Introduction
Passwords alone continue to fail due to phishing, credential stuffing, brute force attacks, and data breaches. That’s where OTP (One-Time Password) comes in.
If you’ve ever had any version of this question in your mind: what does OTP mean, what is OTP, what is an OTP, or what does OTP stand for?
The answer is simple: OTP stands for One-time password. It is a temporary, single-use passcode (sometimes also called a one-time passcode, one-time code, phone code or one time verification code) that adds a short-lived security layer on top of passwords or can even power login via phones / login with OTP flows.
OTP (One-Time Password) is a temporary passcode used for secure authentication. It works once, expires quickly, and can be delivered via SMS, email, authenticator apps, hardware tokens, or generated by algorithms like TOTP and HOTP. Here are some notable characteristics of OTP that helps improve login security:
OTPs improve login security and are widely used in banking, fintech, e-commerce, healthcare, enterprise apps, and consumer services.
-
Consists of 4-8 digits that are valid only for a brief period.
-
Once entered successfully or once they expire, they become completely unusable.
- The one-and-done nature of OTP makes it tough for attackers to exploit.
-
Short lifetime (usually 30 to 120 seconds) which auto expires (helpful in the event of attacks).
OTPs are deeply integrated into modern digital habits. When users receive a code via SMS, open a banking app with app-based OTP, or retrieve a code from email during account verification, they're interacting with OTP authentication. As cyber threats evolve, OTP meaning now extends beyond convenience—it represents a fundamental security layer designed to reduce dependency on static passwords and strengthen verification across distributed, multi-device environments.
As cyber threats evolve, OTP meaning now extends beyond convenience; it represents a fundamental security layer designed to reduce dependency on static passwords and strengthen verification across distributed, multi-device environments.
This guide explains OTP meaning, what is an OTP code, what is the OTP code, how OTP works, different types of OTPs (HOTP vs TOTP), OTP limitations, modern OTP threats, and the best ways to use OTP safely.
You’ll also learn how LoginRadius helps developers and businesses deploy secure, scalable OTP authentication across web, mobile, and enterprise environments—including email OTP, SMS one time password, app-based OTP, and policy-driven controls like OTP expiry time and retry limits.
By the end, you’ll have a complete understanding of what a one-time password is, the strengths and weaknesses of one-time passcodes, and how OTP fits into a modern authentication strategy whether you call it an otp code, otp password, otp security code, otp authentication code, or simply enter OTP at login.
What Is OTP?
A One-Time Password (OTP) is a short-lived, single-use code used to verify a user’s identity during login or transactions. Unlike traditional passwords, an OTP expires quickly and cannot be reused, making it more secure against common attacks.
Passwords alone are no longer sufficient to protect against threats like phishing and credential stuffing. OTP adds an extra layer of security by ensuring that even if login credentials are compromised, unauthorized access is still blocked.
There are two main types of OTP:
-
TOTP (Time-Based OTP): Generates codes based on a time window (e.g., every 30 seconds)
-
HOTP (HMAC-Based OTP): Generates codes based on a counter value
It is a temporary, single-use code generated for authentication purposes. Unlike static passwords, an OTP is valid for only one session or transaction and typically expires within seconds.
In simple terms, OTP adds an extra verification layer to confirm that the user attempting access is legitimate.
This guide explains how OTP works, the differences between TOTP and HOTP, potential security risks, and best practices for implementing OTP in modern authentication systems.
How OTP Works
OTP systems rely on cryptographic algorithms, shared secret keys, time windows, or sequential counters to generate secure one-time passcodes. When a user initiates a login or sensitive action, a server produces a unique OTP and delivers it through SMS, email, voice, push notification, or an authenticator app.
The user enters the OTP, and the server verifies whether it matches the generated value within the allowed timeframe. Behind the scenes, OTP workflows are more sophisticated. For SMS and email OTP, the server instantly sends the code through messaging infrastructure, and the OTP is stored temporarily for verification.
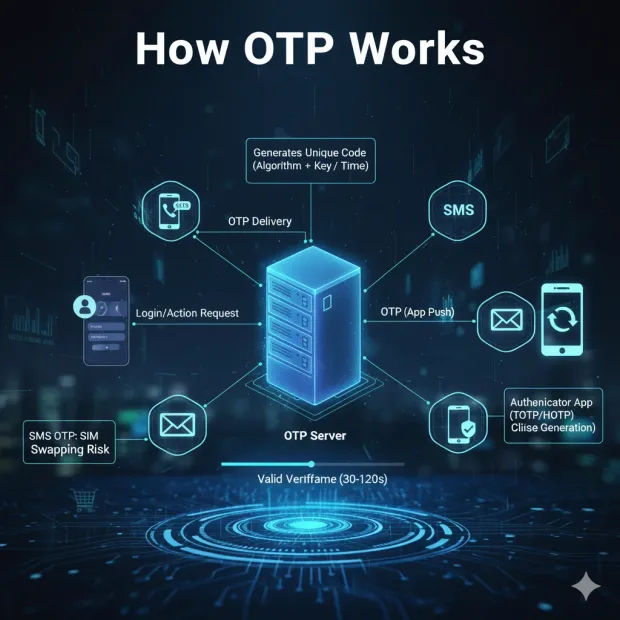
For TOTP or HOTP, the user’s authenticator app generates the OTP independently, using cryptographic calculations that must match the server's own calculation. This allows offline OTP generation and reduces dependency on network delivery.
OTP authentication works because it binds login attempts to a short-lived credential tied to the user or device. Even if an attacker manages to obtain the user's password, they cannot log in without the matching OTP.
However, OTP security heavily depends on delivery channels and user behavior. For instance, SMS OTP can be intercepted via SIM swapping or SS7 network flaws, whereas app-based OTPs are more resilient. Understanding how OTP works helps organizations choose secure OTP types and integrate them into their MFA strategy effectively.
One-Time Password Examples
Below are clear OTP examples so readers understand what is an OTP code in real life is, and what “your OTP code is …” actually means.
Example 1: OTP Login (Password + OTP)
-
User enters username + password
-
System prompts: enter OTP / enter OTP code
-
User receives an OTP and enters the otp number
-
Server validates it and grants access
This is classic OTP authentication, and it’s why people search for what is OTP authentication or what is OTP verification.
Example 2: Login via OTP (Passwordless-ish OTP)
Some apps support login with OTP where the user enters an email/phone and gets a code:
-
User enters identifier (email/phone)
-
System sends one time passcode
-
User enters the one-time code verification prompt
-
System logs the user in
This flow is commonly called login via OTP, otp sign in, or otp based authentication (and it’s also why you see queries like what is my OTP code).
Example 3: Banking / Fintech Transaction Approval
In many financial apps, OTP is used to approve a transaction: This is why people ask meaning of OTP in bank, meaning of OTP in banking, or otp-based authentication for secure banking.
It usually means a single use password (a one-time code) bound to a transaction context and an expiry window.
Modern identity platforms like LoginRadius enable financial institutions to implement secure OTP authentication for high-risk actions such as payments, fund transfers, and account updates while enforcing controls like short expiry windows, retry limits, and adaptive risk-based verification.
With platforms like LoginRadius, OTP is not just a code it becomes part of a broader multi-layered authentication strategy that protects users against fraud, phishing, and unauthorized transactions.
Example 4: Account recovery (email OTP)
A user forgets a password and receives an email OTP:
-
The system shows: “enter your OTP” or “enter the one-time password.”
-
The user enters the otp verification code
-
The reset continues
Types of OTP (SMS, Email, App-Based, Hardware)
OTP systems come in multiple forms, each offering different strengths, limitations, and implementation considerations. Understanding these types helps organizations choose the right blend of security and user experience.
SMS OTP
SMS OTP is the most widely used format, especially in consumer apps. A one time passcode is sent directly to the user’s phone via text message. Advantages include universal accessibility and minimal setup.
Typical UX:
-
“Your OTP is 482193”
-
“Enter OTP meaning: enter the temporary code we sent.”
-
“OTP is valid for how much time?” Usually, a short window like 30–120 seconds, depending on policy.
Why it’s used:
-
Very low setup effort
-
Works on almost any phone
-
Great for onboarding and low/medium-risk actions
Key security note:
- SMS OTP can be vulnerable to SIM swapping, call/SMS forwarding, and certain telecom interception risks. This is why many teams treat SMS OTP as a fallback factor and prefer app-based OTP for higher-risk access.
From a security standpoint, temporary or shared numbers are risky because they weaken identity assurance and can enable account takeovers or fraud. For real authentication, OTP should be sent only to a verified, user-controlled channel. Despite these flaws, businesses still use SMS OTP for onboarding, low-risk actions, and fallback authentication.
Email OTP
Email OTPs send verification codes to users’ inboxes. They provide convenience and easy implementation but rely on email account security—which is often weaker than device security. Email OTP is best suited for account verification, password resets, and medium-risk workflows.
App-Based OTP
Apps such as Google Authenticator, Authy, 1Password, or Microsoft Authenticator generate TOTPs locally on the device. These offer stronger security because they avoid carrier networks and depend on device-based cryptography. They work offline, resist interception, and suit high-risk workflows.
Hardware Token OTP
Physical devices (YubiKeys, RSA tokens) generate OTPs independently of phones or apps.
They offer the highest security but come with cost and operational overhead, making them ideal for enterprise or regulatory environments.
Each OTP type plays a role depending on threat level, user convenience, and authentication requirements.
TOTP vs HOTP vs SMS OTP Comparison
| Feature | TOTP | HOTP | SMS OTP |
|---|---|---|---|
| Security Level | High | Medium | Low-Medium |
| Expiry | Time-based (30 seconds) | Counter-based | Short-lived (varies) |
| Delivery | Authenticator app | Authenticator app | SMS |
| Offline Support | Yes | Yes | No |
| Phishing Resistance | High | Medium | Low |
| Use Case | MFA applications | Legacy systems | Basic verification |
One-Time Password as Voice Message
One-time password as a voice message (voice OTP) calls the user and reads the otp code aloud. This is common when:
-
users can’t receive SMS reliably
-
accessibility needs are a priority
-
multi-channel redundancy is required
Voice OTP still follows the same basics:
-
it’s an otp one time password
-
it expires quickly
-
users must enter OTP code to verify
Security considerations:
-
voice can be targeted by call forwarding scams or social engineering
-
always combine with rate limits, anomaly checks, and fraud monitoring for high-risk actions
One-Time Password as Push Notification
One-time password as push notification is a modern option where the OTP arrives through an app notification, sometimes as:
-
a code the user types (one-time code), or
-
an approve/deny prompt (a push-based verification step)
Why teams like it:
-
better UX than copying codes from SMS/email
-
tighter binding to an app session
-
often pairs well with device signals
Important distinction:
- Push notifications can reduce friction, but your security still depends on device integrity, anti-phishing controls, and secure session handling.
HOTP Explained
HOTP (HMAC-Based One-Time Password) is a counter-based OTP algorithm standardized by the IETF. Both the server and user device store the same shared secret key. During each authentication attempt, they apply a cryptographic hash function (HMAC-SHA1) to the secret key and a counter value. This produces a numerical OTP. Every time a new OTP is requested, the counter increments.
HOTP is reliable but requires synchronization. If the user’s device increments the counter but the server doesn’t, OTP mismatches occur. To compensate, servers often allow a small “look-ahead window” that accepts slightly advanced counter values.
Because HOTP doesn’t depend on time, it works in offline and low-connectivity environments. Hardware tokens commonly rely on HOTP, making it useful in enterprise security, industrial systems, and legacy MFA setups. However, HOTP codes remain active until used, giving attackers more time to exploit intercepted codes. This is why modern applications have shifted toward TOTP, which limits code validity, improving security and reducing replay attacks.
TOTP Meaning and How It Works
TOTP meaning “Time-Based One-Time Password” refers to codes generated using a shared secret and the current time sliced into 30-second or 60-second intervals. Both the server and user’s authenticator app independently compute the OTP, ensuring they match without needing constant network communication.
TOTP is now the industry standard for MFA due to its improved security characteristics. Time-based expiration reduces the threat window dramatically. Even if a TOTP is intercepted, the attacker must use it almost instantly—making most attacks impractical. TOTP algorithms also rely on secure key storage (often in secure enclaves), reducing the risk of secret extraction.
TOTP meaning has expanded beyond cybersecurity circles. It’s now a common feature in consumer apps, enterprise apps, and payment verification. Because TOTPs are easy to implement using open standards and require no messaging infrastructure, they are cost-effective and widely adopted across industries.
App-Based OTP vs SMS OTP
While SMS OTP remains extremely popular due to simplicity, app-based OTPs deliver significantly stronger security. SMS networks rely on older telecom infrastructure (SS7) vulnerable to interception, SIM swap attacks, and unauthorized forwarding. Attackers frequently exploit mobile carriers’ customer support channels to hijack phone numbers and intercept OTPs intended for victims.
App-based OTPs, however, generate TOTPs offline using cryptographic operations. They do not rely on network messaging, making them resistant to interception. The secret key lives securely on the device, reducing exposure to attackers. App-based OTPs also have the advantage of being free to send, unlike SMS OTPs which incur messaging costs.
From a user experience perspective, app-based OTPs require initial setup but become frictionless afterward. Many modern platforms offer push-based OTP or auto-fill integrations to make the experience seamless. For security-conscious organizations, app-based OTP is often recommended as the primary OTP method, with SMS OTP reserved for fallback or customer onboarding.
Why Would You Use One-Time Passwords?
If you’re asking what is meant by OTP or why is one time password safe, here’s the real reason businesses use it: OTP reduces the damage static credentials cause.
1. Passwords get stolen. OTP makes them harder to reuse.
A password can be replayed forever. An OTP one-time password can’t. Even if attackers capture a password through phishing or a breach, they still need the otp code generated for that exact session.
This is why you’ll often see “enter your OTP code” after a password step or in OTP based login / otp login experiences where the one-time code becomes the login factor.
2. OTP is easy to ship, easy to use, and works across channels.
From a product standpoint, OTP is popular because you can deliver it in multiple ways:
-
email one-time password/email OTP
-
one-time password SMS / sms one-time-password
-
authenticator apps (TOTP)
-
hardware tokens (HOTP/TOTP)
It’s also familiar to users: they’ve seen OTP messages, OTP message meaning, and what is an OTP message prompts in banking, checkout, and account recovery.
3. OTP supports step-up verification and risky actions.
OTP isn’t only for login. Teams use it for:
-
payment approval
-
new device verification
-
profile changes
-
admin actions
-
account recovery
This is where one-time authentication code, one-time token authentication, and “enter one-time password (OTP) sent to your email/mobile” patterns come in.
4. OTP helps meet compliance expectations
Many orgs use OTP to support MFA and verification controls in regulated workflows. It’s not automatically “perfect,” but it’s often a baseline factor for controlled access when combined with rate limiting, device intelligence, and monitoring.
Limitations and Security Risks of OTP
Despite its benefits, OTP is not a perfect security measure. Several risks emerge from delivery channels, user behavior, and advanced attacker tooling.
-
SIM Swapping & Phone Number Hijacking: Attackers impersonate users and convince carriers to transfer phone numbers.
-
Phishing & AITM Attacks: Attackers proxy login pages and capture OTPs in real time using automated phishing kits.
-
Malware-Based Interception: Mobile malware can read SMS, steal screen content, or bypass OTP dialogs.
-
Email Account Compromise: If email is compromised, email OTP becomes ineffective.
-
OTP Fatigue: Users become desensitized when repeatedly asked for OTPs, leading to risky behavior.
While OTP provides a good baseline, organizations increasingly combine it with adaptive MFA, device identity, and behavioral analytics to offset these risks. OTP remains valuable but is no longer the strongest MFA factor.
Modern OTP Threats and Attack Techniques
Attackers continue evolving OTP-bypassing techniques. These threats surpass traditional phishing and require extra caution.
-
Adversary-in-the-Middle (AITM): Attackers intercept OTPs using reverse proxy tools like Evilginx.
-
Session Hijacking: Attackers bypass OTP by stealing active sessions rather than verifying credentials.
-
Automated MFA Relay Attacks: Cybercrime kits forward OTPs instantly from victims to attacker servers.
-
SIM-Swap Automation Bots: Some threat actors have automated the SIM swap request process.
-
OTP Harvesting Bots: Voice bots impersonate banks or service providers and persuade victims to reveal OTPs.
These threats underline why OTP should not function as the sole authentication barrier. Stronger phishing-resistant methods may be required for high-risk apps.
OTP Best Practices
To maximize OTP effectiveness and security, organizations should adopt a layered, standards-aligned approach.
-
Prefer app-based OTP or TOTP over SMS OTP
-
Require strong device-level protections for authenticator apps
-
Store secrets in secure enclaves
-
Enforce OTP expiry within 30–60 seconds
-
Implement rate limiting and brute-force detection
-
Use adaptive MFA to request OTP only during risk
-
Treat SMS OTP as a fallback factor
-
Educate users on OTP scams and social engineering
-
Combine OTP with device fingerprinting for high-risk workflows
These best practices ensure OTP remains effective and aligned with modern access security standards.
OTP vs Passkeys
Passkeys represent a modern evolution beyond OTP and passwords. Unlike OTP, which relies on user-entered codes, passkeys use public-key cryptography with device-bound private keys. Passkeys cannot be phished, intercepted, or reused.
Key Differences
| Feature | OTP | Passkeys |
|---|---|---|
| User Input | Required | None |
| Phishing Risk | Medium–High | Zero |
| Delivery Channel | SMS, Email, Apps | Device-based |
| Underlying Tech | Shared secrets | Public/private keys |
| UX | Moderate friction | Highly seamless |
Organizations increasingly pair OTP with passkeys: OTP for recovery or fallback, passkeys for daily authentication.
Industries that Benefit From One Time Passwords
OTPs improve login security and verification, which is why they’re widely used in:
Banking & Fintech
-
card-not-present verification, transfers, high-value actions
-
Common searches here include the meaning of OTP in bank, what is OTP password is, and “OTP code meaning” in transaction screens.
eCommerce & Marketplaces
-
checkout verification, account sign-in protection, fraud reduction
-
OTP helps protect against stolen credential reuse and scripted abuse.
Healthcare
-
secure portal access, patient identity checks, sensitive record workflows
-
OTP supports access control when combined with MFA policies.
Enterprise SaaS & Admin Access
-
admin console step-up authentication
-
remote access verification
-
secure partner/vendor portal logins
OTP via WhatsApp
WhatsApp OTP is rapidly gaining adoption as a secure and user-friendly delivery channel.
Benefits include:
-
Higher delivery reliability compared to SMS
-
End-to-end encrypted communication
-
Better user engagement
This makes WhatsApp OTP especially popular in emerging markets.
Telecom & Consumer Apps
- SIM/account changes, number verification, risky account settings changes
Travel, Logistics, and Shipping Workflows
People sometimes search what OTP means in shipping. In shipping/delivery contexts, OTP may refer to a delivery verification code shared with the recipient to confirm handoff (implementation differs by provider). In identity/security contexts, OTP still means one-time password—so it’s worth clarifying the context in the blog.
How LoginRadius Supports OTP Authentication
LoginRadius strengthens OTP implementation with enterprise-grade security, developer flexibility, and seamless user experience.
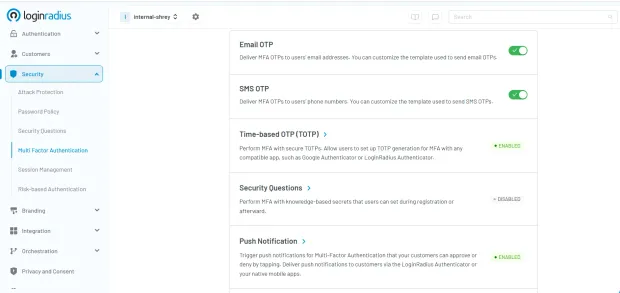
1. Multi-Channel OTP Delivery
SMS, email, voice OTP, WhatsApp OTP, and app-based tokens.
2. Built-In TOTP Support
Natively supports authenticator apps with secure secret provisioning.
3. Adaptive Authentication Integration
LoginRadius automatically analyzes device posture, geolocation, IP reputation, and behavior, triggering OTP only when needed through its advanced adaptive authentication.
4. Robust Security Controls
-
Encrypted secret storage
-
Automated brute-force protection
-
OTP retry policies
-
Device trust integration
5. Flexible Developer Experience
-
SDKs for web, Android, iOS
-
Customizable workflows
6. Enterprise-Ready Governance
Centralized policy control, audit logs, and compliance reporting.
With LoginRadius, OTP becomes part of a broader identity strategy—allowing businesses to secure accounts while preparing for a future powered by passkeys and passwordless authentication.
OTP Troubleshooting: Common Issues
OTP Not Received
Users may not receive OTP due to:
-
Network delays
-
SMS filtering or blocking
-
Incorrect phone number
Solution: Always provide fallback channels like email or authenticator apps.
OTP Expired
Most OTPs expire within 30–60 seconds.
If expired:
-
Request a new OTP
-
Avoid delays in entering the code
Incorrect OTP
Entering wrong OTP multiple times may:
-
Lock the account temporarily
-
Trigger security alerts
Best practice: Implement retry limits and rate limiting.
Conclusion
OTP has become a foundational element of modern authentication. It offers quick, simple, and fairly secure verification that users understand intuitively. But in today’s threat landscape where attackers use SIM swapping, phishing proxies, malware, and automated bots OTP alone is not enough.
OTP (One-Time Password) is a widely used authentication mechanism that enhances security by generating short-lived, single-use codes. While methods like TOTP and HOTP provide stronger security compared to SMS-based OTP, modern threats such as phishing and SIM swap attacks highlight their limitations.
As digital identity evolves, organizations are increasingly adopting phishing-resistant alternatives like passkeys. Still, OTP remains a critical layer in multi-factor authentication strategies, especially when implemented with best practices and secure delivery mechanisms.
The key is to treat OTP as one element of a layered authentication strategy. Pair it with stronger device authentication, adaptive MFA, behavioral analytics, or passkeys to achieve meaningful resistance against modern identity attacks.
Platforms like LoginRadius help organizations strike this balance by integrating OTP into a flexible, multi-factor identity experience that protects users without sacrificing convenience.
As authentication continues evolving, OTP will remain useful but only when deployed intelligently and reinforced with stronger, phishing-resistant capabilities.
FAQs
Q: What does OTP mean?
A: OTP means “One-Time Password.” It’s a temporary, single-use code used for authentication or verification.
Q: What does OTP stand for?
A: OTP stands for One-Time Password, sometimes also called a one-time passcode or one-time code.
Q: What is an OTP code?
A: An OTP code is the short numeric/alphanumeric passcode you receive (via SMS, email, app, voice, or push) and enter OTP to verify your identity.
Q: What does OTP mean in text messages?
A: If someone asks what does OTP mean in a text or meaning of OTP in text, it usually refers to a one-time password code sent via SMS for verification (not a “texting slang” term in most authentication contexts).
Q: What is an OTP message?
A: An OTP message is the SMS/email/push message that contains your one time passcode—for example: “Your OTP is 739201.”
Q: What is OTP verification?
A: OTP verification is the step where the system checks whether the otp number you entered matches the expected value and is still valid (not expired, not already used).
Q: How does OTP work?
A: OTP works by generating a unique code using cryptographic logic (time-based like TOTP or counter-based like HOTP) or server-side generation for SMS/email delivery, then validating it within a short expiry window.
Q: What does OTP mean in banking?
A: In banking, OTP typically means a one-time password used to confirm sensitive actions like logins or transactions—basically a short-lived approval code.
Q: What does OTP mean in shipping?
A: In some delivery/shipping workflows, OTP may mean a delivery confirmation code shared with the recipient to confirm successful handoff. It’s separate from authentication OTP, but the “single-use code” concept is similar.
Q: What is my OTP code?
A: Your OTP code is the temporary code generated for your current verification attempt. If you didn’t request it, don’t share it—OTP scams often rely on social engineering.
Q: OTP security news: is OTP still safe?
A: OTP is safer than passwords alone, but modern threats like AITM phishing, SIM swap, and session hijacking can bypass weak OTP deployments. Best practice is to use app-based OTP/TOTP where possible, enforce short expiry, and add fraud/risk checks.
Q: What is the difference between passwordless and OTP?
A: OTP can be used in passwordless flows (login via OTP), but it’s still a “shared-secret style” code the user types. True passwordless methods like passkeys use device-bound public-key cryptography and are more phishing-resistant.