Introduction
If you’ve ever struggled to manage user access in Salesforce, whether it’s for external partners, customers, or even internal teams, you’re not alone. As the ecosystem around Salesforce grows more complex, so does the need for streamlined and secure login experiences.
Think about it: every extra login prompt, every forgotten password, every form field asking for details a user has already shared elsewhere, all of it adds friction. And in today’s world, friction costs more than just time. It costs trust, productivity, and even conversions.
That’s where Social Sign-On comes in. By allowing users to log in using existing identities from platforms like Google, Facebook, or LinkedIn, you reduce barriers and boost engagement, all while maintaining enterprise-grade security.
But if you're wondering how to actually implement social sign-on in Salesforce with its many menus, metadata settings, and security rules, this guide is here to help. We’ll break it all down: what social SSO is in the context of Salesforce, why it matters for your users and your IT team, and how to implement it step-by-step (with or without a dedicated identity provider like LoginRadius).
Whether you’re a developer building a custom portal, an admin managing Community Cloud, or an architect setting up federated identity across ecosystems, this blog will equip you to deliver a login experience users will love and your security team will approve.
Understanding Social Sign-Ons in Salesforce
Logging into Salesforce doesn’t have to mean remembering yet another password. In fact, it shouldn’t.
That’s the whole promise of Social Sign-On: a way to let users access Salesforce using credentials they already trust, like Google, Facebook, LinkedIn, or even enterprise identity providers. But how does it actually work in Salesforce?

Let’s break it down in simple terms.
At its core, Social Sign-On in Salesforce is a form of Single Sign-On (SSO) that allows external authentication. Instead of storing usernames and passwords in Salesforce, the platform delegates the login process to a social identity provider. That identity provider verifies the user, and Salesforce trusts the result.
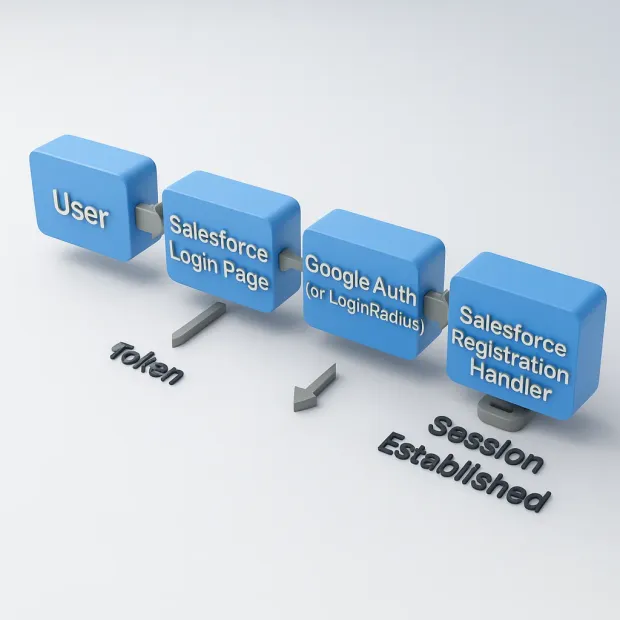
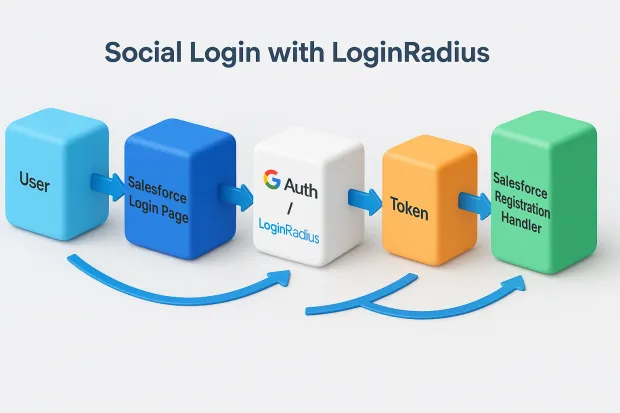
Behind the scenes, this handshake is powered by OAuth 2.0 and OpenID Connect protocols, modern, secure standards that enable token-based logins. Salesforce acts as the Service Provider, while your chosen social login (or LoginRadius as a central identity provider) acts as the Identity Provider (IdP).
-
Single Sign-On in Salesforce: A method that lets users log in to Salesforce via external authentication (like social logins or enterprise SSO), eliminating the need for separate Salesforce credentials.
-
Salesforce Identity Provider (IdP): A trusted system that performs the authentication on Salesforce’s behalf. It can be a social platform (like Google) or a unified platform like LoginRadius.
-
OAuth 2.0: The protocol that securely grants access without exposing user credentials.
-
Registration Handler: A custom Apex class in Salesforce that maps the user info received from the IdP into a valid Salesforce user.
Real-World Example:
Let’s say a new user visits your Salesforce-powered customer portal. Instead of registering from scratch, they click “Continue with Google.”
Google authenticates them → Salesforce receives a token → Salesforce maps or creates the user internally → The user lands on their dashboard.
No new passwords. No manual approval queues. Just one smooth, secure experience.
In short, Salesforce SSO setup via social providers removes complexity for your users and your team.
Why Implement Social Sign-On in Salesforce?
Let’s face it your users don’t want to manage yet another password. And your IT team doesn’t want to deal with password resets, weak credentials, or support tickets either. Social Sign-On helps you eliminate both problems in one go — while improving the way your users interact with your Salesforce environment.
But convenience is just the beginning.
Here’s why implementing Social Sign-On in Salesforce is a strategic move - whether you’re running a partner portal, customer community, or employee interface.
1. Faster Onboarding, Lower Drop-offs
Ever filled out a registration form only to give up halfway through? Your users have too. By allowing them to log in using an existing identity like Google or LinkedIn you cut the signup time to seconds. No extra fields. No confirmation emails. Just one click and they’re in.
For Salesforce portals and Experience Cloud sites where conversion is critical, this speed can make all the difference.
2. Consistent Identity Across Platforms
If your users already sign in to other platforms using social SSO, why make Salesforce an exception?
With social login, you can create a federated identity across apps. Whether a user logs in through your product, support system, or Salesforce portal, their profile stays consistent — and that helps you track, personalize, and support them more effectively.
3. Enterprise-Grade Security Without the Hassle
SSO might sound like a “consumer convenience,” but it’s built on hardened security standards like OAuth 2.0 and OpenID Connect.
By delegating authentication to trusted identity providers (like Google or LoginRadius), you reduce your risk surface. You also gain access to layered protections like multi-factor authentication, device verification, and fraud detection without needing to build them into Salesforce yourself.
4. Less Work for Your Admins and IT Team
With Salesforce SSO setup using social providers or a unified CIAM like LoginRadius, your admins no longer need to:
- Manually create user accounts
- Reset passwords
- Monitor duplicate identities
Everything flows from the user’s existing identity and maps directly into Salesforce using a registration handler.
5. Better User Experience = Higher Engagement
Friction kills conversions. When your login flow is clunky, users bounce. When it’s seamless, they engage.
Social login gives you a branded, modern experience that users are familiar with. And when implemented via LoginRadius, you can customize the look and feel, language, and behavior to align perfectly with your Salesforce branding.
In short, social login in Salesforce is a win-win: faster for users, safer for your organization, and simpler to manage.
Real-World Example
A global SaaS company managing partner onboarding through Salesforce Communities struggled with high support costs from account provisioning and password resets. After integrating LoginRadius for Google and LinkedIn SSO, they saw a 40% drop in password reset tickets, 22% increase in monthly logins, and a 90% faster onboarding time. All without writing custom flows for each provider.
Implementing Social Sign-On in Salesforce
So you’re ready to reduce login friction and improve identity security in Salesforce? Awesome.
Whether you’re building a Salesforce Community, setting up a partner portal, or streamlining customer access, implementing social single sign-on in Salesforce follows a logical flow and we’re breaking it down step-by-step.
You can configure social login directly with identity providers like Google or Facebook. Or, if you’re aiming for scalability, branding, and central management, you can plug in an identity platform like LoginRadius to do the heavy lifting for you.
Let’s walk through the implementation.
Step 1: Enable My Domain and Identity Features
Before anything else, you need to activate My Domain, which is required to customize login flows and connect external IdPs.
Go to Setup → My Domain
Enter a unique subdomain and deploy to users
Once done, go to Authentication Configuration
Enable “Authentication Service” to allow social login on the login page
This gives Salesforce the flexibility to call out to external services (like Google or LoginRadius) when a user initiates login.
Step 2: Register Your Authentication Provider
This is where the magic starts. You tell Salesforce where to send users for authentication.
Navigate to Setup → Auth. Providers
Click New and choose an option (e.g., Google, Facebook, or OpenID Connect)
Fill in:
Name
Consumer Key and Secret (from your social provider dashboard)
Authorize Endpoint URL and Token Endpoint URL
Callback URL (usually auto-generated by Salesforce)
Each Auth Provider connects Salesforce to an external identity source — just like a handshake agreement.
Step 3: Create a Registration Handler (Apex Class)
Once Salesforce receives a valid token from your identity provider, it needs to know what to do with it. That’s where a Registration Handler comes in.
This is a custom Apex class that:
- Maps incoming user data (like name, email) to a Salesforce user or contact
- Automatically creates or updates the user as needed
- Sets their profile, role, permissions, and license
Step 4: Use LoginRadius as a Central Identity Provider (Recommended for Scale)
Instead of configuring individual social logins one by one, you can plug in LoginRadius as your Salesforce identity provider.
Benefits:
- One place to manage all social logins (Google, Facebook, GitHub, etc.)
- Prebuilt connectors and SDKs
- Branded login screens, privacy-first UX
- Built-in fraud detection, progressive profiling, and analytics
How it works:
-
You configure LoginRadius as an OpenID Connect or SAML 2.0 provider in Salesforce
-
LoginRadius handles the social auth → Salesforce handles the session
This setup drastically reduces dev time, especially if your business needs to support multiple IdPs across portals, mobile apps, and more.
Sample OIDC Discovery URL and Claim Mapping for Salesforce
To connect LoginRadius to Salesforce using OpenID Connect, you’ll need the discovery URL and claims to map the user attributes.
Discovery URL Example:
https://<your-app-name>.hub.loginradius.com/.well-known/openid-configuration
Recommended User Claims for Mapping:
| Salesforce Field | LoginRadius OIDC Claim |
|---|---|
| Username | |
| FederationIdentifier | sub |
| FirstName | given_name |
| LastName | family_name |
Once you configure this in Salesforce’s Auth. Provider, the registration handler can map users based on your rules. You can also control login policies and MFA from within LoginRadius.
Step 5: Test and Verify Your Flow
Before going live:
-
Open the My Domain Login Page
-
Click the new social login button (e.g., “Login with Google”)
-
Walk through the flow:
- Are users redirected correctly?
- Is the token exchanged?
- Is the right user profile created or updated?
Use tools like Postman or browser developer tools to debug the auth token and user mapping, especially during the callback.
Conclusion
In today’s experience-first world, login shouldn’t feel like a roadblock. It should be invisible — quick, seamless, and secure.
That’s exactly what Social Sign-On in Salesforce delivers. Whether you're building customer portals, partner communities, or employee workspaces, enabling single sign-on in Salesforce helps you unlock faster access, fewer help desk tickets, and stronger identity assurance — all while improving user satisfaction.
And while you can piece together direct integrations with Google, Facebook, or LinkedIn, the smart choice for scale is leveraging an identity platform like LoginRadius. It gives you the flexibility to plug into multiple social providers, maintain centralized control, and deliver a branded, privacy-first login experience all without wrestling with token handling and Apex logic every time.
So if you're ready to go from complex to simple, from siloed to streamlined it starts at the login box.
Need help setting up SSO for Salesforce? Talk to our CIAM experts at LoginRadius
Because identity should be a growth enabler — not a blocker.
FAQs
1. What are the prerequisites for enabling Social Sign-On in Salesforce?
A: Before enabling Social Sign-On, you need to set up My Domain, enable Authentication Services, and have the necessary OAuth credentials from your identity provider (e.g., Google, Facebook, or LoginRadius). Additionally, ensure that your Salesforce edition supports external identity providers.
2. How do I configure a connected app for social login in Salesforce?
A: You typically don't need to create a connected app for standard social providers; instead, you set up an Auth. Provider using built-in templates for Google, Facebook, etc. If you're using a custom IdP (like LoginRadius), you may configure it via OpenID Connect or SAML, and optionally register a connected app for more control.
3. What are the security considerations for using Social Sign-On?
A: Security best practices include using HTTPS for all endpoints, enforcing scopes and token expiry, enabling multi-factor authentication (MFA) at the IdP level, and using a custom registration handler to control user provisioning in Salesforce. Make sure your identity provider is compliant with standards like OAuth 2.0 and supports token validation.



