Introduction
Identity systems didn’t fail overnight—they aged quietly. Early IAM models were built for predictable users, fixed devices, and clear perimeters, where a single trust decision at login was usually enough.
That world no longer exists. Users move fluidly across devices and sessions, applications span APIs and third parties, and attackers don’t force entry—they log in with stolen credentials and blend in. Yet most identity systems still stop thinking once authentication succeeds.
This guide explains why static identity models break at scale and what replaces them. You’ll learn how Agentic IAM shifts identity from a one-time checkpoint to a continuous decision layer, how trust is evaluated in real time, and how modern CIAM platforms like LoginRadius are evolving to support autonomous, context-aware identity without adding friction.
Why Traditional IAM Was Never Built for This World
The Original Purpose of IAM
Traditional identity and access management (IAM) was created to manage employee access, not unpredictable external users. Its core responsibility was to ensure that the right employee had the right access to the right internal system. This worked well in controlled environments where roles changed slowly, devices were managed, and usage patterns were relatively stable.
The problem is that these same principles were stretched far beyond their original intent when organizations began applying them to customers, partners, and consumers. Static roles, one-time authentication, and long-lived sessions simply do not map well to environments where millions of users behave differently every second.
What Breaks When IAM Meets Scale and Uncertainty
As scale increases, the limitations of static identity models become painfully obvious. A system that only evaluates trust once cannot distinguish between a legitimate customer and a hijacked session later in the day.
Security teams respond by adding more rules, more policies, and more authentication challenges, which increases complexity without actually improving decision quality. Over time, identity systems become brittle, rule-heavy, and difficult to reason about, while attackers continue to adapt faster than the policies meant to stop them.
How CIAM Improved Identity but Still Fell Short
What CIAM Fixed
Customer Identity and Access Management platforms significantly improved the situation by focusing on scalability, usability, and customer experience. CIAM introduced features like social login, adaptive authentication, and centralized identity profiles, making it possible to support millions of users without collapsing under operational complexity. Compared to traditional IAM, this was a major step forward.
Where CIAM Still Struggles
Despite these improvements, most CIAM systems still rely on event-based decisions. Authentication happens, risk is assessed at that moment, and then the session proceeds largely unchecked.
Adaptive authentication helps at login, but once trust is granted, it remains mostly static. This means CIAM can reduce friction during onboarding but still lacks the ability to continuously evaluate whether ongoing behavior makes sense. In other words, CIAM made identity more user-friendly, but not truly intelligent.
What Is Agentic IAM?
Agentic Identity and Access Management (Agentic IAM) is an identity model where trust is evaluated continuously and autonomously, rather than being granted once at login. It uses identity agents to observe behavior, context, and lifecycle signals in real time and dynamically adjust authentication strength, access privileges, or session trust as conditions change.
Unlike traditional IAM or CIAM systems that rely on static, event-based decisions, Agentic IAM treats identity as an ongoing decision process. Authentication is only the starting point. Trust evolves throughout a session based on how an identity—human, service, or AI agent—behaves over time.
Agentic IAM is designed for modern environments where users move across devices, sessions are long-lived, APIs and third-party integrations are common, and attackers or autonomous agents can authenticate successfully using valid credentials.
By continuously reassessing trust instead of assuming it, Agentic IAM reduces fraud, limits account takeover, and enforces proportional access without adding unnecessary friction.
In practice, Agentic IAM extends modern CIAM through identity orchestration, governance, and lifecycle-aware controls, enabling organizations to manage both human users and autonomous AI agents within a single, adaptive trust framework.
Platforms like LoginRadius support this model by providing the infrastructure for continuous identity decisions at scale.
Why the Term “Agentic” Actually Matters
The word “agentic” implies agency, not automation theater. An agent observes its environment, interprets signals, makes decisions, and takes action without needing constant human instruction.
In the context of IAM, this means identity agents can independently decide when to allow frictionless access, when to introduce additional verification, and when to restrict or terminate a session entirely. The system behaves less like a static policy engine and more like a living decision layer.
How Agentic IAM Thinks About Trust
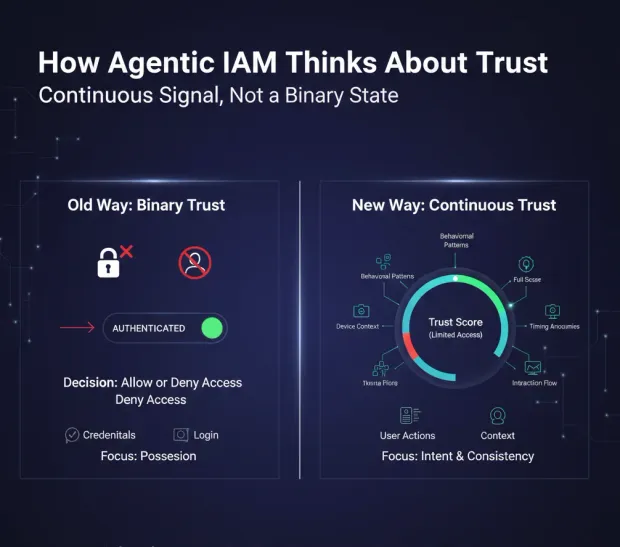
Trust as a Continuous Signal, Not a Binary State
When we talk about AI in identity and access management, trust is not something you either have or do not have. It is a continuously updated signal that reflects how closely current behavior aligns with expected behavior. A user may be trusted enough to browse content but not trusted enough to change account settings, all within the same session. This allows security to become more precise instead of universally restrictive.
Why Behavior Matters More Than Credentials
Credentials prove possession, not intent. Once credentials are compromised, they provide attackers with the same access as legitimate users. Agentic IAM shifts the focus away from credentials and toward behavioral consistency. Subtle deviations in timing, navigation, or interaction patterns often reveal risk long before a traditional system would detect anything suspicious.
Why Agentic IAM Reduces Friction Instead of Increasing It
One of the most counterintuitive aspects of Agentic IAM is that it often leads to fewer visible security challenges. Because the system continuously evaluates trust, it does not need to interrupt every user “just in case.”
Most users experience smoother journeys because the system can silently confirm that nothing looks unusual. When friction does appear, it is targeted, contextual, and justified, rather than arbitrary and repetitive.
This is a fundamental shift away from the common belief that better security always means more prompts and more steps. In reality, better decisions reduce the need for unnecessary friction.
Why Agentic IAM Is Emerging Now
Agentic IAM did not become possible overnight. It emerged because identity infrastructure finally caught up with the complexity of modern digital ecosystems. API-first architectures, real-time event processing, identity orchestration, and advanced risk signals have made continuous decision-making feasible at scale.
At the same time, fraud has become behavioral rather than brute-force, and user experience has become a measurable business outcome rather than a nice-to-have.
Agentic IAM sits at the intersection of these trends, extending modern CIAM architectures into something more adaptive, resilient, and intelligent.
How Agentic IAM Changes the Role of Identity in Architecture
Identity is no longer just an access control layer that lives at the edge of an application. In an Agentic IAM model, identity becomes an intelligence layer that continuously informs security, experience, and business decisions. It influences what users can do, when they can do it, and how much friction they should encounter, all without relying on rigid assumptions or static rules.
This shift is uncomfortable for organizations used to deterministic policies, but it is also unavoidable. Static trust does not survive in dynamic systems.
Agentic IAM Architecture and How Identity Decisions Actually Happen
Once organizations get past the definition of Agentic IAM, the next question is usually a skeptical one: how does this actually work without turning identity into a black box? That skepticism is healthy.
Identity systems already sit in the critical path of user experience and security, and no one wants to replace a predictable but limited system with something opaque and uncontrollable.
The architecture of Agentic IAM exists precisely to avoid that problem. It is not a single magical engine making mysterious decisions. Instead, it is a layered decision system where signals, context, and policy intelligence interact continuously. The key difference from traditional IAM is not complexity for its own sake, but where decisions happen and how often they are revisited.
From Login-Centric Identity to Decision-Centric Identity
Why Login Is the Wrong Anchor Point
Most IAM and CIAM systems are architected around login because that was historically the only moment when identity systems had enough information to make a decision. Credentials were presented, maybe a second factor was verified, and the system made a call. Everything after that was treated as application logic, not identity logic.
Agentic IAM breaks away from this model by decoupling identity decisions from the login event. Authentication still matters, but it becomes just one input into an ongoing decision process rather than the moment where all trust is decided.
Architecturally, this means identity is no longer something that runs once at the edge of an application. It becomes a service that participates throughout the user journey.
Identity as a Continuous Control Plane
In an Agentic IAM architecture, identity functions as a control plane rather than a gate. It continuously receives signals from applications, devices, and sessions, evaluates those signals in context, and influences what happens next.
Sometimes that influence is invisible. Other times it introduces friction, limits capabilities, or shuts things down entirely. The important point is that identity stays present long after login succeeds.
The Core Layers of an Agentic IAM Architecture
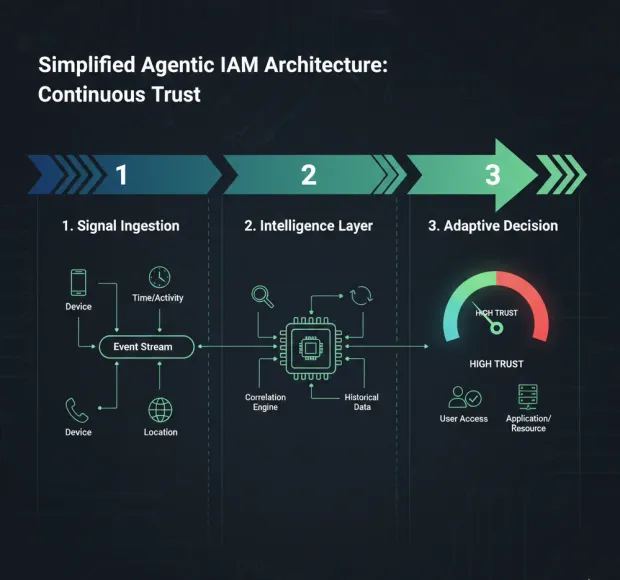
Signal Ingestion as the Foundation
Every Agentic IAM system begins with signals. These signals are not exotic or futuristic; most of them already exist in modern applications. They include authentication context, device characteristics, location changes, session duration, navigation patterns, API usage, and historical behavior associated with an identity.
What changes in an agentic model is how these signals are treated. Instead of being logged for later analysis or used only at login, they are streamed continuously into the identity system. Architecturally, this requires event-driven pipelines rather than request-response checks. Identity becomes reactive to what users are doing, not just what they did at the beginning.
Contextualization and Correlation
Raw signals are not useful on their own. A new device might be perfectly normal, or it might indicate account takeover. An unusual location might be expected for a frequent traveler, or it might signal fraud. Agentic IAM systems introduce a contextualization layer that correlates signals with historical patterns, session state, and environmental factors.
This layer is where identity begins to look less like access control and more like intelligence. Decisions are not made on individual events but on how those events fit into a broader picture of user behavior. Architecturally, this is what allows the system to reduce false positives while still reacting quickly to real risk.
Identity Agents and Decision Engines
What an Identity Agent Actually Is
An identity agent is not a chatbot and not a single AI model making absolute judgments. It is a decision-making component responsible for evaluating trust within a specific scope. One agent may focus on session integrity, another on transaction risk, and another on privilege escalation. Each agent observes relevant signals, applies reasoning, and produces a confidence or risk assessment.
The power of this approach lies in specialization. Instead of one monolithic policy engine trying to understand everything, multiple agents make narrower decisions that are easier to tune, explain, and evolve. This also makes the system more resilient, because no single decision point determines everything.
How Decision Engines Interpret Agent Output
Decision engines sit above identity agents and translate assessments into outcomes. They do not ask whether a user is “good” or “bad.” They ask what should happen next given the current trust state. Should the session continue uninterrupted? Should additional verification be introduced? Should certain actions be temporarily restricted?
This is where Agentic IAM differs sharply from rule-based systems. Traditional policies are brittle because they try to anticipate every scenario in advance. Decision engines, by contrast, work with probabilities and confidence levels, allowing responses to scale with risk rather than flipping abruptly from allow to deny.
Real-Time Decision Flow in Practice
How Decisions Evolve During a Session
In an Agentic IAM system, trust is reassessed continuously as a session unfolds. Early in a session, the system may rely heavily on authentication signals. As time passes, behavioral consistency becomes more important. If behavior aligns with expectations, trust may increase and friction disappears entirely. If behavior begins to drift, the system can respond gradually rather than panicking at the first anomaly.
This gradualism is critical. It allows identity systems to intervene precisely where needed instead of disrupting every user for the sake of caution. Architecturally, it requires low-latency decision paths and tight integration between identity services and application workflows.
Actions as First-Class Outputs
One of the most important architectural shifts in Agentic IAM is that actions are treated as first-class outputs, not side effects. The system does not simply raise alerts and hope someone responds. It actively influences the session by introducing verification steps, adjusting permissions, or terminating access when necessary.
Because these actions are driven by real-time decisions, they can be both faster and less intrusive than traditional security responses. Users who pose no risk rarely notice the system at all, while risky behavior is addressed immediately rather than after damage has already occurred.
How Agentic IAM Fits into Modern CIAM Platforms
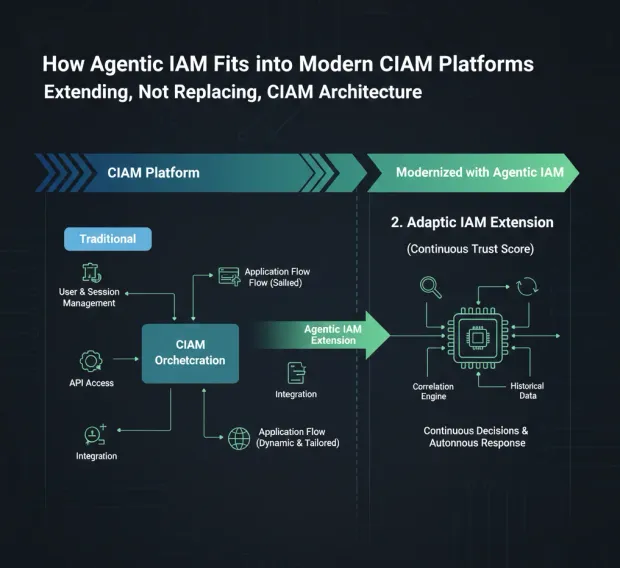
Extending, Not Replacing, CIAM Architecture
Agentic IAM does not require organizations to throw away their CIAM platforms. In practice, it extends them. Modern CIAM already provides identity orchestration, API-first access, session management, and integration with external systems. Agentic IAM builds on these capabilities by adding continuous decision-making and autonomous response.
This is an important distinction because it means Agentic IAM is evolutionary, not revolutionary. Organizations that have already invested in CIAM are closer to this model than they may realize. The architectural shift is about how identity data is used, not about ripping out existing infrastructure.
Why Orchestration Becomes Non-Negotiable
Identity orchestration is what allows Agentic IAM decisions to influence user journeys dynamically. Without orchestration, identity systems can detect risk but struggle to act on it gracefully. With orchestration, decisions can be translated into tailored flows that balance agentic AI security and experience in real time.
Architecturally, orchestration acts as the connective tissue between identity intelligence and application behavior. It ensures that decisions are not just accurate, but also usable.
The Trade-Offs Organizations Need to Understand
Determinism vs Adaptability
One of the biggest mental shifts with Agentic IAM is moving away from deterministic outcomes. Traditional IAM systems are predictable because they are rigid. Agentic systems are adaptive, which means outcomes can change based on context. This can be uncomfortable for teams used to absolute guarantees.
The trade-off is worth it. Adaptability allows identity systems to keep pace with attackers and user behavior instead of falling behind both. The architecture is designed to make this adaptability controlled, observable, and auditable rather than chaotic.
Transparency and Explainability
A common concern is whether Agentic IAM decisions can be explained. Architecturally, this is addressed by keeping agents specialized and decision logic explicit. Instead of a single opaque decision, the system can show which signals contributed to a change in trust and which agent triggered an action.
This transparency is essential for security teams, compliance, and long-term trust in the system.
Where Architecture Meets Reality
Agentic IAM architecture is not theoretical. It reflects how modern systems already operate in areas like fraud detection, recommendation engines, and real-time personalization. Identity is simply catching up to patterns that other domains adopted years ago.
By designing identity as a continuous, agent-driven decision system, organizations gain something traditional IAM never offered: the ability to respond proportionally, intelligently, and immediately to what is actually happening, not just what happened at login.
How Agentic IAM Works in Real Life — Continuous Trust, Fraud, and Zero Trust Without the Pain
Why Real-World Flows Matter More Than Architecture Diagrams
Architecture diagrams are comforting because they look orderly. Real users, unfortunately, are not. They click around unpredictably, switch devices mid-session, travel across time zones, and occasionally do things that look suspicious without actually being malicious. This is exactly why Agentic IAM cannot be understood purely as a system design exercise. Its real value shows up in how it behaves during live user interactions, when conditions change and assumptions fail.
Traditional identity systems are brittle in these moments because they already made their decision at login. Agentic IAM keeps deciding. The difference is subtle in theory and dramatic in practice.
Continuous Authentication Without Turning Users Into Security Test Subjects
Why Continuous Authentication Is Not “Re-Authentication”
Continuous authentication has a bad reputation because it is often confused with repeatedly asking users to prove who they are. That is not what Agentic IAM does. Instead of interrupting users with constant challenges, it continuously evaluates trust in the background using behavioral and contextual signals that users generate naturally.
The important distinction is that authentication is no longer treated as a recurring event. It becomes an ongoing assessment. Users are not asked to re-authenticate unless something meaningfully changes, and even then, the system escalates proportionally rather than reflexively.
How Trust Evolves Over Time
In an Agentic IAM flow, trust typically increases as a session progresses smoothly. A user who logs in successfully, behaves consistently, and interacts with the application in expected ways becomes more trusted over time, not less. This is the opposite of systems that treat long sessions as inherently risky.
When behavior changes, trust does not collapse instantly. It degrades gradually. This allows the system to respond with nuance, such as limiting sensitive actions while allowing low-risk activity to continue uninterrupted. From the user’s perspective, the experience feels stable rather than paranoid.
Fraud and Account Takeover Prevention That Happens Before Damage Is Done
Why Traditional Fraud Detection Is Always Late
Most fraud systems operate after the fact. They detect anomalies, raise alerts, and hand the problem to analysts once something suspicious has already happened. Identity systems often inherit this limitation because they are not designed to intervene mid-session.
Agentic IAM changes this by making identity decisions part of the fraud response itself. Instead of flagging suspicious behavior and hoping someone reacts quickly, the system can act immediately based on confidence shifts observed during the session.
How Agentic IAM Identifies Risk in Motion
Account takeover rarely looks dramatic at first. Attackers log in successfully, browse normally, and only gradually begin probing sensitive areas. Agentic IAM excels at catching this phase because it looks for behavioral drift rather than explicit violations. Subtle changes in navigation speed, action sequencing, or interaction timing can indicate automation or unfamiliarity with the account.
As these signals accumulate, trust decreases incrementally. The system may introduce a verification step before a sensitive action, restrict access to account recovery features, or shorten session lifetimes dynamically. These interventions often stop fraud without ever triggering a visible security incident.
Zero Trust That Does Not Punish Legitimate Users
Why Zero Trust Often Gets a Bad Reputation
Zero Trust is conceptually sound but frequently implemented poorly. Many organizations interpret it as “never trust anyone,” which leads to constant verification, endless prompts, and deeply unhappy users. The irony is that this approach often creates more security fatigue than security.
Agentic IAM provides a more practical interpretation of Zero Trust by enforcing continuous verification without continuous interruption. Trust is never assumed permanently, but it is also not revoked without evidence.
Continuous Verification Without Constant Friction
In an Agentic IAM system, Zero Trust is enforced through observation rather than interrogation. The system continuously verifies that the current behavior aligns with a trusted identity, but it does so quietly. Verification challenges are reserved for moments when confidence actually drops, not when policy says it might.
This approach aligns much more closely with how humans assess trust in the real world. We do not repeatedly ask people to prove who they are if nothing changes. We pay attention, notice deviations, and react when something feels off.
Sensitive Actions and Progressive Risk Escalation
Why Not All Actions Deserve Equal Trust
One of the biggest flaws in traditional IAM systems is that once access is granted, all actions are treated similarly. Browsing content and changing account recovery details often live behind the same trust boundary. Agentic IAM corrects this by evaluating trust at the action level.
Low-risk actions require minimal confidence. High-risk actions demand stronger signals. This allows applications to remain accessible while still protecting the most sensitive operations.
How Agentic IAM Adjusts in Real Time
When a user attempts a sensitive action, the system evaluates current trust rather than relying on the initial login decision. If trust is high, the action proceeds seamlessly. If trust has degraded, the system may request additional verification or temporarily restrict the action until confidence is restored.
This dynamic adjustment feels fair to users because it aligns agentic AI security checks with intent. Users are rarely surprised by a challenge when it appears at a genuinely sensitive moment.
Multi-Device, Multi-Session Reality
Why Static Sessions Break Down
Modern users rarely stay on one device or in one session. They move between mobile and desktop, pause and resume work, and interact with applications throughout the day. Static session models struggle with this reality because they cannot distinguish between legitimate transitions and suspicious ones.
Agentic IAM treats sessions as fluid rather than rigid. Trust can transfer between sessions when behavior remains consistent, and it can decay when context changes abruptly.
Maintaining Continuity Without Blind Trust
By correlating behavior across devices and sessions, Agentic IAM can maintain continuity without blindly extending trust. A user switching devices in a familiar pattern is not treated the same as an attacker suddenly appearing from a new environment. This distinction dramatically improves both agentic security and user experience.
Agentic AI Security- When Agentic IAM Decides to Say No
Why Denial Is Still Necessary
Agentic IAM is not designed to avoid denial at all costs. It is designed to delay denial until it is justified. When trust drops below acceptable thresholds, the system can terminate sessions, block actions, or require remediation steps.
The difference is that these decisions are based on accumulated evidence rather than single events. When denial happens, it is rarely a surprise, and it is usually correct.
Reducing False Positives Without Reducing Agentic Security
Because decisions are incremental, Agentic IAM dramatically reduces false positives. Users are not locked out because of one odd signal. Instead, the system looks for patterns that suggest genuine risk. This balance is what allows organizations to tighten security without increasing support tickets or user frustration.
How These Flows Change the Security Conversation
Agentic IAM shifts security discussions away from “how many factors should we require” and toward “how well do we understand what our users are doing.” This is a healthier conversation because it focuses on intelligence rather than enforcement.
Security becomes something that adapts with users instead of something imposed on them.
Agentic IAM as a Business Capability — and Where LoginRadius Fits In
Why Agentic IAM Is Not Just a Security Upgrade
By the time organizations reach this stage of the conversation, the question is no longer whether Agentic IAM makes sense technically. The more pressing question is whether it actually delivers business value, or whether it is simply a more elegant way to describe security controls that already exist. This skepticism is understandable. Identity has historically been positioned as a cost center, something that exists to prevent bad things rather than enable good ones.
Agentic IAM changes that frame entirely. When identity becomes a continuous decision layer instead of a static gate, it starts influencing outcomes that businesses actually care about. User experience improves because friction is applied only when it is justified.
Fraud losses decrease because interventions happen during risky behavior rather than after damage is done. Engineering teams move faster because identity logic becomes centralized and adaptive instead of scattered across applications.
At this point, Agentic IAM stops being an abstract model and starts behaving like a strategic capability.
How Agentic IAM Improves User Experience Without Compromising Control
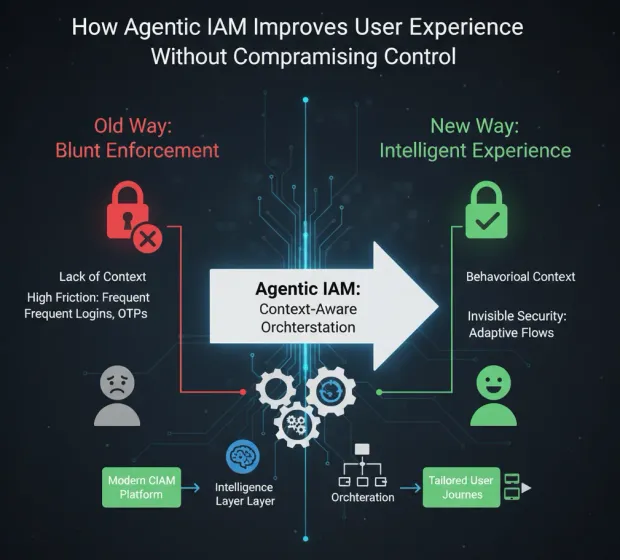
One of the most persistent myths in identity is that security and user experience exist in opposition. Agentic IAM demonstrates that the real conflict is not between security and experience, but between intelligence and blunt enforcement. When systems lack context, they compensate with friction. When systems understand behavior, they can afford to be subtle.
This is where modern CIAM platforms become critical. Agentic IAM depends on the ability to orchestrate identity journeys dynamically, adapting flows based on real-time decisions. LoginRadius has spent years building precisely this kind of orchestration-first CIAM foundation, where authentication, verification, and profile interactions are not hardcoded but configurable and responsive.
In practice, this means that most users experience faster, smoother journeys because nothing unusual is happening. When the system does intervene, it feels contextual rather than arbitrary. From the user’s perspective, security stops feeling like a tax and starts feeling invisible.
Fraud Reduction as a Side Effect of Better Identity Decisions
Traditional fraud prevention often lives outside the identity layer, operating as a separate system that reacts after suspicious activity has already occurred. Agentic IAM collapses that separation by embedding fraud-aware decision-making directly into identity flows.
LoginRadius approaches this problem by treating identity signals, risk indicators, and lifecycle context as part of a unified system rather than isolated features. Behavioral changes, unusual access patterns, and lifecycle anomalies can influence authentication strength, session continuity, and action-level permissions in real time.
The result is not just fewer successful attacks, but fewer unnecessary challenges for legitimate users. Fraud prevention becomes a continuous adjustment process rather than a binary response, which is exactly what Agentic IAM is designed to enable.
Identity Governance and Lifecycle as the Backbone of Agentic IAM
Agentic IAM cannot function without strong identity governance and lifecycle management. Continuous trust decisions only make sense if the system understands where an identity came from, what state it is in, and how it is allowed to evolve over time. This applies just as much to human users as it does to non-human identities such as applications, services, and AI agents.
LoginRadius places identity governance at the center of its Agentic IAM story. Identity is not treated as a static record but as a living entity with a lifecycle that includes onboarding, verification, privilege changes, consent management, and eventual deactivation. Each of these stages provides context that informs trust decisions later.
This governance-first approach is especially important as organizations begin managing AI agents alongside human users. Agentic IAM is not only about humans behaving unpredictably; it is also about machines acting autonomously within defined boundaries. LoginRadius’ focus on lifecycle-aware identity governance provides a practical foundation for managing this complexity without losing control.
Preparing for AI Agents Without Breaking Existing Identity Models
One of the clearest signals that Agentic IAM is becoming unavoidable is the rise of AI agents acting on behalf of users, systems, and businesses. These agents authenticate, access APIs, make decisions, and trigger workflows autonomously. Managing them with static credentials and long-lived tokens is an obvious risk, yet many organizations are heading in that direction out of necessity.
LoginRadius addresses this challenge by extending CIAM principles to AI agents rather than creating a separate identity universe. AI agents are treated as identities with defined lifecycles, permissions, and behavioral expectations. Their access can be governed, monitored, and adjusted dynamically based on context and activity.
This approach aligns naturally with Agentic IAM, where trust is never assumed permanently and actions are continuously evaluated. Instead of bolting security onto AI workflows after the fact, identity becomes the control layer that makes autonomous systems manageable at scale.
Scalability Without Identity Debt
As organizations grow, identity complexity tends to grow faster. New applications, new regions, new user types, and new compliance requirements all pile onto systems that were never designed to adapt continuously. The result is identity debt, where every change becomes harder and riskier than the last.
Agentic IAM reduces this debt by centralizing decision-making and distributing enforcement. LoginRadius’ API-first architecture allows identity intelligence to scale independently of applications, while orchestration ensures that decisions translate into consistent user experiences across channels.
This separation of concerns is critical for global scale. Identity teams can evolve policies, signals, and decision logic without forcing application teams to rewrite authentication flows every time the business changes direction.
Compliance as an Outcome, Not a Constraint
Compliance is often treated as something identity systems endure rather than enable. Static policies and rigid controls make audits easier, but they also make systems inflexible. Agentic IAM takes a different approach by making compliance an outcome of strong governance and observability.
Because LoginRadius tracks identity lifecycle events, consent changes, authentication decisions, and access patterns centrally, compliance reporting becomes a byproduct of normal operation rather than a special project. Continuous decision-making also makes it easier to demonstrate proportional access controls, which is increasingly important under modern privacy and security regulations.
This shift allows organizations to meet regulatory requirements without freezing identity systems in place.
Why LoginRadius Is Positioned for Agentic IAM Today
Agentic IAM is often framed as something futuristic, but the reality is that many of its core capabilities already exist within mature CIAM platforms. LoginRadius stands out because it has consistently treated identity as a dynamic system rather than a static service. Its focus on orchestration, governance, lifecycle management, and AI-readiness aligns naturally with agentic principles.
Rather than introducing Agentic IAM as a radical departure, LoginRadius presents it as the next logical evolution of CIAM. This framing matters because it allows organizations to move forward incrementally, building on existing investments instead of starting over.
From Capability to Competitive Advantage
When identity systems make better decisions, everything downstream improves. Users encounter less friction, security teams spend less time reacting to incidents, and businesses gain the confidence to move faster without increasing risk. Agentic IAM turns identity from a background utility into a competitive advantage, one that quietly shapes outcomes across experience, security, and growth.
LoginRadius’ approach demonstrates that this is not theoretical. It is the result of designing identity systems that think continuously, act proportionally, and evolve alongside the digital environments they protect.
How to Adopt Agentic IAM Without Breaking Everything You’ve Already Built
Why the Real Challenge Is Not Technology but Transition
By this point, Agentic IAM should feel less like a theoretical model and more like an uncomfortable truth: identity systems that make static decisions are no longer sufficient. The real hesitation organizations face is not whether Agentic IAM works, but how to move toward it without rewriting every application, retraining every team, or introducing new risk during the transition.
The good news is that Agentic IAM does not require a dramatic “rip and replace” moment. In practice, it emerges gradually as identity systems become more orchestration-driven, lifecycle-aware, and decision-centric. The transition is evolutionary, not revolutionary, which is precisely why platforms that already treat identity as a living system are best positioned to support it.
Build Versus Platform in an Agentic IAM World
Why Building Sounds Appealing at First
For organizations with strong engineering teams, the temptation to build Agentic IAM capabilities in-house is understandable. The logic seems straightforward: collect more signals, write smarter policies, and add decision logic where needed. In small, controlled environments, this approach can even work for a while.
The problem appears later, when systems grow, teams change, and assumptions age. What begins as a clean implementation quickly turns into a web of fragile logic scattered across services. Decision consistency erodes, explainability disappears, and identity debt accumulates quietly until it becomes impossible to ignore.
Why Platforms Win Over Time
Agentic IAM depends on continuous evaluation, orchestration, governance, and observability. These are not features that sit comfortably inside individual applications. They require a centralized identity layer that can see across sessions, devices, and journeys. This is where CIAM platforms designed for adaptability rather than static enforcement provide a structural advantage.
LoginRadius approaches this problem by treating identity as a shared decision system rather than a collection of isolated integrations. Its architecture allows organizations to introduce agentic behavior incrementally, starting with orchestration and lifecycle awareness, then expanding into continuous trust and autonomous response as maturity grows.
Assessing Organizational Readiness for Agentic IAM
Identity Maturity as the Real Prerequisite
Agentic IAM does not begin with AI models or advanced risk engines. It begins with basic identity hygiene. Organizations need a centralized identity layer, consistent session handling, and visibility into user journeys. Without these foundations, continuous decision-making becomes guesswork rather than intelligence.
This is why CIAM maturity matters more than innovation theater. Platforms that already unify authentication, profiles, consent, and lifecycle events provide the raw material Agentic IAM depends on. The system cannot make good decisions if identity data is fragmented or outdated.
Cultural Readiness Matters Too
There is also a human side to readiness. Agentic IAM challenges teams to move away from rigid certainty and toward probabilistic thinking. Security teams must accept that not every decision is absolute. Product teams must trust identity systems to adapt flows dynamically. Leadership must be comfortable with systems that learn rather than simply enforce.
Organizations that succeed with Agentic IAM are usually the ones that already view identity as a strategic capability rather than a compliance obligation.
Implementing Agentic IAM Incrementally
Starting Where the Impact Is Highest
Most organizations begin their Agentic IAM journey in areas where static decisions are clearly failing. Fraud-prone flows, high-risk account changes, and long-lived sessions are common starting points. Introducing continuous trust evaluation in these areas delivers immediate value without disrupting the entire user base.
LoginRadius supports this incremental approach by allowing identity journeys to be orchestrated dynamically. Decisions can influence specific actions without forcing a global change to authentication policy. This reduces risk while building confidence in agentic behavior.
Letting the System Prove Itself
One of the advantages of Agentic IAM is that it becomes more valuable as it operates. As the system observes behavior and outcomes, decision quality improves. Over time, organizations often find that they can reduce visible security challenges because confidence in continuous evaluation grows.
This feedback loop is what turns Agentic IAM from an experiment into a dependable capability.
The Long-Term Shape of Identity
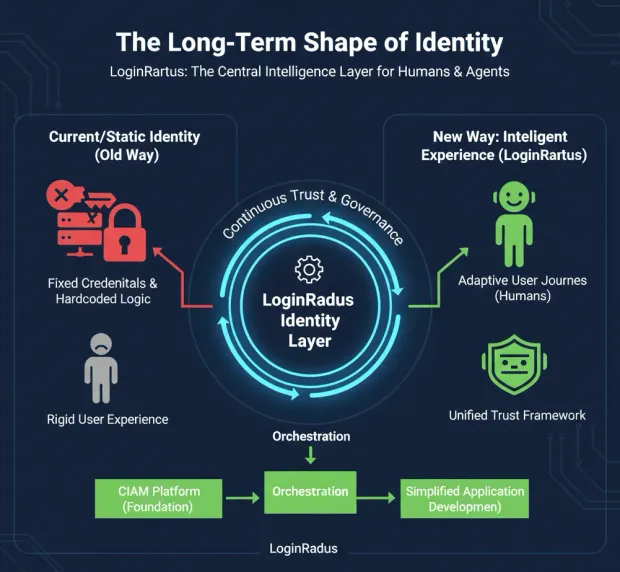
Identity as an Intelligence Layer
As Agentic IAM matures, identity stops being something applications “call” and starts being something they rely on. Decisions about access, experience, and risk are informed continuously by identity intelligence rather than hardcoded logic. This shift simplifies application development because identity concerns move into a centralized layer designed to handle them.
LoginRadius’ emphasis on orchestration, governance, and AI-readiness reflects this future. Identity becomes the system that understands who is interacting, how they are behaving, and what should happen next.
Preparing for a Mixed World of Humans and Agents
The rise of AI agents makes Agentic IAM unavoidable. These agents act autonomously, access sensitive systems, and make decisions at machine speed. Managing them with static credentials and fixed permissions is not just inefficient, it is dangerous.
By extending identity governance and lifecycle principles to non-human identities, platforms like LoginRadius make it possible to manage humans and agents within the same trust framework. This consistency will matter increasingly as AI-driven workflows become mainstream.
Why Agentic IAM Is Not Optional Anymore
Agentic IAM is not a trend waiting for adoption. It is a response to conditions that already exist. Users are dynamic. Attacks are subtle. Sessions are long. Systems are distributed. Static trust does not survive in this environment.
Organizations that continue to rely solely on login-time decisions will compensate with friction, manual review, and reactive controls. Organizations that adopt agentic principles will quietly outperform them by making better decisions more often, with less disruption.
To learn more about agentic IAM and its deployment, contact LoginRadius.
Closing Thought
Identity systems no longer succeed by being strict. They succeed by being smart. Agentic IAM represents the moment identity stops reacting to the past and starts responding to the present. Organizations that embrace this shift will not only be more secure, but more adaptable, more scalable, and more prepared for a future where trust must be earned continuously.
FAQs
What is Agentic IAM?
Agentic IAM is an identity model where trust is evaluated continuously rather than decided once at login. It uses autonomous decision logic to monitor behavior, context, and risk in real time and dynamically adjust access.
How is Agentic IAM different from traditional IAM?
Traditional IAM makes static decisions based on credentials and roles at login. Agentic IAM continuously reassesses trust throughout a session and adapts access based on behavior and context.
How is Agentic IAM different from adaptive authentication?
Adaptive authentication checks risk at specific events, usually during login. Agentic IAM evaluates trust continuously across the entire session, enabling incremental and proportional responses.
Does Agentic IAM require artificial intelligence?
No. Agentic IAM is defined by autonomous, continuous decision-making. AI enhances risk analysis and behavior detection but is not mandatory for implementation.
How does Agentic IAM improve security without increasing friction?
Agentic IAM applies security controls only when risk increases. Most users experience seamless access because verification is triggered dynamically, not universally.
Is Agentic IAM only for large enterprises?
No. Any organization managing customer identities, APIs, or AI agents can benefit from continuous trust evaluation, especially in high-risk or high-scale environments.
How does Agentic IAM support AI agents?
Agentic IAM treats AI agents as governed identities with defined permissions and lifecycles. It continuously evaluates their actions to ensure they operate within approved authority boundaries.
Can Agentic IAM work with existing CIAM platforms?
Yes. Agentic IAM extends modern CIAM by adding continuous trust evaluation, orchestration, and lifecycle-aware decision-making.
Is Agentic IAM compatible with compliance requirements?
Yes. Agentic IAM supports compliance through contextual access control, continuous monitoring, and auditable decision trails.
Why is Agentic IAM becoming important now?
Digital interactions are continuous, attackers mimic legitimate users, and AI agents act autonomously. Static login-based trust models cannot adapt to this environment.