Introduction
If you're building a B2B SaaS product, your biggest challenges aren’t always about features. It's about who gets access to what, and how you control that without turning your codebase into a spaghetti bowl of role checks, login hacks, and emergency support tickets.
Sure, IAM sounds like a security thing. But in B2B SaaS, it’s really an architecture problem. You’re not just dealing with individual users anymore. You're dealing with entire organizations, each with their own login methods, admins, user hierarchies, and sometimes even branding demands. One partner wants Google SSO. Another insists on SAML. A third one wants their logo on the login page.
What you really need is a developer-first IAM platform built specifically for SaaS teams managing external partners and vendors. This system speaks your language (APIs, SDKs, and actual docs), scales across orgs, and doesn’t break every time someone asks for a new login method.
In this blog, we’ll walk through what SaaS IAM actually is and what to look for when implementing it in your stack. We’ll also show you how LoginRadius lets you do all this without reinventing the wheel or sacrificing your architecture to the identity gods.
What is Identity and Access Management (IAM) for SaaS?
Here’s the truth: most identity platforms weren’t built with B2B SaaS in mind. Workforce IAM solutions? Great for internal employees. Traditional CIAM tools? Solid for end-user login flows in consumer apps.
But Business Customer Identity, the kind you deal with in a multi-tenant SaaS app for external partners—is still the awkward middle child. And as a developer or product owner, that leaves you in an all-too-familiar spot: duct-taping features together to make it work.

We’re talking about building your own tenant-aware role logic. Manually provisioning orgs. Creating per-org SSO configs. And maintaining different branding layers, all while praying you don’t break someone else’s flow with your next update.
It’s messy. It’s brittle. It’s expensive to maintain. And it only gets worse as your partner network scales or your product portfolio expands.
That’s where LoginRadius Partner IAM enters the picture. Partner IAM is purpose-built to solve these B2B-specific identity challenges at the architecture level. Instead of treating your partners as just another "user type," SaaS IAM platforms like LoginRadius let you treat them as first-class organizations. That means:
-
You define and manage partner organizations, not just users
-
Each org can have its own login method (SAML, OIDC, passwordless, you name it)
-
You assign delegated admins so partners manage their own users
-
You enforce access controls scoped to their org
-
You provide branded login flows per tenant
-
And you do all of it through APIs designed for SaaS platforms not patched-in afterthoughts
The result? You eliminate the need for custom-coded identity flows, reduce your maintenance burden, and gain a scalable model that actually grows with your product roadmap. To learn more about LoginRadius partner IAM, download the insightful resource:
More importantly, it frees your developers from becoming accidental IAM engineers and lets your product teams roll out new features, org types, or partner-facing apps without reworking the access model every time.
You can learn the difference between Workforce IAM and B2B CIAM in this guide that breaks it down clearly—highlighting why SaaS IAM (B2B IAM) is essential for managing external business users securely and at scale.
SaaS Identity and Access Management Best Practices
When you're deep in the trenches building a B2B SaaS product, identity management isn't something you can afford to "wing" or bolt on later. It’s foundational, like the plumbing that holds your entire partner experience together. And the sooner you set it up right, the fewer late-night fire drills you'll face when your partner count hits double or triple digits.
Let’s walk through some practical best practices that actually scale, based on what experienced dev teams and identity architects have learned (often the hard way).
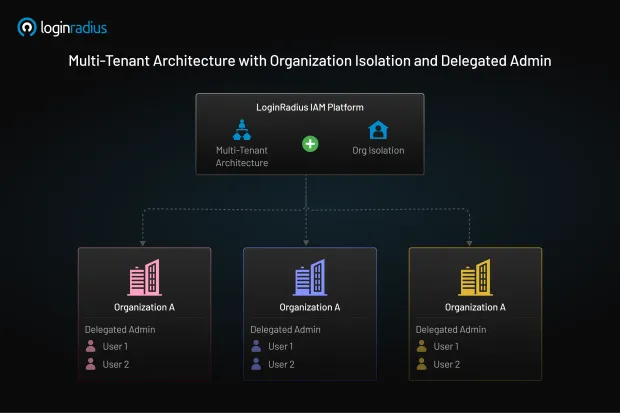
1. Model Your Architecture Around Organizations, Not Just Users
In B2B SaaS, you’re not building for individuals. You’re building for entire organizations that bring their own teams, roles, permissions, and workflows.
Treating every user as flat and unaffiliated leads to painful logic and insecure access patterns. A solid IAM setup gives each organization its own “space” in your system, completely isolated from others. This means their users, policies, authentication settings, and even branding stay cleanly scoped.
Think of each org as its own mini-tenant in your platform. That’s the mindset shift that saves your future self from countless hours of refactoring.
2. Embrace Federated Login Because Partners Will Demand It
The bigger the partner, the more likely they’ll want to use their own identity provider whether it’s Google Workspace, Azure AD, Okta, or something more obscure.
Instead of building custom SSO support for every request, a proper SaaS IAM solution lets you connect each organization to its own login method using standards like SAML or OIDC.
This keeps everyone happy: partners get the enterprise-grade authentication they trust, and your platform stays clean and scalable.
3. Use Delegated Admin So You’re Not Doing Everything
If your internal team is still manually adding users for each partner, it’s time to stop. Seriously.
Delegated admin means you can hand off user and role management to the partner’s internal team. They can invite, disable, promote, and organize their own users, without ever needing to ping your support or dev team.
It’s a win-win: they feel empowered, and your team focuses on building instead of babysitting access requests.
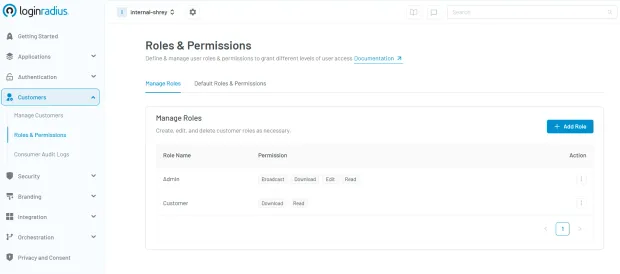
4. Build Role-Based Access That Respects Org Context
Here’s the problem with global roles: what a “Manager” does in one partner org might not match what a “Manager” should do in another. So don’t treat roles like a one-size-fits-all badge.
Instead, define roles and permissions that are scoped to each organization. That way, every partner gets exactly the level of control they need—no more, no less—and your app’s access rules stay predictable and testable.
Here’s how you can quickly define roles and permissions in the LoginRadius Admin Console:
5. Customize the Experience Per Partner
This often gets overlooked—but it’s crucial. Each partner's login experience should reflect their brand, not just yours.
By offering unique login domains, logos, and color themes for each organization, you create a seamless and professional experience. It builds trust, minimizes friction, and shows partners that your platform is built to support their identity.
And the best part? You don’t need to jump through technical hoops to make it happen. With LoginRadius AI Branding, you can effortlessly generate fully branded login experiences—quickly and without coding.

6. Automate Everything You Can
Manual provisioning is a bottleneck. If your team has to create new orgs, invite users, and configure access settins by hand, you're burning time and creating room for error.
The right IAM system will let you automate most of this, whether it’s through APIs, SCIM integrations, or admin portals that partners use themselves. That’s how you scale from five partners to five hundred without collapsing under your own processes.
7. Don’t Skip Audit Trails and Access Logs
As you grow, someone's security, compliance, or even your partners will eventually ask: "Who accessed what, and when?"
If you don’t have centralized logging and per-org audit trails, you’re flying blind. A good IAM setup should let you track access patterns, flag anomalies, and respond to requests without piecing things together from multiple systems.
It’s not the flashy part of identity, but it’s critical for accountability, compliance, and building partner trust.
SaaS IAM isn’t just about login. It’s about scaling access intelligently.
Get your org model right, delegate responsibly, respect tenant boundaries, and automate wherever possible. Do that, and your product team can focus on building value instead of untangling auth logic.
These aren’t just best practices, they’re guardrails for keeping your B2B SaaS architecture sane.
What to Consider When Choosing an IAM Solution
By now, you probably know that rolling your own identity solution or relying on a workforce IAM tool to do the job can only take you so far in B2B SaaS. At some point, you need to choose a purpose-built IAM platform that won’t slow you down as you scale.
But choosing the right solution isn’t just about comparing feature checklists. It’s about understanding the core requirements of your product, your partner ecosystem, and your dev team and finding a platform that aligns with all three.
Here’s what developers, product managers, and identity architects should seriously consider before locking into any IAM provider:
1. Is It Built for B2B SaaS Use Cases?
Many IAM vendors claim to be flexible, but only a few are actually designed with multi-tenant B2B SaaS in mind. Look for solutions that treat organizations as first-class citizens, not just a tag on a user profile.
The platform should let you define, manage, and isolate partner orgs with their own:
-
User base
-
Admin controls
-
Branded login experiences
If it doesn't support those basics out of the box, you'll end up building (and maintaining) them yourself.
2. Is It Developer-Friendly?
This should be non-negotiable. Your IAM provider should offer:
-
Clean, well-documented APIs
-
SDKs in your team’s preferred languages
-
Sandbox environments for testing
-
Architecture guides and example use cases
-
Webhooks, audit logs, and event-based triggers
You don’t want your engineers spending days deciphering docs or hacking together functionality that should be native.
LoginRadius, for example, exposes everything via APIs with org creation, role assignment, SSO config, and user management all fully automatable.
3. Does It Support Flexible Federation?
Enterprise partners will ask for federated login using their own identity providers. Your IAM solution should let you configure SAML or OIDC per organization, and ideally let you manage these settings dynamically, without going through support tickets or static console toggles.
Bonus points if it supports discovery URLs and metadata import to speed things up.
4. How Granular Is Its Access Control?
Look for solutions that support org-scoped RBAC. You should be able to define roles and permissions within each organization, not just globally across your app.
This avoids the “manager in Org A can see Org B’s data” nightmare and gives your team control where it matters most.
5. Can It Handle Branding and Custom Domains?
This one’s easy to overlook but becomes a pain fast. Each partner might want their own login URL, logo, theme, and user experience. Your IAM solution should support:
-
Custom domains (e.g., login.partnerdomain.com)
-
Per-tenant theming
-
White-labeled UIs or embeddable widgets
This isn’t just about UX, it’s about showing that your platform adapts to your partners, not the other way around.
6. Does It Scale with Your Product Roadmap?
You’re not just picking a tool for today. You’re picking a foundation for future services, APIs, mobile apps, and third-party integrations.
Make sure the IAM provider:
-
Supports multi-region deployment and data residency
-
Has strong uptime SLAs and security certifications
-
Offers extensibility for new business models (like multi-org hierarchy, delegated SSO, and fine-grained policy controls)
You don’t want to migrate identity platforms two years from now. Choose one that grows with you.
7. What’s the Admin Experience Like?
You might love the API, but what about your support team? Or your customer success managers?
Make sure the solution includes a clean, usable admin UI with role delegation, org overviews, and search/filter tools so your non-dev teammates can manage identities without needing to file Jira tickets.
Choosing the right IAM platform for your SaaS business isn’t just about today’s features; it’s about avoiding tomorrow’s mess.
If you're building for B2B, you need something that supports multi-tenant architecture, delegated control, and developer-first workflows out of the gate. That's where solutions like LoginRadius Partner IAM stand out: it’s purpose-built for B2B SaaS, designed to reduce friction for your dev team, and flexible enough to adapt as your partner ecosystem grows.
The bottom line? LoginRadius Partner IAM gives you the building blocks to implement identity the right way for B2B SaaS with APIs your dev team will actually want to use, and a structure that doesn’t melt when you scale.
Conclusion
In B2B SaaS, access isn’t just a checkbox feature; it’s the backbone of trust, collaboration, and growth. And when you’re working with external partners, vendors, and resellers, managing access isn’t just about authenticating users… It’s about structuring your entire product experience around organizations.
The truth is, most identity tools weren’t built for this. They either expect you to manage individual users in a silo or retrofit internal IAM models into a multi-tenant SaaS environment. That’s how technical debt builds up. That’s how brittle access logic creeps into your codebase. That’s how onboarding slows to a crawl and security starts slipping through the cracks.
LoginRadius Partner IAM changes that. It’s purpose-built for SaaS teams who manage external organizations at scale, with APIs that feel like they were designed for developers (because they were), and with the flexibility to grow with your product.
If you’re building or scaling a B2B SaaS product, now’s the time to rethink identity. Not when you’ve duct-taped your fifth SSO integration. Not when your support team’s buried in access requests. Not when a data leak forces you to scramble.
Start early. Start right. And let IAM become a foundation for scale, not a blocker.
Ready to modernize how your SaaS platform handles partner access?
Explore the LoginRadius Partner IAM docs, or book a live demo with our team to see how you can build scalable, secure, and developer-friendly identity flows for every organization you work with.
FAQs
1. How does IAM improve security for B2B SaaS platforms?
A: IAM enforces strict access controls, isolates partner organizations, and enables role-based permissions. This minimizes unauthorized access and reduces the attack surface across your multi-tenant environment.
2. What role does Single Sign-On (SSO) play in IAM for SaaS?
A: SSO allows partner organizations to use their own identity providers, streamlining access while maintaining security. It also reduces password fatigue and centralizes authentication management.
3. Can IAM help with customer onboarding and management?
A: Yes, SaaS IAM platforms automate the onboarding of partner orgs, delegate user management, and offer APIs for provisioning. This makes it faster and more scalable to onboard and support external customers.
4. How does IAM support compliance for B2B SaaS products?
A: IAM ensures that only authorized users access data, provides audit logs, and supports MFA and policy enforcement key for meeting industry standards like GDPR, SOC 2, and HIPAA.