reliable. Once users are in, sessions are established, tokens are issued, and identity feels “done.”
That’s where the real problems usually start.
Authorization decides what happens after authentication. It answers questions that change constantly:
-
Can this user act on this resource?
-
Does their role still apply in this tenant?
-
Is the context safe enough right now?
-
Should access be allowed temporarily or not at all?
These decisions aren’t static. They vary by time, environment, ownership, risk, and intent. And they don’t happen once. They happen repeatedly at APIs, services, and data boundaries.
This is why access issues show up even in systems with strong authentication. Authorization logic is often fragmented, inconsistently enforced, or buried inside application code. Over time, exceptions accumulate, rules drift, and access becomes harder to explain than to implement.
Dynamic authorization exists because static permission checks can’t keep up with dynamic systems. The complexity isn’t accidental, it's a reflection of how modern applications actually operate.
RBAC, ABAC, and PBAC What Each Model Is Actually Good At
Debates around rbac vs abac vs pbac often assume these models are competing alternatives. In practice, they solve different parts of the same problem.
Each model answers a specific question:
-
RBAC answers who generally should be allowed to do what
-
ABAC answers under what conditions access should change
-
PBAC answers how access decisions are defined, evaluated, and governed
Understanding what each model is good at and where it breaks is the difference between a clean access strategy and one that slowly collapses under its own exceptions.
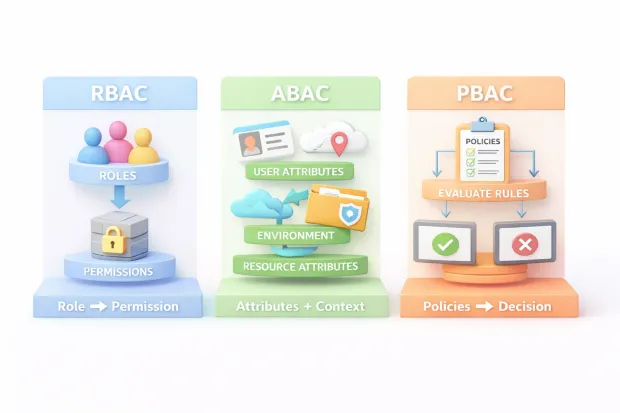
RBAC: Structured, Understandable, and Easy to Govern
Role-based access control is still widely used because it creates order fast.
RBAC maps users to roles and roles to permissions. That structure is intuitive. Teams can explain it. Auditors can review it. Administrators can manage it without reading code.
For stable environments internal tools, back-office systems, well-defined job functions RBAC works extremely well. It establishes clear boundaries and reduces ambiguity.
Problems arise when roles are asked to carry too much meaning.
Real users don’t behave uniformly. They switch contexts, act temporarily, and cross boundaries. RBAC struggles when access depends on factors outside of job function. The result is role sprawl roles created to capture exceptions rather than intent.
RBAC doesn’t fail because it’s outdated. It fails when it’s treated as a complete authorization strategy instead of a foundational layer.
ABAC: When Context Becomes the Decision Driver
Attribute-based access control exists because access decisions rarely depend on identity alone.
ABAC evaluates attributes facts about the user, the resource, and the environment to decide whether an action should be allowed. This enables fine-grained decisions that RBAC can’t express cleanly.
Attributes can represent ownership, location, device trust, subscription level, risk signals, or tenant boundaries. They allow systems to answer questions like “should this role apply here and now?”
This flexibility is powerful, but it comes with a trade-off. Without discipline, ABAC logic spreads. Attributes are interpreted differently across services. Rules are embedded directly into application code. Over time, access behavior becomes difficult to predict or audit.
ABAC is best used as a refinement mechanism not a replacement for structure. It works when attributes are consistent, trusted, and evaluated through a shared decision process.
PBAC: Policies as the Control Layer
Policy-based access control focuses less on what data is used and more on how decisions are managed.
PBAC introduces policies as first-class artifacts. Instead of hardcoding access rules into applications, teams define policies that a decision engine evaluates at runtime.
This separation matters.
Policies make authorization explicit. They capture intent in a way that can be reviewed, tested, versioned, and audited. They allow access logic to evolve without forcing application rewrites.
PBAC works especially well in complex systems because it absorbs both roles and attributes as inputs. A policy might reference roles, attributes, relationships, or context all without locking logic into one service.
PBAC doesn’t simplify authorization decisions. It makes them visible and governable. That visibility is what keeps dynamic systems under control as they scale.
ABAC vs PBAC: Why These Two Get Confused
ABAC and PBAC get mixed up because, in real systems, they often show up together.
ABAC focuses on inputs. It answers the question: what facts are available at decision time? User attributes, resource metadata, environment signals all of these feed into whether access should be allowed. When teams adopt ABAC, they start thinking in conditions instead of titles, which feels like a big leap forward.
PBAC focuses on control. It answers a different question: where is the decision logic defined, evaluated, and governed?
Here’s the subtle but critical distinction. You can write ABAC logic directly inside application code, scattered across services. That’s still ABAC but it’s unmanaged. PBAC pulls that logic out into policies that can be reviewed, tested, and enforced consistently.
This is why teams often say, “We’re already using ABAC,” and still struggle with authorization drift. They’re using attributes, but they don’t have a policy layer holding decisions together.
ABAC decides what information matters. PBAC decides how decisions are expressed and controlled.
Once you separate those concerns, the confusion fades and design choices become much clearer.
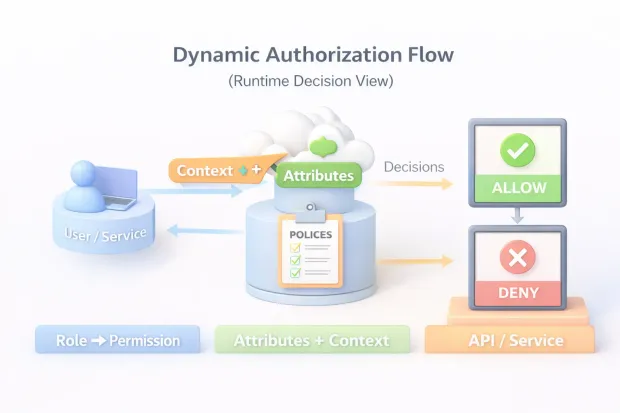
What Dynamic Authorization Looks Like in a Real System
Dynamic authorization isn’t a single feature or product. It’s a pattern that emerges when access decisions are evaluated continuously instead of assumed permanently.
In a real system, access isn’t granted once and forgotten. Every meaningful action triggers a decision. That decision pulls together identity context, resource state, and environmental signals at that moment.
A user’s role might say they can approve something. Attributes might say they’re acting outside their normal region. A policy might say approval is allowed only if risk is low and ownership is verified.
What makes this dynamic isn’t complexity, it's timing.
Decisions happen close to the point of use, not just at login. They’re re-evaluated as context changes. That’s why enforcement usually happens at APIs or service boundaries, even if policies live centrally.
Dynamic authorization accepts that access is temporary, conditional, and situational. Systems that treat access as static inevitably accumulate exceptions. Systems that treat it as dynamic stay adaptable without losing control.
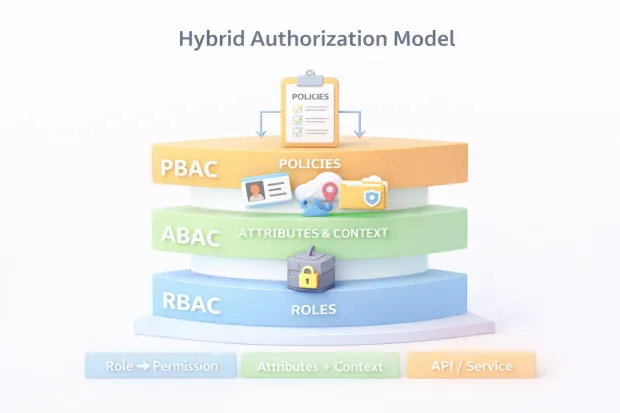
A Hybrid Model That Actually Works
Most successful access control strategies stop arguing about models and start layering them.
RBAC does what it’s good at: establishing baseline structure. It answers who should generally have access and prevents chaos in early design stages. Removing RBAC rarely simplifies systems it just hides complexity elsewhere.
ABAC refines those permissions. It introduces context so access adapts without exploding the role hierarchy. Instead of creating “Admin-But-Only-For-This-Case” roles, attributes handle nuance.
PBAC governs the entire decision process. It defines how roles and attributes interact, where logic lives, and how changes are managed over time.
This hybrid approach works because it mirrors how humans think about access. First, who are you? Then, what’s going on right now? Finally, what rules apply in this situation?
When teams treat these layers as complementary instead of competing, authorization becomes easier to reason about even as systems grow more complex.
RBAC vs Policy Based Access Control in AWS
AWS is often used as an example in the role based access control vs policy based access control AWS debate, but the reality is more blended than the comparison suggests.
IAM roles in AWS establish identity and trust. They define who or what can assume an identity and under what conditions. That’s classic RBAC territory.
IAM policies, however, are where authorization actually happens. Policies define actions, resources, and conditions. They determine whether a request is allowed at runtime.
Those conditions tags, request attributes, environment signals introduce ABAC-style behavior. The evaluation engine that interprets policies acts as a PBAC system.
So AWS doesn’t choose between RBAC and PBAC. It layers them. Roles provide structure. Policies encode logic. Conditions inject context.
Understanding this prevents teams from misusing IAM. When roles start multiplying uncontrollably, it’s usually because policy logic was pushed into identity design instead of expressed where it belongs.
Common Failure Patterns Teams Repeat
Authorization failures tend to follow familiar paths.
Roles accumulate because no one wants to break existing access. Temporary roles become permanent. Edge cases turn into defaults. Over time, nobody remembers why a role exists only that removing it feels risky.
Attributes get added without standards. Different services interpret the same attribute differently. Trust levels aren’t documented. What started as flexibility becomes ambiguity.
Policies are copied instead of designed. Slight variations creep in. Enforcement becomes inconsistent. Audits turn painful.
Worst of all, authorization logic leaks into application code. Business rules and access rules intertwine. Changes require redeployments. Security decisions become side effects.
None of these failures happen overnight. They’re the result of small shortcuts taken repeatedly in systems that keep growing.
Best Practices for Secure Access Controls in Complex Systems
Strong authorization systems aren’t built by choosing the “best” model. They’re built by respecting a few principles.
Design permissions around resources and actions, not users. This keeps access understandable as teams and identities change.
Treat attributes as shared infrastructure. Define them carefully. Document their meaning. Decide where they come from and when they can be trusted.
Centralize decision logic, even if enforcement stays distributed. A single source of truth prevents silent drift.
Log authorization decisions not just outcomes, but why a decision was made. Visibility matters when something goes wrong.
Test policies the way you test code. Expected outcomes, edge cases, regressions. Authorization bugs are still bugs.
And always default to least privilege, expanding access deliberately instead of reacting to failures by opening doors wider.
When these practices are in place, dynamic authorization stops feeling risky. It becomes predictable just flexible enough to match how real systems behave.
Conclusion
If there’s one pattern that shows up again and again, it’s this: teams don’t fail at authorization because they chose the “wrong” model they fail because they tried to force one model to do everything.
RBAC still remains useful. It gives systems a backbone. It answers basic questions quickly and keeps access understandable for humans. For many organizations, removing roles altogether would create more confusion, not less.
ABAC becomes necessary the moment access depends on conditions that roles can’t express. When context matters device trust, tenant boundaries, ownership, environment, risk attributes stop being optional. They become the difference between overexposed systems and controlled ones.
PBAC ties the whole thing together. Not by replacing roles or attributes, but by giving teams a consistent way to express, evaluate, and govern decisions. Policies make authorization explicit. They make intent visible. They make audits survivable.
This is why dynamic authorization isn’t a new access control type, it's a way of combining access control models so decisions adapt without becoming unpredictable.
For simpler systems, RBAC may be enough. For context-heavy systems, ABAC fills critical gaps. For complex, distributed environments, PBAC becomes the control plane that keeps everything from drifting.
The goal isn’t sophistication for its own sake. It’s confidence.
Confidence that users have only the access they need.
Confidence that exceptions don’t silently turn into permanent privileges.
Confidence that access decisions can evolve without rewriting your application every quarter.
If your current approach feels brittle, inconsistent, or overly manual, it’s probably not because authorization is hard. It’s because your system has outgrown a single model.
Dynamic authorization is what happens when your access strategy finally grows up with your architecture.
FAQs
Q: What is the difference between RBAC, ABAC, and PBAC?
A: RBAC assigns access based on roles, ABAC refines access using attributes and context, and PBAC governs how authorization rules are defined and evaluated. Most modern systems combine all three rather than choosing one.
Q: When should teams use dynamic authorization instead of static RBAC?
A: Dynamic authorization becomes necessary when access depends on context like tenant, device, risk, or ownership. If roles keep multiplying to handle exceptions, the system has already outgrown static RBAC.
Q: Is policy based access control the same as ABAC?
A: No. ABAC focuses on using attributes in decisions, while PBAC focuses on managing authorization logic through policies. ABAC often feeds data into PBAC rather than replacing it.
Q: How does AWS use RBAC, ABAC, and PBAC together?
A: AWS uses roles for identity, policies for authorization logic, and conditions for context-aware decisions. The IAM policy evaluation engine effectively combines all three models at runtime.



