Introduction
If your B2B SaaS product is heading into 2026 with an SSO pitch that begins and ends with “Yes, we support SAML,” that is usually where the trouble starts.
Enterprise buyers are not checking for a basic single sign-on feature. They are trying to figure out whether your authentication architecture can hold up inside real customer environments. That means multiple identity providers, multiple tenants, strict security policies, custom domains, routing complexity, and almost no patience for login failures.
A surprising pattern we’ve seen: plenty of SaaS teams think they have enterprise SSO because they can complete a SAML handshake. Then the first serious customer asks harder questions.
And those questions come fast. How do you identify which tenant is trying to log in? How do you route users to the right IdP? Can one product support different enterprise login flows without mixing up tenant context? What happens when one customer wants SP-initiated login and another insists on IdP-initiated access? If the answers sound improvised, security teams notice. Procurement notices too.
Here’s where teams usually go wrong: they treat SSO as a feature instead of an architectural layer. In smaller SaaS products, that shortcut can survive for a while. In enterprise SaaS, it usually does not. SSO touches tenant isolation, redirect logic, assertion validation, policy enforcement, session scope, and auditability. Miss tenant awareness early, and the rest of the authentication flow gets shaky fast.
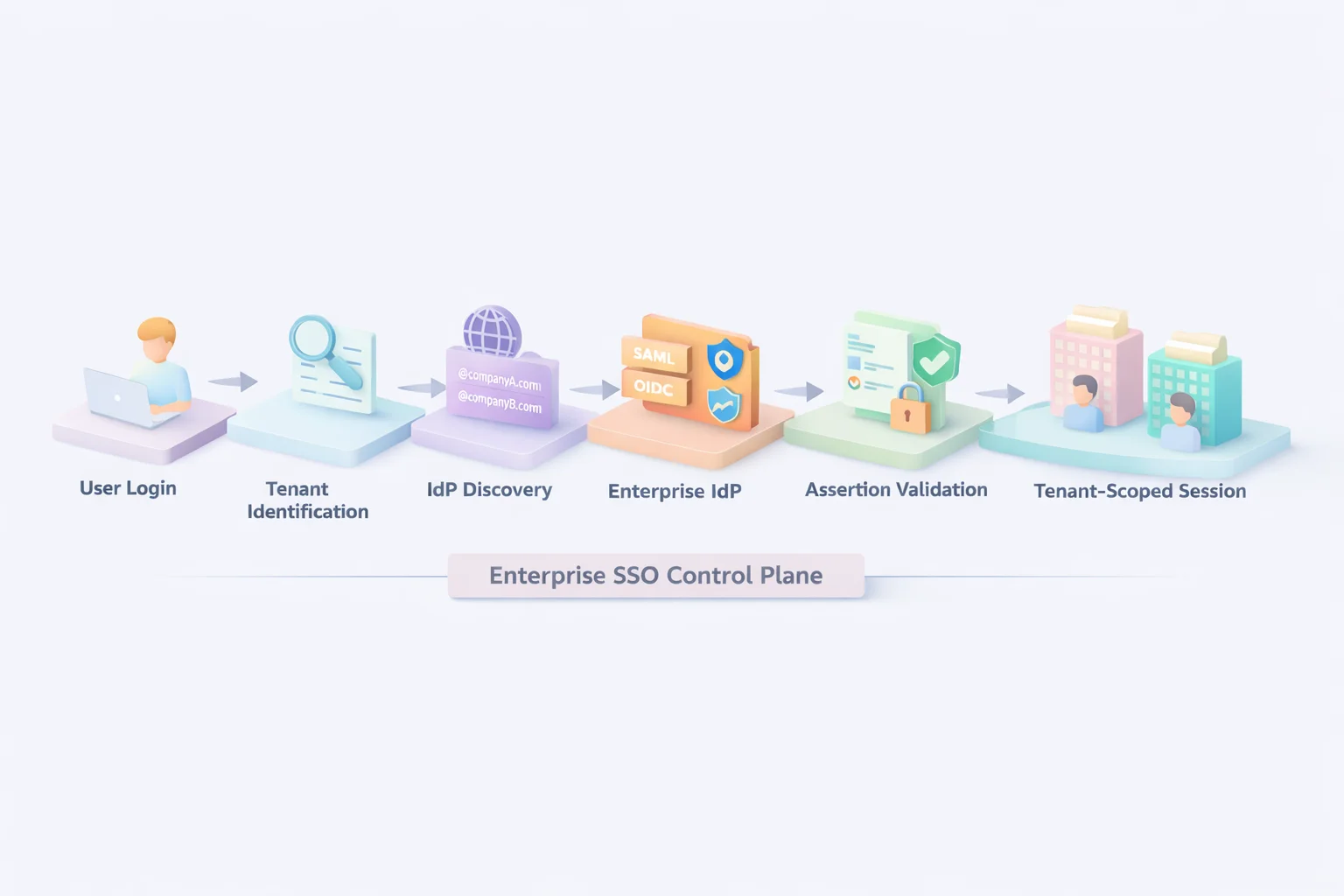
Modern enterprise SSO is not just about connecting to an identity provider. It is about knowing which organization is logging in, routing that request correctly, validating the response securely, and creating a session that stays cleanly scoped to the right tenant. No leakage. No guessing. No brittle routing rules hiding behind the login screen.
This is exactly where many SaaS implementations start breaking under growth. IdPs get hardcoded. Tenant routing gets bolted on later. One customer per environment becomes an invisible design assumption. It works right up until the product starts landing larger accounts.
This guide focuses on two layers that separate basic SSO from enterprise-ready SaaS authentication: IdP discovery and tenant routing. Because in B2B SaaS, login is not just a sign-in flow. It is one of the first places enterprise buyers test whether your platform is actually built for them.
What Enterprise Buyers Actually Expect from SSO for Enterprise SaaS
Enterprise buyers don’t ask whether you support SSO. They assume you do. What they’re really evaluating is whether your SSO for enterprise can operate inside their identity ecosystem without creating risk, friction, or operational chaos.
In modern single sign-on SaaS, enterprises expect support for both SAML and OIDC without workarounds. They expect just-in-time provisioning, so users don’t need to be pre-created. They expect SCIM for lifecycle management. They expect role mapping that respects their internal group structure. And they expect custom domains that preserve branding and security boundaries.
More importantly, they expect multi-tenant awareness. Every enterprise customer should have its own identity configuration, its own certificates, its own metadata, and its own policy controls. If your SaaS platform authentication layer shares configuration logic across tenants without strict isolation, security teams will notice.
Traditional SaaS authentication models often break here. Many platforms start with a single IdP integration and then scale by duplicating the configuration manually. That approach works until you onboard your tenth enterprise customer. After that, certificate rotation becomes messy, metadata updates become risky, and tenant routing starts depending on brittle logic.
Enterprise buyers also expect flexibility in authentication flows. Some want SP-initiated login from your application. Others demand an IdP-initiated login from their identity dashboard. A serious authentication SaaS platform must support both without compromising security controls or deep linking.
They also expect reliability. SSO outages are not minor bugs; they are business interruptions. When login fails, productivity stops. That’s why buyers look for architecture that isolates tenants, validates assertions strictly, enforces audience restrictions correctly, and handles certificate rotation without downtime.
In short, enterprise SSO is not about “logging in with SAML.” It’s about designing SSO for SaaS as a control plane that understands tenants, enforces boundaries, and scales without breaking under complexity. And that’s where architecture decisions begin to matter.
Architecture Deep Dive: How SSO for SaaS Actually Works
At a surface level, single sign-on SaaS sounds simple. Redirect the user to their identity provider, receive an assertion, validate it, and create a session. Done.
In reality, enterprise-grade SSO for enterprise involves far more moving parts, especially in multi-tenant B2B SaaS environments.
When a user attempts to log in, your SaaS platform authentication layer must first determine context. Who is this user associated with? Which tenant are they part of? Which identity provider should handle authentication? Without resolving the tenant context early, everything that follows becomes fragile.
Once the tenant context is identified, the IdP discovery logic selects the correct enterprise identity provider. The user is redirected to that IdP, where authentication occurs under the enterprise’s own policies, MFA rules, device trust, network restrictions, and conditional access.
After successful authentication, the IdP sends back a signed assertion or token. This is where many SaaS authentication implementations underestimate the importance of strict validation.
Signature verification, certificate trust validation, issuer checks, audience restriction, and replay protection must all be enforced before a session is created.
But the most critical step in enterprise authentication SaaS architecture happens after validation: tenant binding.
The returned identity must be bound explicitly to the correct tenant context. The session issued must be tenant-scoped. Access tokens must carry tenant identifiers. Role mapping must be evaluated within that organization’s boundary. Without tenant-scoped enforcement, cross-tenant exposure becomes a real risk.
Enterprise buyers expect this entire flow to be deterministic and isolated. They do not want a shared control plane where one misconfiguration affects another customer. They want confidence that every authentication event is evaluated within strict organizational boundaries.
In short, SSO for SaaS is not just federation. It is tenant-aware federation backed by strict validation, context binding, and isolation-first session issuance. And before any of that works reliably, one key layer must function correctly: IdP discovery.
Tenant Routing: Where Most SaaS Platforms Quietly Fail
If IdP discovery determines where a user goes to authenticate, tenant routing determines what happens when they come back.
This is the layer that separates demo-ready single sign-on SaaS from enterprise-grade SSO for enterprise.
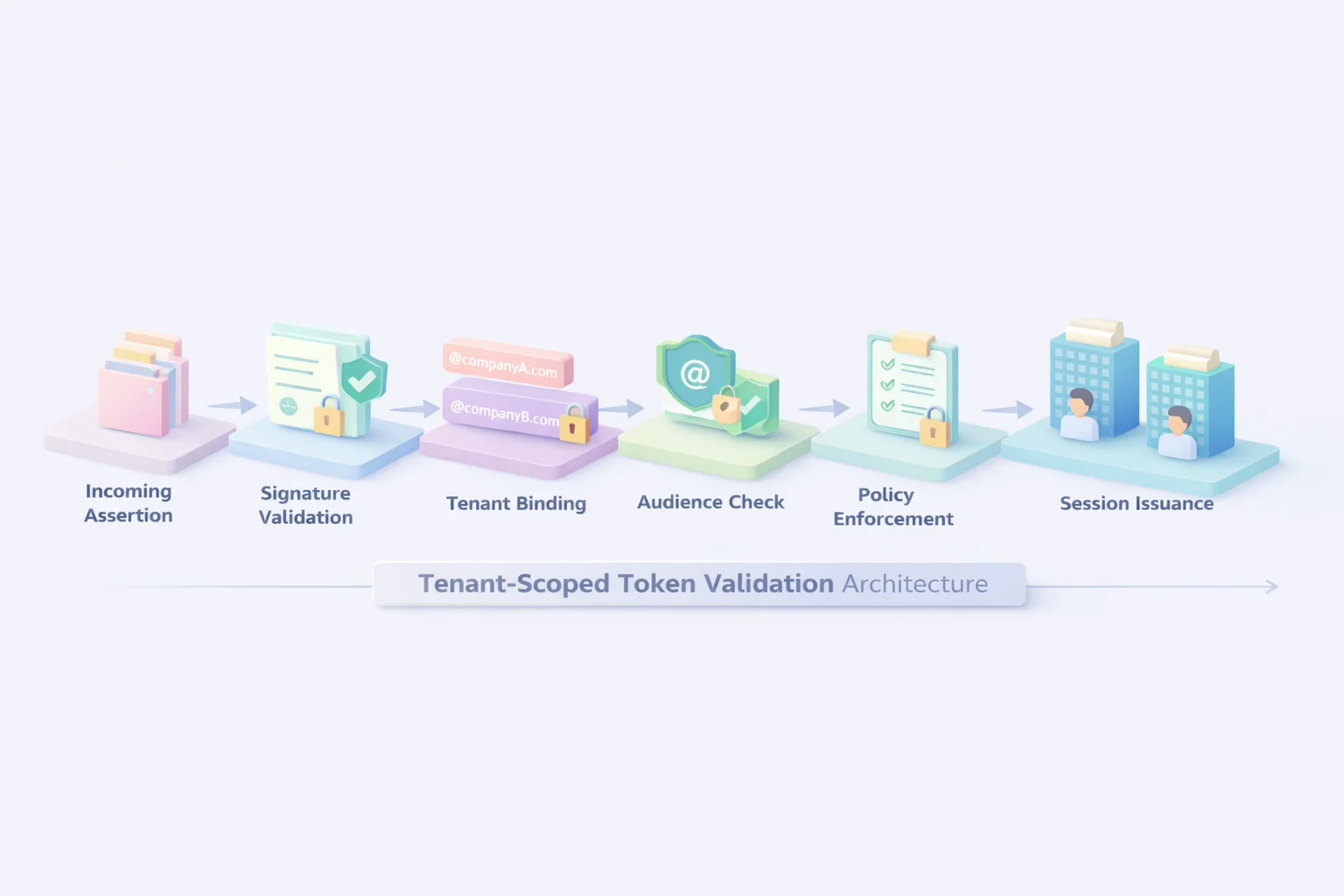
Tenant routing is the process of binding an authentication response to the correct organizational context before issuing access. In multi-tenant SaaS platform authentication, this step must happen before session creation, before role mapping, and before any authorization logic runs.
When the identity provider sends back a SAML assertion or OIDC token, your system cannot simply validate the signature and log the user in. It must resolve which tenant this authentication belongs to, confirm that the assertion was intended for that tenant, and enforce tenant-specific policies.
This is where fragile SaaS authentication designs start to show cracks.
If the tenant context is inferred loosely, perhaps from a shared callback endpoint or a generic login URL, the risk of cross-tenant confusion increases. If tenant identifiers are not embedded and validated properly, session isolation weakens. If audience restrictions are not enforced per tenant, assertions may technically validate but still violate organizational boundaries.
Enterprise buyers know this. Their security teams will ask whether tenant IDs are part of the token validation process. They will ask how audience claims are enforced. They will ask whether certificate trust is scoped per organization. These are not theoretical concerns. They are standard evaluation criteria for serious authentication SaaS platforms.
Proper tenant routing means that every authentication response is evaluated within a strict tenant context. Signature verification happens against the correct certificate. Audience validation checks against the tenant-specific service identifier. Role mapping applies only to that organization’s configuration. Session issuance includes tenant-scoped claims.
When done correctly, tenant routing becomes invisible. Users log in seamlessly, and enterprises feel confident that their identity boundary is respected.
When done poorly, authentication may still “work,” but isolation becomes fragile. And in B2B SaaS, fragile isolation is not something enterprise buyers tolerate.
In modern SaaS SSO, tenant routing is not a background process. It is the core enforcement layer that keeps one customer’s identity policies from bleeding into another’s environment.
SP-Initiated vs IdP-Initiated SSO: Buyers Will Test Both
If your enterprise-only SSO works only in one direction, enterprise buyers will find out quickly.
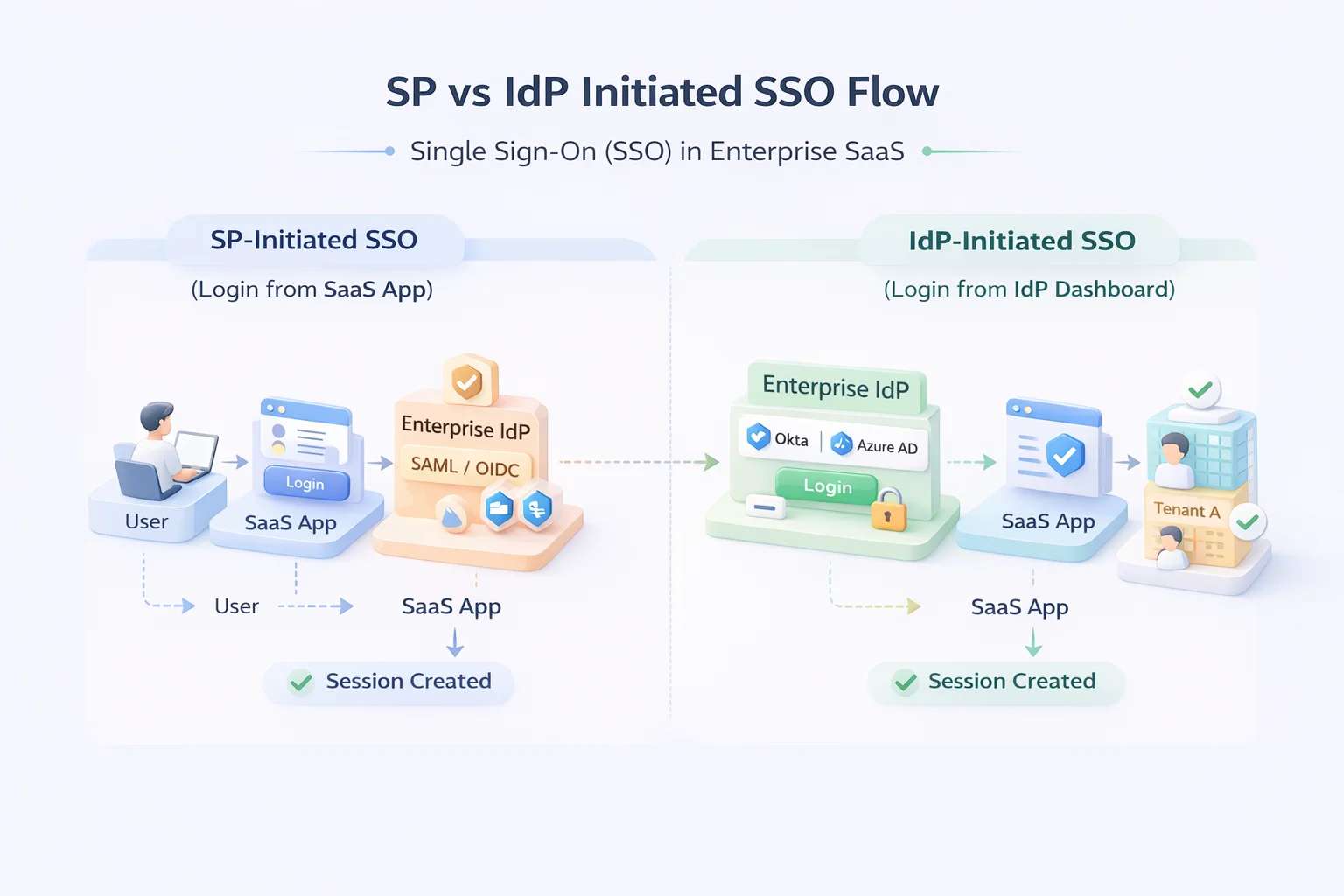
There are two primary flows in single sign-on SaaS: SP-initiated and IdP-initiated. Supporting both is not a “nice to have.” In B2B environments, it’s expected.
In an SP-initiated flow, the user starts at your SaaS application. They click login, your SaaS platform authentication layer identifies tenant context, performs IdP discovery, and redirects them to their enterprise identity provider. After authentication, the assertion returns to your assertion consumer service (ACS), where validation and tenant binding occur before session issuance.
This flow gives your application more control. You can enforce pre-authentication logic, preserve deep links, and ensure routing decisions happen before redirect. Most modern saas platforms prefer SP-initiated flows because they provide cleaner context management.
In an IdP-initiated flow, the user starts at their enterprise identity dashboard. They click your application tile inside Okta, Azure AD, or another IdP. The identity provider sends a signed assertion directly to your ACS endpoint. No prior context was established by your application.
This is where weaker SaaS authentication designs struggle. Without careful tenant routing, the system must infer tenant context purely from the incoming assertion. Audience validation, issuer validation, and strict certificate scoping become critical. RelayState handling must be secure to avoid open redirect issues. CSRF protections must still apply.
Enterprise IT teams often prefer IdP-initiated login because it centralizes application access within their identity portal. If your authentication SaaS architecture cannot support this cleanly, it signals immaturity.
Security teams will also evaluate replay protection, assertion expiration handling, and strict enforcement of assertion audiences. They will test whether deep links survive the flow. They will test what happens when assertions are sent without proper tenant context.
Supporting both SP-initiated and IdP-initiated flows is not just about protocol compliance. It’s about proving that your SSO for SaaS architecture can operate safely regardless of where authentication begins.
And for enterprise buyers, flexibility combined with strict validation is the standard, not the exception.
Multi-Tenant SaaS Authentication: The Hidden Complexity Behind “It Just Works”
On the surface, SSO for enterprise sounds like federation plus token validation. In multi-tenant B2B SaaS, it’s significantly more complex.
Every enterprise customer expects isolation. Not logical isolation. Real isolation. Their own identity provider configuration, their own certificates, their own attribute mappings, and their own policy controls.
When they evaluate your SaaS platform authentication, they are assessing whether your architecture respects that boundary at every layer.
In true multi-tenant SaaS authentication, each tenant must have a dedicated configuration scope. That includes SAML metadata, signing certificates, OIDC client credentials, redirect URIs, and role mapping rules. These configurations cannot leak across tenants, even accidentally.
Certificate management alone becomes a serious architectural concern. Enterprises rotate certificates. They update metadata. They change signing algorithms. Your authentication SaaS platform must handle certificate updates without downtime and without affecting other tenants. If one tenant rotates a certificate, another tenant’s login flow must remain untouched.
Custom domains add another layer. Many enterprise customers require branded login URLs. That means your SSO for SaaS architecture must support custom subdomains or vanity domains while still maintaining centralized validation and strict tenant routing. The routing logic cannot rely on shared callback endpoints without enforcing tenant context rigorously.
Provisioning increases complexity further. Enterprises expect just-in-time provisioning during SSO, and many expect SCIM-based lifecycle management. User deactivation in their identity provider should reflect in your system automatically.
If your architecture treats SSO and provisioning as separate concerns, identity drift becomes inevitable.
Auditability is another expectation. Enterprises want tenant-scoped logs. They want to know which assertion was validated, which certificate was used, which attributes were mapped, and which session was issued. Multi-tenant single sign-on SaaS must produce logs that are isolated and traceable per organization.
What often breaks immature implementations is shared state. Shared signing keys. Shared callback URLs without strict scoping. Shared role mappings across tenants. These shortcuts may simplify early development, but they become liabilities at scale.
Enterprise buyers are not evaluating whether login works today. They are evaluating whether your SaaS authentication architecture can handle hundreds of enterprise tenants tomorrow without compromising isolation, performance, or security.
In multi-tenant B2B environments, SSO is not just about federating identities. It is about maintaining strict boundaries while operating on shared infrastructure. And that complexity is exactly why architecture matters.
Enterprise Buyer Checklist: What Security Teams Evaluate Before Signing
By the time an enterprise reaches the contract stage, they are no longer asking what SSO for the enterprise means. They are evaluating whether your architecture survives scrutiny.
Security reviews for single sign-on SaaS are structured. Buyers run through detailed checklists, and the questions are rarely superficial. They want to understand how your SaaS platform authentication behaves under edge cases, not just in happy-path demos.
One of the first areas they examine is IdP discovery. They will ask how tenant resolution happens. Is it based on email domain, subdomain, custom domain, or metadata mapping? Is routing deterministic? Can two tenants share similar domains without collision? If discovery logic feels fragile, confidence drops quickly.
Next comes tenant isolation. They will want confirmation that each enterprise configuration is fully isolated. Separate certificates, separate metadata, separate policy enforcement. They will ask how your SaaS authentication system prevents cross-tenant assertion validation. If certificate scoping is shared, it becomes a red flag.
Token validation practices are another critical area. Enterprise buyers expect strict signature validation, issuer verification, and audience restriction enforcement. They will check whether assertions are validated against tenant-specific identifiers.
They will look for replay protection and expiration enforcement. In serious authentication SaaS platforms, token validation is strict by default, not optional.
Provisioning capabilities are also evaluated. Does your system support just-in-time provisioning? Is SCIM supported for automated lifecycle management? Can role mapping occur dynamically based on IdP attributes? Enterprise IT teams expect onboarding and deprovisioning to be automated, not manual.
Support for both SP-initiated and IdP-initiated flows is usually tested. They will attempt login from their identity dashboard. They will test deep linking. They will simulate certificate rotation. They may even intentionally misconfigure metadata to observe failure behavior.
Operational maturity matters as well. Buyers will ask about certificate rotation without downtime. They will ask about SLA-backed reliability for SSO endpoints. They will review audit logging capabilities and tenant-scoped event tracing.
In short, enterprise security teams treat SSO for SaaS as a critical infrastructure component. They are not evaluating a feature; they are evaluating a trust boundary.
And if your SaaS platform authentication architecture cannot answer these questions clearly, the evaluation does not move forward.
Where LoginRadius Fits in Modern SSO for Enterprise SaaS
Enterprise buyers are not looking for patched-together SAML connectors. They are looking for a control plane that understands multi-tenant B2B reality from the ground up.
This is where LoginRadius positions itself differently in the SSO for enterprise conversation.
Instead of treating SSO as an add-on, LoginRadius approaches SaaS platform authentication as a tenant-aware identity layer. IdP discovery is configurable and dynamic. Tenant routing is built into the authentication flow, not layered on top as an afterthought. Each enterprise tenant maintains isolated configurations, certificates, metadata, and policy enforcement rules.
For organizations implementing single sign-on SaaS, this means supporting both SAML and OIDC without compromising validation strictness. Assertions are validated against tenant-specific certificates. Audience restrictions are enforced per organization. Sessions are issued with a tenant-scoped context embedded into tokens.
LoginRadius also supports both SP-initiated and IdP-initiated flows in a structured manner, ensuring that deep links are preserved and routing decisions remain deterministic. This is critical in enterprise environments where login may originate from multiple directions.
Provisioning is another layer that enterprises evaluate carefully. With support for just-in-time provisioning and SCIM, SaaS authentication extends beyond login into lifecycle management. User onboarding and deprovisioning remain synchronized with enterprise identity systems, reducing drift and manual intervention.
Operational maturity matters as well. Certificate rotation, metadata updates, and tenant configuration changes are handled without impacting other customers. This isolation-first model aligns with how enterprise security teams expect authentication SaaS platforms to operate.
In short, LoginRadius is built to support SSO for SaaS environments where tenant isolation, strict validation, and dynamic discovery are not optional features but architectural requirements.
Because in enterprise B2B SaaS, SSO is not just about enabling login. It is about enforcing trust boundaries at scale.
The Future of Single Sign-On SaaS: Beyond Federation
Enterprise SSO for enterprises is evolving. Federation is still foundational, but buyers are beginning to expect more than SAML compatibility and OIDC support.
One clear shift is toward adaptive and risk-aware authentication layered on top of traditional SaaS platform authentication. Enterprises want to evaluate context during login, device posture, geolocation anomalies, behavioral patterns, even when authentication originates from a trusted identity provider. Static trust based solely on a signed assertion is no longer sufficient.
Another trend is the convergence of passkeys and enterprise SSO. As WebAuthn adoption increases, enterprise identity providers are embedding phishing-resistant authentication into their flows. That means SaaS platforms that support single sign-on must be ready to handle stronger upstream authentication signals without breaking tenant routing or policy enforcement.
Multi-tenant SaaS environments are also moving toward tighter integration between authentication and authorization. Identity assertions alone are not enough. Enterprises expect fine-grained role enforcement based on tenant context, group claims, and dynamic attribute mapping.
Authentication SaaS systems are gradually becoming unified identity control planes that bridge federation and authorization.
AI-driven anomaly detection is another emerging layer. Future-ready SaaS authentication platforms will analyze login patterns across tenants without compromising isolation. Suspicious routing patterns, repeated assertion failures, and abnormal token behavior can signal potential configuration drift or malicious activity.
Zero-trust principles are influencing enterprise SSO design as well. Trust is no longer permanent once a session is issued. Continuous validation, session re-evaluation, and context-aware enforcement are becoming standard expectations in high-security environments.
What remains constant is the requirement for strict tenant isolation. As enterprise ecosystems grow more complex, routing accuracy, certificate management, and policy enforcement must scale cleanly. The future of SSO for SaaS will reward architectures that were designed for multi-tenant precision from the beginning.
Federation may still initiate login. But the next generation of enterprise SSO is about dynamic trust evaluation layered on top of deterministic tenant routing.
And that shift will separate platforms that merely support SSO from those that are architected for enterprise identity at scale.
Conclusion
In B2B SaaS, login is not a UI interaction. It is a trust negotiation between your platform and an enterprise security perimeter.
If your SSO for enterprise strategy is limited to “we support SAML,” you are solving the wrong problem. Enterprise buyers are evaluating routing logic, tenant isolation, assertion validation strictness, provisioning depth, and operational maturity. They are assessing whether your SaaS platform authentication layer behaves predictably under complexity.
IdP discovery determines where authentication begins. Tenant routing determines whether it ends safely. Everything in between certificate validation, audience enforcement, role mapping, session binding must operate within strict organizational boundaries.
Weak single-sign-on SaaS implementations often appear functional during demos but reveal architectural gaps under real-world enterprise scrutiny. Hardcoded IdPs, shared validation layers, loosely scoped tokens, and brittle routing logic eventually surface. And when they do, trust erodes quickly.
Enterprise-ready SaaS authentication is isolation-first. Every tenant has its own configuration scope. Every assertion is validated within the tenant context. Every session carries explicit organizational binding. Reliability, certificate rotation, SP and IdP-initiated support, and provisioning synchronization are not advanced features. They are baseline expectations.
As B2B ecosystems expand and security standards tighten, authentication SaaS platforms must evolve beyond simple federation. The future demands deterministic routing, adaptive enforcement, and architectural discipline from the first redirect to the final session issuance.
In short, SSO is no longer a feature checkbox. It is the foundation of enterprise trust in your SaaS platform. Design it accordingly.
FAQs
Q: What is SSO for enterprise SaaS?
A: SSO for enterprise SaaS allows users to authenticate through their organization’s identity provider (like Okta or Azure AD) while securely accessing a multi-tenant SaaS platform with tenant-scoped isolation.
Q: How does IdP discovery work in SaaS authentication?
A: IdP discovery identifies which enterprise identity provider should authenticate a user, typically using email domain, subdomain, or custom routing logic before redirecting for login.
Q: What is tenant routing in multi-tenant SaaS?
A: Tenant routing binds an incoming authentication response to the correct organization, ensuring tokens, policies, and sessions are enforced within the proper tenant boundary.
Q: What is the difference between SP-initiated and IdP-initiated SSO?
A: In SP-initiated SSO, login begins from the SaaS application. In IdP-initiated SSO, login starts from the enterprise identity provider’s dashboard and sends an assertion directly to the app.
Q: Why is SSO architecture important for B2B SaaS platforms?
A: Because enterprise buyers evaluate isolation, validation strictness, and tenant awareness. Weak SSO architecture risks cross-tenant exposure and can stall enterprise deals.



