Introduction
In today’s digital-first world, identity is everything. Whether it’s an employee logging into internal tools, a partner accessing sensitive APIs, or a customer managing their account across platforms, identity sits at the center of the experience. But as digital ecosystems expand, so does the complexity of managing who gets access to what, when, and how.
Most businesses start small. A few apps, a handful of users, maybe some local admin controls. But fast forward to scale multiple teams, hybrid cloud infrastructure, partner organizations, compliance demands, and the cracks begin to show. Suddenly, user provisioning becomes a hassle. Access audits take weeks. And enforcing consistent security policies across systems feels like a never-ending game of catch-up.
This is exactly where centralized identity management comes in. Instead of scattering identity data across different apps and silos, centralized identity management offers a single point of control to manage user identities, access rights, and authentication flows. Think of it as a command center where IT teams, security leaders, and even product owners can define who has access to what, across the entire ecosystem, from one place.
This blog explores how centralized identity management works, why it’s gaining momentum across industries, the key benefits it brings to the table, and how to evaluate whether it’s the right choice for your organization.
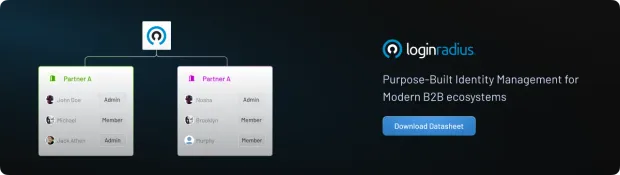
We’ll also look at how solutions like LoginRadius use a centralized identity architecture to streamline identity for businesses, especially those operating in B2B, SaaS, or multi-tenant environments. Let’s get started with the basics.
What is Centralized Identity Management?
Imagine running a business with five internal apps, a few customer-facing portals, a growing number of remote employees, and several third-party partners. Now imagine trying to manage each user account, permission, and authentication method separately for every system. Sounds like a nightmare, right? That’s exactly what centralized identity management solves.
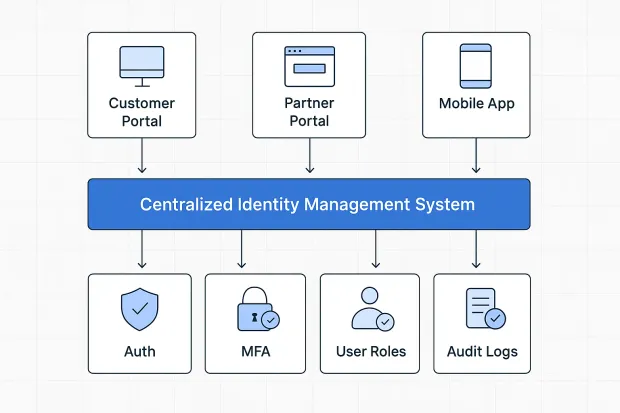
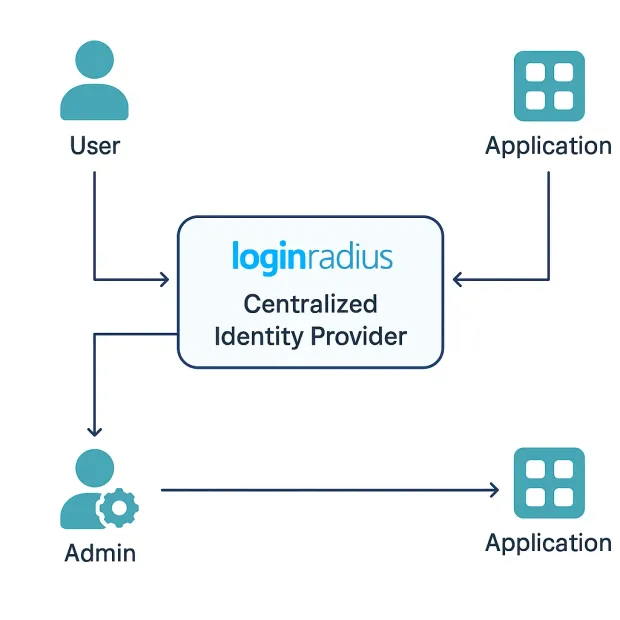
At its core, centralized identity management is about putting all your identity-related processes user authentication, access control, permission settings, and policy enforcement, under one roof. Instead of managing identities in silos across various apps and services, everything gets routed through a single, unified platform. This could be a dedicated identity management system or a modern CIAM solution like LoginRadius.
So, what does that look like in practice? It means when a user logs in, they’re authenticated through a central engine that knows:
-
who they are (identity),
-
what they’re allowed to do (authorization),
-
and where they’re coming from (context-aware security).
This centralized access control helps enforce consistent rules across the board, whether someone is accessing your main app, a legacy system, or a third-party integration. And from the admin’s side? It’s a dream.
You can:
-
Onboard or offboard users with a few clicks,
-
Monitor login activity across platforms,
-
Apply global security policies like MFA or password resets,
-
And manage role-based access all from a centralised system.
This model also leans heavily on centralized authentication, meaning all login requests, tokens, or session data are managed and validated through a trusted, secure hub. For developers, it offers clean APIs and SDKs to hook into your systems. For security teams, it reduces blind spots and misconfigurations. And for businesses, it brings agility, compliance, and peace of mind.
In short, centralized identity management is the foundation for building secure, scalable, and user-friendly access in today’s complex digital environment.
Next, let’s dive into how this actually works behind the scenes.
What is Centralized Identity Management?
Imagine running a business with five internal apps, a few customer-facing portals, a growing number of remote employees, and several third-party partners. Now imagine trying to manage each user account, permission, and authentication method separately for every system. Sounds like a nightmare, right?
That’s exactly what centralized identity management solves. At its core, centralized identity management is about putting all your identity-related processes user authentication, access control, permission settings, and policy enforcement, under one roof. Instead of managing identities in silos across various apps and services, everything gets routed through a single, unified platform. This could be a dedicated identity management system or a modern CIAM solution like LoginRadius.
So, what does that look like in practice?
It means when a user logs in, they’re authenticated through a central engine that knows:
-
who they are (identity),
-
what they’re allowed to do (authorization),
-
and where they’re coming from (context-aware security).
This centralized access control helps enforce consistent rules across the board, whether someone is accessing your main app, a legacy system, or a third-party integration. And from the admin’s side? It’s a dream.
You can:
-
Onboard or offboard users with a few clicks,
-
Monitor login activity across platforms,
-
Apply global security policies like MFA or password resets,
-
And manage role-based access all from a centralised system.
This model also leans heavily on centralized authentication, meaning all login requests, tokens, or session data are managed and validated through a trusted, secure hub. For developers, it offers clean APIs and SDKs to hook into your systems. For security teams, it reduces blind spots and misconfigurations. And for businesses, it brings agility, compliance, and peace of mind.
How Does Centralized Identity Management Work?
Let’s walk through the mechanics of how a centralized identity management system actually functions behind the scenes.
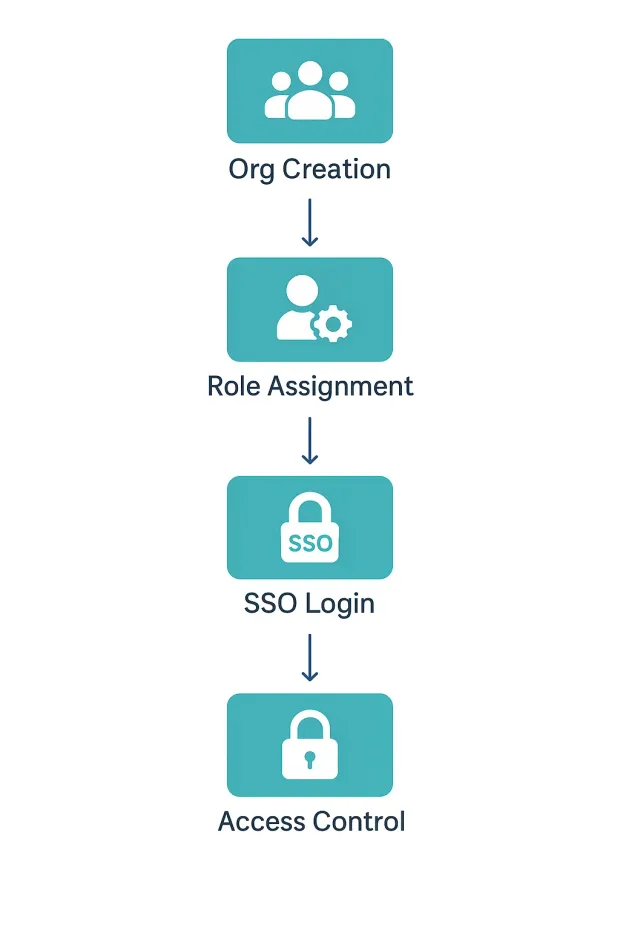
At a high level, it all starts with a single source of truth, your centralized identity platform. This is where all user identities are created, stored, and managed. Think of it like the air traffic control tower for all identity interactions across your organization. Every login attempt, every permission check, every user role assignment, everything routes through this core engine.
Here’s how it typically works:
1. Identity Enrollment and Provisioning
When a new user, be it an employee, partner, or external customer, needs access to your system, their identity is created within the centralized platform. Instead of provisioning them separately on each app, the system acts as the master record.
For B2B organizations or partner ecosystems, this often involves setting up the partner’s organization first and then provisioning users under it.
Example: Creating a New Organization via LoginRadius Partner IAM API
POST https://api.loginradius.com/identity/v2/manage/account/organization
1{
2"organizationName": "Tech Vendor Ltd",
3"organizationDescription": "B2B Vendor from EU",
4"adminEmail": "admin@techvendor.com"
5}This creates a new partner organization. You can then add users, assign roles, and configure domain restrictions all from your central identity layer.
More info: Organizations Management – LoginRadius Docs
2. Centralized Authentication
Once identities are created, the next piece is login. When users try to sign in, they’re routed through a centralized authentication service, often using protocols like OpenID Connect or SAML.
Here, LoginRadius (or your chosen IAM system) validates:
-
Credentials (password, OTP, passkey, etc.)
-
Context (IP address, device fingerprint, time of access)
-
MFA policies (step up if something looks off)
All this happens in real-time, through a unified gateway that ensures consistency and security, no matter which app the user is accessing.
3. Authorization and Access Control
Once authenticated, the system moves to centralized access control. This is where role-based or policy-based access comes in.
For example:
-
A “Partner Manager” role might allow access to dashboards, user invites, and reporting tools.
-
An “End Customer” might only get read-only access to their own data.
This access control logic is centrally defined and enforced across applications, ensuring that no one has more (or less) access than intended.
4. Session and Token Management
In modern architectures, once a user is authenticated, a secure session or access token (JWT or opaque) is issued. This token is trusted by all apps connected to the centralized system, so users don’t need to log in again when switching apps, enabling seamless single sign-on (SSO) experiences.
And if a user logs out or their access is revoked, the token is invalidated across the ecosystem.
5. Audit, Monitoring, and Compliance
All of these activity logins, role changes, and access attempts are logged and stored in a centralized audit trail. This is a lifesaver for:
-
Security teams are monitoring anomalies
-
Admins reviewing permission grants
-
Compliance officers tracking data access
With a centralized security management layer, it’s easier to stay on top of regulations like GDPR, HIPAA, or SOC 2.
Real-Life Example
Let’s say your SaaS platform has:
-
A web dashboard for customers
-
An internal admin console
-
A partner portal
With LoginRadius acting as the centralized identity hub, each of these apps connects to the same user store, authentication flow, and role-based access system.
So when a new partner signs up via the portal:
-
They’re added to your organization model
-
Assigned roles via a predefined template
-
Given access to APIs, resources, or dashboards, all governed centrally
Example: Token Validation Using LoginRadius
Here’s how you can validate access tokens from any app using LoginRadius:
1GET https://api.loginradius.com/identity/v2/auth/access_token/validate?access_token=YOUR_ACCESS_TOKENThis is exactly how centralized identity management brings order to the identity chaos.
Benefits of a Centralized Identity Management System
Managing digital identities used to be a patchwork effort—each department had its own system, access controls varied by application, and onboarding new users felt like reinventing the wheel. But that’s no longer sustainable in a world where businesses rely on dozens (if not hundreds) of apps, APIs, and external partners.
A centralized identity management system doesn’t just simplify how identities are handled; it fundamentally improves how your organization operates, secures itself, and scales.
Let’s break down the key benefits.
1. Unified Control Across the Ecosystem
With centralized identity management, you gain a single pane of glass to manage identities across your entire digital footprint. Whether it’s a customer-facing app, a backend partner portal, or internal tools, everything connects to one central identity store.
This unified view enables:
-
Consistent policy enforcement
-
Cross-application role management
-
Simplified audits and monitoring
No more jumping between admin panels or asking “Where is this user configured again?”
2. Stronger Security Through Centralized Access Control
Security is only as strong as its weakest link. Decentralized systems often have inconsistent password policies, outdated roles, or unmonitored admin accounts. Centralizing access allows you to close these gaps.
With centralized access control:
-
You can apply MFA, login alerts, or session timeouts across all apps.
-
Any suspicious login can trigger adaptive responses like risk-based authentication.
-
Offboarding users is immediate and universal no dangling access rights.
This level of centralized security management drastically reduces your attack surface and helps enforce least privilege across users and apps.
3. Seamless User Onboarding and Delegated Admin
Onboarding users, especially in B2B environments, can get messy. But with a centralized identity approach, you can automate and delegate onboarding while still maintaining tight control.
For example, using LoginRadius Partner IAM:
-
You can auto-provision users under their organization.
-
Admins can be granted limited roles to manage users within their own org.
-
You define what they can and cannot do centrally—no micromanagement needed.
This simplifies collaboration with external vendors, partners, or franchise teams, without sacrificing governance.
4. Better Developer Productivity
For dev teams, integrating identity often becomes a side quest. Centralized IAM platforms eliminate that complexity with clean APIs, prebuilt workflows, and centralized logs. That means:
-
No need to reinvent login or user provisioning flows.
-
Easier debugging across environments.
-
One token model for SSO across apps.
This speeds up shipping, simplifies maintenance, and aligns with dev-first environments.
5. Compliance Without the Headache
Whether you’re navigating GDPR, HIPAA, SOC 2, or industry-specific compliance standards, centralized IAM simplifies things drastically:
-
Unified logs make auditing easy.
-
Consent management is consistent across apps.
-
You can quickly locate, export, or delete user data.
In regulated industries like finance, healthcare, or education, this is no longer optional—it’s expected.
6. Scalability for the Long Run
Adding new applications or business units? Expanding globally? Integrating with partners?
A centralised system gives you a scalable foundation. You don’t need to re-architect identity flows every time just plug into the centralized platform and inherit existing authentication, authorization, and logging capabilities.
A centralized identity management system isn’t just about simplifying logins. It’s about unlocking visibility, control, and trust at every level of the identity lifecycle. From onboarding to offboarding, from securing access to meeting compliance, it offers a reliable foundation that grows with your business.
Real-World Example
Swann, a global security camera brand, uses centralized identity management with LoginRadius to provide seamless access to millions of users across apps, while their developers manage users, roles, and API permissions from a single pane of glass.
Challenges of Centralized Identity Management
While centralized identity management offers clarity, control, and consistency, it’s not a silver bullet. Like any system design, centralization brings its own set of challenges. These are not flaws, per se, but trade-offs that must be carefully considered during implementation.
Let’s break down the major challenges that organizations, especially growing SaaS platforms and B2B ecosystems, should be aware of before going all-in.
1. Single Point of Failure (If Not Designed Resiliently)
The biggest concern with any centralized architecture is this: what happens if the central system goes down?
If your centralized authentication provider is unavailable, users can’t log in, admins can’t manage access, and critical applications may become unusable. The business impact? Downtime, support overload, and lost trust.
This doesn’t mean centralized systems are unreliable only that they must be built for high availability. A production-grade solution like LoginRadius mitigates this through:
-
Distributed infrastructure across cloud regions
-
Load-balanced authentication nodes
-
Auto-failover and real-time health monitoring
If you’re building a self-hosted identity management system, replicating this level of reliability is a serious engineering commitment.
2. Migration Complexity from Legacy or Siloed Systems
Transitioning to a centralized model isn’t as simple as flipping a switch especially for organizations that have:
-
Multiple identity providers (e.g., social logins, LDAP, homegrown systems)
-
Different user schemas and naming conventions
-
Inconsistent access policies across applications
The migration process involves:
-
Auditing and cleaning up user data
-
Unifying identity records (merging duplicate accounts)
-
Reintegrating all your apps with the new system
-
Re-educating users and teams on how access works now
Without careful planning, this phase can result in broken login flows, access gaps, or unnecessary user friction.
That said, tools like LoginRadius offer progressive migration allowing you to sync users over time and integrate with existing apps using standards like OpenID Connect and SAML.
3. Delegation and Multi-Level Access Hierarchies
In real-world businesses, access isn’t flat. You don’t just have one admin and one group of users you often need:
-
Organization-level segmentation (e.g., partners, franchises, regional teams)
-
Delegated admin rights (e.g., an org admin managing their own users)
-
Scoped permissions (e.g., access only to specific modules)
Configuring this in a centralized access management setup is not trivial. It requires:
-
Role-based access control (RBAC)
-
Attribute-based access control (ABAC)
-
Hierarchical policy enforcement
Done wrong, this leads to either over-permissioned users (a major security risk) or under-permissioned users (a massive productivity blocker).
With LoginRadius Partner IAM, however, these concerns are baked in supporting organization isolation, role delegation, and custom branding at scale.
4. Vendor Lock-in and Loss of Flexibility
When you centralize identity with a single provider, you’re not just using their login form—you’re adopting their:
-
APIs
-
Token formats
-
Session management logic
-
Admin tools
This deep integration can make it hard to switch vendors later. If pricing changes, a feature gets deprecated, or support becomes unresponsive you may feel stuck.
To reduce the risk of lock-in:
-
Choose vendors who follow identity standards (OIDC, SAML, SCIM)
-
Use abstraction layers where possible
-
Keep critical user data portable
LoginRadius, for example, is API-first and standards-compliant, which gives developers the flexibility to integrate or migrate without being boxed in.
5. Data Sovereignty and Privacy Regulations
Centralizing identity means centralizing personal data usernames, emails, IP addresses, session activity, etc. That creates compliance implications, especially if:
-
Your users are in Europe (GDPR)
-
You handle health data (HIPAA)
-
You serve enterprise clients with strict contractual requirements
Some countries also enforce data localization laws, requiring user data to be stored within national borders. If your identity provider doesn’t offer regional hosting or compliance alignment, you may face legal and contractual pushback.
This is why centralization in management must be balanced with data residency controls. LoginRadius, for instance, supports localized data hosting options, helping you stay compliant while remaining centralized.
So, Is Centralized Identity Worth It?
The short answer: yes—but only when done right. Centralized identity management offers enormous benefits—but it’s not plug-and-play. You need:
-
The right architecture
-
The right partner
-
And the right operational practices
The good news? Mature platforms like LoginRadius already solve many of these challenges with enterprise-grade features, global infrastructure, and developer-friendly APIs.
Centralized vs. Decentralized Identity Management
Centralized identity management isn’t the only way to manage users. In recent years, a growing number of businesses and communities have started exploring decentralized identity models often built on blockchain, cryptographic proofs, or peer-to-peer protocols.
So how do the two compare? Let’s break it down simply.
Key Differences at a glance
| Criteria | Centralized Identity Management | Decentralized Identity Management |
|---|---|---|
| Ownership of Identity Data | Controlled and stored by a central authority (e.g., LoginRadius) | Controlled by the user; data is stored on user devices or distributed networks |
| Trust Model | Trust is placed in a single, vetted identity provider | Trust is distributed across cryptographic proofs and decentralized networks |
| Access Management | Centralized access policies, RBAC/ABAC, delegated admin | Access granted by the user or issuer; no central enforcement layer |
| Authentication Method | Username/password, SSO, MFA via centralized systems | Wallet-based login, verifiable credentials, device-held keys |
| Scalability and Deployment | Proven for SaaS, B2B platforms, multi-tenant models | Still experimental at scale; more suited for niche or privacy-first apps |
| Developer Experience | API-driven, fast integration, mature SDKs and tools | Emerging tools, less standardized integration patterns |
| Security Management | Centralized threat detection, MFA enforcement, session monitoring | Lower attack surface per user, but fewer enterprise-grade controls |
| Compliance and Governance | Easy to enforce GDPR, HIPAA, SOC2 via unified logging and consent management | Requires custom mapping to compliance rules; harder to audit due to decentralized data |
| Recovery and Support | Admin-driven recovery, centralized user helpdesk workflows | User-driven recovery; often limited or complex fallback options |
| Use Case Examples | LoginRadius, Okta, Ping Identity, Azure AD B2C | Microsoft Entra Verified ID, Sovrin, Dock, Web3 wallets |
When Centralized Identity Works Best
Centralized identity management is ideal when:
-
You’re running a SaaS platform with multiple user groups (customers, partners, admins)
-
You need to enforce consistent security policies across your ecosystem
-
You want to provide seamless SSO across all your apps
-
You require a unified audit trail for compliance
-
You want to delegate access control (e.g., for partner orgs) while keeping a central overview
This is why platforms like LoginRadius are designed with centralized authentication, multi-tenant management, and fine-grained access control baked in.
Where Decentralized Identity Has an Edge
Decentralized identity is a better fit when:
-
Users need full control over their credentials (e.g., digital ID wallets)
-
Privacy is a top priority and you want to minimize central data storage
-
You're building for a Web3 or blockchain-native environment
-
You’re experimenting with SSI (Self-Sovereign Identity) or verifiable credentials
But make no mistake decentralization doesn’t mean no complexity. The onboarding process can be slower, recovery mechanisms can be clunky, and most enterprises still lack infrastructure to support it at scale.
Real-World Analogy
Think of centralized identity like a passport office it manages all records, verifies your identity, and gives you a globally trusted ID. Decentralized identity is more like carrying a self-issued ID that others can verify without checking a central registry.
| If you need… | Choose… |
|---|---|
| Scalability, compliance, and partner orgs | Centralized Identity Management |
| Full user control, privacy-first design | Decentralized Identity Management |
Centralized or Decentralized: Which One Is Better?
The short answer? It depends on what you're building and who you're building for.
Both centralized and decentralized identity management have their place in the modern identity landscape. The key is to match the model to your business requirements, technical maturity, user expectations, and regulatory obligations.
Let’s break it down a little more practically.
Choose Centralized Identity Management If:
You’re an enterprise, SaaS platform, or B2B provider that needs:
-
A single source of truth for users, roles, and permissions
-
Fine-grained access control across multiple apps or organizations
-
High availability, disaster recovery, and support SLAs
-
Compliance-ready architecture for GDPR, HIPAA, SOC2, etc.
-
A streamlined way to onboard and manage partners, vendors, or clients
Centralized IAM solutions like LoginRadius offer:
-
Unified user stores
-
Delegated admin with organization isolation
-
Centralized authentication with SSO/MFA
-
Secure APIs and token management
-
Global infrastructure with region-specific data residency
In short, if scalability, control, and integration matter more than end-user credential ownership, centralized is the way to go.
Consider Decentralized Identity Management If:
You’re building:
-
A privacy-first product where users want full control of their data
-
An app that operates in Web3, blockchain, or P2P ecosystems
-
A solution that embraces self-sovereign identity (SSI) or verifiable credentials
-
A platform where trust is distributed and identities are validated by consensus or proofs
Decentralized identity is still in its early days, but it's powerful for:
-
Reducing data collection
-
Preventing vendor lock-in
-
Giving users autonomy over their identity footprint
However, you’ll need to be ready to educate users, handle complex recovery flows, and potentially build out infrastructure that's not yet as mature or enterprise-ready as centralized options.
Centralized vs. Decentralized: Which One Fits Your Use Case?
| Use Case / Requirement | Centralized Identity Management | Decentralized Identity Management |
|---|---|---|
| You manage SaaS products with multiple user roles (admin, partners, customers) | ✅ Supports RBAC/ABAC, multi-tenant orgs, and delegated admin | ❌ Not ideal for role-based access across enterprise systems |
| Need enterprise-grade security (MFA, SSO, audit trails) | ✅ Built-in support for SSO, MFA, session monitoring, real-time logging | ❌ Requires custom development; lacks mature enterprise tooling |
| Compliance with GDPR, HIPAA, SOC2, etc. | ✅ Easy to implement via centralized logs, consent, and data residency options | ❌ Complex due to distributed storage and user-controlled data |
| Onboarding vendors, franchises, or external teams | ✅ Organization-level isolation, role delegation, API-based provisioning | ❌ No native concept of "organizations"; onboarding flows are user-driven |
| Developer velocity and ease of integration | ✅ Mature APIs, SDKs, and plug-and-play integrations with cloud apps | ❌ Limited tooling, steep learning curve, evolving ecosystem |
| Need for offline credentials or digital identity wallets | ❌ Not designed for offline or wallet-based verification | ✅ Purpose-built for user-held credentials and peer-to-peer validation |
| User wants full control of their identity and no central storage | ❌ Centralized platform stores identity metadata and activity logs | ✅ Identity is owned and stored by the user, not the provider |
| Building on blockchain or Web3 infrastructure | ❌ Centralized architecture doesn't align with decentralized protocols | ✅ Designed for distributed networks, smart contracts, and token-based auth |
| Long-term scalability for partner ecosystems | ✅ Proven across B2B platforms, supports multi-org growth, regional scaling | ⚠️ Still experimental for enterprise use at global scale |
| Recovery, account lockouts, user support | ✅ Admin-assisted recovery, email/SMS fallback, helpdesk-friendly | ⚠️ Recovery relies on user key management; no admin override possible |
Still unsure? Many modern architectures are hybrid, combining centralized identity (for access management) with support for decentralized credentials (for privacy or verification use cases).
If you’re managing users, roles, permissions, and logins at scale—and want to move fast while staying secure centralized identity management gives you the reliability, scalability, and control needed to grow confidently.
And with platforms like LoginRadius, you don’t have to start from scratch. You get a fully managed, enterprise-ready identity solution with APIs, SDKs, and prebuilt integrations tailored to your stack.
Conclusion
Identity is no longer just a login box it’s the foundation of trust, security, and user experience in the digital age. Whether you're onboarding new partners, managing internal teams, or securing customer portals, how you manage identity determines how securely and efficiently your business runs.
Centralized identity management offers a unified, scalable approach that simplifies access control, improves security posture, and reduces operational overhead. It’s especially powerful for SaaS platforms, B2B ecosystems, and enterprises that need to scale quickly without sacrificing visibility or compliance.
Yes, there are challenges, such as migration complexity, delegation models, and potential vendor lock-in—but with the right architecture and a mature platform like LoginRadius, these can be handled confidently.
On the flip side, decentralized identity introduces powerful concepts like self-sovereign identity, data minimization, and cryptographic trust—but it’s still evolving and isn’t always practical for enterprise or multi-user environments just yet.
Ready to Streamline Your Identity Strategy?
LoginRadius makes centralized identity management enterprise-ready and developer-friendly. With multi-tenant org structures, delegated admin, robust APIs, and support for regional data residency, you get the power of control without the complexity. Explore LoginRadius Partner IAM
FAQs
1. How does Centralized Identity Management improve security?
A: It enforces consistent access policies, enables real-time threat monitoring, and reduces misconfigurations by managing all authentication and authorization from a single control point.
2. What components are typically involved in a Centralized Identity Management system?
A: Core components include a centralized user directory, authentication engine, access control policies (RBAC/ABAC), SSO integration, MFA support, and audit logging tools.
3. Can Centralized Identity Management support SSO and MFA?
A: Yes, it natively supports Single Sign-On (SSO) and Multi-Factor Authentication (MFA) across apps, ensuring seamless access and strong layered security.
4. Is Centralized Identity Management scalable for large organizations?
A: Absolutely. With multi-tenant architecture, delegated admin, and API-first design, it scales effortlessly to support thousands of users, partners, and applications.
5. What role does Centralized Identity Management play in compliance?
A: It simplifies compliance by centralizing audit logs, enforcing global security policies, managing consent, and supporting region-specific data residency requirements.