Introduction
Most SaaS teams think they have a scaling problem: more users, more traffic, more data. But in reality, the bigger risk is something else: broken tenant boundaries.
In a multi-tenant SaaS architecture, every customer shares the same system, same application, the same infrastructure, sometimes even the same database. The only thing keeping Tenant A from seeing Tenant B’s data is your authorization layer.
And that’s where things often fall apart.
Authentication gets all the attention. Users log in, tokens are issued, MFA is enabled it feels secure. But authentication only answers one question: Who is this user?
Authorization answers the one that actually matters in SaaS: What can this user access and are they strictly limited to their own tenant?
That’s not just a permissions problem. It’s an isolation problem.
In a well-designed system, tenant boundaries are enforced everywhere at the token level, in APIs, inside policies, and down to the database. There’s no reliance on “remembering to filter by tenant_id.” Because the moment isolation depends on developer discipline, it’s already fragile.
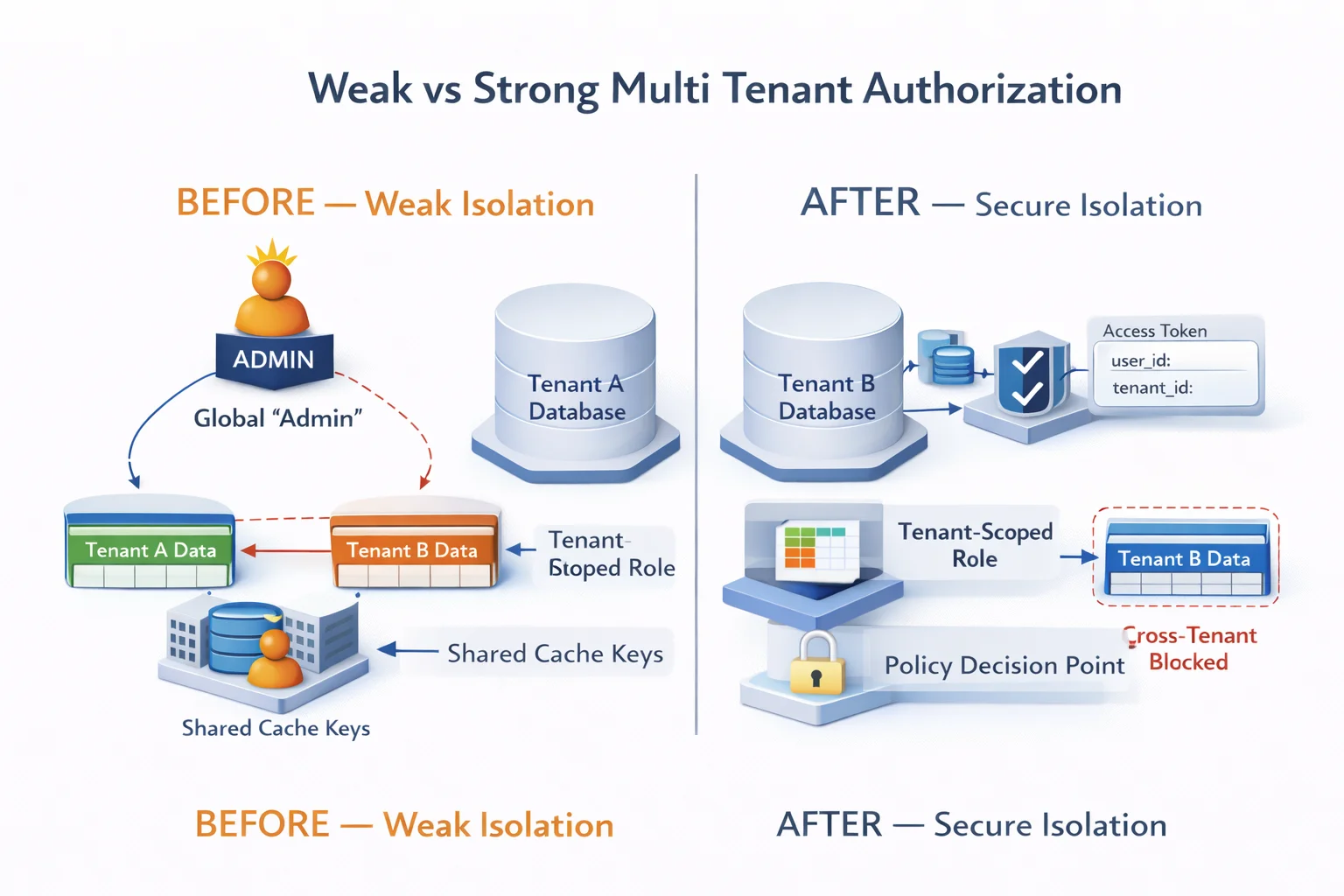
And here’s the reality most teams learn the hard way: Cross-tenant leaks don’t fail loudly, they slip through quietly.
-
A missing filter in one query.
-
A shared cache key.
-
An “admin” role that isn’t properly scoped.
Individually, they look harmless. Together, they break tenant isolation and with it, customer trust.
That’s why modern multi-tenant authorization isn’t optional or secondary. It’s foundational. Because in a shared environment, trust isn’t assumed. It has to be enforced consistently, at every layer.
What Is Multi-Tenant Authorization? (And Why RBAC Alone Isn’t Enough)
Multi-tenant authorization is an access control model in which permissions are scoped within a tenant boundary, ensuring that users can access only resources within their own tenant in a shared system.
In a multi-tenancy architecture, multiple organizations share the same application infrastructure. That means users from different companies operate inside the same runtime environment. The only thing preventing cross-tenant access is your authorization logic.
Authentication proves identity. Multi-tenant authentication and authorization are often mentioned together, but they solve different problems.
Authentication answers: Who are you? Authorization answers: What can you access? Multi-tenant authorization adds: Within which tenant boundary?
If your system validates identity but does not strictly enforce tenant scoping, isolation fails.
RBAC alone does not solve this. RBAC assigns permissions based on roles like “Admin” or “Editor.” But unless roles are explicitly scoped to a tenant, they can become dangerously broad.
An “Admin” role without a tenant context is a global privilege.
True multi-tenant authorization requires evaluating: The user identity, the tenant identity, the resource, and the action.
Miss one, and isolation weakens.
Multi Tenancy Architecture: Where Isolation Actually Begins
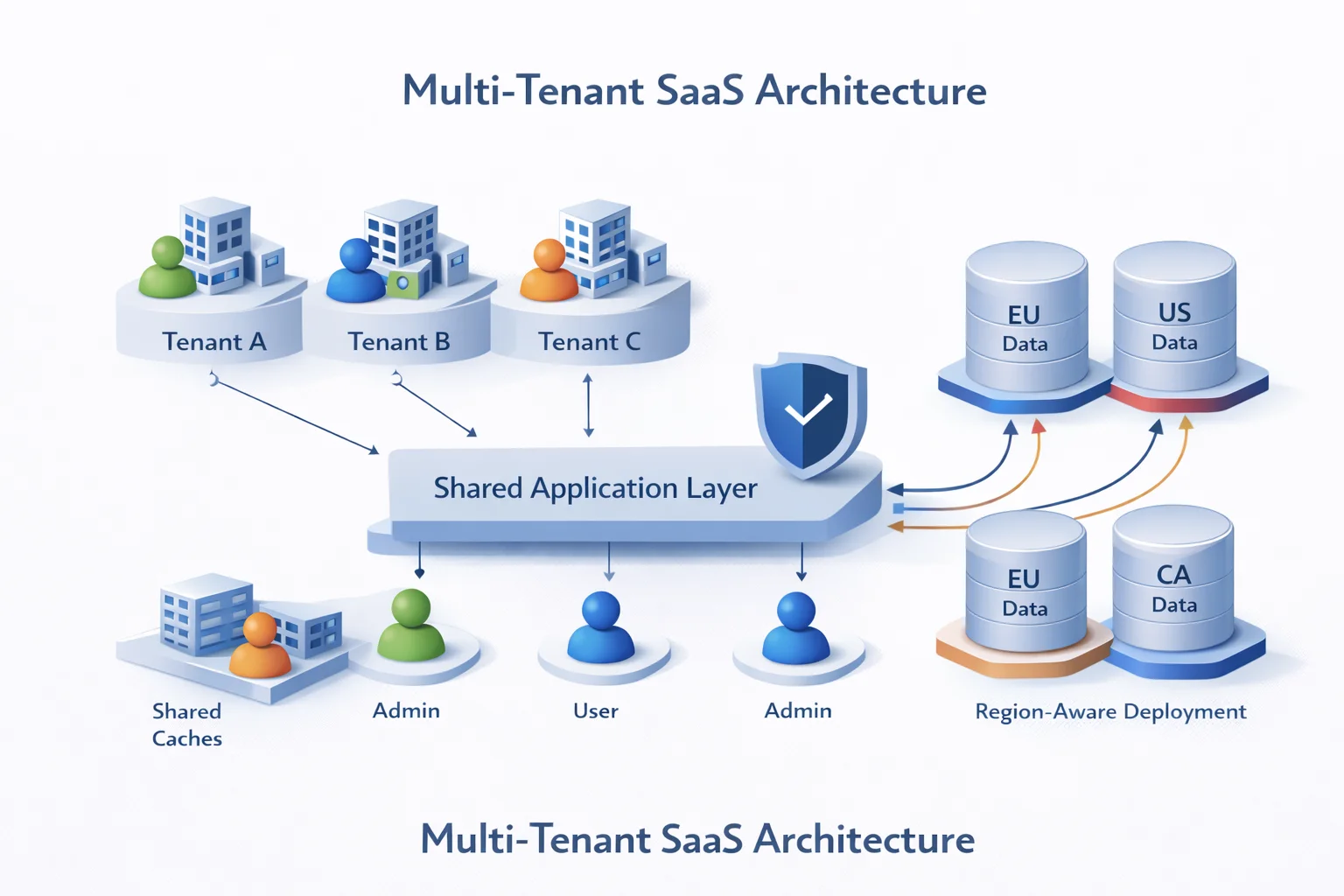
Before designing multi-tenant authorization, you must understand your multi-tenancy architecture. Isolation starts with a data structure.
The first model is a shared database, shared schema. All tenants store data in the same tables, separated by tenant_id. This is cost-efficient but highly dependent on strict query filtering.
Every read and write must include tenant scoping. Miss it once, and data crosses boundaries.
The second model is a shared database, separate schema. Each tenant has its own schema. This reduces accidental cross-tenant queries but still requires correct schema routing and authorization enforcement.
The third model is a separate database per tenant. This provides the strongest physical isolation but increases operational cost.
Architecture defines the potential blast radius. Authorization determines whether access is permitted. Regardless of the model, multi-tenant access control must consistently validate:
Does this user belong to this tenant, and are they allowed to perform this action?
Without deterministic enforcement, architecture alone is insufficient.
Why Multi-Tenant Access Control Fails (And Leaks Data Quietly)
Multi-tenant failures rarely occur due to dramatic breaches. They happen because of small authorization gaps.
One common issue is the lack of tenant context in access tokens. A user authenticates, but the JWT lacks tenant claims. The system then attempts to infer tenant context during request processing.
Another failure is trusting client-supplied tenant IDs. If the backend relies on a frontend parameter for tenant scoping, isolation is delegated to the browser.
Query oversight is frequent. A query filters by user ID but omits the tenant ID. In shared environments, overlapping identifiers can expose cross-tenant data.
Global roles create privilege inflation. An unscoped “Admin” role can unintentionally span multiple tenants.
Caching layers also introduce risk. Shared keys or tenant-agnostic namespaces can return incorrect data.
Isolation fails when authorization is inconsistently enforced across layers. In a multi-tenant data architecture, leaks are usually silent.
Tenant Isolation Patterns That Don’t Leak Data
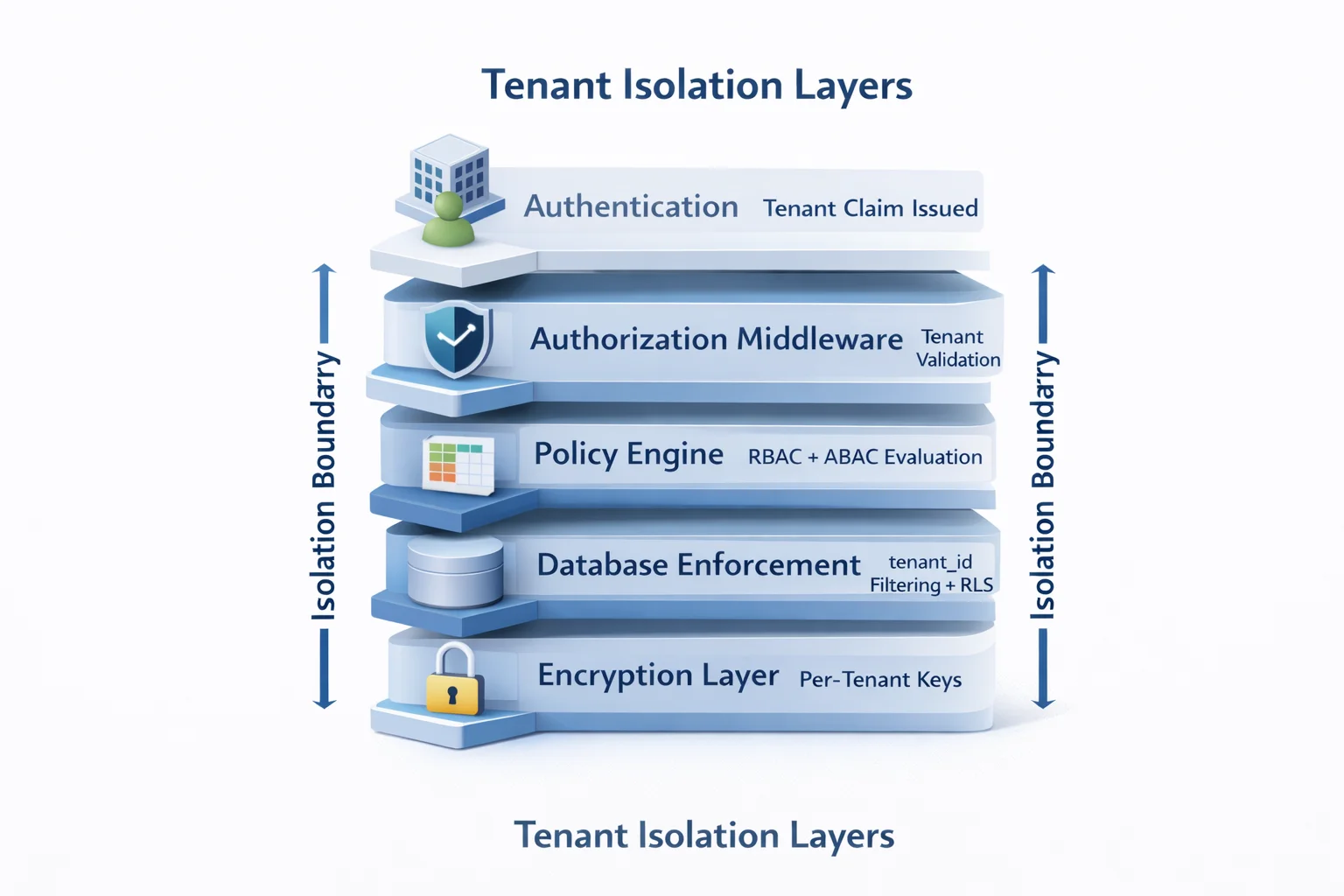
Multi-tenant authorization becomes reliable only when isolation is enforced structurally.
Tenant ID must be treated as a first-class security attribute. It should be embedded in the access token and validated server-side on every request.
Tenant context must be derived from trusted claims, not user input.
Roles must be tenant-scoped. “Admin of Tenant A” is distinct from “Admin of Tenant B.” Role evaluation must include tenant context.
A hybrid RBAC and attribute-based model supports fine-grained access control in a complex multi-tenant SaaS architecture.
Row-level security adds database-level enforcement. Even if the application fails to filter, the database blocks unauthorized rows.
Centralized, tenant-aware authorization middleware prevents scattered policy logic.
For high-security environments, per-tenant encryption keys introduce cryptographic separation.
Isolation must be enforced at: Token level, Middleware level, Policy level, Database level, Encryption level
Anything less relies on developer memory.
Real-World Multi Tenancy Example: B2B SaaS Without Boundary Confusion
Consider a B2B CRM platform serving 500 companies. Each tenant has its own users, data, and roles within the shared infrastructure.
Company A’s users should only access Company A’s resources. Company B must never see Company A’s data.
Multi-tenant authentication verifies that the user belongs to Company A. Authorization ensures every request is evaluated within that tenant boundary.
The system must ensure:
-
Access tokens include the tenant identity
-
Roles are tenant-scoped
-
APIs validate tenant context
-
Queries filter by tenant
-
Audit logs reflect tenant-aware access
Internal support access must be tightly scoped, time-bound, and logged.
Solutions like LoginRadius support tenant-aware token issuance, scoped roles, and centralized policy enforcement. Embedding tenant context in identity claims reduces inconsistent authorization logic across services.
Multi-tenant authorization prevents accidental overreach as systems scale.
Multi-Tenant Authentication and Authorization: How They Actually Work Together
This is where many systems go wrong they treat authentication and authorization as the same thing. They’re not.
Authentication answers: Who is this user?
Authorization answers: What can they access and within which tenant?
Both are critical, but they solve different problems. And in a multi-tenant system, they have to work in sync, not overlap.
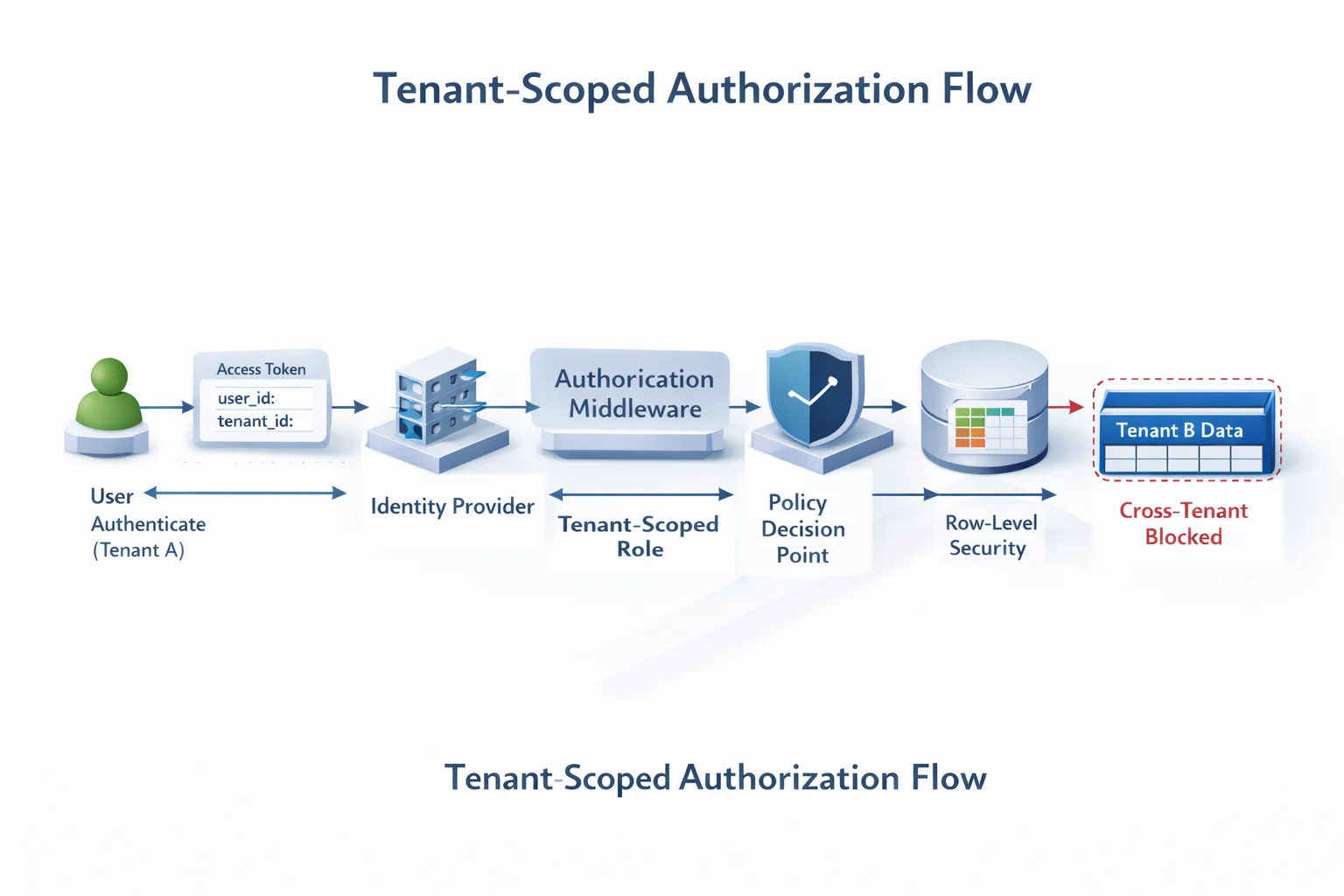
It starts with authentication. The identity provider verifies the user and issues a token. But here’s the catch if that token doesn’t include tenant context, everything that follows becomes unreliable. Authorization has nothing solid to enforce against.
That token isn’t just proof of identity. It’s the foundation of tenant isolation.
Once the request hits your system, authorization takes over and it has a job to do:
-
Confirm who the user is
-
Verify which tenant they belong to
-
Check their role within that tenant
-
Validate what resource they’re trying to access
-
Ensure the action is actually allowed
Miss any one of these, and your isolation starts to crack.
In a well-designed system, the flow is straightforward and strict:
-
The user authenticates via an identity provider
-
A token is issued with user ID and tenant ID
-
Every request carries that token
-
Middleware validates tenant scope before anything else
-
Policies evaluate roles and attributes within that tenant
-
The database enforces tenant-level filtering
What doesn’t happen is just as important.
The frontend doesn’t decide the tenant.
The API doesn’t “guess” it.
The database doesn’t rely on someone remembering a filter.
Tenant identity comes from a trusted source (authentication), and every layer enforces it consistently.
That separation is what keeps things secure at scale.
Authentication proves where a user belongs.
Authorization ensures they never step outside it.
Compliance, GEO, and Data Residency: Isolation Is Not Optional Anymore
Multi-tenant authorization is not just a technical concern. It is a regulatory one. In regulated industries, tenant isolation is directly tied to compliance. If your multi-tenant SaaS architecture cannot guarantee the strict separation of customer data, you are not just risking a bug. You are risking legal exposure.
Take GDPR. If EU customer data is stored in a shared multi-tenant data architecture, logical isolation must be airtight. Unauthorized cross-tenant access is considered a data breach, even if it was accidental.
HIPAA raises the stakes further. In healthcare SaaS platforms, tenant boundaries protect sensitive medical records. A misconfigured multi-tenant access control layer could expose protected health information across organizations.
SOC 2 audits focus on tenant isolation controls. Auditors want evidence that your multi-tenant authorization model enforces least privilege, tenant-scoped permissions, and auditable access decisions. “We filter by tenant_id in queries” is not considered a mature control strategy. Data residency requirements add another layer of complexity.
Many regions, including Canada and parts of the EU, require data to remain within specific geographic boundaries. In a multi-tenancy architecture, this may mean region-specific tenant segregation or separate deployments per geography. Now isolation is not just about tenant boundaries. It is about tenant boundaries within regional boundaries.
That requires:
-
Tenant-aware deployment strategies
-
Region-scoped data storage
-
Policy enforcement aligned with jurisdiction
-
Audit logs that reflect tenant and regional context
Multi-tenant authentication and authorization must adapt accordingly. Tokens may need to include region metadata. Authorization policies may enforce region-specific constraints. Data access decisions may consider geographic rules in addition to tenant identity.
This is where centralized authorization management becomes critical. Without a structured, policy-driven system, maintaining consistent isolation across tenants and regions becomes operational chaos.
Enterprise CIAM platforms such as LoginRadius support tenant-aware identity management, scoped access controls, and region-aligned deployment models. This reduces the burden of stitching together compliance controls manually across services.
In modern SaaS, tenant isolation is no longer just good engineering. It is contractual. And in a world where regulators assume breach by default, multi-tenant authorization must prove continuously that boundaries are enforced.
Centralized Authorization Management: Because Scattered Logic Always Fails
Authorization checks start simple. A few if statements in controllers. Some role checks in middleware. A tenant filter was added in repository code. It works. Until it doesn’t.
As your multi-tenant SaaS architecture grows, services multiply. Microservices are introduced. APIs expand. New roles are added. Suddenly, multi-tenant authorization logic is scattered across the system. And scattered logic is inconsistent logic.
One endpoint validates the tenant ID from the token. Another trusts a request parameter. A background job forgets to scope data access entirely. A reporting service bypasses the main middleware. Isolation begins to drift. Centralized authorization management exists to prevent this entropy.
Instead of embedding permission checks everywhere, a centralized authorization layer evaluates identity, tenant context, role, and policy before granting access. The enforcement logic becomes consistent, predictable, and auditable.
In a robust multi-tenant access control model, decision-making is separated from enforcement.
The policy engine answers: Does this user, within this tenant, have permission to perform this action on this resource?
The enforcement layer ensures that the decision is applied uniformly across APIs, services, and data layers.
This approach strengthens multi-tenant data architecture because it removes reliance on developer memory. Policies become declarative rather than scattered conditionals.
It also enables fine-grained authorization. Instead of broad tenant-level permissions, policies can evaluate attributes such as:
-
Tenant membership
-
Role hierarchy
-
Resource ownership
-
Environment or region
-
Time-bound access
For complex B2B platforms, this level of control is not a luxury. It is necessary. Modern CIAM platforms like LoginRadius support centralized, tenant-aware authorization models that align identity claims with policy enforcement.
By embedding tenant context in tokens and enabling scoped roles and policy evaluation, they reduce the risk of inconsistent authorization across distributed systems.
In multi-tenant systems, isolation fails gradually when logic drifts. Centralization prevents drift. Because in multi tenancy, consistency is security.
Conclusion
Multi-tenant authorization is not something you “add” once the product gains traction. It is something you decide at the architectural level long before scale exposes weaknesses.
In a multi-tenant SaaS architecture, infrastructure is shared by design. That is the economic advantage of SaaS. But shared infrastructure demands disciplined isolation. Without it, the very efficiency that makes multi tenancy attractive becomes its biggest liability.
Authentication alone is not enough. Roles alone are not enough. Even a well-designed multi-tenant data architecture is not enough if authorization enforcement is inconsistent. True tenant isolation requires alignment across layers.
Tenant-aware authentication that embeds trusted claims. Multi-tenant authorization that evaluates identity within tenant boundaries.Tenant-scoped roles and fine-grained policies. Database-level enforcement and query discipline. Centralized decision logic to prevent drift.
When these layers work together, multi-tenant access control becomes predictable. Deterministic. Auditable. When they don’t, isolation becomes a suggestion.
And in B2B SaaS, tenant isolation is not just a technical safeguard. It is a trust contract. Customers assume their data is invisible to competitors. Regulators assume boundaries are enforced. Auditors assume policies are consistent.
If your system cannot clearly demonstrate that Tenant A can never access Tenant B’s data even by accident, then your multi tenancy architecture is incomplete.
Isolation is not optional. It is foundational. Design it deliberately. Enforce it consistently. Audit it continuously. Because in multi-tenant systems, the most dangerous leaks are the quiet ones.
Ready to Strengthen Your Multi-Tenant Authorization?
If you're building or scaling a multi-tenant SaaS architecture and want tenant isolation enforced, not assumed, it's time to evaluate your authorization model.
Explore how LoginRadius enables tenant-aware authentication, scoped roles, centralized policy enforcement, and secure multi-tenant access control designed for modern B2B platforms.
Don’t wait for an audit or a leak to expose the gaps. Build tenant isolation that scales.
FAQs
Q: What is multi-tenant authorization?
A: Multi-tenant authorization is an access control model that restricts users to resources within their assigned tenant in a shared system. It prevents cross-tenant data access in multi-tenant SaaS architecture.
Q: How is multi-tenant access control different from standard RBAC?
A: Standard RBAC assigns permissions based on roles. Multi-tenant access control adds tenant boundaries, ensuring roles are scoped within a specific organization rather than applied globally.
Q: What is the safest multi-tenant architecture?
A: The safest multi-tenancy architecture combines tenant-scoped roles, centralized authorization, and database-level enforcement such as row-level security. Physical separation (separate databases) adds stronger isolation but increases cost.
Q: How do multi-tenant authentication and authorization work together?
A: Authentication verifies user identity and embeds tenant context in a token. Authorization then evaluates permissions within that tenant boundary before granting access to resources.
Q: Can a shared database be secure in a multi-tenant SaaS architecture?
A: Yes, a shared database can be secure if strict tenant filtering, row-level security, and centralized multi-tenant authorization are consistently enforced across all services and APIs.



