Introduction
Enterprise SSO solved the problem everyone was tired of fighting: passwords, login sprawl, endless credential resets. Centralized authentication felt like a breakthrough and for good reason. One identity. One login. Access everywhere. And then something subtle happened.
Access got too easy.
Teams rolled out SAML and OIDC, wired up half a dozen apps, synced directories, and called it secure. But what they really built was a wide-open hallway with unclear doors. Everyone could get in. No one was quite sure who should go where.
This is where RBAC in security stops being a theoretical model and starts becoming painfully real.
Enterprise SSO doesn’t determine what users can do. The Federation doesn’t decide how much access someone should have. They only answer who the user is. Everything else, every permission, every boundary, every risky overreach comes down to how well role-based access control is designed and enforced.
And here’s the part teams don’t like admitting: most RBAC implementations inside SSO environments were never designed. They emerged.
Directory groups quietly became authorization logic. Roles grew organically, without owners. SAML attributes got overloaded. OIDC tokens started carrying half the org chart.
From the outside, everything still looked “secure.” From the inside, access control slowly drifted out of control.
This is why role-based access control best practices matter far more in federated systems than they ever did in single-app setups. SSO increases blast radius. Federation amplifies mistakes. And without disciplined RBAC, every new integration quietly widens the risk surface.
In this blog, we’re not going to repeat the RBAC definitions you’ve already seen a hundred times. Instead, we’ll look at how RBAC actually behaves inside enterprise SSO and federation across SAML, OIDC, and SCIM where it works, where it quietly breaks, and how teams implement role-based access control without creating chaos they’ll regret a year later.
What Is RBAC in Security?
When people ask what is RBAC in security, they’re usually expecting a clean definition: users get roles, roles get permissions, and permissions control access. Simple. Logical. Orderly.
That definition isn’t wrong but it’s incomplete.
In real systems, RBAC isn’t just a model. It’s a constraint mechanism. It exists to stop access decisions from becoming subjective, inconsistent, or quietly dangerous. Instead of asking every application to decide who should be allowed to do what, RBAC creates a shared language for access: roles represent intent, permissions represent capability, and assignments tie the two together.
This is why RBAC in cybersecurity remains widely used even as systems grow more distributed. It gives organizations a way to scale access without scaling chaos.
But here’s the part most glossed over: RBAC only works when roles mean something. If roles are vague, overloaded, or constantly changing, the model collapses under its own weight. Security teams feel it first through overprivileged users, messy audits, and unclear ownership but developers feel it too, when access logic starts leaking into application code.
At its best, RBAC answers one critical question consistently: Given who this user is, what are they allowed to do right now? At its worst, it becomes a bucket where every exception goes to die.
Why RBAC Shows Up in Enterprise SSO + Federation
Enterprise SSO and federation didn’t make RBAC popular. They made it unavoidable.
SSO solves authentication. Federation extends that authentication across systems. Neither of them decides what users are allowed to do once they’re inside an application. That gap has to be filled somehow, and RBAC is the most common way teams do it.
In federated environments, a single identity often unlocks access to dozens of applications, APIs, and services. That concentration of trust is powerful, but it’s also risky. Without RBAC, every downstream system ends up reinventing authorization logic, often inconsistently and without shared governance.
This is why implementing role-based access control becomes a foundational requirement in enterprise SSO setups. Roles act as the contract between the identity provider and the service provider. They translate organizational intent into enforceable access decisions.
The challenge is that federation encourages shortcuts.
Directory groups quietly become roles. Application permissions get bundled together “for convenience.” Temporary access becomes permanent because no one owns cleanup.
From the outside, access still appears controlled. From the inside, it’s drifting.
RBAC shows up in enterprise SSO not because it’s fashionable, but because without it, federation turns into a trust amplifier with no brakes.
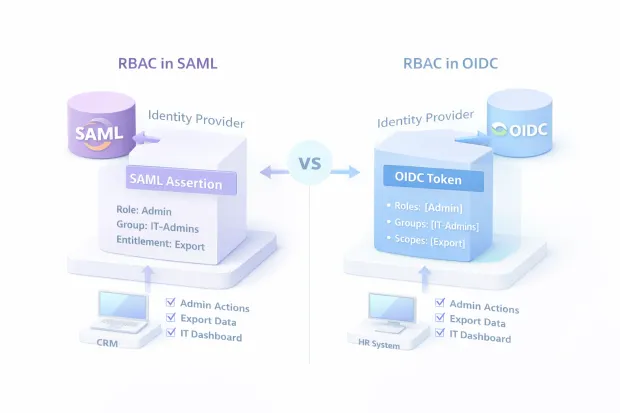
RBAC + SAML: Where Roles Hide Inside Assertions
SAML doesn’t talk about RBAC directly. It doesn’t need to. SAML’s job is to assert identity. Authorization sneaks in through attributes.
In most SAML-based systems, RBAC shows up as attributes inside the assertion often labeled as roles, groups, or entitlements. The identity provider authenticates the user, packages these attributes into the assertion, and the service provider decides what access to grant based on their values.
On paper, this looks clean. In practice, this is where RBAC design choices quietly solidify into long-term behavior.
If roles are mapped directly from directory groups, every directory decision becomes an authorization decision. If attributes are poorly named or inconsistently formatted, every consuming application interprets them differently. Over time, assertions start carrying more than they should, because removing attributes feels risky once systems depend on them.
Here’s where teams usually go wrong: they treat SAML attributes as passive metadata, not as authorization inputs. But the moment an application makes an access decision based on an assertion, that attribute becomes part of your security model, whether it was designed that way or not.
Well-designed RBAC in SAML environments is boring by design. Few attributes. Clear ownership. Explicit mappings. Anything else tends to age badly.
RBAC + OIDC: Roles Inside Tokens, Mistakes Inside Claims
OIDC feels more modern than SAML, and in many ways it is. Tokens are lighter. APIs are friendlier. But RBAC mistakes don’t disappear; they just move into claims.
In OIDC-based systems, roles often appear as custom claims inside ID tokens or access tokens. APIs and applications inspect those claims to decide what actions are allowed. This works well when done intentionally. It fails quietly when it isn’t.
One common issue is scope confusion. Scopes are often treated as roles, even though they were never meant to represent business permissions. Another is claim overload tokens stuffed with group lists, role hierarchies, and organizational metadata that changes more often than the token lifecycle allows.
And then there’s staleness. If a user’s role changes but their token remains valid, authorization decisions lag behind reality. In low-risk apps, that’s annoying. In high-privilege systems, it’s dangerous.
Strong role-based access control best practices in OIDC environments treat tokens as decision inputs, not sources of truth. Roles should be concise, purpose-driven, and mapped intentionally. Claims should express what the application needs to know, not everything the identity system happens to know.
OIDC doesn’t break RBAC. It just exposes how disciplined or undisciplined your authorization design really is.
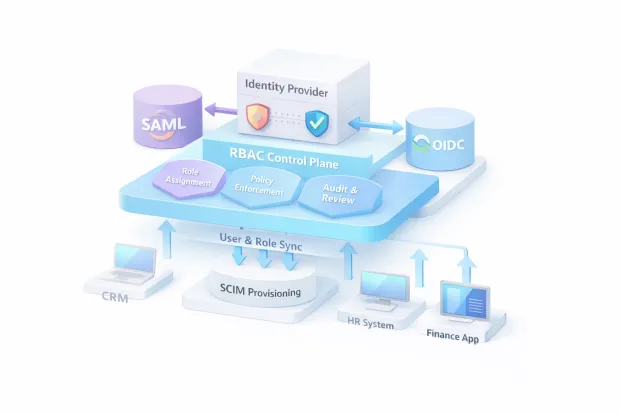
SCIM: The Unglamorous Piece That Prevents RBAC Drift
SCIM is rarely the hero of identity conversations. It doesn’t get the attention SSO gets. It doesn’t feel strategic. And yet, it’s the piece that quietly determines whether your RBAC model stays accurate or slowly falls apart.
Here’s the uncomfortable truth: RBAC doesn’t fail because roles are wrong. It fails because roles stop matching reality.
People join. People move. People leave. Teams restructure. Contractors rotate. Titles change. None of this is rare. What is rare is access being updated at the same speed as those changes unless SCIM is doing the heavy lifting.
Without SCIM, RBAC becomes manual maintenance. Someone has to remember to remove roles. Someone has to clean up old group memberships. Someone has to notice that a former admin is now a contractor with lingering access. In theory, that “someone” exists. In practice, drift sets in quietly.
This is why SCIM matters so much to role-based access control best practices. It ties authorization to the identity lifecycle, not memory or process docs. When implemented properly, SCIM ensures that:
-
New users receive the right roles automatically
-
Role changes propagate across applications without delay
-
Deprovisioning actually means access removal, not just account disablement
SCIM doesn’t make RBAC smarter. It makes RBAC honest. And in enterprise environments, honesty is what prevents privilege from accumulating where no one intended it to.
Example of Role-Based Access Control
Let’s step away from abstract models and look at something that resembles an actual organization.
Company: Mid-size B2B SaaS platform
Identity Stack: Enterprise SSO using SAML and OIDC, SCIM-enabled provisioning
Applications: Internal admin portal, customer support tools, billing system, APIs
Roles Defined
-
Support Agent Can view customer profiles, reset MFA, and access tickets. No billing access. No exports.
-
Account Manager Can view subscription details, generate quotes, and initiate upgrades. Cannot touch security settings.
-
Security Admin Manages authentication policies, reviews audit logs, and handles access reviews. No financial permissions.
-
Super Admin (Break-glass) Time-bound access for critical incidents. Fully audited. Rarely used.
How Federation Works
-
The identity provider authenticates users via SAML or OIDC.
-
Role assignments are included as attributes or claims.
-
Applications map those roles to permissions internally.
-
SCIM keeps role membership synced with HR and directory changes.
This example of role-based access control works because roles were designed with enforcement in mind, not convenience. Nothing here is exotic. What’s uncommon is the discipline to keep roles boring and predictable.
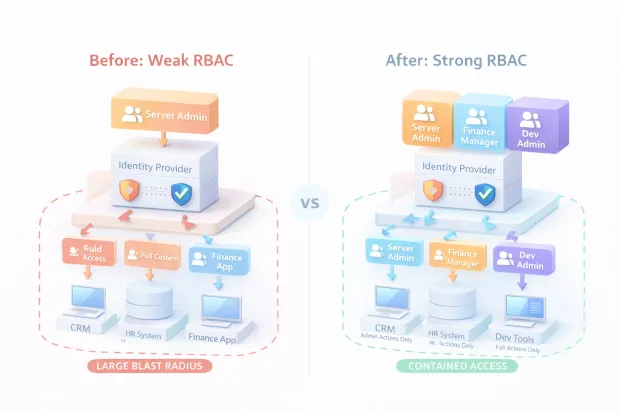
RBAC in Cyber Security: What Attackers Love About “Federated” Setups
Federation simplifies access for users. Attackers appreciate the same efficiency.
In federated environments, a single compromised identity often unlocks multiple systems. That concentration of trust is the appeal and the danger. When RBAC is loose, attackers don’t need to escalate privileges aggressively. They often start with more access than they should have had in the first place.
This is why RBAC in cybersecurity isn’t theoretical. It directly influences blast radius.
Attackers look for:
-
Broad roles assigned for convenience
-
Directory groups doubling as admin access
-
Tokens carrying stale or excessive claims
-
Lack of enforcement at the API layer
-
No meaningful separation between user and admin privileges
Federation doesn’t cause breaches. Poor authorization does. RBAC defines whether a compromised session becomes a contained incident or a lateral movement playground.
Strong RBAC reduces what attackers can do after they get in. And in real-world breaches, that “after” phase is where damage compounds.
SSO decides identity. RBAC decides impact.
And that’s why attackers pay close attention to federated access models, especially the ones that look clean on the surface.
Role-Based Access Control Best Practices for SSO + Federation
Most RBAC advice sounds reasonable until you try applying it inside a federated environment. SSO changes the rules. Federation magnifies mistakes. What worked in a single app starts leaking fast when access spans dozens of systems.
The first best practice is uncomfortable but necessary: stop treating roles as job titles. Job titles change more often than access intent. RBAC works when roles describe what someone is allowed to do, not where they sit on an org chart. “Finance Admin” means something enforceable. “Senior Analyst” does not.
The second is restraint. Fewer roles, clearer permissions. Federation punishes role explosion because every new role has to be mapped, synced, asserted, enforced, audited, and eventually retired. If a role exists only to satisfy one edge case, it’s already a maintenance liability.
Another rule teams underestimate: separate convenience from privilege. It’s tempting to bundle permissions so users don’t “hit friction.” In federated systems, that friction often exists for a reason. Admin actions, data exports, policy changes these should live in isolated roles, not ride along with everyday access.
Lifecycle automation matters more than elegance. SCIM-backed provisioning ensures RBAC reflects reality, not best intentions. Joiners get access without delay. Movers don’t accumulate permissions quietly. Leavers lose access everywhere, not just where someone remembered to check.
Finally, governance can’t be optional. Access reviews aren’t bureaucracy; they’re drift detection. Logging access decisions, not just logins, gives teams visibility into how RBAC behaves under pressure. The goal isn’t perfection. It’s catching problems before they turn into incidents.
These role-based access control best practices don’t make systems flashy. They make them survivable.
How to Implement Role-Based Access Control in a Federated Environment
Implementing RBAC in federated systems fails when teams start with protocols instead of decisions. SAML, OIDC, and SCIM are tools. They don’t design access for you.
Start with permissions. Not roles. List the actual actions that matter: read data, modify records, approve changes, manage policies, export sensitive information. If permissions aren’t clear, roles will be arbitrary.
Once permissions exist, group them into roles that represent intent. Each role should answer a simple question: “What kind of access is this role meant to grant?” If that answer takes a paragraph, the role is doing too much.
Next, choose a single source of truth for role assignment. HR systems, directories, or identity platforms can all work, but ambiguity cannot. One system assigns roles. Everything else consumes them.
Then comes federation mapping. Roles become attributes in SAML assertions or claims in OIDC tokens. This mapping should be explicit, documented, and consistent across applications. Avoid leaking raw directory groups downstream unless they were designed for authorization from day one.
SCIM follows naturally. It synchronizes role membership and ensures changes propagate automatically. Without SCIM, RBAC becomes a promise that relies on human memory. That never ends well.
Finally, enforce roles at the application and API layers. Federation communicates intent. Enforcement makes it real. Authorization checks must happen where actions occur, not just at login.
This is how teams implement role-based access control without overengineering: design first, map carefully, automate lifecycle, and enforce consistently.
Common Failure Patterns
Most RBAC failures don’t happen on day one. They emerge quietly, months after launch, when no one is watching closely anymore.
One of the most common patterns is role explosion. Every exception becomes a new role. Over time, no one knows which roles are safe to remove. Teams stop touching them altogether, and stale access becomes permanent.
Another is directory group abuse. Groups created for email lists or org charts get reused for authorization because they’re convenient. Suddenly, HR changes become security changes without anyone realizing it.
Token and assertion overload is another red flag. When roles, groups, and metadata pile into SAML assertions or OIDC tokens, performance suffers and authorization logic becomes brittle. Worse, access decisions start relying on data that changes more often than tokens expire.
Then there’s lifecycle neglect. Users move teams. Contractors leave. Temporary access becomes forever because no one owns cleanup. Without SCIM or regular reviews, RBAC slowly detaches from reality.
Perhaps the most dangerous pattern is the illusion of security. “We have SSO, so we’re fine.” Federation creates confidence. RBAC determines whether that confidence is earned.
These failures aren’t caused by bad technology. They’re caused by treating authorization as a configuration task instead of a system design problem.
Conclusion
Enterprise SSO and federation changed how organizations authenticate. They did not magically solve authorization, and they never claimed to. That responsibility sits squarely with RBAC.
When role-based access control is designed intentionally, federation becomes powerful. Identities flow cleanly. Access is predictable. Permissions align with business intent. SCIM keeps lifecycle changes honest. Reviews are possible. Audits make sense.
When RBAC is treated as an afterthought, federation quietly turns dangerous.
Groups become permissions. Permissions become assumptions. Assumptions turn into overreach.
And because everything is centralized, the impact spreads faster than teams expect.
This is why RBAC in cybersecurity isn’t about ticking compliance boxes. It’s about controlling how trust propagates across systems. SSO shortens the distance between identity and access. RBAC decides whether that distance is safe.
The teams that get this right don’t necessarily build complex systems. They build clear ones.
They start from permissions, not titles. They limit roles instead of multiplying them. They use SCIM to keep access aligned with reality. They separate convenience from privilege. They review access before incidents force them to.
Most importantly, they accept a simple truth: Authentication gets you in the door, Authorization decides what happens next.
If your enterprise SSO feels mature but your access model feels fragile, the fix is rarely another protocol or another integration. It’s revisiting how roles are defined, mapped, enforced, and governed across your federated ecosystem.
RBAC isn’t exciting. But it’s the reason the federation either scales cleanly or collapses quietly.
And that choice shows up faster than most teams expect.
FAQs
Q: What is RBAC in security?
A: RBAC (Role-Based Access Control) is a security model where permissions are grouped into roles and users are assigned those roles. It ensures access is predictable, auditable, and aligned with least-privilege principles.
Q: Why is RBAC important in enterprise SSO and federation?
A: SSO and federation authenticate users across systems, but RBAC controls what they can actually do after login. Without RBAC, federated access can easily become over-permissive.
Q: How does RBAC work with SAML and OIDC?
A: In SAML and OIDC, RBAC is enforced through attributes or claims that represent roles. Applications use these values to map users to permissions and enforce access decisions.
Q: What are common RBAC mistakes in federated environments?
A: Overloading directory groups as roles, allowing role sprawl, and missing SCIM-based deprovisioning are common issues. These lead to access drift and increased security risk over time.


